nginx 第三方模块 modsecurity安装使用
官方链接:http://www.modsecurity.org/
参考链接:https://github.com/SpiderLabs/ModSecurity/wiki/Reference-Manual#Installation_for_NGINX
简介
安装modsecurity
安装nginx
配置nginx
添加OWASP ModSecurity CRS
一、简介
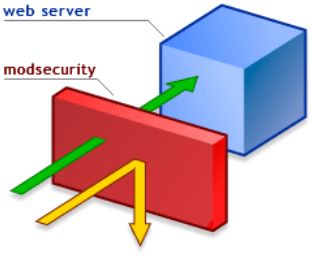
ModSecurity是一个入侵侦测与防护引擎,它主要是用于Web 应用程序,所以也被称为Web应用程序防火墙。 它可以作为Apache Web服务器的模块或是单独的应用程序来运作。ModSecurity的功能是增强Web application的安全性和保护Web application以避免遭受来自已知与未知的攻击。其防护的概念如图-1所示:
ModSecurity入侵侦测与防护引擎安装位置示意图
ModSecurity计划是从2002年开始,后来由Breach Security Inc.收购,但Breach Security Inc.允诺ModSecurity仍旧为open source,并开放源代码给大家使用。最新版的ModSecurity(一个开源的Web应用防火墙,即WAF)开始支持核心规则集(Core Rule Set,即CRS,可用于定义旨在保护Web应用免受零日及其他安全攻击的规则)了。ModSecurity团队发布的2.5.10 版还包含了其他一些特性,如并行文本匹配、Geo IP解析和信用卡号检测等,同时还支持内容注入、自动化的规则更新和脚本等内容。可以通过ModSecurity手工创建安全过滤器、定义攻击并实现主动的安全输入验证。此外,它还提供了一个面向Lua语言的新的API,为开发者提供一个脚本平台以实现用于保护Web应用的复杂逻辑。
ModSecurity的运作设计有以下的基础概念:
l 让使用者可以做任何想做的事情(Empower users to do what they want)
l 使用者设定的动作才会执行(Don’t do anything implicitly)
l 预设是不做任何动作(Be passive)
ModSecurity的部署架构
l 与Web Server结合 。
l 与Apache/nginx结合部署为网关,当作一个反向代理。
总结:
ModSecurity是一个Web应用防火墙(WAF)。当前已经有超过70%的攻击发生在网络应用层,各级组织急需要能够保证他们的系统安全性的帮助。WAF系统的部署,可以为web应用增加一个外部安全层来检测或防止攻击。针对一系列的攻击,ModSecurity为web应用提供了强大的保护,并对HTTP流量进行监测和实时分析,这些都只是很少或是根本没有影响系统的基础设施。
二、安装modsecurity
[root@slave2 work]#
wget 'https://www.modsecurity.org/tarball/2.8.0/modsecurity-2.8.0.tar.gz' tar -zxvf modsecurity-2.8.0.tar.gz cd modsecurity-2.8.0 ./configure --enable-standalone-module --disable-mlogc make
如果提示没有apxs请执行
[root@slave2 conf]# yum install httpd-devel
三、安装nginx
wget 'http://nginx.org/download/nginx-1.6.1.tar.gz' tar -zxf nginx-1.6.1.tar.gz cd nginx-1.6.1 ./configure --with-debug --prefix=/opt/nginx --add-module=../modsecurity-2.8.0/nginx/modsecurity/ make -j2 && make install
如果提示没有libxml2类似的请执行
[root@slave2 work]# yum install libxml2-devel
然后重新configure
四、配置nginx
以下为原文:
The ModSecurity configuration file must be linked in nginx.conf file using the following directives defined by nginx’s ModSecurity extension module:
location / {
ModSecurityEnabled on;
ModSecurityConfig modsecurity.conf;
ModSecurityPass @backend;
}
location @backend {
proxy_pass http://localhost:8011;
proxy_read_timeout 180s;
}
This configures ModSecurity as an Nginx request handler. The updated request flow is now: request -> modsecurity handler -> backend You will need to modify the @backend definition to point to your correct back-end web application that Nginx is proxying to. Starting with ModSecurity 2.7.2 the ModSecurityPass option was removed. So the config file looks like:
location / {
ModSecurityEnabled on;
ModSecurityConfig modsecurity.conf;
proxy_pass http://localhost:8011;
proxy_read_timeout 180s;
}
需要说明的是根据您下载的modsecurity的版本 配置稍有差别。
这里我使用的是当前最新版本2.8,应该使用
location / {
ModSecurityEnabled on;
ModSecurityConfig modsecurity.conf;
proxy_pass http://localhost:8011;
proxy_read_timeout 180s;
}
如果nginx提示你没有ModSecurityPass,很有可能你的版本为高版本。
五、添加OWASP ModSecurity CRS
参考了链接:http://blog.csdn.net/kaelrock/article/details/29840443
在你的modsecurity编译目录下文件目录类似这样
[root@slave2 modsecurity-2.8.0]# ll
total 1268
-rw------- 1 119 128 45789 Apr 15 12:44 aclocal.m4
drwx------ 2 119 128 4096 Apr 15 12:44 alp2
drwx------ 5 119 128 4096 Aug 27 02:49 apache2
-rw------- 1 119 128 381 Apr 15 12:44 authors.txt
-rwx------ 1 119 128 371 Apr 15 12:44 autogen.sh
drwx------ 2 119 128 4096 Aug 27 02:49 build
-rw------- 1 119 128 65609 Apr 15 12:44 CHANGES
-rw-r--r-- 1 root root 46341 Aug 27 02:49 config.log
-rwxr-xr-x 1 root root 67812 Aug 27 02:49 config.status
-rwx------ 1 119 128 518496 Apr 15 12:44 configure
-rw------- 1 119 128 20018 Apr 15 12:44 configure.ac
drwx------ 2 119 128 4096 Apr 15 12:44 doc
drwx------ 2 119 128 4096 Apr 15 12:44 ext
drwx------ 4 119 128 4096 Apr 15 12:44 iis
-rwxr-xr-x 1 root root 293135 Aug 27 02:49 libtool
-rw------- 1 119 128 11357 Apr 15 12:44 LICENSE
-rw-r--r-- 1 root root 29445 Aug 27 02:49 Makefile
