CentOS 6.4安装配置ldap+svn
一.安装ldap
[root@dev ~]# yum install openldap openldap-* -y [root@dev ~]# yum install nscd nss-pam-ldapd nss-* pcre pcre-* -y
二.配置ldap
[root@dev ~]# cd /etc/openldap/ [root@dev openldap]# ll total 16 drwxr-xr-x. 2 root root 4096 Jul 13 20:10 certs -rw-r--r--. 1 root root 282 Jun 21 17:19 ldap.conf drwxr-xr-x 2 root root 4096 Jul 13 20:10 schema drwx------ 3 ldap ldap 4096 Jul 13 20:10 slapd.d
复制配置文件
[root@dev openldap]# cp /usr/share/openldap-servers/slapd.conf.obsolete slapd.conf [root@dev openldap]# cp slapd.conf slapd.conf_`date +%Y%m%d`.bak
设置ldap管理员密码
[root@dev openldap]# slappasswd -s weyee
{SSHA}4zVLzQItaa9wp00xF7oSynhPPNKfGyJ1
[root@dev openldap]# slappasswd -s weyee |sed -e "s#{SSHA}#rootpw\t{SSHA}#g" >>/etc/openldap/slapd.conf #设置密码是weyee
[root@dev openldap]# tail -1 /etc/openldap/slapd.conf
rootpw {SSHA}6jZP4UfMlMfN0XKPch70R5+TiRCV+yT7
修改dc配置
[root@dev openldap]# vim /etc/openldap/slapd.conf #以下参数大概在114行 database bdb #使用bdb数据库 suffix "dc=dev,dc=com" #定义dc,指定搜索的域 rootdn "cn=admin,dc=dev,dc=com" #定义管理员的dn,使用这个dn能登陆openldap
优化ldap配置参数
[root@dev openldap]# vim /etc/openldap/slapd.conf loglevel 296 #定义日志级别 cachesize 1000 #换成条目数 checkpoint 2048 10 #表示内存中达到2048k或者10分钟,执行一次checkpoint,即写入数据文件的操作
配置相关权限
[root@dev openldap]# vim /etc/openldap/slapd.conf #删除默认权限,将下面的内容都删除 database config access to * by dn.exact="gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth" manage by * none # enable server status monitoring (cn=monitor) database monitor access to * by dn.exact="gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth" read by dn.exact="cn=Manager,dc=my-domain,dc=com" read by * none #添加新的权限(这是2.3的权限设置方式) access to * by self write by anonymous auth by * read
配置syslog记录ldap的服务日志
[root@dev openldap]# cp /etc/rsyslog.conf /etc/rsyslog.conf_`date +%Y%m%d`.bak #往配置文件中增加如下内容 [root@dev openldap]# tail -1 /etc/rsyslog.conf local4.* /var/log/ldap.log #重启rsyslog服务 [root@dev openldap]# /etc/init.d/rsyslog restart Shutting down system logger: [ OK ] Starting system logger: [ OK ]
配置ldap数据库路径
#创建数据文件 [root@dev openldap]# cp /usr/share/openldap-servers/DB_CONFIG.example /var/lib/ldap/DB_CONFIG [root@dev openldap]# chown ldap.ldap /var/lib/ldap/DB_CONFIG [root@dev openldap]# chmod 700 /var/lib/ldap/ [root@dev openldap]# ll /var/lib/ldap/ total 4 -rw-r--r-- 1 ldap ldap 845 Jul 13 21:05 DB_CONFIG [root@dev openldap]# egrep -v "\#|^$" /var/lib/ldap/DB_CONFIG set_cachesize 0 268435456 1 set_lg_regionmax 262144 set_lg_bsize 2097152 [root@dev openldap]# slaptest -u #检查配置文件是否正常 config file testing succeeded
ldap最后的完整配置如下
[root@dev openldap]# egrep -v "\#|^$" /var/lib/ldap/DB_CONFIG
set_cachesize 0 268435456 1
set_lg_regionmax 262144
set_lg_bsize 2097152
[root@dev openldap]# slaptest -u
config file testing succeeded
[root@dev openldap]# egrep -v "^#|^$" /etc/openldap/slapd.conf
include /etc/openldap/schema/corba.schema
include /etc/openldap/schema/core.schema
include /etc/openldap/schema/cosine.schema
