source:http://m.blog.csdn.net/blog/jiftlixu/19159345
原理分析:http://blog.csdn.net/zhuojiuyihu/article/details/5930043
sha1withRSA md5withRSA分析
2014-2-13阅读115 评论0
sha1withRSA哈希算法分析
参考资料
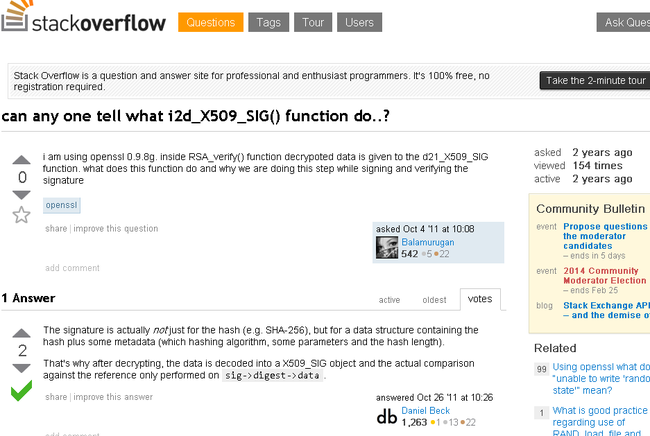
http://stackoverflow.com/questions/7646259/can-any-one-tell-what-i2d-x509-sig-function-do
http://www.cnblogs.com/adylee/archive/2009/08/03/1537813.html
提问帖子
can any one tell what i2d_X509_SIG() function do..?
i am using openssl 0.9.8g. inside RSA_verify() function decrypoted data is given to the d21_X509_SIG function. what does this function do and why we are doing this step while signing and verifying the signature
我正在使用openssl 0.98g.RSA_verify()函数解密数据调用了d2i_x509_sig函数,这个函数到底实现了什么,我们正在做签名和验签的项目。(译者:翻译不好见笑了)
openssl
asked Oct 4 '11 at 10:08
1 Answer
The signature is actually not just for the hash (e.g. SHA-256), but for a data structure containing the hash plus some metadata (which hashing algorithm, some parameters and the hash length).That's why after decrypting, the data is decoded into a X509_SIG object and the actual comparison against the reference only performed on sig->digest->data.
这个签名事实上不仅是哈希(例如,SHA-256),而是一个哈希加上一些数据元素(哈希算法、一些参数和哈希长度)。这就是为什么解密到X509_SIG结构的和
sig->digest->data的数据不一致。
示例数据一
-------------------------------------------------------------------------------------------------------------------------------------------
哈希算法:sha1
签名
3eda2b913d484b2ec347fe68200f25aadc041e1d199e1f288178bcbd08ad8d7009c17ac44d4de88286b8430553ba61948d317d1c06bd9b3359a08a57e9ce22503e982840b8b6e392ba4d793c5a3012f42edc88daf92376c1efe099ba4f9a045b1fe26c80290bcafe93f438aa2854eb89398896686b6f08932c7c26e7463154920bfeb75726cae1fdba3d26f2a11313def6b4b2c4cf8716c50403c0c928affda0652671dcd5cc66c72fd89d635850179dafe0adfb211e470ac5c9ee39ff012b44d0a9b707f96356f6f1e0ecb85a8ed18951bec317d30af0fa7998dc946123b7e2900600f65e2d66d089602c7b2aae713b55f9575a69ac4011080c24b877ad60bb
