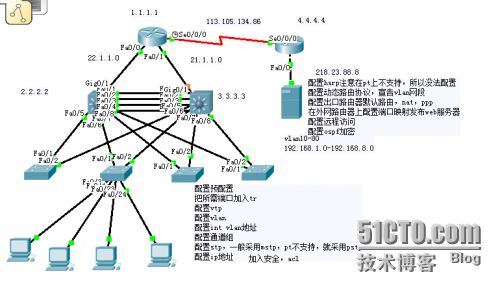
4)配置ospf协议
Conf t
router ospf 1
router-id 2.2.2.2
log-adjacency-changes
network 22.1.1.2 0.0.0.0 area 0
network 2.2.2.2 0.0.0.0 area 0
network 192.168.1.2 0.0.0.0 area 0
network 192.168.2.2 0.0.0.0 area 0
network 192.168.3.2 0.0.0.0 area 0
network 192.168.4.2 0.0.0.0 area 0
network 192.168.5.2 0.0.0.0 area 0
network 192.168.6.2 0.0.0.0 area 0
network 192.168.7.2 0.0.0.0 area 0
network 192.168.8.2 0.0.0.0 area 0
Iou2
//把所需使用vtp协议的端口线路更改为trunk模式
en
conf t
int rang f0/1-8
sw tr en d //在pt中不需要,真实环境和iou中都要加
sw mo tr
//创建vtp并把这台交换机设为server模式
conf t
vtp dom ccie
vtp mod server
vtp pruning // //在pt中不支持这命令,真实环境和iou中都支持这样节省带宽开销
End
//创建管理地址,方便管理员管理
conf t
int vlan 100
ip add 192.168.9.2 255.255.255.0
no shut
End
//设置vtp版本密码(为了安全起见)
conf t
vtp pass lu@123
vtp ver 2
End
//创建二层组,使用以太网端口聚合技术,实现高速负载分流
conf t
int rang f0/1-4
Channel-protocol lacp
channel-g 1 mode active
end
//Mst 是pvst 的升级版,通过不同实例给vlan 做冗余备分。创建了两个实例1 2,分别将vlan10-80加入到对应实例,并设置主从,实现不同实例的冗余备份
conf t
spanning-tree mode mst //在pt中不支持mst,只能用rstp来实现了,现实生活和iou上都支持
spanning-tree mst configu
instance 1 vlan 10,20,30,40
revision 1
instance 2 vlan 50,60,70,80
revision 1
exit
spanning-tree mst 1 root primary
spanning-tree mst 2 root secondary
End
En
Conf t
Spanning-tree mode rap
spanning-tree vlan 50,60,70,80 root primary
spanning-tree vlan 10,20,30,40 root seconday
End
//为不同vlan划分网关,实现不同vlan基于三层交换机的路由互通
conf t
int vlan 10
ip add 192.168.1.3 255.255.255.0
no shut
int vlan 20
ip add 192.168.2.3 255.255.255.0
no shut
int vlan 30
ip add 192.168.3.3 255.255.255.0
no shut
int vlan 40
ip add 192.168.4.3 255.255.255.0
no shut
int vlan 50
ip add 192.168.5.3 255.255.255.0
no shut
int vlan 60
ip add 192.168.6.3 255.255.255.0
no shut
int vlan 70
ip add 192.168.7.3 255.255.255.0
no shut
int vlan 80
ip add 192.168.8.3 255.255.255.0
no shut
End
//配置hsrp实现网关高可用性,sw1是vlan10,20,30,40-的主网关,是50,60,70,80 的备用网关。
Sw2是vlan50,60,70,80的主网关,是10,20,30,40 的备网关。
注意State is Active 为主网关
State is Standby 为备网关
conf t
int vlan 10
standby 10 ip 192.168.1.1
standby 10 priority 105
standby 10 preempt
standby 10 track g0/1
end
conf t
int vlan 20
standby 20 ip 192.168.2.1
standby 20 priority 105
standby 20 preempt
standby 20 track g0/1
end
conf t
int vlan 30
standby 30 ip 192.168.3.1
standby 30 priority 105
standby 30 preempt
standby 30 track g0/1
end
conf t
int vlan 40
standby 40 ip 192.168.4.1
standby 40 priority 105
standby 40 preempt
standby 40 track g0/1
end
conf t
int vlan 50
standby 50 ip 192.168.5.1
standby 50 priority 100
standby 50 preempt
standby 50 track g0/1
end
conf t
int vlan 60
standby 60 ip 192.168.6.1
standby 60 priority 100
standby 60 preempt
standby 60 track g0/1
end
conf t
int vlan 70
standby 70 ip 192.168.7.1
standby 70 priority 100
standby 70 preempt
standby 70 track g0/1
end
conf t
int vlan 80
standby 80 ip 192.168.8.1
standby 80 priority 100
standby 80 preempt
standby 80 track g0/1
end
write
5)配置dhcp
ip dhcp excluded-address 192.168.1.1
ip dhcp excluded-address 192.168.1.2
ip dhcp excluded-address 192.168.1.3
ip dhcp pool vlan10
network 192.168.1.0 255.255.255.0
default-router 192.168.1.1
dns-server 202.96.128.86
Exit
ip dhcp excluded-address 192.168.2.1
ip dhcp excluded-address 192.168.2.2
ip dhcp excluded-address 192.168.2.3
ip dhcp pool vlan20
network 192.168.2.0 255.255.255.0
default-router 192.168.2.1
dns-server 202.96.128.86
exit
ip dhcp excluded-address 192.168.3.1
ip dhcp excluded-address 192.168.3.2
ip dhcp excluded-address 192.168.3.3
ip dhcp pool vlan30
network 192.168.3.0 255.255.255.0
default-router 192.168.3.1
dns-server 202.96.128.86
exit
ip dhcp excluded-address 192.168.4.1
ip dhcp excluded-address 192.168.4.2
ip dhcp excluded-address 192.168.4.3
ip dhcp pool vlan40
network 192.168.4.0 255.255.255.0
default-router 192.168.4.1
dns-server 202.96.128.86
exit
ip dhcp excluded-address 192.168.5.1
ip dhcp excluded-address 192.168.5.2
ip dhcp excluded-address 192.168.5.3
ip dhcp pool vlan50
network 192.168.5.0 255.255.255.0
default-router 192.168.5.1
dns-server 202.96.128.86
exit
ip dhcp excluded-address 192.168.6.1
ip dhcp excluded-address 192.168.6.2
ip dhcp excluded-address 192.168.6.3
ip dhcp pool vlan60
network 192.168.6.0 255.255.255.0
default-router 192.168.6.1
dns-server 202.96.128.86
ip dhcp excluded-address 192.168.7.1
ip dhcp excluded-address 192.168.7.2
ip dhcp excluded-address 192.168.7.3
ip dhcp pool vlan70
network 192.168.7.0 255.255.255.0
default-router 192.168.7.1
dns-server 202.96.128.86
exit
ip dhcp excluded-address 192.168.8.1
ip dhcp excluded-address 192.168.8.2
ip dhcp excluded-address 192.168.8.3
ip dhcp pool vlan80
network 192.168.8.0 255.255.255.0
default-router 192.168.8.1
dns-server 202.96.128.86
end
6)配置ospf协议
Conf t
router ospf 1
router-id 2.2.2.2
log-adjacency-changes
network 22.1.1.2 0.0.0.0 area 0
network 2.2.2.2 0.0.0.0 area 0
network 192.168.1.3 0.0.0.0 area 0
network 192.168.2.3 0.0.0.0 area 0
network 192.168.3.3 0.0.0.0 area 0
network 192.168.4.3 0.0.0.0 area 0
network 192.168.5.3 0.0.0.0 area 0
network 192.168.6.3 0.0.0.0 area 0
network 192.168.7.3 0.0.0.0 area 0
network 192.168.8.3 0.0.0.0 area 0
Iou3
conf t
int rang f0/1-2
sw tr en d
sw mo tr
end
conf t
vtp dom ccie
vtp mod c
vtp pruning
end
conf t
int vlan 100
ip add 192.168.9.3 255.255.255.0
no shut
end
conf t
vtp pass lu@123
vtp ver 2
end
write
Iou4
conf t
int rang f0/1-2
sw tr en d
sw mo tr
end
conf t
vtp dom ccie
vtp mod c
vtp pruning
end
conf t
int vlan 100
ip add 192.168.9.4 255.255.255.0
no shut
end
conf t
vtp pass lu@123
vtp ver 2
end
write
Iou5
conf t
int rang f0/1-2
sw tr en d
sw mo tr
end
conf t
vtp dom ccie
vtp mod c
vtp pruning
end
conf t
int vlan 100
