Xiang Li
文章目录
- 1 摘要
- 2 Nmap作用
- 3 常用Nmap扫描指令
- 4 端口扫描状态
- 5 TCP/IP协议与Http协议的区别
- 6 使用Nmap探测目标开放端口
1 摘要
一 端口是个网络应用中很重要的东西,相当于“门”。
二 什么是端口
端口在计算机网络中是个非常重要的概念,他不是硬件,不同于计算机中的插槽,可以说是个软插槽。如果有需要,一台计算机中可以由上万个端口。
端口是由计算通信协议TCP/IP协议定义的。其中规定,用IP地址和端口作为套接字,它代表TCP链接的一个连接端,一般称为socket,具体来说,就是用[ip:端口]来定位一台主机中的进程。可以做这样的比喻,端口相当于两台计算机进程间的大门,可随便定义,其目的只是为了让两台计算机能找到对方的进程。计算机就想一座大楼,这个大楼有好多入口(端口),进到不同的入口中就可以找到不同的公司(进程)。如果要和远程主机A的程序通信,那么只要把数据发向[A;端口]就可以实现通信了。
三 端口的分类
在Internet上,按照协议类型分类,端口被分为TCP端口和UDP端口两类,虽然他们都用正整数标识,但这并不会引起歧义,比如TCP的80端口和UDP的80端口,因为数据报在标明端口的同时,还将标明端口的类型。
从端口的分配来看,端口被分为固定端口和动态端口两大类(一些教程还将极少被用到的高端口划分为第三类:私有端口):
固定端口(0-1023):
使用集中式管理机制,即服从一个管理机构对端口的指派,这个机构负责发布这些指派。由于这些端口紧绑于一些服务,所以我们会经常扫描这些端口来判断对方 是否开启了这些服务,如TCP的21(ftp),80(http),139(netbios),UDP的7(echo),69(tftp)等等一些大家熟 知的端口;
动态端口(1024-49151):
这些端口并不被固定的捆绑于某一服务,操作系统将这些端口动态的分配给各个进程, 同一进程两次分配有可能分配到不同的端口。不过一些应用程序并不愿意使用操作系统分配的动态端口,他们有其自己的‘商标性’端口,如oicq客户端的 4000端口,木马冰河的7626端口等都是固定而出名的。
四 端口在入侵中的作用
有人曾经把服务器比作房子,而把端口比作通向不同房间(服务)的门,如果不考虑细节的话,这是一个不错的比喻。入侵者要占领这间房子,势必要破门而入(物理入侵另说),那么对于入侵者来说,了解房子开了几扇门,都是什么样的门,门后面有什么东西就显得至关重要。
入侵者通常会用扫描器对目标主机的端口进行扫描,以确定哪些端口是开放的,从开放的端口,入侵者可以知道目标主机大致提供了哪些服务,进而猜测可能存在 的漏洞,因此对端口的扫描可以帮助我们更好的了解目标主机,而对于管理员,扫描本机的开放端口也是做好安全防范的第一步。
五、端口扫描原理:尝试与目标主机建立连接,如果目标主机有回复则说明端口开放。
扫描分类:
1. 全TCP连接,这种方法使用三次握手与目标主机建立标准的tcp连接。但是这种方法跟容易被发现,被目标主机记录。
2. SYN扫描,扫描主机自动向目标主机的指定端口发送SYN数据段,表示发送建立连接请求。
