FreeIPA LDAP HA安装
本文通过实际案例描述如何在两个节点上安装FreeIPA的LDAP HA,参考https://www.certdepot.net/rhel7-configure-freeipa-server/及其他相关官网介绍。
实验环境
两台虚拟机-openstack-1.novalocal,openstack-2.novalocal
安装主要步骤请参考以下,
1 分别在两台机器上YUM安装ipa-server相关包
yum install -y ipa-server 2 在openstack-1上安装并启动IPA服务
(注:以下安装过程中可能会遇到错误:Apache is already configured with a listener on port 443。解决方案:修改/etc/httpd/conf.d/ssl.conf替换所有443为444)
[root@openstack-1 ~]# ipa-server-install
The log file for this installation can be found in /var/log/ipaserver-install.log
==============================================================================
This program will set up the IPA Server.
This includes:
* Configure a stand-alone CA (dogtag) for certificate management
* Configure the Network Time Daemon (ntpd)
* Create and configure an instance of Directory Server
* Create and configure a Kerberos Key Distribution Center (KDC)
* Configure Apache (httpd)
To accept the default shown in brackets, press the Enter key.
Enter the fully qualified domain name of the computer
on which you're setting up server software. Using the form
.
Example: master.example.com.
server host name [openstack-1.novalocal]:
The domain name has been determined based on the host name.
Please confirm the domain name [novalocal]:
The kerberos protocol requires a Realm name to be defined.
This is typically the domain name converted to uppercase.
Please provide a realm name [NOVALOCAL]:
Certain directory server operations require an administrative user.
This user is referred to as the Directory Manager and has full access
to the Directory for system management tasks and will be added to the
instance of directory server created for IPA.
The password must be at least 8 characters long.
Directory Manager password:
Password must be at least 8 characters long
Directory Manager password:
Password (confirm):
The IPA server requires an administrative user, named 'admin'.
This user is a regular system account used for IPA server administration.
IPA admin password:
Password (confirm):
The IPA Master Server will be configured with:
Hostname: openstack-1.novalocal
IP address: 192.168.1.93
Domain name: novalocal
Realm name: NOVALOCAL
Continue to configure the system with these values? [no]: y
The following operations may take some minutes to complete.
Please wait until the prompt is returned.
Configuring NTP daemon (ntpd)
[1/4]: stopping ntpd
[2/4]: writing configuration
[3/4]: configuring ntpd to start on boot
[4/4]: starting ntpd
Done configuring NTP daemon (ntpd).
Configuring directory server for the CA (pkids): Estimated time 30 seconds
[1/3]: creating directory server user
[2/3]: creating directory server instance
[3/3]: restarting directory server
Done configuring directory server for the CA (pkids).
Configuring certificate server (pki-cad): Estimated time 3 minutes 30 seconds
[1/21]: creating certificate server user
[2/21]: creating pki-ca instance
[3/21]: configuring certificate server instance
[4/21]: disabling nonces
[5/21]: creating CA agent PKCS#12 file in /root
[6/21]: creating RA agent certificate database
[7/21]: importing CA chain to RA certificate database
[8/21]: fixing RA database permissions
[9/21]: setting up signing cert profile
[10/21]: set up CRL publishing
[11/21]: set certificate subject base
[12/21]: enabling Subject Key Identifier
[13/21]: setting audit signing renewal to 2 years
[14/21]: configuring certificate server to start on boot
[15/21]: restarting certificate server
[16/21]: requesting RA certificate from CA
[17/21]: issuing RA agent certificate
[18/21]: adding RA agent as a trusted user
[19/21]: configure certificate renewals
[20/21]: configure Server-Cert certificate renewal
[21/21]: Configure HTTP to proxy connections
Done configuring certificate server (pki-cad).