ip add 192.168.9.5 255.255.255.0
no shut
end
conf t
vtp pass lu@123
vtp ver 2
end
write
Iou6
conf t
int rang f0/1-2
sw tr en d
sw mo tr
end
conf t
vtp dom ccie
vtp mod c
vtp pruning
end
conf t
int vlan 100
ip add 192.168.9.6 255.255.255.0
no shut
end
conf t
vtp pass lu@123
vtp ver 2
end
write
7)出口配置动态路由协议让全网互通,配置nat让公司内部可以上网
RI
En
Conf t
interface Loopback0
ip address 1.1.1.1 255.255.255.255
No shut
interface FastEthernet0/1
ip address 21.1.1.1 255.255.255.0
duplex full
speed auto
No shut
interface FastEthernet0/0
ip address 22.1.1.1 255.255.255.0
duplex full
speed auto
No shut
interface Serial0/0/0
ip address 113.105.134.85 255.255.255.0
clock rate 64000
No shut
End
Conf t
router ospf 1
router-id 1.1.1.1
network 21.1.1.1 0.0.0.0 area 0
network 22.1.1.1 0.0.0.0 area 0
network 113.105.134.85 0.0.0.0 area 0
network 1.1.1.1 0.0.0.0 area 0
default-information originate
End
Conf t
ip route 0.0.0.0 0.0.0.0 Serial0/0/0
配置nat
End
Conf t
En
Conf t
Int f0/0
Ip nat inside
Int f0/1
Ip nat inside
Int s0/0/0
Ip nat outside
Exit
Access-list 1 permit 192.168.1.0 0.0.0.255
Access-list 1 permit 192.168.2.0 0.0.0.255
Access-list 1 permit 192.168.3.0 0.0.0.255
Access-list 1 permit 192.168.4.0 0.0.0.255
Access-list 1 permit 192.168.5.0 0.0.0.255
Access-list 1 permit 192.168.6.0 0.0.0.255
Access-list 1 permit 192.168.7.0 0.0.0.255
Access-list 1 permit 192.168.8.0 0.0.0.255
Ip nat inside source list 1 int s0/0/0 overload
End
write
8)在出口路由器和分公司路由器上走ppp协议实现全网互通
R1配置
En
Conf t
Username r2 password cisco
Int s0/0/0
Encapsulation ppp
Ppp authentication chap
end
write
R2配置
En
Conf t
Username r1 password cisco
Int s0/0/0
Encapsulation ppp
Ppp authentication chap
End
Conf t
interface Loopback0
ip address 4.4.4.4 255.255.255.255
No shut
interface Serial0/0/0
Clock rate 64000
ip address 113.105.134.86 255.255.255.0
No shut
interface FastEthernet0/0
ip address 218.23.88.1 255.255.255.0
duplex auto
speed auto
No shut
Write
9)将公司内部接入层交换机端口加入到对应的vlan,把电脑连接上交换机,整个项目完成!
实例:将iou3当做人事办公室,配置如下
Iou3上
En
Conf t
Int rang f0/3-24
Sw mo acc
Sw acc vlan 10
End
Write
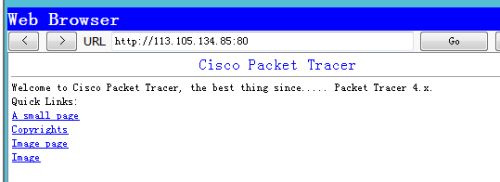
10)发布web服务器出去让外网用户能够访问到公司利用web服务器发布的消息
在出口路由器上配置
En
Conf t
Ip nat inside source static tcp 192.168.2.5 80 113.105.134.85 80
Access-list 1 permit 192.168.2.0 0.0.0.255
End
Write
验证结果如下:
11)配置acl8.0网段的用户只能访问公司ftp服务器,各vlan部分之间不能互访,但是网管1点段可以访问任意内外网方便管理,公司ftp是可以让任何人都访问到使用,web服务器除了8.0的用户其他用户都可以访问得到,公司除了8.0网段的用户,其他用户都可以访问web服务器和ftp服务器以及外网,只是不能访问到其他内部部门网段而已。
备注:真实环境和iou都是两边路由器配置一模一样,在pt中因为没有做hsrp,所以在
调用acl时候,sw1分别只调用int vlan30 -40 而在sw2上只调用50-80
access-list 100 deny ip 192.168.8.0 0.0.0.255 192.168.2.5 0.0.0.0
access-list 100 permit ip any any
Int vlan 80
ip access-group 100 in
sw1(config)#access-list 101 deny ip 192.168.3.0 0.0.0.255 192.168.4.0 0.0.0.255
sw1(config)#access-list 101 deny ip 192.168.3.0 0.0.0.255 192.168.5.0 0.0.0.255
