Kubernetes系列---Kubernetes dashboard部署 | 命令参数 | 详解
dashboard部署
- 一、Kubectl 概述
-
- 1.1 kuerber 命令行的语法
-
- ① command:
- ② TYPE:
- ③ NAME:
-
- Ⅰ 通过类型和名称指定资源:
- 若分别指定多个资源类型:
- Ⅱ 若需要使用一个或多个文件指定资源:
- ④ flags:
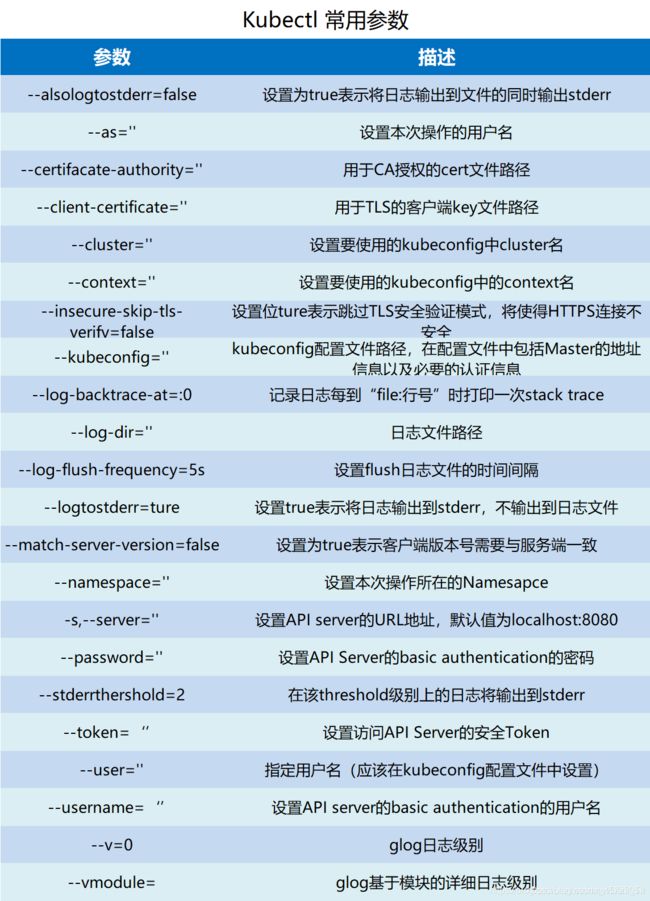
- 1.2 Kubectl 常用命令
- 1.3kubectl 输出选项
- 二、Kubernetes dashboard 部署
一、Kubectl 概述
kubectl是Kubernetes集群的命令行工具,通过kubectl能够对集群本身进行管理(删除、更新、回滚)控制着Pod的生命周期,同时能够在集群上进行容器化应用的安装部署。
1.1 kuerber 命令行的语法
语法:
kubectl [command] [TYPE] [NAME] [flags]
基本参数介绍:
① command:
子命令,用于操作kubernetes集群资源对象的命令,例如create、delete、describe、get、apply等。
② TYPE:
指定资源类型。资源类型不区分大小写,您可以指定单数,复数或缩写形式。例如,以下命令产生相同的输出
kubectl get pod pod1
kubectl get pods pod1
kubectl get po pod1
③ NAME:
指定资源的名称。名称区分大小写。如果省略名称,则显示所有资源的详细信息
例如:kubectl gets pods
对多个资源执行操作时,可以按类型和名称指定每个资源,也可以指定一个或多个文件 :
Ⅰ 通过类型和名称指定资源:
如果资源均为同一类型,则将其分组:
格式:TYPE1 name1 name2 name<#>
示例:kubectl get pod pod1 example-pod2
若分别指定多个资源类型:
格式: TYPE1/name1 TYPE1/name2 TYPE2/name3 TYPE<#>/name<#>
示例: kubectl get pod/example-pod1 replicationcontroller/example-rc1
Ⅱ 若需要使用一个或多个文件指定资源:
格式: -f file1 -f file2 -f file<#>
示例: kubectl get pod -f ./pod.yaml
一般使用YAML而不是JSON,主要因为YAML往往更加的友好,尤其是对配置文件
④ flags:
指定可选标志。例如,可以使用 -s 或 --server 标志来指定Kubernetes API服务器的地址和端口
PS: 在命令行中指定的标志将覆盖默认值和任何相应的环境变量。
1.2 Kubectl 常用命令
1.3kubectl 输出选项
kubectl 默认的输出格式为纯文本格式,可以通过-o或者-output字段指定命令的输出格式
语法如下
kubectl [command] [TYPE] [NAME] -o=<output_format>
以下为可选的输出格式及对应功能
-o=custom-columns=<spec> 根据自定义列名进行输出,以逗号分隔
-o=custom-columns-file=<filename> 从文件中获取自定义列名进行输出
-o=json
以JSON格式显示结果
-o=jsonpath=<template> 输出jsonpath表达式定义的字段信息
-o=jsonpath-file=<filename>
输出jsonpath表达式定义的字段信息,来源于文件
-o=name
仅输出资源对象的名称
-o=wide
输出额外信息,对于pod,将输出pod所在的Node名称
-o=yaml
以YAML格式显示结果
输出pod额外信息,示例:
kubectl get pod <pod-name> -o wide
以YAML格式显示Pod详细信息,示例:
kubect get pod <pod-name> -o yaml
自定义列表显示Pod信息,示例:
kubectl get pod <pod-name> -o=custom-columns=NAME:.metadata.name,RSRC:.metadata.resourceVersion
基于文件的自定义列名输出
kubectl get pods <pod-name> -o=custom-columns-file=template.txt
kubectl 还可以将输出的结果按指定字段进行排序,使用–sort-by参数以jsonpath表达式进行指定即可~