!!如果目标主机的回应报文SYN=1,ACK=1.则说明该端口是活动的,接着扫描主机发送回一个RST给目标主机拒绝连接。导致三次握手失败。
!!如果目标主机回应是RST则端口是“死的”。
3 FIN扫描,发送一个FIN=1的报文到一个关闭的窗口该报文将丢失并返回一个RST,如果该FIN报文发送到活动窗口则报文丢失,不会有任何反应。
4.代理扫描。就是抓鸡啦。
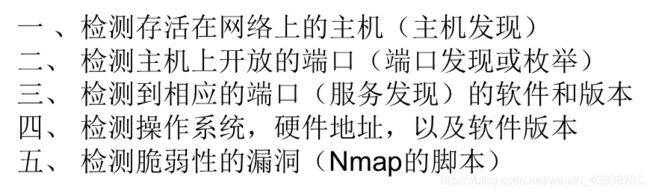
2 Nmap作用
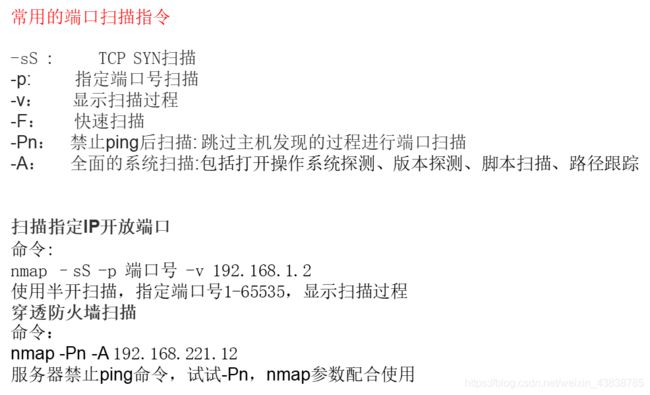
3 常用Nmap扫描指令
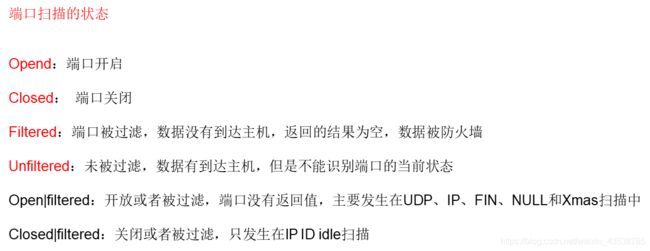
4 端口扫描状态
5 TCP/IP协议与Http协议的区别
TPC/IP协议是传输层协议,主要解决数据如何在网络中传输,而HTTP是应用层协议,主要解决如何包装数据。关于TCP/IP和HTTP协议的关系,网络有一段比较容易理解的介绍:“我们在传输数据时,可以只使用(传输层)TCP/IP协议,但是那样的话,如果没有应用层,便无法识别数据内容,如果想要使传输的数据有意义,则必须使用到应用层协议,应用层协议有很多,比如HTTP、FTP、TELNET等,也可以自己定义应用层协议。WEB使用HTTP协议作应用层协议,以封装HTTP 文本信息,然后使用TCP/IP做传输层协议将它发到网络上。”
术语TCP/IP代表传输控制协议/网际协议,指的是一系列协议。“IP”代表网际协议,TCP和UDP使用该协议从一个网络传送数据包到另一个网络。把IP想像成一种高速公路,它允许其它协议在上面行驶并找到到其它电脑的出口。TCP和UDP是高速公路上的“卡车”,它们携带的货物就是像HTTP,文件传输协议FTP这样的协议等。
你应该能理解,TCP和UDP是FTP,HTTP和SMTP之类使用的传输层协议。虽然TCP和UDP都是用来传输其他协议的,它们却有一个显著的不同:TCP提供有保证的数据传输,而UDP不提供。这意味着TCP有一个特殊的机制来确保数据安全的不出错的从一个端点传到另一个端点,而UDP不提供任何这样的保证。
HTTP(超文本传输协议)是利用TCP在两台电脑(通常是Web服务器和客户端)之间传输信息的协议。客户端使用Web浏览器发起HTTP请求给Web服务器,Web服务器发送被请求的信息给客户端。
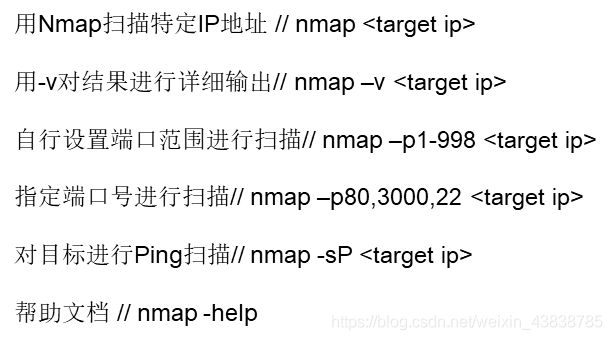
6 使用Nmap探测目标开放端口
nmap有图形化界面 也可以在shell中使用
先探测一下win7虚拟机的端口
root@kali:~# nmap -h
Nmap 7.70 ( https://nmap.org )
Usage: nmap [Scan Type(s)] [Options] {target specification}
TARGET SPECIFICATION:
Can pass hostnames, IP addresses, networks, etc.