include /etc/openldap/schema/duaconf.schema
include /etc/openldap/schema/dyngroup.schema
include /etc/openldap/schema/inetorgperson.schema
include /etc/openldap/schema/java.schema
include /etc/openldap/schema/misc.schema
include /etc/openldap/schema/nis.schema
include /etc/openldap/schema/openldap.schema
include /etc/openldap/schema/ppolicy.schema
include /etc/openldap/schema/collective.schema
allow bind_v2
pidfile /var/run/openldap/slapd.pid
argsfile /var/run/openldap/slapd.args
TLSCACertificatePath /etc/openldap/certs
TLSCertificateFile "\"OpenLDAP Server\""
TLSCertificateKeyFile /etc/openldap/certs/password
access to *
by self write
by anonymous auth
by * read
database bdb
suffix "dc=dev,dc=com"
checkpoint 1024 15
rootdn "cn=admin,dc=dev,dc=com"
directory /var/lib/ldap
index objectClass eq,pres
index ou,cn,mail,surname,givenname eq,pres,sub
index uidNumber,gidNumber,loginShell eq,pres
index uid,memberUid eq,pres,sub
index nisMapName,nisMapEntry eq,pres,sub
rootpw {SSHA}6jZP4UfMlMfN0XKPch70R5+TiRCV+yT7
loglevel 296
cachesize 1000
checkpoint 2048 10
三.启动ldap服务
[root@dev ~]# /etc/init.d/slapd start Starting slapd: [ OK ] [root@dev ~]# ps aux |grep ldap ldap 2012 0.3 1.9 490532 19656 ? Ssl 21:13 0:00 /usr/sbin/slapd -h ldap:/// ldapi:/// -u ldap root 2018 0.0 0.0 103248 872 pts/0 S+ 21:14 0:00 grep ldap [root@dev ~]# netstat -tunlp |grep slapd tcp 0 0 0.0.0.0:389 0.0.0.0:* LISTEN 2012/slapd tcp 0 0 :::389 :::* LISTEN 2012/slapd #普通端口389,加密后的是689 #添加到开机自启动 [root@dev ~]# chkconfig slapd on #查看日志文件 [root@dev ~]# tail /var/log/ldap.log Jul 13 21:14:00 dev slapd[2011]: @(#) $OpenLDAP: slapd 2.4.39 (Oct 15 2014 09:51:43) $#012#[email protected]:/builddir/build/BUILD/openldap-2.4.39/openldap-2.4.39/build-servers/servers/slapd
查询一下ldap的内容
[root@dev ~]# ldapsearch -LLL -W -x -H ldap://dev.com -D "cn=admin,dc=dev,dc=com" -b "dc=dev,dc=com" "(uid=*)" Enter LDAP Password: ldap_bind: Invalid credentials (49) #这里报错 #解决如下,删除默认2.4的配置文件,重新生成2.3的配置文件 [root@dev ~]# rm -rf /etc/openldap/slapd.d/* [root@dev ~]# slaptest -f /etc/openldap/slapd.conf -F /etc/openldap/slapd.d/ 55a3bf76 bdb_monitor_db_open: monitoring disabled; configure monitor database to enable config file testing succeeded [ OK ] [root@dev ~]# ll /etc/openldap/slapd.d/ total 8 drwxr-x--- 3 root root 4096 Jul 13 21:39 cn=config -rw------- 1 root root 1302 Jul 13 21:39 cn=config.ldif #重启服务 [root@dev ~]# /etc/init.d/slapd restart Stopping slapd: [ OK ] Checking configuration files for slapd: [FAILED] 55a3bfd6 ldif_read_file: Permission denied for "/etc/openldap/slapd.d/cn=config.ldif" slaptest: bad configuration file! [root@dev ~]# chown -R ldap.ldap /etc/openldap/slapd.d [root@dev ~]# /etc/init.d/slapd restart Stopping slapd: [FAILED] Starting slapd: [ OK ] [root@dev ~]# netstat -tunlp |grep slapd tcp 0 0 0.0.0.0:389 0.0.0.0:* LISTEN 5906/slapd tcp 0 0 :::389 :::* LISTEN 5906/slapd #再重新查询ldap内容 [root@dev ~]# ldapsearch -LLL -W -x -H ldap://dev.com -D "cn=admin,dc=dev,dc=com" -b "dc=dev,dc=com" "(uid=*)" Enter LDAP Password: #密码是上文中的weyee No such object (32) #ldap中还没有任何数据