Configuring directory server (dirsrv): Estimated time 1 minute
[1/38]: creating directory server user
[2/38]: creating directory server instance
[3/38]: adding default schema
[4/38]: enabling memberof plugin
[5/38]: enabling winsync plugin
[6/38]: configuring replication version plugin
[7/38]: enabling IPA enrollment plugin
[8/38]: enabling ldapi
[9/38]: disabling betxn plugins
[10/38]: configuring uniqueness plugin
[11/38]: configuring uuid plugin
[12/38]: configuring modrdn plugin
[13/38]: enabling entryUSN plugin
[14/38]: configuring lockout plugin
[15/38]: creating indices
[16/38]: enabling referential integrity plugin
[17/38]: configuring ssl for ds instance
[18/38]: configuring certmap.conf
[19/38]: configure autobind for root
[20/38]: configure new location for managed entries
[21/38]: restarting directory server
[22/38]: adding default layout
[23/38]: adding delegation layout
[24/38]: adding replication acis
[25/38]: creating container for managed entries
[26/38]: configuring user private groups
[27/38]: configuring netgroups from hostgroups
[28/38]: creating default Sudo bind user
[29/38]: creating default Auto Member layout
[30/38]: adding range check plugin
[31/38]: creating default HBAC rule allow_all
[32/38]: Upload CA cert to the directory
[33/38]: initializing group membership
[34/38]: adding master entry
[35/38]: configuring Posix uid/gid generation
[36/38]: enabling compatibility plugin
[37/38]: tuning directory server
[38/38]: configuring directory to start on boot
Done configuring directory server (dirsrv).
Configuring Kerberos KDC (krb5kdc): Estimated time 30 seconds
[1/10]: adding sasl mappings to the directory
[2/10]: adding kerberos container to the directory
[3/10]: configuring KDC
[4/10]: initialize kerberos container
[5/10]: adding default ACIs
[6/10]: creating a keytab for the directory
[7/10]: creating a keytab for the machine
[8/10]: adding the password extension to the directory
[9/10]: starting the KDC
[10/10]: configuring KDC to start on boot
Done configuring Kerberos KDC (krb5kdc).
Configuring kadmin
[1/2]: starting kadmin
[2/2]: configuring kadmin to start on boot
Done configuring kadmin.
Configuring ipa_memcached
[1/2]: starting ipa_memcached
[2/2]: configuring ipa_memcached to start on boot
Done configuring ipa_memcached.
Configuring the web interface (httpd): Estimated time 1 minute
[1/14]: setting mod_nss port to 443
[2/14]: setting mod_nss protocol list to TLSv1.0 - TLSv1.2
[3/14]: setting mod_nss password file
[4/14]: enabling mod_nss renegotiate
[5/14]: adding URL rewriting rules
[6/14]: configuring httpd
[7/14]: setting up ssl
[8/14]: setting up browser autoconfig
[9/14]: publish CA cert
[10/14]: creating a keytab for httpd
[11/14]: clean up any existing httpd ccache
[12/14]: configuring SELinux for httpd
[13/14]: restarting httpd
[14/14]: configuring httpd to start on boot
Done configuring the web interface (httpd).
Applying LDAP updates
Restarting the directory server
Restarting the KDC
Sample zone file for bind has been created in /tmp/sample.zone.8tNQAM.db
Restarting the web server
==============================================================================
Setup complete
Next steps:
1. You must make sure these network ports are open:
TCP Ports:
* 80, 443: HTTP/HTTPS
* 389, 636: LDAP/LDAPS
* 88, 464: kerberos
UDP Ports:
* 88, 464: kerberos
* 123: ntp
2. You can now obtain a kerberos ticket using the command: 'kinit admin'
This ticket will allow you to use the IPA tools (e.g., ipa user-add)
and the web user interface.
