微信XXE安全漏洞处理(Java)
登录微信提供处理XXE安全漏洞页面
地址:https://pay.weixin.qq.com/wiki/doc/api/micropay.php?chapter=23_5
原文如下:
最佳安全实践
关于XML解析存在的安全问题指引
微信支付商户,最近暴露的XML外部实体注入漏洞(XML External Entity Injection,简称 XXE),该安全问题是由XML组件默认没有禁用外部实体引用导致,非微信支付系统存在漏洞。
如果你在使用支付业务回调通知中,存在以下场景有使用XML解析的情况,请务必检查是否对进行了防范。
场景1:支付成功通知;
场景2:退款成功通知;
场景3:委托代扣签约、解约、扣款通知;
场景4:车主解约通知;
场景5:扫码支付模式一回调;
注:APP支付的用户端SDK不受影响,但APP支付成功回调通知里面要检查。
微信支付会通过这几个系统号码通知商户进行安全周知和询问是否授权平台进行安全扫描。
(0755)36560292
(0755)61954612
(0755)61954613
(0755)61954614
(0755)61954615
(0755)61954616
授权检测支付系统操作,不会影响商户系统安全。
注:商户如需自我检测XXE漏洞,可前往商户平台(pay.weixin.qq.com)-->产品中心-->安全医生进行测试。
检查及修复建议
1.如果您的后台系统使用了官方SDK,请更新SDK到最新版本 SDK的链接:https://pay.weixin.qq.com/wiki/doc/api/jsapi.php?chapter=11_1
2.如果您是有系统提供商,请联系提供商进行核查和升级修复;
3.如果您是自研系统,请联系技术部门按以下指引核查和修复:
如有疑问,可通过邮箱[email protected]与我们联系,感谢您对微信支付的支持。
XXE漏洞需要你在代码中进行相应的设置,不同语言设置的内容不同,下面提供了几种主流开发语言的设置指引:
【PHP】
libxml_disable_entity_loader(true);【JAVA】
import javax.xml.parsers.DocumentBuilderFactory;
import javax.xml.parsers.ParserConfigurationException; // catching unsupported features
DocumentBuilderFactory dbf = DocumentBuilderFactory.newInstance();
String FEATURE = null;
try {
// This is the PRIMARY defense. If DTDs (doctypes) are disallowed, almost all XML entity attacks are prevented
// Xerces 2 only - http://xerces.apache.org/xerces2-j/features.html#disallow-doctype-decl
FEATURE = "http://apache.org/xml/features/disallow-doctype-decl";
dbf.setFeature(FEATURE, true);
// If you can't completely disable DTDs, then at least do the following:
// Xerces 1 - http://xerces.apache.org/xerces-j/features.html#external-general-entities
// Xerces 2 - http://xerces.apache.org/xerces2-j/features.html#external-general-entities
// JDK7+ - http://xml.org/sax/features/external-general-entities
FEATURE = "http://xml.org/sax/features/external-general-entities";
dbf.setFeature(FEATURE, false);
// Xerces 1 - http://xerces.apache.org/xerces-j/features.html#external-parameter-entities
// Xerces 2 - http://xerces.apache.org/xerces2-j/features.html#external-parameter-entities
// JDK7+ - http://xml.org/sax/features/external-parameter-entities
FEATURE = "http://xml.org/sax/features/external-parameter-entities";
dbf.setFeature(FEATURE, false);
// Disable external DTDs as well
FEATURE = "http://apache.org/xml/features/nonvalidating/load-external-dtd";
dbf.setFeature(FEATURE, false);
// and these as well, per Timothy Morgan's 2014 paper: "XML Schema, DTD, and Entity Attacks"
dbf.setXIncludeAware(false);
dbf.setExpandEntityReferences(false);
// And, per Timothy Morgan: "If for some reason support for inline DOCTYPEs are a requirement, then
// ensure the entity settings are disabled (as shown above) and beware that SSRF attacks
// (http://cwe.mitre.org/data/definitions/918.html) and denial
// of service attacks (such as billion laughs or decompression bombs via "jar:") are a risk."