附上2个脚本
添加本地存在用户到目录服务
#脚本内容
[root@dev ~]# cat ldapuser.sh
###### ldapuser script start ######
# extract local users who have 500-999 digit UID
# replace "SUFFIX=***" to your own suffix
# this is an example
#!/bin/bash
SUFFIX='dc=dev,dc=com'
LDIF='ldapuser.ldif'
echo -n > $LDIF
for line in `grep "x:[5-9][0-9][0-9]:" /etc/passwd | sed -e "s/ /%/g"`
do
UID1=`echo $line | cut -d: -f1`
NAME=`echo $line | cut -d: -f5 | cut -d, -f1`
if [ ! "$NAME" ]
then
NAME=$UID1
else
NAME=`echo $NAME | sed -e "s/%/ /g"`
fi
SN=`echo $NAME | awk '{print $2}'`
if [ ! "$SN" ]
then
SN=$NAME
fi
GIVEN=`echo $NAME | awk '{print $1}'`
UID2=`echo $line | cut -d: -f3`
GID=`echo $line | cut -d: -f4`
PASS=`grep $UID1: /etc/shadow | cut -d: -f2`
SHELL=`echo $line | cut -d: -f7`
HOME=`echo $line | cut -d: -f6`
EXPIRE=`passwd -S $UID1 | awk '{print $7}'`
FLAG=`grep $UID1: /etc/shadow | cut -d: -f9`
if [ ! "$FLAG" ]
then
FLAG="0"
fi
WARN=`passwd -S $UID1 | awk '{print $6}'`
MIN=`passwd -S $UID1 | awk '{print $4}'`
MAX=`passwd -S $UID1 | awk '{print $5}'`
LAST=`grep $UID1: /etc/shadow | cut -d: -f3`
echo "dn: uid=$UID1,ou=people,$SUFFIX" >> $LDIF
echo "objectClass: inetOrgPerson" >> $LDIF
echo "objectClass: posixAccount" >> $LDIF
echo "objectClass: shadowAccount" >> $LDIF
echo "uid: $UID1" >> $LDIF
echo "sn: $SN" >> $LDIF
echo "givenName: $GIVEN" >> $LDIF
echo "cn: $NAME" >> $LDIF
echo "displayName: $NAME" >> $LDIF
echo "uidNumber: $UID2" >> $LDIF
echo "gidNumber: $GID" >> $LDIF
echo "userPassword: {crypt}$PASS" >> $LDIF
echo "gecos: $NAME" >> $LDIF
echo "loginShell: $SHELL" >> $LDIF
echo "homeDirectory: $HOME" >> $LDIF
echo "shadowExpire: $EXPIRE" >> $LDIF
echo "shadowFlag: $FLAG" >> $LDIF
echo "shadowWarning: $WARN" >> $LDIF
echo "shadowMin: $MIN" >> $LDIF
echo "shadowMax: $MAX" >> $LDIF
echo "shadowLastChange: $LAST" >> $LDIF
echo >> $LDIF
done
###### ldapuser script end ######
#使用方法
[root@dev ~]# sh ldapuser.sh
[root@dev ~]# ldapadd -x -D cn=admin,dc=dev,dc=com -W -f ldapuser.ldif
添加本地存在组到目录服务
#脚本内容
[root@dev ~]# cat ldapgroup.sh
# extract local groups who have 500-999 digit UID
# replace "SUFFIX=***" to your own suffix
# this is an example
#!/bin/bash
SUFFIX='dc=dev,dc=com'
LDIF='ldapgroup.ldif'
echo -n > $LDIF
for line in `grep "x:[5-9][0-9][0-9]:" /etc/group`
do
CN=`echo $line | cut -d: -f1`
GID=`echo $line | cut -d: -f3`
echo "dn: cn=$CN,ou=groups,$SUFFIX" >> $LDIF
echo "objectClass: posixGroup" >> $LDIF
echo "cn: $CN" >> $LDIF
echo "gidNumber: $GID" >> $LDIF
users=`echo $line | cut -d: -f4 | sed "s/,/ /g"`
for user in ${users} ; do
echo "memberUid: ${user}" >> $LDIF
done
echo >> $LDIF
done
#使用方法和前面的脚本一样
添加一个系统用户,使用脚本添加进ldap中
#创建系统用户user1,设置密码user1 [root@dev ~]# useradd user1 [root@dev ~]# passwd user1 Changing password for user user1. New password: BAD PASSWORD: it is too short BAD PASSWORD: is too simple Retype new password: passwd: all authentication tokens updated successfully.
