openssl建立CA中心
openssl建立CA中心
实验用了三台机:
CA中心:server1.example.com(192.168.10.254)
mail server: station20.example.com(192.168.10.20)
mail client: station19.example.com(192.168.10.19)
实验基于Red Hat Enterprise Linux server 5 update 4版
一.CA中心(server1.example.com:192.168.10.254)的设置
[root@server1 tls]# pwd
/etc/pki/tls
[root@server1 tls]# ls
cert.pem certs misc openssl.cnf private
[root@server1 tls]# rpm -qa |grep openssl
openssl-0.9.8e-12.el5
##linux下的ssl是由openssl提供的。
--------------->开始配置openssl.cnf
[root@server1 tls]#vim openssl.cnf
[ CA_default ]
dir = /etc/pki/CA #CA存放的路径
certs = $dir/certs #存放签名的公钥
crl_dir = $dir/crl # 证书过期列表,存放过期证书
database = $dir/index.txt # 证书颁发、吊销的信息
new_certs_dir = $dir/newcerts # 证书副本(吊销凭证)
certificate = $dir/my-ca.crt #CA公钥(任何人都可以拥有的)
serial = $dir/serial # 序列号(每作一次签名,序列号就增加1)
crlnumber = $dir/crlnumber #吊销序列号
crl = $dir/my-ca.crl #吊销证书名单列表
private_key = $dir/private/my-ca.key# The private key
RANDFILE = $dir/private/.rand # private random number file
x509_extensions = usr_cert # The extentions to add to the cert
default_days = 365 # 证书有效期
default_crl_days= 30 #crl更新时间
default_md = sha1 # which md to use.
preserve = no # keep passed DN ordering
[ policy_match ]
countryName = match #国家代码必须完全匹配
stateOrProvinceName = match #
organizationName = match
organizationalUnitName = optional #optional可以不一样
commonName = supplied #代表唯一身份,必须不匹配
emailAddress = optional
[ req_distinguished_name ]
countryName = Country Name (2 letter code)
countryName_default = CN #国家代码
countryName_min = 2
countryName_max = 2
stateOrProvinceName = State or Province Name (full name)
stateOrProvinceName_default = Hubei #洲或省
localityName = Locality Name (eg, city)
localityName_default = Wuhan #城市
0.organizationName = Organization Name (eg, company)
0.organizationName_default = Example, Inc. #组织
##openssl.cnf配置完成
[root@server1 tls]# cd ../CA/
[root@server1 CA]# ls
private
[root@server1 CA]# mkdir {certs,newcerts,crl} #创建刚才定义的那几个目录
[root@server1 CA]# ls
certs crl newcerts private
[root@server1 CA]# echo 00 > serial ;touch index.txt #分配一个开始序列号并创建index.txt
[root@server1 CA]# echo 00 >crlnumber #同上
------------->开始生成CA中心自己的私钥
[root@server1 CA]#(umask 077; openssl genrsa –out private/my-ca.key –des3 2048 )
Generating RSA private key, 2048 bit long modulus
..................+++
.........................................................................................................................................+++
e is 65537 (0x10001)
Enter pass phrase for private/my-ca.key:redhat #输入私钥密码
Verifying - Enter pass phrase for private/my-ca.key:redhat #确认输入
-------------->通过私钥来生成公钥:
[root@server1 CA]# openssl req -new -x509 -key private/my-ca.key -days 365 > my-ca.crt
Enter pass phrase for private/my-ca.key:
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [CN]:
State or Province Name (full name) [Hubei]:
Locality Name (eg, city) [Wuhan]:
Organization Name (eg, company) [Example, Inc.]:
Organizational Unit Name (eg, section) []:
Common Name (eg, your name or your server's hostname) []:server1.example.com
Email Address []:
##CA中心已经搭完了,,
下面开始用服务来验证
用一台机搭建mail服务器(station20.example.com:192.168.10.20)
[root@station20 ~]# yum install –y dovecot postfix system-switch-mail
[root@station20 ~]#vim /etc/postfix/main.cf
inet_interfaces = all
[root@station20 ~]# vim /etc/dovecot.conf
protocols = imaps pop3s
[root@station20 ~]#service postfix restart
[root@station20 ~]#service dovecot restart
-------------->生成私钥
[root@station20 ~]# openssl genrsa 1024 > station20.key
Generating RSA private key, 1024 bit long modulus
.........................++++++
..............++++++
e is 65537 (0x10001)
[root@station20 ~]# ls
anaconda-ks.cfg Desktop install.log install.log.syslog station20.key
--------------->通过私钥生成一个证书请求文件.
[root@station20 ~]# openssl req -new -key station20.key -out dovecot.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [GB]:CN
State or Province Name (full name) [Berkshire]:Hubei
Locality Name (eg, city) [Newbury]:Wuhan
Organization Name (eg, company) [My Company Ltd]:Example, Inc.
Organizational Unit Name (eg, section) []: ###以上填写均要跟CA中心的一致
Common Name (eg, your name or your server's hostname) []:station20.example.com
Email Address []:
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
---------------->把证书请求文件发给CA中心
[root@station20 ~]# scp dovecot.csr 192.168.10.254:/root
[email protected]'s password:
dovecot.csr 100% 647 0.6KB/s 00:00
--------------->CA中心签名[注意:现在在CA中心(server1.example.com:192.168.10.254)操作了]
[root@server1 ~]# openssl ca -in dovecot.csr -out dovecot.crt
Using configuration from /etc/pki/tls/openssl.cnf
Enter pass phrase for /etc/pki/CA/private/my-ca.key:
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 0 (0x0)
Validity
Not Before: Sep 3 12:06:36 2010 GMT
Not After : Sep 3 12:06:36 2011 GMT
Subject:
countryName = CN
stateOrProvinceName = Hubei
organizationName = Example, Inc.
commonName = station20.example.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
C8:F2:8B:F3:21:E4:AD:65:FC:C6:2A:E2:AB:26:8A:8D:57:A2:3A:84
X509v3 Authority Key Identifier:
keyid:5D:81:EC:7B:76:E0:9E:34:A9:99:05:0F:23:91:B9:EB:64:A6:37:05
Certificate is to be certified until Sep 3 12:06:36 2011 GMT (365 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
-------------->生成后传回给mailserver(station20.example.com:192.168.10.20)
[root@server1 ~]# cp /etc/pki/CA/my-ca.crt pub/
[root@server1 ~]# cp dovecot.crt pub/
[root@server1 ~]# cd pub/
[root@server1 pub]# ls
dovecot.crt my-ca.crt
[root@server1 pub]# scp * 192.168.10.20:/root
[email protected]'s password:
dovecot.crt 100% 3699 3.6KB/s 00:00
my-ca.crt 100% 1472 1.4KB/s 00:00
-------------->设置/etc/dovecot.conf
[root@station20 ~]# ls
anaconda-ks.cfg dovecot.crt install.log my-ca.crt
Desktop dovecot.csr install.log.syslog station20.key
[root@station20 ~]# cp station20.key /etc/pki/tls/private/dovecot.pem #公钥
[root@station20 ~]# cp dovecot.crt /etc/pki/tls/certs/dovecot.pem #私钥
[root@station20 ~]# vim /etc/dovecot.conf
ssl_cert_file = /etc/pki/tls/certs/dovecot.pem
ssl_key_file = /etc/pki/tls/private/dovecot.pem
下面客户端(station19.example.com:192.168.10.19)开始验证
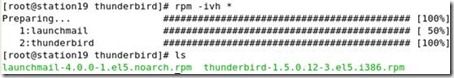
---------------à安装雷鸟.(当然条件好的话咱可以使用win下的outlook或foxmail)

