c++ AES实现CBC,CTR模式解密函数
高级加密标准(英语:Advanced Encryption Standard,缩写:AES),在密码学中又称Rijndael加密法,是美国联邦政府采用的一种区块加密标准。这个标准用来替代原先的DES,已经被多方分析且广为全世界所使用。本文将介绍AES的具体流程,以及c++实现,并且实现了CBC和CTR模式的解密函数。
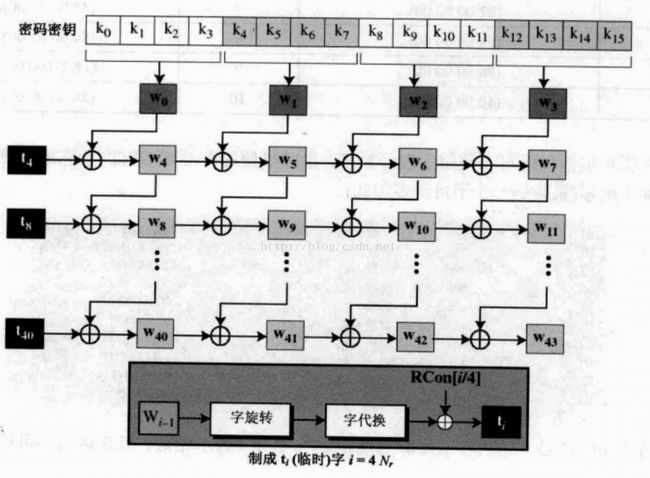
1.关于AES(高级加密标准):在这里一个分组为128bit(16byte),密钥也是128bit(16byte),密钥要先通过密钥扩展,具体过程如图:
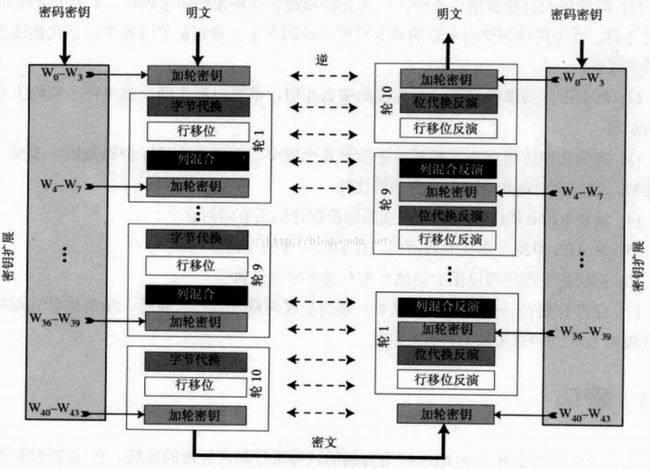
然后加轮密钥(第一轮之前),之后再经过每一轮的比特代换,行移位,列混合和加轮密钥,每个分组一共10轮,如下图所示的加密过程:
解密则是相逆的过程,如上图所示,首先是密钥扩展,先加轮密钥,然后在经过每一轮的行移位反演,位代换反演,加轮密钥和列混合反演,每个分组一共进行10轮。还要注意的一点是在每一轮里的结构是状态(state),是4*4的矩阵。
下面是c++代码:
AES.h
#ifndef __SymmetricKeyCipher__AES__
#define __SymmetricKeyCipher__AES__
#include
typedef unsigned char Byte;
// Each word is 4 Bytes
#define BYTES_IN_WORD (4)
// Each round of key is 4 words
#define WORD_IN_ROUND (4)
// Each byte has 8 bits
#define BIT_IN_BYTE (8)
// Each round of key is 4 words, say 4 * 4 = 16 Bytes
#define BYTES_IN_ROUND (16)
// Expended key length is 11 round, say 11 * 16 = 176 Bytes
#define BYTES_IN_EXPANDED_KEY (176)
// In AES128 has 10 rounds except the initialization round
#define NUM_OF_ROUNDS (10)
static Byte sBox[16][16] = {
{0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76},
{0xCA, 0x82, 0xC9, 0x7D, 0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0},
{0xB7, 0xFD, 0x93, 0x26, 0x36, 0x3F, 0xF7, 0xCC, 0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15},
{0x04, 0xC7, 0x23, 0xC3, 0x18, 0x96, 0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2, 0xEB, 0x27, 0xB2, 0x75},
{0x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0, 0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84},
{0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB, 0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF},
{0xD0, 0xEF, 0xAA, 0xFB, 0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F, 0x50, 0x3C, 0x9F, 0xA8},
{0x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5, 0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF, 0xF3, 0xD2},
{0xCD, 0x0C, 0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D, 0x64, 0x5D, 0x19, 0x73},
{0x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A, 0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB},
{0xE0, 0x32, 0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3, 0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79},
{0xE7, 0xC8, 0x37, 0x6D, 0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A, 0xAE, 0x08},
{0xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6, 0xB4, 0xC6, 0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A},
{0x70, 0x3E, 0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E, 0x61, 0x35, 0x57, 0xB9, 0x86, 0xC1, 0x1D, 0x9E},
{0xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9, 0x8E, 0x94, 0x9B, 0x1E, 0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF},
{0x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F, 0xB0, 0x54, 0xBB, 0x16}