四.安装migrationtools
[root@dev ~]# yum install migrationtools -y
编辑migrationtool的配置文件/usr/share/migrationtools/migrate_common.ph
[root@dev ~]# vim /usr/share/migrationtools/migrate_common.ph # Default DNS domain $DEFAULT_MAIL_DOMAIN = "dev.com"; # Default base $DEFAULT_BASE = "dc=dev,dc=com";
下面利用pl脚本将/etc/passwd 和/etc/shadow生成LDAP能读懂的文件格式,保存在/tmp/下
[root@dev ~]# /usr/share/migrationtools/migrate_base.pl >/tmp/base.ldif [root@dev ~]# /usr/share/migrationtools/migrate_passwd.pl /etc/passwd >/tmp/passwd.ldif [root@dev ~]# /usr/share/migrationtools/migrate_passwd.pl /etc/group >/tmp/group.ldif
下面就要把这三个文件导入到LDAP,这样LDAP的数据库里就有了我们想要的用户
#导入base [root@dev ~]# ldapadd -x -D "cn=admin,dc=dev,dc=com" -W -f /tmp/base.ldif Enter LDAP Password: adding new entry "dc=dev,dc=com" adding new entry "ou=Hosts,dc=dev,dc=com" adding new entry "ou=Rpc,dc=dev,dc=com" adding new entry "ou=Services,dc=dev,dc=com" adding new entry "nisMapName=netgroup.byuser,dc=dev,dc=com" adding new entry "ou=Mounts,dc=dev,dc=com" adding new entry "ou=Networks,dc=dev,dc=com" adding new entry "ou=People,dc=dev,dc=com" adding new entry "ou=Group,dc=dev,dc=com" adding new entry "ou=Netgroup,dc=dev,dc=com" adding new entry "ou=Protocols,dc=dev,dc=com" adding new entry "ou=Aliases,dc=dev,dc=com" adding new entry "nisMapName=netgroup.byhost,dc=dev,dc=com" #导入passwd [root@dev ~]# ldapadd -x -D "cn=admin,dc=dev,dc=com" -W -f /tmp/passwd.ldif Enter LDAP Password: adding new entry "uid=root,ou=People,dc=dev,dc=com" adding new entry "uid=bin,ou=People,dc=dev,dc=com" adding new entry "uid=daemon,ou=People,dc=dev,dc=com" adding new entry "uid=adm,ou=People,dc=dev,dc=com" adding new entry "uid=lp,ou=People,dc=dev,dc=com" adding new entry "uid=sync,ou=People,dc=dev,dc=com" adding new entry "uid=shutdown,ou=People,dc=dev,dc=com" adding new entry "uid=halt,ou=People,dc=dev,dc=com" adding new entry "uid=mail,ou=People,dc=dev,dc=com" adding new entry "uid=uucp,ou=People,dc=dev,dc=com" adding new entry "uid=operator,ou=People,dc=dev,dc=com" adding new entry "uid=games,ou=People,dc=dev,dc=com" adding new entry "uid=gopher,ou=People,dc=dev,dc=com" adding new entry "uid=ftp,ou=People,dc=dev,dc=com" adding new entry "uid=nobody,ou=People,dc=dev,dc=com" adding new entry "uid=dbus,ou=People,dc=dev,dc=com" adding new entry "uid=vcsa,ou=People,dc=dev,dc=com" adding new entry "uid=abrt,ou=People,dc=dev,dc=com" adding new entry "uid=haldaemon,ou=People,dc=dev,dc=com" adding new entry "uid=ntp,ou=People,dc=dev,dc=com" adding new entry "uid=saslauth,ou=People,dc=dev,dc=com" adding new entry "uid=postfix,ou=People,dc=dev,dc=com" adding new entry "uid=sshd,ou=People,dc=dev,dc=com" adding new entry "uid=tcpdump,ou=People,dc=dev,dc=com" adding new entry "uid=rpc,ou=People,dc=dev,dc=com" adding new entry "uid=hacluster,ou=People,dc=dev,dc=com" adding new entry "uid=rpcuser,ou=People,dc=dev,dc=com" adding new entry "uid=nfsnobody,ou=People,dc=dev,dc=com" adding new entry "uid=ldap,ou=People,dc=dev,dc=com" adding new entry "uid=nscd,ou=People,dc=dev,dc=com" adding new entry "uid=nslcd,ou=People,dc=dev,dc=com" adding new entry "uid=user1,ou=People,dc=dev,dc=com" #导入group [root@dev ~]# ldapadd -x -D "cn=admin,dc=dev,dc=com" -W -f /tmp/group.ldif
再次查询ldap的内容
[root@dev ~]# ldapsearch -LLL -W -x -H ldap://dev.com -D "cn=admin,dc=dev,dc=com" -b "dc=dev,dc=com" "(uid=user1)" Enter LDAP Password: dn: uid=user1,ou=People,dc=dev,dc=com uid: user1 #这里我们只查询user1 cn: user1 objectClass: account objectClass: posixAccount objectClass: top objectClass: shadowAccount userPassword:: e2NyeXB0fSQxJC5CTHJNWDJEJE9FYnNMc2N4S3NQQ2liLk5uVC5ZMTA= shadowLastChange: 16629 shadowMin: 0 shadowMax: 99999 shadowWarning: 7 loginShell: /bin/bash uidNumber: 500 gidNumber: 500 homeDirectory: /home/user1 #不用输入密码查询 [root@dev ~]# ldapsearch -LLL -w weyee -x -H ldap://dev.com -D "cn=admin,dc=dev,dc=com" -b "dc=dev,dc=com" "(uid=user1)" dn: uid=user1,ou=People,dc=dev,dc=com uid: user1 cn: user1 objectClass: account objectClass: posixAccount objectClass: top objectClass: shadowAccount userPassword:: e2NyeXB0fSQxJC5CTHJNWDJEJE9FYnNMc2N4S3NQQ2liLk5uVC5ZMTA= shadowLastChange: 16629 shadowMin: 0 shadowMax: 99999 shadowWarning: 7 loginShell: /bin/bash uidNumber: 500 gidNumber: 500 homeDirectory: /home/user1
备份ldap数据
[root@dev ~]# ldapsearch -LLL -w weyee -x -H ldap://dev.com -D "cn=admin,dc=dev,dc=com" -b "dc=dev,dc=com" >ldap.bak
五.安装配置ldap客户端ldap-account-manager
#安装软件包 [root@dev ~]# yum install httpd php php-ldap php-gd -y #下载软件包 [root@dev ~]# wget http://downloads.sourceforge.net/project/lam/LAM/3.7/ldap-account-manager-3.7.tar.gz?r=&ts=1436962983&use_mirror=ncu [root@dev ~]# tar xf ldap-account-manager-3.7.tar.gz [root@dev ~]# cd /var/www/html/ [root@dev html]# cp -r ~/ldap-account-manager-3.7 . [root@dev html]# mv ldap-account-manager-3.7 ldap [root@dev html]# cd ldap/config [root@dev config]# cp config.cfg_sample config.cfg [root@dev config]# cp lam.conf_sample lam.conf [root@dev config]# sed -i 's#cn=Manager#cn=admin#g' lam.conf [root@dev config]# sed -i 's#dc=my-domain#dc=dev#g' lam.conf [root@dev config]# chown -R apache.apache /var/www/html/ldap [root@dev config]# /etc/init.d/httpd start Starting httpd: [ OK ]
访问web界面http://192.168.1.13/ldap

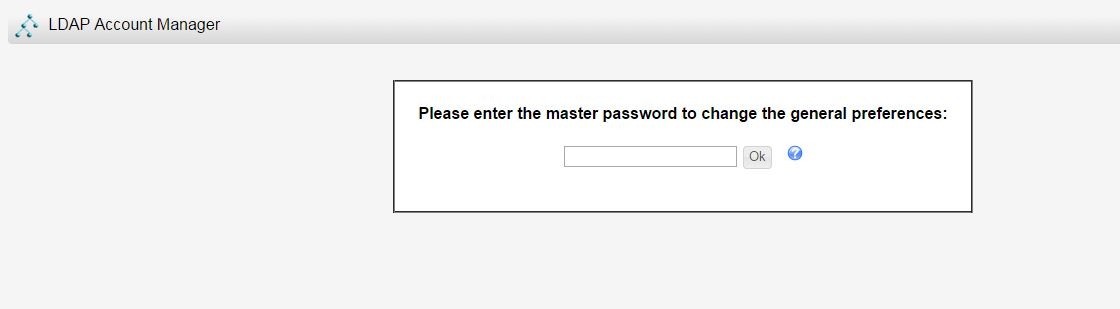