Ex: scanme.nmap.org, microsoft.com/24, 192.168.0.1; 10.0.0-255.1-254
-iL : Input from list of hosts/networks
-iR : Choose random targets
--exclude [,host2][,host3],...>: Exclude hosts/networks
--excludefile : Exclude list from file
HOST DISCOVERY:
-sL: List Scan - simply list targets to scan
-sn: Ping Scan - disable port scan
-Pn: Treat all hosts as online -- skip host discovery
-PS/PA/PU/PY[portlist]: TCP SYN/ACK, UDP or SCTP discovery to given ports
-PE/PP/PM: ICMP echo, timestamp, and netmask request discovery probes
-PO[protocol list]: IP Protocol Ping
-n/-R: Never do DNS resolution/Always resolve [default: sometimes]
--dns-servers [,serv2],...>: Specify custom DNS servers
--system-dns: Use OS's DNS resolver
--traceroute: Trace hop path to each host
SCAN TECHNIQUES:
-sS/sT/sA/sW/sM: TCP SYN/Connect()/ACK/Window/Maimon scans
-sU: UDP Scan
-sN/sF/sX: TCP Null, FIN, and Xmas scans
--scanflags : Customize TCP scan flags
-sI : Idle scan
-sY/sZ: SCTP INIT/COOKIE-ECHO scans
-sO: IP protocol scan
-b : FTP bounce scan
PORT SPECIFICATION AND SCAN ORDER:
-p : Only scan specified ports
Ex: -p22; -p1-65535; -p U:53,111,137,T:21-25,80,139,8080,S:9
--exclude-ports : Exclude the specified ports from scanning
-F: Fast mode - Scan fewer ports than the default scan
-r: Scan ports consecutively - don' t randomize
--top-ports : Scan most common ports
--port-ratio : Scan ports more common than
SERVICE/VERSION DETECTION:
-sV: Probe open ports to determine service/version info
--version-intensity : Set from 0 (light) to 9 (try all probes)
--version-light: Limit to most likely probes (intensity 2)
--version-all: Try every single probe (intensity 9)
--version-trace: Show detailed version scan activity (for debugging)
SCRIPT SCAN:
-sC: equivalent to --script=default
--script=: is a comma separated list of
directories, script-files or script-categories
--script-args=,[n2=v2,...]>: provide arguments to scripts
--script-args-file=filename: provide NSE script args in a file
--script-trace: Show all data sent and received
--script-updatedb: Update the script database.
--script-help=: Show help about scripts.
is a comma-separated list of script-files or
script-categories.
OS DETECTION:
-O: Enable OS detection
--osscan-limit: Limit OS detection to promising targets
--osscan-guess: Guess OS more aggressively
TIMING AND PERFORMANCE:
Options which take root@kali:~# nmap shop.aqlab.cn
Starting Nmap 7.70 ( https://nmap.org ) at 2020-03-15 04:50 EDT
Stats: 0:00:31 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 91.45% done; ETC: 04:50 (0:00:03 remaining)
Stats: 0:00:32 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 91.70% done; ETC: 04:50 (0:00:03 remaining)
Stats: 0:00:33 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 91.80% done; ETC: 04:50 (0:00:03 remaining)
Stats: 0:00:33 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 91.85% done; ETC: 04:50 (0:00:03 remaining)
Stats: 0:00:34 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 92.00% done; ETC: 04:50 (0:00:03 remaining)
Stats: 0:00:34 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 92.05% done; ETC: 04:50 (0:00:03 remaining)
Stats: 0:00:34 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 92.10% done; ETC: 04:50 (0:00:03 remaining)
Stats: 0:00:34 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 92.15% done; ETC: 04:50 (0:00:03 remaining)
Nmap scan report for shop.aqlab.cn (59.63.200.79)
Host is up (0.076s latency).