公钥数据
3082010a0282010100a01ba9a2d772a1959533752c64f5cee4b5534e14c605b297bcbc23c6d4e9d083ffc3238c95a2c881f989106fec5dc4427ffb4b9358d6ded2ae7d87b8e447b597c921ae6054c77a2545283778d297ade3b15e77df0cd2eba51e8224ff0ca5c970a0e170134195e9c99ba4568f9c7295343c442447015e40d867f2db8a47ac56f7ec4e3596c3bc04e7c9e0a7a58f0ff3070b681017e45fea4f55a0e6e5ff28169f66b4b2da919229427be4be6c7ddb4c69270399bf0e3d990f67e116ddce96f7af323eb8373cf81d6c6118d2c32fffb16ff3d055e4cf1276a0a9e172fb6a17f016638ecf855c6e05b41253af84916c3da54de4a673d1ffe6c44b343fa367ba890f0203010001
解密结果
0001ffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffff003021300906052b0e03021a050004149bb631ae07153885e2d3ae693f0ff86ebf5d6f51
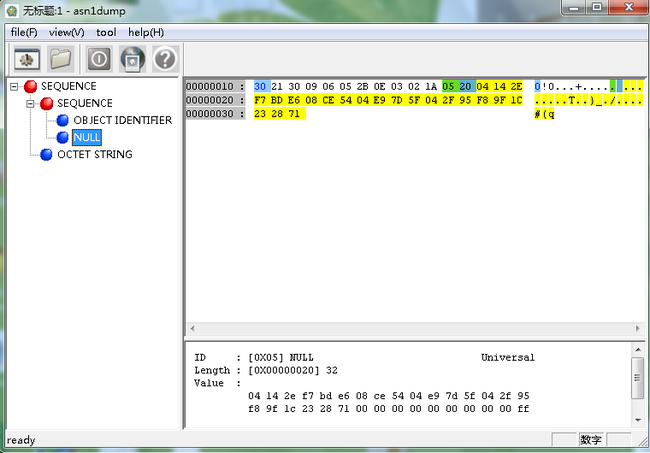
3021300906052b0e03021a050004149bb631ae07153885e2d3ae693f0ff86ebf5d6f51(35字节 ? + 哈希值20字节)
sha1哈希值应该是20字节
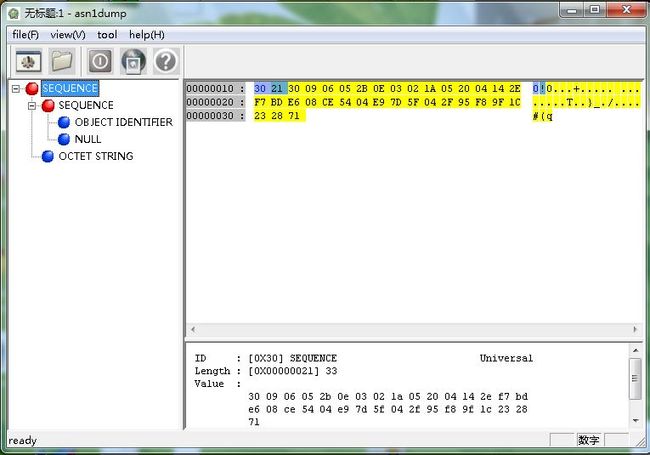
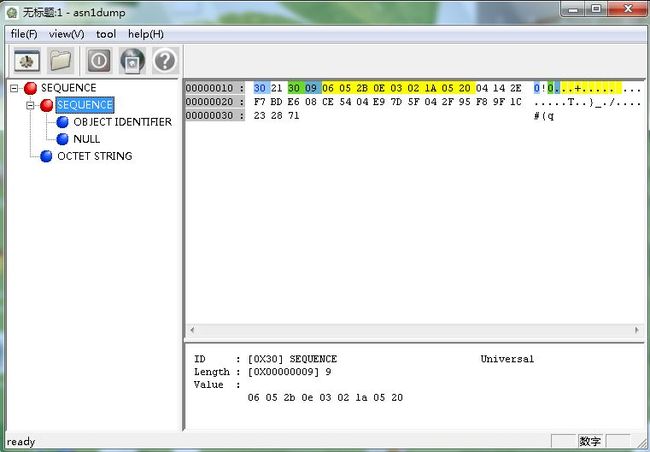
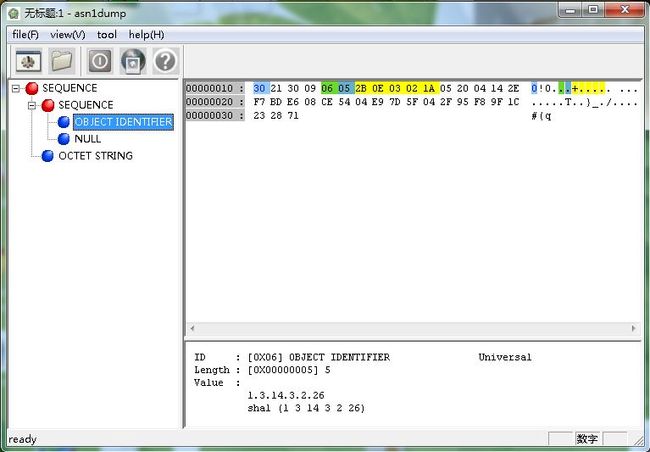
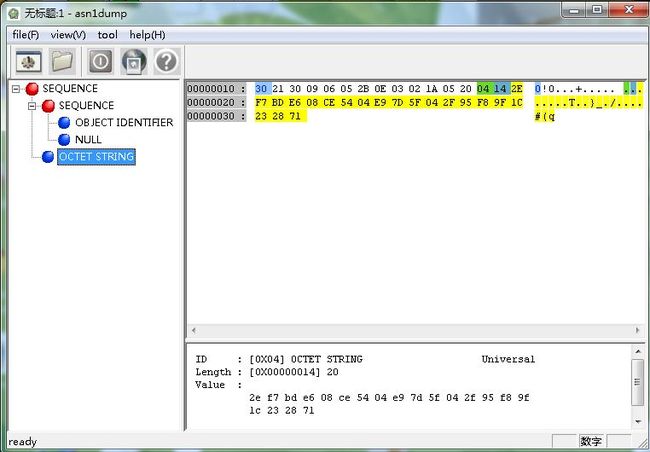
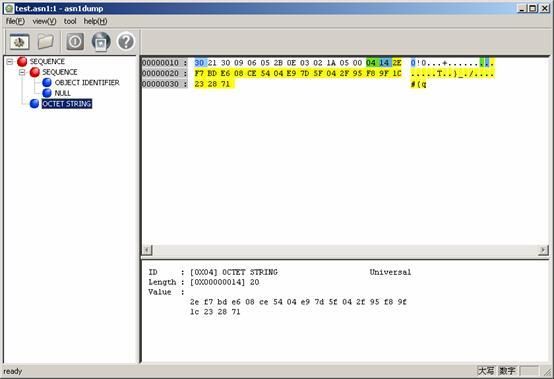
数据拆分(ASN.1 结构)
30(类型Sequence) 21(总长度) 30(类型Sequence) 09(长度) 06052b0e03021a 05(类型NULL)00(长度为0) 04(类型字符串) 14(长度) 9bb631ae07153885e2d3ae693f0ff86ebf5d6f51(20字节哈希值)
示例数据二
----------------------------------------------------------------------------------------
为了验证X509_sign调用PKCS#11接口的情况,自己实现了一个PKCS#11的包装壳(68个导出函数),实现时注意C_GetFunctionList应该指向本包装壳的函数,不然错误的使用实际的C_GetFunctionList作返回结构便也就失去意义了。X509_sign的调用方式还是不同的,java中如果使用SHA1WithRSA传入到PKCS#11接口的C_Sign或者C_SignUpdate的数据是完整的明文,但是X509_sign传入的是一个ASN.1 Sequence的一个结构,结构中包含待签名数据的摘要散列。
举例来说: