【userfaultfd 条件竞争】starCTF2019 - hackme
前言
呜呜呜,这题不难,但是差不多一个多月没碰我的女朋友 kernel pwn 了,对我的 root 宝宝也是非常想念,可惜这题没有找到我的 root 宝宝,就偷了她的 flag。
哎有点生疏了,这题没看出来堆溢出,直接条件竞争打了,但感觉条件竞争打简单一些。
题目分析
内核版本 4.20.13
开了 smap/smep/kaslr
给了 config 配置文件,查看得到如下信息:
# CONFIG_SLAB is not set
# CONFIG_SLAB_MERGE_DEFAULT is not set
# CONFIG_SLAB_FREELIST_RANDOM is not set
# CONFIG_SLAB_FREELIST_HARDENED is not set
# CONFIG_STATIC_USERMODEHELPER is not set
所以这里的 slub obj 的 freelist 在头8字节,调试也是如此
然后题目实现了一个菜单堆,有增删改查的功能,漏洞主要全程没用上锁,但是我做完后去网上搜了一下,发现这题还有堆溢出,这里堆溢出就不说了,笔者是利用条件竞争做的:
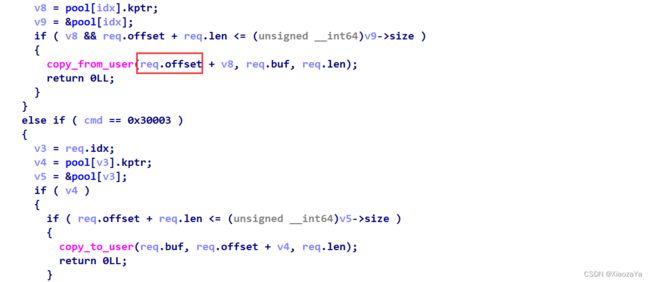
网上说这里 offset 可以为负数,导致向上溢出:) 这里我看比较是 unsigned 的就没想着溢出,而且条件竞争也很明显
漏洞利用
整体比较简单,就不多说了,主要就记录一下关键点,其实这里利用方式还挺多的,毕竟堆块大小没有限制
初始想法 seq_operations + pt_regs 进行提权 【X 没有合适的 gadget】
这里讲下为啥失败,因为这里的 gadget 大多都是这样的:)这里找了好久的 gadget,没一个行的
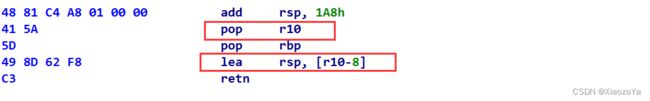
可以看到这里的 pop r10; lea rsp, [r10-8] 导致了我们无法成功劫持 rsp, 除非泄漏内核栈地址,但是如果都可以泄漏内核栈地址了,就不用这样搞了
修改 freelist 劫持 modprobe_path
劫持 freelist 的时候,这里不要直接修改 freelist 为 modprobe_path,因为系统可能会分配堆块,这时候就会报错,为啥呢?话不多说,放图:
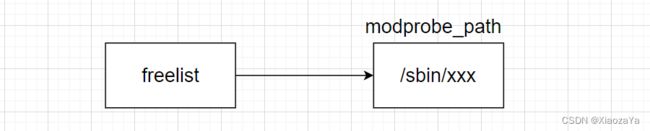
这里的 /sbin/xxx 肯定是个无效的地址啊,但是这里发现 modprobe_path 前面就是一片0区域,所以让 freelist 指向0区域即可
exp 如下:
#ifndef _GNU_SOURCE
#define _GNU_SOURCE
#endif
#include 总结
好久没碰 kernel pwn,写 exp 很不熟练了,期末后再练练,复现一些 cve