出现这个界面后需要先配置,点击lam configuration,默认密码是lam
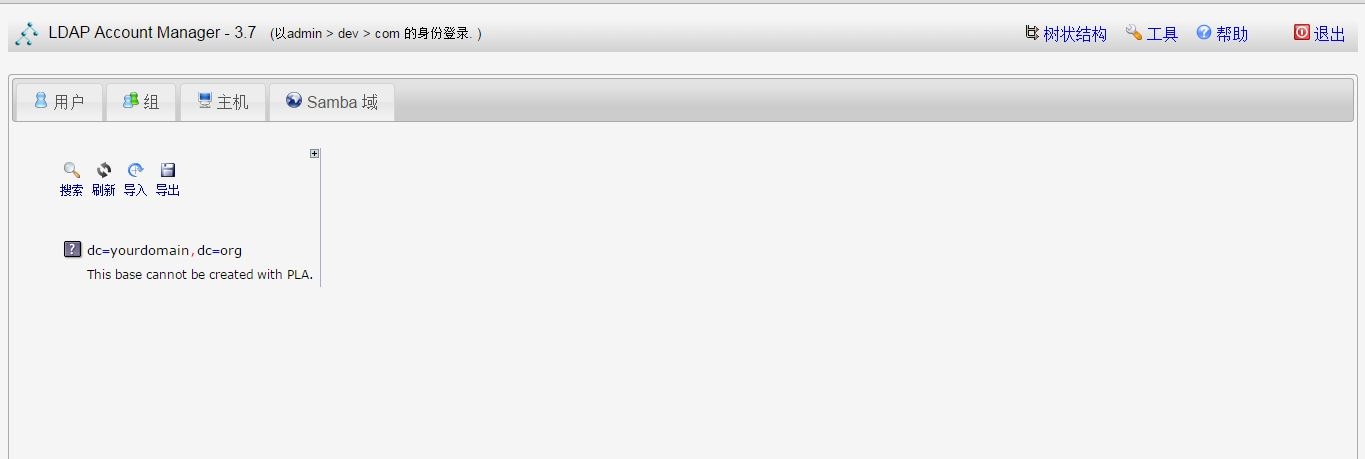
登陆后的界面如下
创建一个新用户www
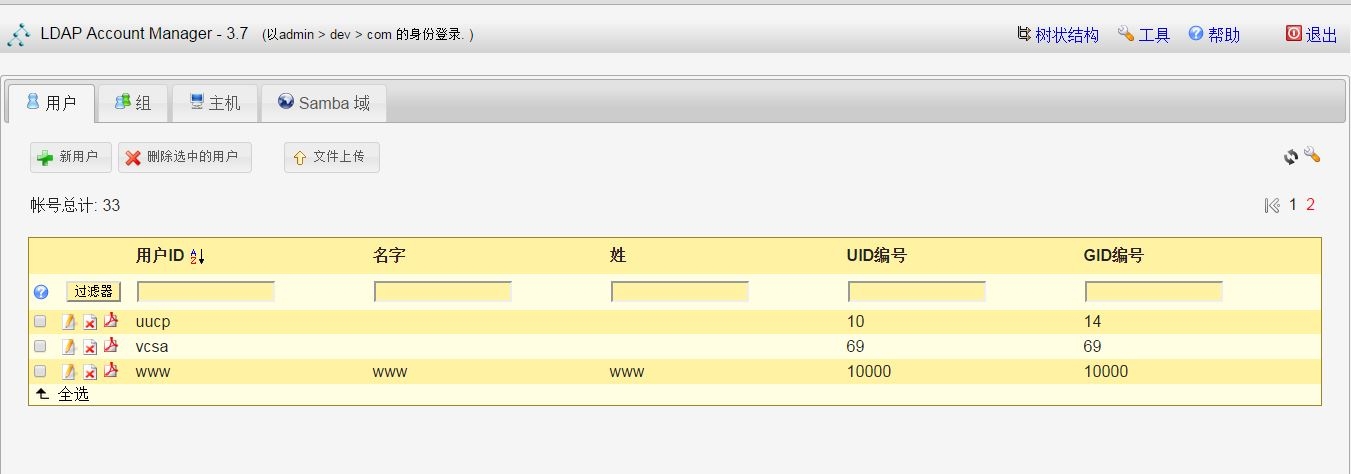
在系统中查询刚才添加的结果
[root@dev ~]# ldapsearch -LLL -w weyee -x -H ldap://192.168.1.13 -D "cn=admin,dc=dev,dc=com" -b "dc=dev,dc=com" "(uid=www)" dn: uid=www,ou=People,dc=dev,dc=com objectClass: posixAccount objectClass: inetOrgPerson objectClass: organizationalPerson objectClass: person homeDirectory: /home/wwww loginShell: /bin/bash cn: www www uidNumber: 10000 gidNumber: 10000 userPassword:: e1NTSEF9K2VUTGdMYmo3WWZ3K25kQlRZNnlRaks5MHVWQUtXK3I= sn: www givenName: www uid: www
六、配置svn+sasl通过ldap进行身份认证(独立的svn服务)
#安装sasl [root@dev ~]# yum install *sasl* -y #查看sasl的认证机制 [root@dev ~]# saslauthd -v saslauthd 2.1.23 authentication mechanisms: getpwent kerberos5 pam rimap shadow ldap #默认的认证方式如下 #忽略大小写查询 [root@dev ~]# grep -i mech /etc/sysconfig/saslauthd # Mechanism to use when checking passwords. Run "saslauthd -v" to get a list # of which mechanism your installation was compiled with the ablity to use. MECH=pam # Options sent to the saslauthd. If the MECH is other than "pam" uncomment the next line. #将认证方式改成shadow测试一下 [root@dev ~]# sed -i 's#MECH=pam#MECH=shadow#g' /etc/sysconfig/saslauthd [root@dev ~]# grep -i mech /etc/sysconfig/saslauthd # Mechanism to use when checking passwords. Run "saslauthd -v" to get a list # of which mechanism your installation was compiled with the ablity to use. MECH=shadow # Options sent to the saslauthd. If the MECH is other than "pam" uncomment the next line. #重启sasl服务 [root@dev ~]# /etc/init.d/saslauthd restart Stopping saslauthd: [FAILED] Starting saslauthd: [ OK ] [root@dev ~]# ps aux |grep sasl root 1848 0.0 0.0 66376 1000 ? Ss 21:12 0:00 /usr/sbin/saslauthd -m /var/run/saslauthd -a shadow root 1850 0.0 0.0 66376 688 ? S 21:12 0:00 /usr/sbin/saslauthd -m /var/run/saslauthd -a shadow root 1851 0.0 0.0 66376 688 ? S 21:12 0:00 /usr/sbin/saslauthd -m /var/run/saslauthd -a shadow root 1852 0.0 0.0 66376 688 ? S 21:12 0:00 /usr/sbin/saslauthd -m /var/run/saslauthd -a shadow root 1853 0.0 0.0 66376 688 ? S 21:12 0:00 /usr/sbin/saslauthd -m /var/run/saslauthd -a shadow root 1858 0.0 0.0 103248 836 pts/0 S+ 21:13 0:00 grep sasl #使用本地系统账号进行测试 [root@dev ~]# testsaslauthd -uroot -p123123 0: OK "Success." #测试成功 #配置通过ldap进行认证,修改sasl的认证方式 [root@dev ~]# sed -i 's#MECH=shadow#MECH=ldap#g' /etc/sysconfig/saslauthd [root@dev ~]# grep MECH /etc/sysconfig/saslauthd MECH=ldap [root@dev ~]# /etc/init.d/saslauthd restart Stopping saslauthd: [ OK ] Starting saslauthd: [ OK ] #创建sasl认证配置文件 [root@dev ~]# cat /etc/saslauthd.conf ldap_servers: ldap://192.168.1.13/ ldap_bind_dn: cn=admin,dc=dev,dc=com ldap_bind_pw: weyee ldap_search_base: ou=People,dc=dev,dc=com ldap_filter: uid=%U ldap_password_attr: userPassword #用户www只在ldap中有 [root@dev ~]# id www id: www: No such user [root@dev ~]# ldapsearch -LLL -w weyee -x -H ldap://192.168.1.13 -D "cn=admin,dc=dev,dc=com" -b "dc=dev,dc=com" "(uid=www)" dn: uid=www,ou=People,dc=dev,dc=com objectClass: posixAccount objectClass: inetOrgPerson objectClass: organizationalPerson objectClass: person homeDirectory: /home/wwww loginShell: /bin/bash cn: www www uidNumber: 10000 gidNumber: 10000 userPassword:: e1NTSEF9K2VUTGdMYmo3WWZ3K25kQlRZNnlRaks5MHVWQUtXK3I= sn: www givenName: www uid: www #从上面的结果中能看出www是ldap中的用户 #测试 [root@dev ~]# testsaslauthd -uwww -pwww 0: OK "Success." #测试成功
安装配置svn
[root@dev ~]# yum install subversion -y #创建相关目录 [root@dev ~]# mkdir -p /data/svndata [root@dev ~]# mkdir -p /data/svnpasswd #启动svn [root@dev ~]# svnserve -d -r /data/svndata/ [root@dev ~]# netstat -tunlp|grep svn tcp 0 0 0.0.0.0:3690 0.0.0.0:* LISTEN 2259/svnserve #创建项目 [root@dev ~]# svnadmin create /data/svndata/sadoc [root@dev ~]# cd /data/svndata/sadoc/ [root@dev sadoc]# cd conf/ [root@dev conf]# cp svnserve.conf svnserve.conf_`date +%Y%m%d`.bak [root@dev conf]# sed -i 's/#auth-access=write/auth-access=write/' svnserve.conf #修改后的配置文件内容如下 [root@dev conf]# egrep -v "^$|^#" svnserve.conf [general] anon-access = none auth-access=write password-db = /data/svnpasswd/passwd authz-db = /data/svnpasswd/authz [sasl] #复制权限配置文件 [root@dev conf]# pwd /data/svndata/sadoc/conf [root@dev conf]# cp authz passwd /data/svnpasswd/ [root@dev conf]# chmod 700 /data/svnpasswd/ [root@dev conf]# pkill svnserve [root@dev conf]# ps aux |grep svn root 2293 0.0 0.0 103248 848 pts/0 S+ 21:56 0:00 grep svn #配置svn通过ldap认证 #创建认证配置文件 [root@dev ~]# cat /etc/sasl2/svn.conf pwcheck_method: saslauthd mech_list: PLAIN LOGIN #重启sasl服务 [root@dev ~]# /etc/init.d/saslauthd restart Stopping saslauthd: [ OK ] Starting saslauthd: [ OK ] [root@dev ~]# testsaslauthd -uwww -pwww 0: OK "Success." #更改svn配置文件sasl参数 [root@dev ~]# cd /data/svndata/sadoc/ [root@dev sadoc]# cd conf/ [root@dev conf]# cp svnserve.conf svnserve.conf_`date +%Y%m%d`.bak [root@dev conf]# egrep -v "^#|^$" svnserve.conf [general] anon-access = none auth-access=write password-db = /data/svnpasswd/passwd authz-db = /data/svnpasswd/authz [sasl] use-sasl = true #开启认证 [root@dev ~]# pkill svnserve [root@dev ~]# svnserve -d -r /data/svndata/ #在authz文件中赋予权限 [root@dev ~]# egrep -v "^$|^#" /data/svnpasswd/authz [aliases] [groups] admin = www [sadoc:/] @admin = rw #测试 [root@dev ~]# id www id: www: No such user [root@dev ~]# ldapsearch -LLL -w weyee -x -H ldap://192.168.1.13 -D "cn=admin,dc=dev,dc=com" -b "dc=dev,dc=com" "(uid=www)" dn: uid=www,ou=People,dc=dev,dc=com objectClass: posixAccount objectClass: inetOrgPerson objectClass: organizationalPerson objectClass: person homeDirectory: /home/wwww loginShell: /bin/bash cn: www www uidNumber: 10000 gidNumber: 10000 userPassword:: e1NTSEF9K2VUTGdMYmo3WWZ3K25kQlRZNnlRaks5MHVWQUtXK3I= sn: www givenName: www uid: www #访问svn服务器 [root@dev ~]# svn co svn://192.168.1.13/sadoc /tmp --username=www --password=www ----------------------------------------------------------------------- ATTENTION! Your password for authentication realm: <svn://192.168.1.13:3690> d3eed2b4-64de-4aec-836a-39bc34d3d957 can only be stored to disk unencrypted! You are advised to configure your system so that Subversion can store passwords encrypted, if possible. See the documentation for details. You can avoid future appearances of this warning by setting the value of the 'store-plaintext-passwords' option to either 'yes' or 'no' in '/root/.subversion/servers'. ----------------------------------------------------------------------- Store password unencrypted (yes/no)? yes Checked out revision 0. #结果显示能通过ldap认证正常访问svn服务器 #我们在ldap中添加一个用户ldapsvn,密码是ldapsvn再次认证一次 [root@dev ~]# id ldapsvn id: ldapsvn: No such user [root@dev ~]# ldapsearch -LLL -w weyee -x -H ldap://192.168.1.13 -D "cn=admin,dc=dev,dc=com" -b "dc=dev,dc=com" "(uid=ldapsvn)" dn: uid=ldapsvn,ou=People,dc=dev,dc=com objectClass: posixAccount objectClass: inetOrgPerson objectClass: organizationalPerson objectClass: person homeDirectory: /home/ldapsvn loginShell: /bin/bash uid: ldapsvn cn: ldapsvn ldapsvn userPassword:: e1NTSEF9Zno4TjZBZ2FwWWo3NUY3ZGl5ZU5uKzJyd0lQVlVHUlc= uidNumber: 10001 gidNumber: 10000 sn: ldapsvn givenName: ldapsvn #将ldapsvn添加到authz文件中,过程略 [root@dev ~]# svn co svn://192.168.1.13/sadoc /tmp/test/ --username=ldapsvn --password=ldapsvn ----------------------------------------------------------------------- ATTENTION! Your password for authentication realm: <svn://192.168.1.13:3690> d3eed2b4-64de-4aec-836a-39bc34d3d957 can only be stored to disk unencrypted! You are advised to configure your system so that Subversion can store passwords encrypted, if possible. See the documentation for details. You can avoid future appearances of this warning by setting the value of the 'store-plaintext-passwords' option to either 'yes' or 'no' in '/root/.subversion/servers'. ----------------------------------------------------------------------- Store password unencrypted (yes/no)? yes Checked out revision 0. #到此svn+ldap认证配置过程结束