H3C GRE over IPsec实验
GRE over IPsec VPN实验
- 一、拓扑图
- 二、组网需求
- 三、配置步骤
-
- 1.配置各设备IP地址
- 2.配置默认路由
- 3.配置DHCP
- 4.配置 GRE over IPsec VPN
-
- (1)在 R1 上配置 GRE over IPsec VPN
- (2)在 R3 上配置 GRE over IPsec VPN
- (3)在 R4 上配置 GRE over IPsec VPN
- 5. 配置 RIP
- 总结
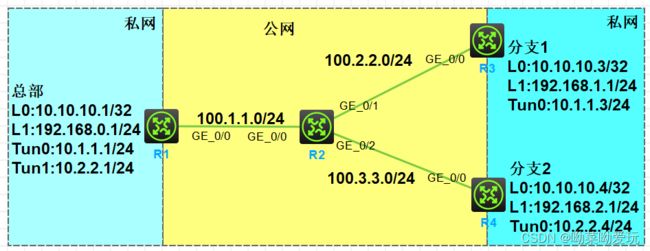
一、拓扑图
二、组网需求
- 某企业总部、分支1、分支2分别通过 R1,R3,R4 接入互联网,配置默认路由连通公网
- 按照图示配置 IP 地址,R1,R3,R4 分别配置 Loopback0 口匹配感兴趣流,Loopback1 口模拟业务网段
- 总部拥有固定公网地址,在 R2 上配置 DHCP,对 R3 和 R4 动态分配 IP 地址,IP 地址网段如图
- 总部、分支1、分支2配置 GRE over IPsec VPN 连通内网,要求总部使用模板来简化配置
- 总部和分支之间配置 RIPv2 传递内网路由
注:设备IP地址为标志网段+设备号,如R1的G0/0端口的IP地址为1.1.1.1/24
三、配置步骤
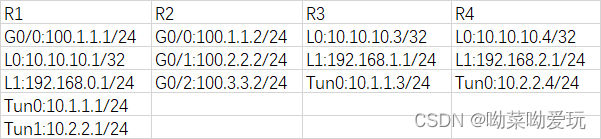
1.配置各设备IP地址
Tunnel口的IP地址配置(以Tun0为例):
[R1]interface Tunnel 0 mode gre
[R1-Tunnel0]ip address 10.1.1.1 24
2.配置默认路由
- 为R1配置默认路由,使全网可通
[R1]ip route-static 0.0.0.0 0 100.1.1.2
- 为R3配置默认路由,使全网可通
[R3]ip route-static 0.0.0.0 0 100.2.2.2
- 为R4配置默认路由,使全网可通
[R4]ip route-static 0.0.0.0 0 100.3.3.2
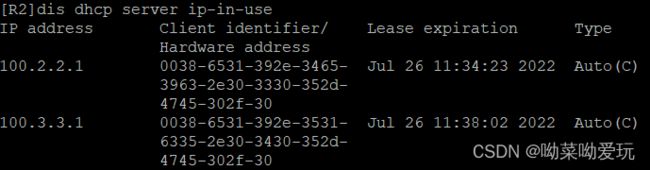
3.配置DHCP
在R2上配置DHCP,模拟运营商分配IP地址给R3、R4
- 开启 DHCP 服务
[R2]dhcp enable
[R2]interface GigabitEthernet 0/1
[R2-GigabitEthernet0/1]dhcp select server
[R2]interface GigabitEthernet 0/2
[R2-GigabitEthernet0/2]dhcp select server
- 配置 DHCP 地址池
[R2]dhcp server ip-pool 1
[R2-dhcp-pool-1]network 100.2.2.0 mask 255.255.255.0
[R2-dhcp-pool-1]gateway-list 100.2.2.2
[R2]dhcp server ip-pool 2
[R2-dhcp-pool-1]network 100.3.3.0 mask 255.255.255.0
[R2-dhcp-pool-1]gateway-list 100.3.3.2
- 在R3、R4上,开启端口获取DHCP地址
[R3]interface GigabitEthernet 0/0
[R3-GigabitEthernet0/0]ip address dhcp-alloc
[R4]interface GigabitEthernet 0/0
[R4-GigabitEthernet0/0]ip address dhcp-alloc
4.配置 GRE over IPsec VPN
(1)在 R1 上配置 GRE over IPsec VPN
- 在 R1 上配置GRE tunnel 口,指定源目IP为双方 LoopBack 口。
[R1]interface Tunnel0
[R1-Tunnel0]source LoopBack 0
[R1-Tunnel0]destination 10.10.10.3
[R1]interface Tunnel1
[R1-Tunnel1]source LoopBack 0
[R1-Tunnel1]destination 10.10.10.4
- 在 R1 上配置 FQDN 名为 zb
[R1]ike identity fqdn zb
- 在 R1 上创建 IKE 提议,使用默认配置即可
[R1]ike proposal 1
- 在 R1 上创建 IKE 预共享密钥
[R1]ike keychain fz
[R1-ike-keychain-fz]pre-shared-key hostname fz1 key simple 123