};
static Byte sBoxInv[16][16] = {
{0x52, 0x09, 0x6A, 0xD5, 0x30, 0x36, 0xA5, 0x38, 0xBF, 0x40, 0xA3, 0x9E, 0x81, 0xF3, 0xD7, 0xFB},
{0x7C, 0xE3, 0x39, 0x82, 0x9B, 0x2F, 0xFF, 0x87, 0x34, 0x8E, 0x43, 0x44, 0xC4, 0xDE, 0xE9, 0xCB},
{0x54, 0x7B, 0x94, 0x32, 0xA6, 0xC2, 0x23, 0x3D, 0xEE, 0x4C, 0x95, 0x0B, 0x42, 0xFA, 0xC3, 0x4E},
{0x08, 0x2E, 0xA1, 0x66, 0x28, 0xD9, 0x24, 0xB2, 0x76, 0x5B, 0xA2, 0x49, 0x6D, 0x8B, 0xD1, 0x25},
{0x72, 0xF8, 0xF6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0x65, 0xB6, 0x92},
{0x6C, 0x70, 0x48, 0x50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0x15, 0x46, 0x57, 0xA7, 0x8D, 0x9D, 0x84},
{0x90, 0xD8, 0xAB, 0x00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0x58, 0x05, 0xB8, 0xB3, 0x45, 0x06},
{0xD0, 0x2C, 0x1E, 0x8F, 0xCA, 0x3F, 0x0F, 0x02, 0xC1, 0xAF, 0xBD, 0x03, 0x01, 0x13, 0x8A, 0x6B},
{0x3A, 0x91, 0x11, 0x41, 0x4F, 0x67, 0xDC, 0xEA, 0x97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0x73},
{0x96, 0xAC, 0x74, 0x22, 0xE7, 0xAD, 0x35, 0x85, 0xE2, 0xF9, 0x37, 0xE8, 0x1C, 0x75, 0xDF, 0x6E},
{0x47, 0xF1, 0x1A, 0x71, 0x1D, 0x29, 0xC5, 0x89, 0x6F, 0xB7, 0x62, 0x0E, 0xAA, 0x18, 0xBE, 0x1B},
{0xFC, 0x56, 0x3E, 0x4B, 0xC6, 0xD2, 0x79, 0x20, 0x9A, 0xDB, 0xC0, 0xFE, 0x78, 0xCD, 0x5A, 0xF4},
{0x1F, 0xDD, 0xA8, 0x33, 0x88, 0x07, 0xC7, 0x31, 0xB1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xEC, 0x5F},
{0x60, 0x51, 0x7F, 0xA9, 0x19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9F, 0x93, 0xC9, 0x9C, 0xEF},
{0xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0x83, 0x53, 0x99, 0x61},
{0x17, 0x2B, 0x04, 0x7E, 0xBA, 0x77, 0xD6, 0x26, 0xE1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0C, 0x7D}
};
static Byte constantMatrix[4][4] = {
{0x02, 0x03, 0x01, 0x01},
{0x01, 0x02, 0x03, 0x01},
{0x01, 0x01, 0x02, 0x03},
{0x03, 0x01, 0x01, 0x02}
};
static Byte constantMatrixInv[4][4] = {
{0x0E, 0x0B, 0x0D, 0x09},
{0x09, 0x0E, 0x0B, 0x0D},
{0x0D, 0x09, 0x0E, 0x0B},
{0x0B, 0x0D, 0x09, 0x0E}
};
static Byte GF_constant[8] = {0x1B, 0x36, 0x6C, 0xD8, 0xAB, 0x4D, 0x9A, 0x2F};
static Byte roundConstant[10] = {0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1B, 0x36};
Byte *keyExpansion(Byte *cipherKey);
void AES_Encryption(Byte state[][BYTES_IN_WORD], Byte* key);
void AES_Decryption(Byte state[][BYTES_IN_WORD], Byte* key);
void rotateWord(Byte *word, int offset);
void substitutionWord(Byte *word);
void substitutionWord(Byte state[][BYTES_IN_WORD]);
void substitutionWordInv(Byte state[][BYTES_IN_WORD]);
void shiftRow(Byte state[][BYTES_IN_WORD]);
void shiftRowInv(Byte state[][BYTES_IN_WORD]);
void mixColumn(Byte state[][BYTES_IN_WORD]);
void mixColumnInv(Byte state[][BYTES_IN_WORD]);
Byte GF_Multiplication(Byte a, Byte b);
void addRoundKey(Byte state[][BYTES_IN_WORD], Byte* key, int round);
void printState(Byte state[][BYTES_IN_WORD]);