-rw------- 1 119 128 1209 Apr 15 12:44 Makefile.am
-rw------- 1 119 128 28889 Apr 15 12:44 Makefile.in
drwx------ 2 119 128 4096 Apr 15 12:44 mlogc
-rw------- 1 119 128 8412 Apr 15 12:44 modsecurity.conf-recommended
drwx------ 3 119 128 4096 Apr 15 12:44 nginx
-rw------- 1 119 128 200 Apr 15 12:44 NOTICE
-rw------- 1 119 128 4089 Apr 15 12:44 README.TXT
-rw------- 1 119 128 7741 Apr 15 12:44 README_WINDOWS.TXT
-rw------- 1 119 128 40 Apr 15 12:44 stamp-h1
drwx------ 4 119 128 4096 Aug 27 02:50 standalone
drwx------ 7 119 128 4096 Aug 27 02:49 tests
drwx------ 2 119 128 4096 Aug 27 02:49 tools
-rw------- 1 119 128 53642 Apr 15 12:44 unicode.mapping
[root@slave2 modsecurity-2.8.0]# pwd
/root/work/modsecurity-2.8.0
复制 modsecurity.conf-recommended到nginx.conf 同级目录下并修改名字为nginx.conf中的文件名。
[root@slave2 conf]# cp modsecurity.conf-recommended /opt/nginx/conf/modsecurity.conf
[root@slave2 conf]# cp unicode.mapping /opt/nginx/conf/unicode.mapping
下载OWASP ModSecurity CRS
[root@slave2 conf]#
wget 'https://github.com/SpiderLabs/owasp-modsecurity-crs/archive/master.zip'
[root@slave2 conf]# cp master.zip /opt/nginx/conf/
[root@slave2 conf]# unzip master.zip
[root@slave2 conf]# ll owasp-modsecurity-crs-master/
total 108
drwxr-xr-x 2 root root 4096 Apr 16 22:24 activated_rules
drwxr-xr-x 2 root root 4096 Aug 27 05:50 base_rules
-rw-r--r-- 1 root root 39431 Apr 16 22:24 CHANGES
drwxr-xr-x 2 root root 4096 Apr 16 22:24 experimental_rules
-rw-r--r-- 1 root root 7485 Apr 16 22:24 INSTALL
-rw-r--r-- 1 root root 11357 Apr 16 22:24 LICENSE
drwxr-xr-x 2 root root 4096 Apr 16 22:24 lua
-rw-r--r-- 1 root root 13813 Apr 16 22:24 modsecurity_crs_10_setup.conf.example
drwxr-xr-x 2 root root 4096 Apr 16 22:24 optional_rules
-rw-r--r-- 1 root root 1485 Apr 16 22:24 README.md
drwxr-xr-x 2 root root 4096 Apr 16 22:24 slr_rules
drwxr-xr-x 8 root root 4096 Apr 16 22:24 util
[root@slave2 conf]#
cp owasp-modsecurity-crs-master/modsecurity_crs_10_setup.conf.example modsecurity_crs_10_setup.conf
在modsecurity.conf的顶部载入OWASP ModSecurity CRS,(根据需要载入特定的conf文件)。
像这样
[root@slave2 conf]# more modsecurity.conf
Include /opt/nginx/conf/modsecurity_crs_10_setup.conf
Include /opt/nginx/conf/owasp-modsecurity-crs-master/base_rules/modsecurity_crs_41_sql_injection_attacks.conf
# -- Rule engine initialization ----------------------------------------------
# Enable ModSecurity, attaching it to every transaction. Use detection
# only to start with, because that minimises the chances of post-installation
# disruption.
#
#SecRuleEngine DetectionOnly
SecRuleEngine On
# -- Request body handling ---------------------------------------------------
# Allow ModSecurity to access request bodies. If you don't, ModSecurity
# won't be able to see any POST parameters, which opens a large security
# hole for attackers to exploit.
#
SecRequestBodyAccess On
# Enable XML request body parser.
# Initiate XML Processor in case of xml content-type
#
SecRule REQUEST_HEADERS:Content-Type "text/xml" \
"id:'200000',phase:1,t:none,t:lowercase,pass,nolog,ctl:requestBodyProcessor=XML"
# Enable JSON request body parser.
# Initiate JSON Processor in case of JSON content-type; change accordingly
# if your application does not use 'application/json'
#
SecRule REQUEST_HEADERS:Content-Type "application/json" \
"id:'200001',phase:1,t:none,t:lowercase,pass,nolog,ctl:requestBodyProcessor=JSON"
# Maximum request body size we will accept for buffering. If you support
# file uploads then the value given on the first line has to be as large
# as the largest file you are willing to accept. The second value refers
# to the size of data, with files excluded. You want to keep that value as
# low as practical.
#
SecRequestBodyLimit 13107200
SecRequestBodyNoFilesLimit 131072
重启nginx, 在url后面加?and 1=1 测试,返回403,并在/var/log/modsec_audit.log产生攻击日志表示安装成功,规则文件可以根据自己需要引入base_rules里的规则文件;
本文出自 “monkey的linux小路” 博客,请务必保留此出处http://monkeyzhu.blog.51cto.com/5764358/1545651