示例:
格式:kebuctl [command] [TYPE] [NAME] --sort-by=<jsonpath_exp>
按照名称进行排序
示例:
kubectl get pods --sort-by=.metadata.name
二、Kubernetes dashboard 部署
vim dashboard-configmap.yaml
apiVersion: v1
kind: ConfigMap
metadata:
labels:
k8s-app: kubernetes-dashboard
# Allows editing resource and makes sure it is created first.
addonmanager.kubernetes.io/mode: EnsureExists
name: kubernetes-dashboard-settings
namespace: kube-system
vim dashboard-controller.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
addonmanager.kubernetes.io/mode: Reconcile
name: kubernetes-dashboard
namespace: kube-system
---
apiVersion: apps/v1
kind: Deployment
metadata:
name: kubernetes-dashboard
namespace: kube-system
labels:
k8s-app: kubernetes-dashboard
kubernetes.io/cluster-service: "true"
addonmanager.kubernetes.io/mode: Reconcile
spec:
selector:
matchLabels:
k8s-app: kubernetes-dashboard
template:
metadata:
labels:
k8s-app: kubernetes-dashboard
annotations:
scheduler.alpha.kubernetes.io/critical-pod: ''
seccomp.security.alpha.kubernetes.io/pod: 'docker/default'
spec:
priorityClassName: system-cluster-critical
containers:
- name: kubernetes-dashboard
image: siriuszg/kubernetes-dashboard-amd64:v1.8.3
resources:
limits:
cpu: 100m
memory: 300Mi
requests:
cpu: 50m
memory: 100Mi
ports:
- containerPort: 8443
protocol: TCP
args:
# PLATFORM-SPECIFIC ARGS HERE
- --auto-generate-certificates
volumeMounts:
- name: kubernetes-dashboard-certs
mountPath: /certs
- name: tmp-volume
mountPath: /tmp
livenessProbe:
httpGet:
scheme: HTTPS
path: /
port: 8443
initialDelaySeconds: 30
timeoutSeconds: 30
volumes:
- name: kubernetes-dashboard-certs
secret:
secretName: kubernetes-dashboard-certs
- name: tmp-volume
emptyDir: {}
serviceAccountName: kubernetes-dashboard
tolerations:
- key: "CriticalAddonsOnly"
operator: "Exists"
vim dashboard-rbac.yaml
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
labels:
k8s-app: kubernetes-dashboard
addonmanager.kubernetes.io/mode: Reconcile
name: kubernetes-dashboard-minimal
namespace: kube-system
rules:
# Allow Dashboard to get, update and delete Dashboard exclusive secrets.
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs"]
verbs: ["get", "update", "delete"]
# Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
# Allow Dashboard to get metrics from heapster.
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
labels:
k8s-app: kubernetes-dashboard
addonmanager.kubernetes.io/mode: Reconcile
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: kubernetes-dashboard-minimal
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
vim dashboard-secret.yaml
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
# Allows editing resource and makes sure it is created first.
addonmanager.kubernetes.io/mode: EnsureExists
name: kubernetes-dashboard-certs
namespace: kube-system
type: Opaque
---
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
# Allows editing resource and makes sure it is created first.
addonmanager.kubernetes.io/mode: EnsureExists
name: kubernetes-dashboard-key-holder
namespace: kube-system
type: Opaque
vim dashboard-service.yaml
apiVersion: v1
kind: Service
metadata:
name: kubernetes-dashboard
namespace: kube-system
labels:
k8s-app: kubernetes-dashboard
kubernetes.io/cluster-service: "true"
addonmanager.kubernetes.io/mode: Reconcile
spec:
type: NodePort
selector:
k8s-app: kubernetes-dashboard
ports:
- port: 443
targetPort: 8443
nodePort: 30001
vim k8s-admin.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: dashboard-admin
namespace: kube-system
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata: name: dashboard-admin
subjects:
- kind: ServiceAccount
name: dashboard-admin
namespace: kube-system
roleRef:
kind: ClusterRole
name: cluster-admin
apiGroup: rbac.authorization.k8s.io
--master创建dashboard工作目录--
mkdir /root/dashboard
cd dashboard/ '//将下载好的yaml文件传至该目录下'
vim /root/dashboard/k8s-admin.yaml
--资源详解--
dashboard-configmap.yaml:管理K8S业务资源,例如配置文件
dashboard-rbac.yaml:安全框架,权限分配
dashboard-service.yaml:暴露本地以供外部访问依赖service,还需要kube-proxy
dashboard-controller.yaml:网站的一些配置,例如证书
dashboard-secret.yaml:用户凭证,dashboard登录K8S需要这个
k8s-admin.yaml:管理员用户
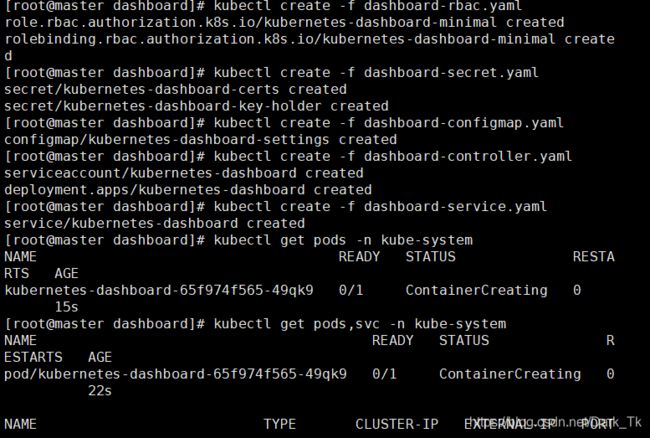
--创建资源--
'//-f表示指定文件名,以下创建顺序很重要'
kubectl create -f dashboard-rbac.yaml
kubectl create -f dashboard-secret.yaml
kubectl create -f dashboard-configmap.yaml
kubectl create -f dashboard-controller.yaml
kubectl create -f dashboard-service.yaml
'//完成后查看创建在指定的kube-system命名空间下'
kubectl get pods -n kube-system
'//查看产生的pod容器与service产生的端口映射'
kubectl get pods,svc -n kube-system
'//注意TYPE类型为NodePort,即为node节点暴露'
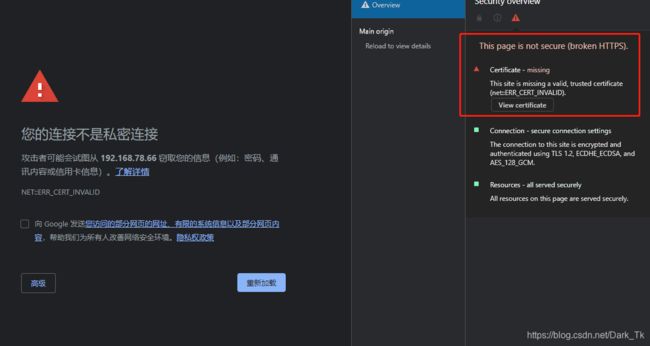
'//谷歌浏览器访问https://192.168.78.66:30001/,注意这里为https'
`创建顺序:rbac.yaml---->secret.yaml---->configmap.yaml---->controller.yaml----->service.yaml`
'//谷歌浏览器安全机制较强,暂时无法访问,不过用其他的浏览器,例如火狐就可以'
'//下面我们来解决这个问题,完成其证书的自签'
vim /root/dashboard/dashboard-cert.sh
'//撰写一个脚本,完成这个目的'
cat > dashboard-csr.json <<EOF
{
"CN": "Dashboard",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF
K8S_CA=$1
cfssl gencert -ca=$K8S_CA/ca.pem -ca-key=$K8S_CA/ca-key.pem -config=$K8S_CA/ca-config.json -profile=kubernetes dashboard-csr.json | cfssljson -bare dashboard
kubectl delete secret kubernetes-dashboard-certs -n kube-system
kubectl create secret generic kubernetes-dashboard-certs --from-file=./ -n kube-system
'//用json格式建立证书,然后删除原有证书'
. dashboard-cert.sh /root/k8s-cert/
'//执行脚本,并指定K8S的证书目录'
vim dashboard-controller.yaml
'//让自签的证书能被识别,需要修改配置文件'
45 args:
46 # PLATFORM-SPECIFIC ARGS HERE
47 - --auto-generate-certificates
'//加入以下两行'
48 - --tls-key-file=dashboard-key.pem '//注意路径'
49 - --tls-cert-file=dashboard.pem
'//修改配置文件后需apply重新更新一下'
kubectl apply -f dashboard-controller.yaml
'//注意以上报错,这里apply若不能成功创建资源,可以先delete清除资源,再来apply'
kubectl delete -f dashboard-controller.yaml
kubectl apply -f dashboard-controller.yaml '//创建成功'
kubectl get pods -n kube-system -o wide
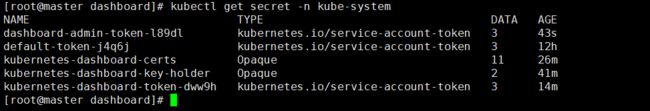
'//使用令牌来验证登录,我们先使用admin来创建管理员用户'
kubectl create -f k8s-admin.yaml
kubectl get secret -n kube-system
'//dashboard-admin-token-l89dl'
kubectl describe secret dashboard-admin-token-l89dl -n kube-system
'//查看token令牌'
'//复制这一大段令牌内容去浏览器登录'
eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJkYXNoYm9hcmQtYWRtaW4tdG9rZW4tbDg5ZGwiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC5uYW1lIjoiZGFzaGJvYXJkLWFkbWluIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQudWlkIjoiZGY3NDdlODEtYzYxNy0xMWViLWJhNWQtMDAwYzI5MTQ2NDc0Iiwic3ViIjoic3lzdGVtOnNlcnZpY2VhY2NvdW50Omt1YmUtc3lzdGVtOmRhc2hib2FyZC1hZG1pbiJ9.SfIsFrd6ungUmWoyP0sw4WDrJ7ZwZDM0TDh8rnG6TrJPy14HqSuNqLXTBfdkvh2NvS7gFXD2m4wwNIF3ht2qvIsu66UhrAVN7lDibL7To_dz1-fxyf39WC0WBSWUMHjHYiOsttmssZdJlDZAsq4MYEmnRD6Pvjnt1BM9EfW2a346_02g-YYyTJ7XJJlYNPp8egY6g2Qsf5yJin2K-zS6n3P71Wggh5cR2VuTOO83ujckRecMJI0VFrWukw1nA1uYDYfeCTcFZMt9meG2Qcd5CjXKxTGr8HSmxryE6kt8dqUt6G6l7NGnOGR6RyjVKiUkHf-J9j0P-KJC49DoQQ1P1w