#endif AES.cpp
#include
#include
#include "AES.h"
Byte *keyExpansion(Byte *cipherKey) {
Byte *expandedKey = (Byte *)malloc(sizeof(Byte) * BYTES_IN_EXPANDED_KEY);
// get the key of the first round
for(int i = 0; i < BYTES_IN_ROUND; i++)
expandedKey[i] = cipherKey[i];
// get the key of other rounds
Byte *temporary_word = (Byte *)malloc(sizeof(Byte) * BYTES_IN_WORD);
for(int i = 1; i <= NUM_OF_ROUNDS; i++) {
// calculate the temporary word
for(int j = 0; j < BYTES_IN_WORD; j++)
temporary_word[j] = expandedKey[i * BYTES_IN_ROUND - BYTES_IN_WORD + j];
rotateWord(temporary_word, 1);
substitutionWord(temporary_word);
temporary_word[0] = (temporary_word[0] ^ roundConstant[i - 1]);
// get the key of this round
for(int j = 0; j < BYTES_IN_WORD; j++)
expandedKey[i * BYTES_IN_ROUND + j] = temporary_word[j]
^ expandedKey[(i - 1) * BYTES_IN_ROUND + j];
for(int j = 1; j < WORD_IN_ROUND; j++) {
for(int k = 0; k < BYTES_IN_WORD; k++) {
expandedKey[i * BYTES_IN_ROUND + j * BYTES_IN_WORD + k] =
expandedKey[i * BYTES_IN_ROUND + (j - 1) * BYTES_IN_WORD + k] ^
expandedKey[(i - 1) * BYTES_IN_ROUND + j * BYTES_IN_WORD + k];
}
}
}
free(temporary_word);
return expandedKey;
}
void AES_Encryption(Byte state[][BYTES_IN_WORD], Byte* key) {
// Round 0: addRoundKey
addRoundKey(state, key, 0);
// Round 1~9: substitutionWord + shiftRow + mixColumn + addRoundKey
for(int i = 1; i < 10; i++) {
substitutionWord(state);
shiftRow(state);
mixColumn(state);
addRoundKey(state, key, i);
}
// Round 10: substitutionWord + shiftRow + addRoundKey
substitutionWord(state);
shiftRow(state);
addRoundKey(state, key, 10);
}
void AES_Decryption(Byte state[][BYTES_IN_WORD], Byte* key) {
// Inv round 10: addRoundKey + shiftRowInv + substitutionWordInv
addRoundKey(state, key, 10);
shiftRowInv(state);
substitutionWordInv(state);
// Inv round 9~1: addRoundKey + mixColumnInv + shiftRowInv + substitutionWordInv
for(int i = 9; i > 0; i--) {
addRoundKey(state, key, i);
mixColumnInv(state);
shiftRowInv(state);
substitutionWordInv(state);
}
// Inv round 0: addRoundKey
addRoundKey(state, key, 0);
}
void rotateWord(Byte *word, int offset) {
Byte *temp = (Byte *)malloc(sizeof(Byte) * BYTES_IN_WORD);
for(int i = 0; i < BYTES_IN_WORD; i++)
temp[(i + BYTES_IN_WORD - offset) % 4] = word[i];
for(int i = 0; i < BYTES_IN_WORD; i++)
word[i] = temp[i];
free(temp);
}
void substitutionWord(Byte *word) {
for(int i = 0; i < BYTES_IN_WORD; i++)
word[i] = sBox[word[i] / 16][word[i] % 16];
}
void substitutionWord(Byte state[][BYTES_IN_WORD]) {
for(int i = 0; i < BYTES_IN_WORD; i++)
for(int j = 0; j < BYTES_IN_WORD; j++)
state[i][j] = sBox[state[i][j] / 16][state[i][j] % 16];
}
void substitutionWordInv(Byte state[][BYTES_IN_WORD]) {
for(int i = 0; i < BYTES_IN_WORD; i++)
for(int j = 0; j < BYTES_IN_WORD; j++)
state[i][j] = sBoxInv[state[i][j] / 16][state[i][j] % 16];