sw1(config)#access-list 101 deny ip 192.168.3.0 0.0.0.255 192.168.6.0 0.0.0.255
sw1(config)#access-list 101 deny ip 192.168.3.0 0.0.0.255 192.168.7.0 0.0.0.255
sw1(config)#access-list 101 deny ip 192.168.3.0 0.0.0.255 192.168.8.0 0.0.0.255
sw1(config)#access-list 101 permit ip any any
sw1(config)#access-list 102 deny ip 192.168.4.0 0.0.0.255 192.168.3.0 0.0.0.255
sw1(config)#access-list 102 deny ip 192.168.4.0 0.0.0.255 192.168.5.0 0.0.0.255
sw1(config)#access-list 102 deny ip 192.168.4.0 0.0.0.255 192.168.6.0 0.0.0.255
sw1(config)#access-list 102 deny ip 192.168.4.0 0.0.0.255 192.168.7.0 0.0.0.255
sw1(config)#access-list 102 deny ip 192.168.4.0 0.0.0.255 192.168.8.0 0.0.0.255
sw1(config)#access-list 102 permit ip any any
sw1(config)#access-list 103 deny ip 192.168.5.0 0.0.0.255 192.168.4.0 0.0.0.255
sw1(config)#access-list 103 deny ip 192.168.5.0 0.0.0.255 192.168.3.0 0.0.0.255
sw1(config)#access-list 103 deny ip 192.168.5.0 0.0.0.255 192.168.6.0 0.0.0.255
sw1(config)#access-list 103 deny ip 192.168.5.0 0.0.0.255 192.168.7.0 0.0.0.255
sw1(config)#access-list 103 deny ip 192.168.5.0 0.0.0.255 192.168.8.0 0.0.0.255
sw1(config)#access-list 103 permit ip any any
sw1(config)#access-list 104 deny ip 192.168.6.0 0.0.0.255 192.168.4.0 0.0.0.255
sw1(config)#access-list 104 deny ip 192.168.6.0 0.0.0.255 192.168.5.0 0.0.0.255
sw1(config)#access-list 104 deny ip 192.168.6.0 0.0.0.255 192.168.3.0 0.0.0.255
sw1(config)#access-list 104 deny ip 192.168.6.0 0.0.0.255 192.168.7.0 0.0.0.255
sw1(config)#access-list 104 deny ip 192.168.6.0 0.0.0.255 192.168.8.0 0.0.0.255
sw1(config)#access-list 104 permit ip any any
sw1(config)#access-list 103 deny ip 192.168.7.0 0.0.0.255 192.168.4.0 0.0.0.255
sw1(config)#access-list 103 deny ip 192.168.7.0 0.0.0.255 192.168.3.0 0.0.0.255
sw1(config)#access-list 103 deny ip 192.168.7.0 0.0.0.255 192.168.6.0 0.0.0.255
sw1(config)#access-list 103 deny ip 192.168.7.0 0.0.0.255 192.168.5.0 0.0.0.255
sw1(config)#access-list 103 deny ip 192.168.7.0 0.0.0.255 192.168.8.0 0.0.0.255
sw1(config)#access-list 103 permit ip any any
sw1(config)#access-list 104 deny ip 192.168.8.0 0.0.0.255 192.168.4.0 0.0.0.255
sw1(config)#access-list 104 deny ip 192.168.8.0 0.0.0.255 192.168.5.0 0.0.0.255
sw1(config)#access-list 104 deny ip 192.168.8.0 0.0.0.255 192.168.3.0 0.0.0.255
sw1(config)#access-list 104 deny ip 192.168.8.0 0.0.0.255 192.168.7.0 0.0.0.255
sw1(config)#access-list 104 deny ip 192.168.8.0 0.0.0.255 192.168.6.0 0.0.0.255
sw1(config)#access-list 104 permit ip any any
Int vlan 20到80之间分别调用acl命令如下;因为这里需要vlan10和所有人通讯,服务器是管理员在管理,并且所有人都可以访问它,所以并没有写入acl,实际上也是这样,当然你可以精确到哪个ip地址,写法完全一样
ip access-group 101 in
ip access-group 102 in
ip access-group 103 in
ip access-group 104 in
-----------------------end---------------------------------此致为止公司内部网络就完全配置完毕,接下来等同学们学完网络安全后再配置***部分,谢谢大家的耐心听课