Be sure to back up the CA certificate stored in /root/cacert.p12
This file is required to create replicas. The password for this
file is the Directory Manager password 3 检查openstack-1上的IPA服务是否正常运行
(注:IPA相关的日志目录主要在/var/log/dirsrv、/var/log/pki-ca下面)
[root@openstack-1 ~]# ipactl status
Directory Service: RUNNING
KDC Service: RUNNING
KPASSWD Service: RUNNING
MEMCACHE Service: RUNNING
HTTP Service: RUNNING
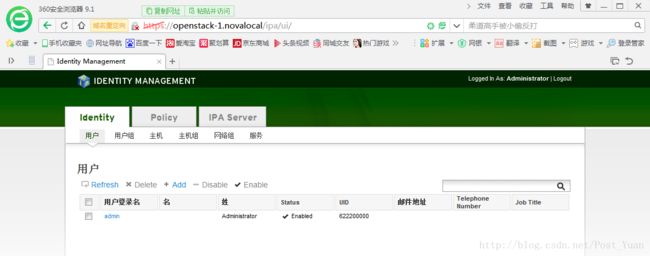
CA Service: RUNNING4 上述安装完成后可打开IPA Web UI(https://openstack-1/ipa/ui)
5 在openstack-1上创建用于安装openstack-2的replica文件
[root@openstack-1 slapd-NOVALOCAL]# ipa-replica-prepare openstack-2.novalocal
Directory Manager (existing master) password:
Preparing replica for openstack-2.novalocal from openstack-1.novalocal
Creating SSL certificate for the Directory Server
Creating SSL certificate for the dogtag Directory Server
Creating SSL certificate for the Web Server
Exporting RA certificate
Copying additional files
Finalizing configuration
Packaging replica information into /var/lib/ipa/replica-info-openstack-2.novalocal.gpg6 将上述生成的replica-info-openstack-2.novalocal.gpg拷贝到openstack-2:/var/lib/ipa/
[root@openstack-1 slapd-NOVALOCAL]# scp /var/lib/ipa/replica-info-openstack-2.novalocal.gpg openstack-2:/var/lib/ipa/7 根据上述创建的.gpg文件在openstack-2上执行安装
[root@openstack-2 yum.repos.d]# ipa-replica-install /var/lib/ipa/replica-info-openstack-2.novalocal.gpg
Directory Manager (existing master) password:
Run connection check to master
Check connection from replica to remote master 'openstack-1.novalocal':
Directory Service: Unsecure port (389): OK
Directory Service: Secure port (636): OK
Kerberos KDC: TCP (88): OK
Kerberos Kpasswd: TCP (464): OK
HTTP Server: Unsecure port (80): OK
HTTP Server: Secure port (443): OK
The following list of ports use UDP protocol and would need to be
checked manually:
Kerberos KDC: UDP (88): SKIPPED
Kerberos Kpasswd: UDP (464): SKIPPED
Connection from replica to master is OK.
Start listening on required ports for remote master check
Get credentials to log in to remote master
admin@NOVALOCAL password:
Execute check on remote master
Check connection from master to remote replica 'openstack-2.novalocal':
Directory Service: Unsecure port (389): OK
Directory Service: Secure port (636): OK
Kerberos KDC: TCP (88): OK
Kerberos KDC: UDP (88): OK
Kerberos Kpasswd: TCP (464): OK
Kerberos Kpasswd: UDP (464): OK
HTTP Server: Unsecure port (80): OK
HTTP Server: Secure port (443): OK
Connection from master to replica is OK.
Connection check OK
Configuring NTP daemon (ntpd)
[1/4]: stopping ntpd
[2/4]: writing configuration
[3/4]: configuring ntpd to start on boot
[4/4]: starting ntpd
Done configuring NTP daemon (ntpd).
Configuring directory server (dirsrv): Estimated time 1 minute
[1/31]: creating directory server user
[2/31]: creating directory server instance
[3/31]: adding default schema
[4/31]: enabling memberof plugin
[5/31]: enabling winsync plugin
[6/31]: configuring replication version plugin
[7/31]: enabling IPA enrollment plugin
[8/31]: enabling ldapi
[9/31]: disabling betxn plugins
[10/31]: configuring uniqueness plugin
[11/31]: configuring uuid plugin
[12/31]: configuring modrdn plugin
[13/31]: enabling entryUSN plugin
[14/31]: configuring lockout plugin
[15/31]: creating indices
[16/31]: enabling referential integrity plugin
[17/31]: configuring ssl for ds instance
[18/31]: configuring certmap.conf
[19/31]: configure autobind for root
[20/31]: configure new location for managed entries
[21/31]: restarting directory server
[22/31]: setting up initial replication
Starting replication, please wait until this has completed.