// remaining parser logic
} catch (ParserConfigurationException e) {
// This should catch a failed setFeature feature
logger.info("ParserConfigurationException was thrown. The feature '" +
FEATURE + "' is probably not supported by your XML processor.");
}
catch (SAXException e) {
// On Apache, this should be thrown when disallowing DOCTYPE
logger.warning("A DOCTYPE was passed into the XML document");
}
catch (IOException e) {
// XXE that points to a file that doesn't exist
logger.error("IOException occurred, XXE may still possible: " + e.getMessage());
}
DocumentBuilder safebuilder = dbf.newDocumentBuilder();
【.Net】
XmlDocument doc= new XmlDocument();
doc.XmlResolver = null;
【ASP】
Set xmldom = Server.CreateObject("MSXML2.DOMDocument")
xmldom.resolveExternals = false
【Python】
from lxml import etree
xmlData = etree.parse(xmlSource,etree.XMLParser(resolve_entities=False))
【c/c++(常用库为libxml2 libxerces-c)】 【libxml2】: 确保关闭配置选项:XML_PARSE_NOENT 和 XML_PARSE_DTDLOAD
2.9版本以上已修复XXE
【libxerces-c】:
如果用的是XercesDOMParser:
XercesDOMParser *parser = new XercesDOMParser;
parser->setCreateEntityReferenceNodes(false);如果是用SAXParser:
SAXParser* parser = new SAXParser;
parser->setDisableDefaultEntityResolution(true);如果是用SAX2XMLReader:
SAX2XMLReader* reader = XMLReaderFactory::createXMLReader();
parser->setFeature(XMLUni::fgXercesDisableDefaultEntityResolution, true);附录:更多开源库/语言版本的修复建议可参考:
https://www.owasp.org/index.php/XML_External_Entity_(XXE)_Prevention_Cheat_Sheet#C.2FC.2B.2B
##############################分割线##############################################################
综上所述,XXE 是 XML外部实体注入漏洞(XML External Entity Injection,简称 XXE)
该安全问题是由XML组件默认没有禁用外部实体引用导致
非微信支付系统存在漏洞。
Java. .net C# PHP的可以通过 https://pay.weixin.qq.com/wiki/doc/api/jsapi.php?chapter=11_1 地址进行sdk下载
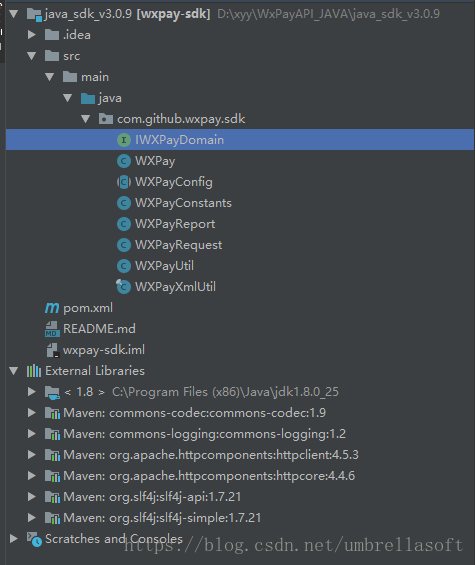
下载回来的Java SDK 结构如下:
提供了非常多的微信工具(相当全啊,毕竟是官方的)
官方已经将XXE漏洞的工具封装好了
找到 WXPayUtil.xmlToMap() 方法/**
* XML格式字符串转换为Map
*
* @param strXML XML字符串
* @return XML数据转换后的Map
* @throws Exception
*/
public static Map xmlToMap(String strXML) throws Exception {
try {
Map data = new HashMap();
DocumentBuilder documentBuilder = WXPayXmlUtil.newDocumentBuilder();
InputStream stream = new ByteArrayInputStream(strXML.getBytes("UTF-8"));
org.w3c.dom.Document doc = documentBuilder.parse(stream);
doc.getDocumentElement().normalize();
NodeList nodeList = doc.getDocumentElement().getChildNodes();
for (int idx = 0; idx < nodeList.getLength(); ++idx) {
Node node = nodeList.item(idx);
if (node.getNodeType() == Node.ELEMENT_NODE) {
org.w3c.dom.Element element = (org.w3c.dom.Element) node;
data.put(element.getNodeName(), element.getTextContent());
}
}
try {
stream.close();
} catch (Exception ex) {
// do nothing
}
return data;
} catch (Exception ex) {
WXPayUtil.getLogger().warn("Invalid XML, can not convert to map. Error message: {}. XML content: {}", ex.getMessage(), strXML);
throw ex;
}
} 接下来就看自己看着办吧