新建一个账号

使用pop3,等下还要修改为pop3s的

其他的猛电击下一步就可以了
然后再设置为995的pop3s

因为CA公钥是权威机构,所以mail client 需要导入CA权威公钥,现在我从mail server 传送CA公钥给mail client.
[root@station20 ~]# scp my-ca.crt 192.168.10.19:/root/
[email protected]'s password:
my-ca.crt 100% 1472 1.4KB/s 00:00
我们可以先试着接收一下邮件看效果先

看吧,告诉我这是一个不受信任的证书,问you要不要信任,信不信由你, 这个在实际环境挺险的,所以我要做下一步,把咱的权威CA导入到信任列表中,成为受信任的权威合法机构.
雷鸟导入CA证书

点import导入
点啥都信它.

查看一下证书列表,看到了我们搭的CA中心了
![]()
再收邮件看看还有没有那个不受信任的效果呢/
直接提示输入密码

最后啥提示都没有,全亮绿灯,实验基本成功

二.再香的饽饽也有过期的时候,下面做一下CA中心测试吊销证书的实验
------------>生成吊销证书
[root@server1 newcerts]# pwd
/etc/pki/CA/newcerts
[root@server1 newcerts]# openssl ca -revoke 00.pem
Using configuration from /etc/pki/tls/openssl.cnf
Enter pass phrase for /etc/pki/CA/private/my-ca.key:
Revoking Certificate 00.
Data Base Updated
[root@server1 newcerts]# ls
00.pem
---------------->生成过期列表.
[root@server1 CA]# openssl ca -gencrl -out /etc/pki/CA/crl/my-ca.crl
Using configuration from /etc/pki/tls/openssl.cnf
Enter pass phrase for /etc/pki/CA/private/my-ca.key:
由于firefox与thunderbird不支持此格式,需要转换,一般别的不需要此步
[root@server1 crl]# openssl crl -in my-ca.crl -outform DER -out my-ca-der.crl
[root@server1 crl]# ls
my-ca.crl my-ca-der.crl
顺便搭个httpserver让别人能下载得到过期列表
[root@server1 crl]# yum install -y httpd
[root@server1 crl]# service httpd restart
[root@server1 crl]# mkdir /var/www/html/certs
[root@server1 crl]# cp my-ca-der.crl /var/www/html/certs/
客户端导入过期列表.

当再接收邮件时,将不可用了1!

CA的研究先到这里了,俺是新手,欢迎学习!