Not shown: 990 filtered ports
PORT STATE SERVICE
80/tcp open http
443/tcp open https
1433/tcp open ms-sql-s
3389/tcp open ms-wbt-server
8001/tcp open vcom-tunnel
8002/tcp open teradataordbms
8007/tcp open ajp12
8008/tcp open http
8010/tcp open xmpp
8082/tcp open blackice-alerts
Nmap done: 1 IP address (1 host up) scanned in 40.27 seconds
root@kali:~# nmap -p 80-10000 -A shop.aplab.cn -v
Starting Nmap 7.70 ( https://nmap.org ) at 2020-03-15 04:53 EDT
NSE: Loaded 148 scripts for scanning.
NSE: Script Pre-scanning.
Initiating NSE at 04:53
Completed NSE at 04:53, 0.00s elapsed
Initiating NSE at 04:53
Completed NSE at 04:53, 0.00s elapsed
Failed to resolve "shop.aplab.cn".
NSE: Script Post-scanning.
Initiating NSE at 04:53
Completed NSE at 04:53, 0.00s elapsed
Initiating NSE at 04:53
Completed NSE at 04:53, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
WARNING: No targets were specified, so 0 hosts scanned.
Nmap done: 0 IP addresses (0 hosts up) scanned in 1.23 seconds
Raw packets sent: 0 (0B) | Rcvd: 0 (0B)
root@kali:~# nmap -p 80-10000 -A shop.aplab.cn -v
Starting Nmap 7.70 ( https://nmap.org ) at 2020-03-15 04:56 EDT
NSE: Loaded 148 scripts for scanning.
NSE: Script Pre-scanning.
Initiating NSE at 04:56
Completed NSE at 04:56, 0.00s elapsed
Initiating NSE at 04:56
Completed NSE at 04:56, 0.00s elapsed
Failed to resolve "shop.aplab.cn".
NSE: Script Post-scanning.
Initiating NSE at 04:56
Completed NSE at 04:56, 0.00s elapsed
Initiating NSE at 04:56
Completed NSE at 04:56, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
WARNING: No targets were specified, so 0 hosts scanned.
Nmap done: 0 IP addresses (0 hosts up) scanned in 1.07 seconds
Raw packets sent: 0 (0B) | Rcvd: 0 (0B)
root@kali:~# nmap -p 80-10000 -A shop.aplab.cn -v
Starting Nmap 7.70 ( https://nmap.org ) at 2020-03-15 05:00 EDT
NSE: Loaded 148 scripts for scanning.
NSE: Script Pre-scanning.
Initiating NSE at 05:01
Completed NSE at 05:01, 0.00s elapsed
Initiating NSE at 05:01
Completed NSE at 05:01, 0.00s elapsed
Failed to resolve "shop.aplab.cn".
NSE: Script Post-scanning.
Initiating NSE at 05:01
Completed NSE at 05:01, 0.00s elapsed
Initiating NSE at 05:01
Completed NSE at 05:01, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
WARNING: No targets were specified, so 0 hosts scanned.
Nmap done: 0 IP addresses (0 hosts up) scanned in 1.06 seconds
Raw packets sent: 0 (0B) | Rcvd: 0 (0B)
root@kali:~# nmap -p80-10000 -A shop.aplab.cn -v
Starting Nmap 7.70 ( https://nmap.org ) at 2020-03-15 05:01 EDT
NSE: Loaded 148 scripts for scanning.
NSE: Script Pre-scanning.
Initiating NSE at 05:01
Completed NSE at 05:01, 0.00s elapsed
Initiating NSE at 05:01
Completed NSE at 05:01, 0.00s elapsed
Failed to resolve "shop.aplab.cn".
NSE: Script Post-scanning.
Initiating NSE at 05:01
Completed NSE at 05:01, 0.00s elapsed
Initiating NSE at 05:01
Completed NSE at 05:01, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
WARNING: No targets were specified, so 0 hosts scanned.
Nmap done: 0 IP addresses (0 hosts up) scanned in 1.05 seconds
Raw packets sent: 0 (0B) | Rcvd: 0 (0B)
-A表示全面的系统扫描
经过验证 8001端口可能是脆弱站点
Here