幽灵漏洞的补救措施
近期幽灵漏洞正在疯狂传播着,希望在下的文章能帮助到大家
vim GHOST.c
#include <netdb.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <errno.h>
#include <gnu/libc-version.h>
#define CANARY "in_the_coal_mine"
struct {
char buffer[1024];
char canary[sizeof(CANARY)];
} temp = { "buffer", CANARY };
int main(void) {
struct hostent resbuf;
struct hostent *result;
int herrno;
int retval;
/*** strlen (name) = size_needed - sizeof (*host_addr) - sizeof (*h_addr_ptrs) - 1; ***/
size_t len = sizeof(temp.buffer) - 16*sizeof(unsigned char) - 2*sizeof(char *) - 1;
char name[sizeof(temp.buffer)];
memset(name, '0', len);
name[len] = '\0';
retval = gethostbyname_r(name, &resbuf, temp.buffer, sizeof(temp.buffer), &result, &herrno);
if (strcmp(temp.canary, CANARY) != 0) {
puts("vulnerable");
exit(EXIT_SUCCESS);
}
if (retval == ERANGE) {
puts("not vulnerable");
exit(EXIT_SUCCESS);
}
puts("should not happen");
exit(EXIT_FAILURE);
}
运行 gcc GHOST.c -o GHOST
./GHOST
如果显示
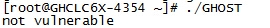
标识没有漏洞,如果相反表示存在漏洞
如果不想使用上面的检测脚本,可以去csdn下载我上传的redhat的官方的检测脚本
http://download.csdn.net/detail/xinsir88/8407621
更新办法:
Centos系统
yum clean all && yum makecache && yum -y install glibc*
关于ubunt系统的补救措施我没有测试,此处不做阐述