[R1-ike-keychain-fz]pre-shared-key hostname fz2 key simple 123
- 在 R1 上创建 IKE Profile
[R1]ike profile fz1
[R1-ike-profile-fz1]exchange-mode aggressive
[R1-ike-profile-fz1]match remote identity fqdn fz1
[R1-ike-profile-fz1]priority 1
[R1-ike-profile-fz1]keychain fz
[R1]ike profile fz2
[R1-ike-profile-wh]exchange-mode aggressive
[R1-ike-profile-wh]match remote identity fqdn fz2
[R1-ike-profile-wh]proposal 1
[R1-ike-profile-wh]keychain fz
- 在 R1 上创建 IPsec 转换集,对两个分支可以使用同一个转换集
[R1]ipsec transform-set fz
[R1-ipsec-transform-set-fz]esp authentication-algorithm sha1
[R1-ipsec-transform-set-fz]esp encryption-algorithm aes-cbc-128
- 在 R1 上分别创建对上海和武汉分支的 IPsec 策略模板
[R1]ipsec policy-template fz1 1
[R1-ipsec-policy-template-sh-1]transform-set fz
[R1-ipsec-policy-template-sh-1]ike-profile fz1
[R1]ipsec policy-template fz2 1
[R1-ipsec-policy-template-wh-1]transform-set fz
[R1-ipsec-policy-template-wh-1]ike-profile fz2
- 在 R1 上创建 IPsec 策略,绑定两个模板
[R1]ipsec policy fz 1 isakmp template fz1
[R1]ipsec policy fz 2 isakmp template fz2
- 在 R1 的公网接口上下发 IPsec 策略
[R1]interface GigabitEthernet 0/0
[R1-GigabitEthernet0/0]ipsec apply policy fz
(2)在 R3 上配置 GRE over IPsec VPN
- 在 R3 上配置 GRE Tunnel 口
[R3]interface Tunnel0
[R3-Tunnel0]source LoopBack 0
[R3-Tunnel0]destination 10.10.10.1
- 配置 ACL
[R3]acl advanced 3000
[R3-acl-ipv4-adv-3000]rule permit ip source 10.10.10.3 0 destination 10.10.10.1 0
- 在 R3 上配置 FQDN 名为 fz1
[R3]ike identity fqdn fz1
- 在 R3 上创建 IKE 提议
[R3]ike proposal 1
- 在 R3 上创建 IKE 预共享密钥,匹配对端公网地址
[R3]ike keychain zb
[R3-ike-keychain-zb]pre-shared-key address 100.1.1.1 key simple 123
- 在 R3 上创建 IKE Profile
[R3]ike profile zb
[R3-ike-profile-bj]exchange-mode aggressive
[R3-ike-profile-bj]match remote identity fqdn zb
[R3-ike-profile-bj]proposal 1
[R3-ike-profile-bj]keychain zb
- 在 R3 上创建 IPsec 转换集
[R3]ipsec transform-set zb
[R3-ipsec-transform-set-fz]esp authentication-algorithm sha1
[R3-ipsec-transform-set-fz]esp encryption-algorithm aes-cbc-128
- 在 R3 上创建 IPsec 策略
[R3]ipsec policy zb 1 isakmp
[R3-ipsec-policy-isakmp-zb-1]security acl 3000
[R3-ipsec-policy-isakmp-zb-1]remote-address 100.1.1.1
[R3-ipsec-policy-isakmp-zb-1]ike-profile zb
