Scapy 嗅探Python仿真实验(GUI界面)--2.2使用sniff监听网口抓包
导入scapy库
from scapy.all import *
import time
##同时导入了time,后面会使用到
简单使用sniff函数
使用方式:
sniff(filter=filt,prn=pack_callback,iface=IFACES.dev_from_index(port_num), count=1)
解释
| 项 | 含义 |
|---|---|
| filter | 过滤器 |
| prn | 调用函数 |
| iface | 网卡标识,port_num是网卡序号 |
| count | 抓包数量 |
过滤器
上面filt是一个可选字符串,若留空则嗅探所有类型的数据包,若 filt=‘tcp’,则嗅探tcp包,依次类推
获取网卡标识
1.打开cmd窗口,进入scapy
2.输入:ifaces,回车
3.INDEX一列代表port_num,我们要获取监听的网卡前的那个数字,这里我连的是wifi,所以我的网卡标识序号是:6,即port_num=6

输出数据包的内容
用sniff嗅探到数据包后,我们来简单输出看看,代码如下(这里只简单显示ip,tcp):
#!/usr/bin/python
# -*- coding:UTF-8 -*-
import time
from scapy.all import *
from scapy.layers.inet import IP, TCP, UDP, ICMP
from scapy.sendrecv import sniff
from scapy.layers import http
def nowTime(timestamp):
timeArray=time.localtime(timestamp)
mytime =time.strftime("%Y-%m-%d %H:%M:%S",timeArray)
return mytime
def dns_sniff(pkt,udp_p):
dns=pkt['DNS']
if int(udp_p.dport) == 53:
print(dns.name,"qd, :",dns.qd.qname)
elif int(udp_p.sport) ==53:
if dns.ancount == 0:
print(dns.name,"qd, :",dns.qd.qname)
return 0
for i in range(dns.ancount):
dns_r = dns.an[i]
print(dns.name,'an,:',dns_r.rrname,'->',dns_r.rdata)
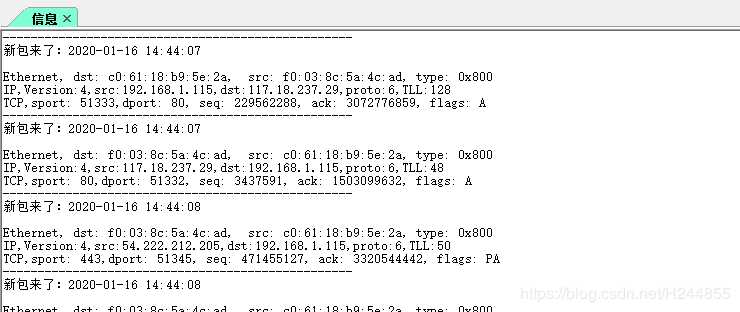
def pack_callback(packet):
print('-' * 50)
print('新包来了:'+nowTime(packet.time)+'\n')
p=packet
print("%s, dst: %s, src: %s, type: %s" %(p.name,p.dst,p.src,hex(p.type)))
if 'IP' in p:
ip=p.getlayer(IP)
print("%s,Version:%s,src:%s,dst:%s,proto:%s,TLL:%s" % (ip.name, ip.version, ip.src, ip.dst, str(ip.proto), str(ip.ttl)))
if 'TCP' in p:
tcp=p.getlayer(TCP)
print("%s,sport: %s,dport: %s, seq: %s, ack: %s, flags: %s" %( \
tcp.name,str(tcp.sport),str(tcp.dport),\
str(tcp.seq),str(tcp.ack),str(tcp.flags)))
while 1:
filt=""
sniff(filter=filt,prn=pack_callback,iface=IFACES.dev_from_index(6), count=1)
##留空过滤filter