Update in progress
Update in progress
Update in progress
Update succeeded
[23/31]: adding replication acis
[24/31]: setting Auto Member configuration
[25/31]: enabling S4U2Proxy delegation
[26/31]: initializing group membership
[27/31]: adding master entry
[28/31]: configuring Posix uid/gid generation
[29/31]: enabling compatibility plugin
[30/31]: tuning directory server
[31/31]: configuring directory to start on boot
Done configuring directory server (dirsrv).
Configuring Kerberos KDC (krb5kdc): Estimated time 30 seconds
[1/9]: adding sasl mappings to the directory
[2/9]: writing stash file from DS
[3/9]: configuring KDC
[4/9]: creating a keytab for the directory
[5/9]: creating a keytab for the machine
[6/9]: adding the password extension to the directory
[7/9]: enable GSSAPI for replication
[8/9]: starting the KDC
[9/9]: configuring KDC to start on boot
Done configuring Kerberos KDC (krb5kdc).
Configuring kadmin
[1/2]: starting kadmin
[2/2]: configuring kadmin to start on boot
Done configuring kadmin.
Configuring ipa_memcached
[1/2]: starting ipa_memcached
[2/2]: configuring ipa_memcached to start on boot
Done configuring ipa_memcached.
Configuring the web interface (httpd): Estimated time 1 minute
[1/13]: setting mod_nss port to 443
[2/13]: setting mod_nss protocol list to TLSv1.0 - TLSv1.2
[3/13]: setting mod_nss password file
[4/13]: enabling mod_nss renegotiate
[5/13]: adding URL rewriting rules
[6/13]: configuring httpd
[7/13]: setting up ssl
[8/13]: publish CA cert
[9/13]: creating a keytab for httpd
[10/13]: clean up any existing httpd ccache
[11/13]: configuring SELinux for httpd
[12/13]: restarting httpd
[13/13]: configuring httpd to start on boot
Done configuring the web interface (httpd).
Applying LDAP updates
Restarting the directory server
Restarting the KDC
Restarting the web server8 检查openstack-2安装是否成功
[root@openstack-2 yum.repos.d]# ipactl status
Directory Service: RUNNING
KDC Service: RUNNING
KPASSWD Service: RUNNING
MEMCACHE Service: RUNNING
HTTP Service: RUNNING9 使用ipa-replica-manage list检查HA是否安装成功
[root@openstack-2 yum.repos.d]# ipa-replica-manage list
Directory Manager password:
openstack-2.novalocal: master
openstack-1.novalocal: master
[root@openstack-1 ~]# ipa-replica-manage list
openstack-2.novalocal: master
openstack-1.novalocal: master至此,IPA LDAP HA已经安装成功并可以正常使用,下面我们就试试通过Web UI创建自己的LDAP用户吧~
注:如何是要配置连接Trafodion做LDAP认证,Trafodion中关于UniqueIdentifier应配置为:uid=,cn=users,cn=accounts,dc=novalocal;如果dc=cluster.com,则应该为uid=,cn=users,cn=accounts,dc=cluster,dc=com。
UniqueIdentifier的信息可以在/var/log/ipaserver-install.log中找到,例如
2017-10-11T07:52:04Z DEBUG args=/usr/bin/ldappasswd -h openstack-1.novalocal -ZZ -x -D cn=Directory Manager -y /var/lib/ipa/tmpwLnP2m -T /var/lib/ipa/tmp1GUzKv uid=admin,cn=users,cn=accounts,dc=novalocal
2017-10-11T07:52:08Z DEBUG args=/usr/sbin/ipa-client-install --on-master --unattended --domain novalocal --server openstack-1.novalocal --realm NOVALOCAL --hostname openstack-1.novalocal