7.4 Windows驱动开发:内核运用LoadImage屏蔽驱动
在笔者上一篇文章《内核监视LoadImage映像回调》中LyShark简单介绍了如何通过PsSetLoadImageNotifyRoutine函数注册回调来监视驱动模块的加载,注意我这里用的是监视而不是监控之所以是监视而不是监控那是因为PsSetLoadImageNotifyRoutine无法实现参数控制,而如果我们想要控制特定驱动的加载则需要自己做一些事情来实现,如下LyShark将解密如何实现屏蔽特定驱动的加载。
要想实现驱动屏蔽其原理很简单,通过ImageInfo->ImageBase得到镜像基地址,然后调用GetDriverEntryByImageBase函数来得到程序的入口地址,找NT头的OptionalHeader节点,该节点里面就是被加载驱动入口,通过汇编在驱动头部写入ret返回指令,即可实现屏蔽加载特定驱动文件。
原理其实很容易理解,如果我们需要实现则只需要在《内核监视LoadImage映像回调》这篇文章的代码上稍加改进即可,当检测到lyshark.sys驱动加载时,直接跳转到入口处快速写入一个Ret让驱动返回即可,至于如何写出指令的问题如果不懂建议回头看看《内核CR3切换读写内存》文章中是如何读写内存的,这段代码实现如下所示。
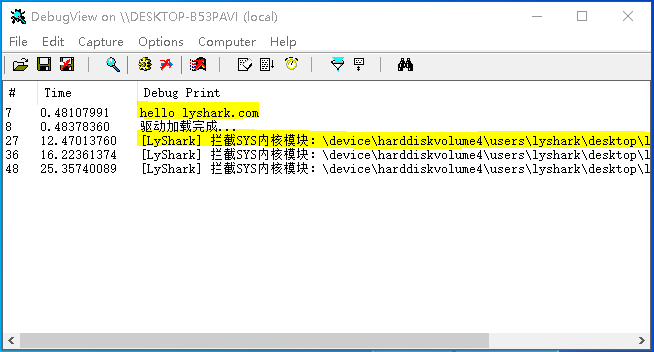
#include 首先运行我们的驱动,然后我们接着加载lyshark.sys则你会发现驱动被拦截了。
我们看下驱动加载器,提示的信息是拒绝访问,因为这个驱动其实是加载了的,只是入口处被填充了返回而已。
除了使用Ret强制返回的方法意外,屏蔽驱动加载还可以使用另一种方式实现禁用模块加载,例如当驱动被加载首先回调函数内可以接收到,当接收到以后直接调用MmUnmapViewOfSection函数强制卸载掉即可,如果使用这种方法实现则这段代码需要改进成如下样子。
#include 加载这段驱动程序,当有DLL文件被加载后,则会强制弹出,从而实现屏蔽模块加载的作用。
当然用LoadImage回调做监控并不靠谱,因为它很容易被绕过,其实系统里存在一个开关,叫做PspNotifyEnableMask如果它的值被设置为0,那么所有的相关操作都不会经过回调,所有回调都会失效。