虚拟机插入 Centos 7 Min .ISO 光盘
进入到安装选 项 按tab键
添加 inst.ks=http://dl.efa-project.org/build/4/kstesting.cfg
按Enter 自动安装,网络安装 大概需要下载500MB左右的文件 需要等60分钟左右
安装完成
安装配置
修改网卡
vi /etc/sysconfig/network-scripts/ifcfg-ens160
你不会在eFa上使用智能主机,而是建立eFa作为出站中继。
EFA配置选项7)邮件设置 - >选项1)出站邮件中继
EFA配置选项7“出站智能主机”(7,2)“智能主机:已禁用”,因为您希望EFA直接发送邮件
EFA配置选项7“传输设置” “(7,4)as”domain.com“”<您的交换服务器的内部IP地址“
EFA配置选项8“垃圾邮件设置” “(8,1)非垃圾邮件设置
垃圾邮件设置>非垃圾邮件设置
- 禁用存储非垃圾邮件:否(这允许培训误报以及最近的存档/恢复)。
禁用非垃圾邮件签名:是(此设置取决于您是否需要EFA水印,我禁用它,因为我们(IT管理员)管理垃圾邮件而不是用户。此外,我们的大多数(99%)用户都是外部的将全民教育暴露在互联网上。)
- EFA配置选项9“垃圾邮件设置” “(8,2)圾邮件设置
- 推荐:垃圾邮件设置>垃圾邮件设置。启用垃圾邮件传递:是的。(这与后面提到的其他规则相结合,允许可疑垃圾邮件进入用户的垃圾邮件文件夹。
EFA V4与Active Directory集成
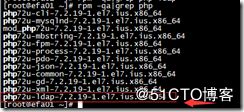
请安装 php-ldap (rpm -qa|grep php)
yum install lrzsz -y
vi /var/www/html/mailscanner/conf.php(编辑后重启系统 需要开启apache https)
// LDAP settings for authentication
define('USE_LDAP', true);
define('LDAP_SSL', false);
define('LDAP_HOST', '192.168.32.83');
define('LDAP_PORT', '389');
define('LDAP_DN', 'OU=email,DC=test,DC=xyz');
define('LDAP_USER', '[email protected]');
define('LDAP_PASS', '123456');
define('LDAP_SITE', 'Default-First-Site-Name');
define('LDAP_FILTER', 'proxyAddresses=smtp:%s', 'mail=%s');
define('LDAP_PROTOCOL_VERSION', 3);
define('LDAP_EMAIL_FIELD', 'mail');
define('LDAP_USERNAME_FIELD', 'cn');
define('LDAP_MS_AD_COMPATIBILITY', true);
vi /etc/hosts (添加exchange服务器IP和域名)
192.168.32.83 mail.test.xyz
设置垃圾邮件不修改主题
vi /etc/MailScanner/MailScanner.conf
Spam Subject Text =
/etc/init.d/spamassassin restart
exchange 设置垃圾邮件过滤
添加规则
New-TransportRule -Name "EFA to Junk Folder" -HeaderMatchesMessageHeader "X-Spam-Status" -HeaderMatchesPatterns "Yes" -SetSCL 9 -Comments "This rule moves spam messages from the EFA filter to the users junk mail folder."
步骤 2:使用命令行管理程序重新启动 Microsoft Exchange 传输服务
运行命令:Restart-Service MSExchangeTransport
重启服务
service sqlgrey restart
service spamassassin restart
service webmin restart
service clamd restart
service MailScanner restart
service postfix restart
MailScanner --lint
spamassassin -D --lint (重新加载规则)
安装fail2ban 自动拦截邮件***
yum install fail2ban –y
# vi /etc/fail2ban/jail.conf
最后一行添加如下:
[postfix]
enabled = true
filter = postfix
action = iptables-allports[name=postfix, port=25, protocol=tcp]
ignoreip = 127.0.0.1
logpath = /var/log/maillog
bantime = 6048000
findtime = 120
maxretry = 3
[postfix-ddos]
enabled = true
filter = postfix-ddos
action = iptables-allports[name=MAIL, protocol=all]
logpath = /var/log/maillog
maxretry = 2
findtime = 86400
bantime = 604800
/etc/fail2ban/filter.d中编辑或新加文件,文件名一定要跟上一步jail.conf配置文件中的“filter=”对应
POSTFIX
vi /etc/fail2ban/filter.d/postfix.conf
# Fail2Ban configuration file
#
# Author: Cyril Jaquier
#
# $Revision: 510 $
#
[Definition]
# Option: failregex
# Notes.: regex to match the password failures messages in the logfile. The
# host must be matched by a group named "host". The tag "
# be used for standard IP/hostname matching and is only an alias for
# (?:::f{4,6}:)?(?P
# Values: TEXT
#
failregex = warning: (.*)\[
reject: RCPT from (.*)\[
reject: RCPT from (.*)\[
reject: RCPT from (.*)\[
reject: RCPT from (.*)\[
reject: RCPT from (.*)\[
reject: RCPT from (.*)\[
reject: RCPT from (.*)\[
reject: RCPT from (.*)\[
# Option: ignoreregex
# Notes.: regex to ignore. If this regex matches, the line is ignored.
# Values: TEXT
#
ignoreregex =
--------------------------------------------------------------------------------------------------------------
vi /etc/fail2ban/filter.d/postfix-ddos.conf
# Fail2Ban filter for Postfix DDOS attacks # [INCLUDES] before = common.conf [Definition] _daemon = postfix/(submission/)?smtp(d|s) failregex = ^%(__prefix_line)sNOQUEUE: reject: RCPT from \S+\[
启动fail2ban
systemctl start fail2ban
查看拦截fail2ban
fail2ban-client status postfix
CentOS7版本后防火墙默认使用firewalld
systemctl start firewalld
yum install -y iptables-services
service iptables start
vi /etc/sysconfig/iptables
-A INPUT -p tcp -m state --state NEW -m tcp --dport 80 -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 587 -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 22 -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 25 -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 10000 -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 443 -j ACCEPT
测试邮件内容过滤
发送测试邮件的文本内容如下:
XJS*C4JDBQADN1.NSBN3*2IDNEN*GTUBE-STANDARD-ANTI-UBE-TEST-EMAIL*C.34X
测试反病毒邮件
发送测试邮件的文本内容如下:
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
关闭MailScanner 对邮件内容扫描签名
vi /etc/MailScanner/MailScanner.conf
Dangerous Content Scanning = no
对发送的邮件进行签名
vi /etc/Mailscanner/Mailscanner.conf
Sign Clean Messages = no
这个选项默认是打开的,表示MailScanner对邮件内容进行扫描,但是过于严格了,会把很多html邮件滤掉,所以我把它关了。
systemctl restart mailscanner.service
Virus Scanners = clamd
设置杀毒软件,如果使用clamav,则Virus Scanners = clamav。
vi /etc/MailScanner/MailScanner.conf
在2242行
Required SpamAssassin Score = 4
(高评分垃圾邮件投递)
High Scoring Spam Actions = deliver header "X-Spam-Status:Yes"
systemctl restart mailscanner.service