[R3-ipsec-policy-isakmp-zb-1]transform-set zb
- 在 R3 的公网接口上下发 IPsec 策略
[R3]interface GigabitEthernet 0/0
[R3-GigabitEthernet0/0]ipsec apply policy zb
(3)在 R4 上配置 GRE over IPsec VPN
- 在 R4 上配置 GRE Tunnel 口
[R4]interface Tunnel0
[R4-Tunnel0]source LoopBack 0
[R4-Tunnel0]destination 10.10.10.1
- 配置 ACL
[R4]acl advanced 3000
[R4-acl-ipv4-adv-3000]rule permit ip source 10.10.10.4 0 destination 10.10.10.1 0
- 在 R4 上配置 FQDN 名为 fz2
[R4]ike identity fqdn fz2
- 在 R4 上创建 IKE 提议
[R4]ike proposal 1
- 在 R4 上创建 IKE 预共享密钥,匹配对端公网地址
[R4]ike keychain zb
[R4-ike-keychain-zb]pre-shared-key address 100.1.1.1 key simple 123
- 在 R4 上创建 IKE Profile
[R4]ike profile zb
[R4-ike-profile-bj]exchange-mode aggressive
[R4-ike-profile-bj]match remote identity fqdn zb
[R4-ike-profile-bj]proposal 1
[R4-ike-profile-bj]keychain zb
- 在 R4 上创建 IPsec 转换集
[R4]ipsec transform-set zb
[R4-ipsec-transform-set-fz]esp authentication-algorithm sha1
[R4-ipsec-transform-set-fz]esp encryption-algorithm aes-cbc-128
- 在 R4 上创建 IPsec 策略
[R4]ipsec policy zb 1 isakmp
[R4-ipsec-policy-isakmp-zb-1]security acl 3000
[R4-ipsec-policy-isakmp-zb-1]remote-address 100.1.1.1
[R4-ipsec-policy-isakmp-zb-1]ike-profile zb
[R4-ipsec-policy-isakmp-zb-1]transform-set zb
- 在 R4 的公网接口上下发 IPsec 策略
[R4]interface GigabitEthernet 0/0
[R4-GigabitEthernet0/0]ipsec apply policy zb
5. 配置 RIP
- 在 R1,R3,R4 上分别配置 RIPv2,宣告 Tunnel 口网段和各自业务网段
[R1]rip
[R1-rip-1]version 2
[R1-rip-1]undo summary
[R1-rip-1]network 192.168.0.1 0.0.0.255
[R1-rip-1]network 10.1.1.0 0.0.0.255
[R1-rip-1]network 10.2.2.0 0.0.0.255
[R3]rip
[R3-rip-1]version 2
[R3-rip-1]undo summary
[R3-rip-1]network 192.168.1.0 0.0.0.255
[R3-rip-1]network 10.1.1.0 0.0.0.255
[R4]rip
[R4-rip-1]version 2
[R4-rip-1]undo summary
[R4-rip-1]network 192.168.2.0 0.0.0.255
[R4-rip-1]network 10.2.2.0 0.0.0.255
- 在 R1,R3,R4 上分别配置到达其他两个站点环回口的静态路由,下一跳指向公网
[R1]ip route-static 10.10.10.3 32 100.1.1.2
[R1]ip route-static 10.10.10.4 32 100.1.1.2
[R3]ip route-static 10.10.10.1 32 100.2.2.2
[R4]ip route-static 10.10.10.1 32 100.3.3.2
总结
注意:ipsec配置完成后,需通过ping触发sa。野蛮模式须用被动端ping主动端。
查看ike/ipse命令:display ike sa / display ipsec sa