}
void shiftRow(Byte state[][BYTES_IN_WORD]) {
for(int i = 0; i < BYTES_IN_WORD; i++)
rotateWord(state[i], i);
}
void shiftRowInv(Byte state[][BYTES_IN_WORD]) {
for(int i = 1; i < BYTES_IN_WORD; i++)
rotateWord(state[i], 4 - i);
}
void mixColumn(Byte state[][BYTES_IN_WORD]) {
Byte *temp = (Byte *)malloc(sizeof(Byte) * BYTES_IN_WORD);
for(int i = 0; i < BYTES_IN_WORD; i++) {
for(int j = 0; j < BYTES_IN_WORD; j++)
temp[j] = state[j][i];
for(int j = 0; j < BYTES_IN_WORD; j++) {
state[j][i] = 0;
for(int k = 0; k < BYTES_IN_WORD; k++)
state[j][i] = (state[j][i] ^ GF_Multiplication(constantMatrix[j][k], temp[k]));
}
}
free(temp);
}
void mixColumnInv(Byte state[][BYTES_IN_WORD]) {
Byte *temp = (Byte *)malloc(sizeof(Byte) * BYTES_IN_WORD);
for(int i = 0; i < BYTES_IN_WORD; i++) {
for(int j = 0; j < BYTES_IN_WORD; j++)
temp[j] = state[j][i];
for(int j = 0; j < BYTES_IN_WORD; j++) {
state[j][i] = 0;
for(int k = 0; k < BYTES_IN_WORD; k++)
state[j][i] = (state[j][i] ^ GF_Multiplication(constantMatrixInv[j][k], temp[k]));
}
}
free(temp);
}
Byte GF_Multiplication(Byte a, Byte b) {
bool *temp = (bool *)malloc(sizeof(bool) * BIT_IN_BYTE * 2);
for(int i = 0; i < BIT_IN_BYTE; i++) {
temp[i] = b % 2;
b /= 2;
}
short result = 0;
for(int i = 0; i < BIT_IN_BYTE; i++) {
result = result ^ ((temp[i] * a) << i);
}
int count = 0;
int temp_result = result;
for(int i = 0; i < BIT_IN_BYTE * 2; i++) {
temp[count++] = temp_result % 2;
temp_result /= 2;
}
for(int i = BIT_IN_BYTE; i < BIT_IN_BYTE * 2; i++)
if(temp[i] == 1)
result = result ^ GF_constant[i - BIT_IN_BYTE];
free(temp);
return (Byte)result;
}
void addRoundKey(Byte state[][BYTES_IN_WORD], Byte* key, int round) {
for(int i = 0; i < BYTES_IN_WORD; i++)
for(int j = 0; j < BYTES_IN_WORD; j++)
state[j][i] = (state[j][i] ^ key[round * BYTES_IN_ROUND + i * 4 + j]);
}
void printState(Byte state[][BYTES_IN_WORD]) {
for(int i = 0; i < BYTES_IN_WORD; i++) {
for(int j = 0; j < BYTES_IN_WORD; j++)
printf("%02X ", state[i][j]);
printf("\n");
}
printf("\n");
}
2.关于CBC(密码分组链接模式),如它的名称所示,它是让相邻的分组进行异或操作,让前后分组有关联,在发送方,异或要在加密之前完成,相对的,在接收方,异或操作要在解密之后进行,如下图所示CBC模式:
其中关键的是chainModeDecryption(Byte *stream,Byte *IV,Byte *fullKey,int size);函数,如下,stream数组是密文数组(Byte),IV为初始向量,fullkey为密钥扩展后的key,size是密文的长度,具体代码实现如下:
void chainModeDecryption(Byte *stream,Byte *IV,Byte *fullKey,int size){
//将解密后的明文保存在restream数组
Byte *restream = new Byte[size+1];
int cnt = 0;
for(int r = 0;r*163.关于CTR(计数器模式):CTR模式不存在反馈机制,也不是对明文进行直接的加密,而是对一个counter(这里是IV,)进行加密,而这个counter每进行一轮就加1,如下图所示:
其中关键的是counterModeDecryption(Byte *stream,Byte *IV,Byte *fullKey,int size);函数,如下,stream数组是密文数组(Byte),IV为初始向量,fullkey为密钥扩展后的key,size是密文的长度,具体代码如下:
void counterModeDecryption(Byte *stream,Byte *IV,Byte *fullKey,int size){
//将解密后的明文保存在restream数组
Byte *restream = new Byte[size+1];
int cnt = 0;
for(int r = 0;r*16