简单易懂的Kubernetes(K8S)单节点二进制部署详细步骤
文章目录
- 一:环境部署
- 二:K8S部署
-
- (一)、ETCD组件部署
-
- 1、下载证书制作工具
- 2、下载cfssl官方包
- 3、开始制作证书
- 4、指定etcd三个节点之间的通信验证
- 5、生成ETCD证书 `server-key.pem server.pem`
- 6、将以上三个压缩包上传到 /root/k8s 目录中
- 7、证书拷贝
- 8、进入卡住状态等待其他节点加入
- 9、拷贝证书去其他节点
- 10、启动脚本拷贝其他节点
- 11、在node1节点与node2节点均需修改
- 13、启动
- 14、检查群集状态,在master1上进行检查
- (二)、docker引擎部署
-
- 1、安装docker的依赖环境
- 2、设置docker的镜像源(此处是阿里源)
- 3、安装docker
- 4、启动并设置为开启自启动
- 5、配置阿里云镜像加速
- 6、网络优化
- (三)、flannel网络配置
-
- 1、写入分配的子网段到ETCD中,供flannel使用
- 2、拷贝到所有node节点(只需要部署在node节点即可)
- 3、所有node节点操作解压
- 4、所有node节点创建k8s工作目录
- 5、开启flannel网络功能
- 6、配置docker连接flannel
- 7、重启docker服务
- 8、查看flannel网络
- 9、测试ping通对方docker0网卡 证明flannel起到路由作用
- (四)、部署master组件
-
- 1、api-server生成证书
- 2、生成k8s证书
- 3、解压kubernetes压缩包
- 4、复制关键命令文件
- 5、二进制文件,token,证书都准备好,开启apiserver
- 6、查看配置文件
- 7、启动scheduler服务
- 8、启动controller-manager
- 9、查看master 节点状态
- (五)、node节点部署
-
- 1、把 kubelet、kube-proxy拷贝到node节点上去
- 1、复制node.zip到/root目录下再解压
- 1、获取token信息
- 2、配置文件修改为tokenID
- 3、设置环境变量(可以写入到/etc/profile中)
- 4、生成配置文件
- 5、拷贝配置文件到node节点
- 6、创建bootstrap角色赋予权限用于连接apiserver请求签名(关键)
- 1、执行kubelet.sh脚本
- 2、检查kubelet服务启动
- 1、检查到node01节点的请求
- 2、继续查看证书状态
- 3、查看群集节点,成功加入node01节点
- 1、启动proxy服务
- 1、在node01节点操作
- 2、把kubelet,kube-proxy的service文件拷贝到node2中
- 1、首先删除复制过来的证书,等会node02会自行申请证书
- 2、修改配置文件kubelet kubelet.config kube-proxy(三个配置文件)
- 3、启动服务
- 1、查看node2请求
- 2、授权许可加入群集
- 3、查看群集中的节点
- (六)、组件证书级配置参数
-
- 1、ca.pem & ca-key.pem & ca.csr
- 2、token.csv
- 3、bootstrap.kubeconfig
- 4、kubectl
- 5、kubelet
- 6、kube-apiserver
- 7、kube-controller-manager
- 8、kube-scheduler && kube-proxy
一:环境部署
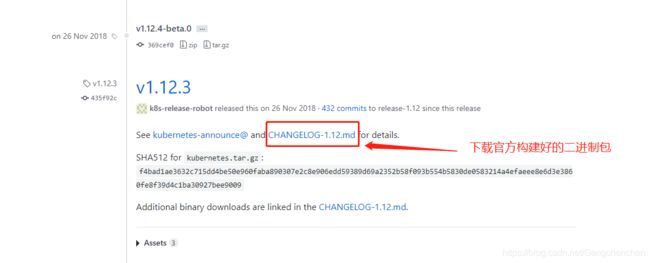
官网地址:https://github.com/kubernetes/kubernetes/releases?after=v1.13.1

二:K8S部署
Master1:192.168.200.10/24 kube-apiserver kube-controller-manager kube-scheduler etcd
Node01:192.168.200.40/24 kubelet kube-proxy docker flannel etcd
Node02:192.168.200.60/24 kubelet kube-proxy docker flannel etcd
(一)、ETCD组件部署
master1上进行操作
[root@master1 ~]# mkdir k8s
[root@master1 ~]# cd k8s/
[root@master1 k8s]# ls #将以下两个脚本文件上传到该目录下
etcd-cert.sh etcd.sh #etcd-cert.sh为etcd证书的脚本,etcd.sh为etcd服务的脚本
[root@master1 k8s]# mkdir etcd-cert
[root@master1 k8s]# ls
etcd-cert etcd-cert.sh etcd.sh
[root@master1 k8s]# mv etcd-cert.sh etcd-cert
1、下载证书制作工具
[root@master1 k8s]# vim cfssl.sh
curl -L https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 -o /usr/local/bin/cfssl
curl -L https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 -o /usr/local/bin/cfssljson
curl -L https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 -o /usr/local/bin/cfssl-certinfo
chmod +x /usr/local/bin/cfssl /usr/local/bin/cfssljson /usr/local/bin/cfssl-certinfo
2、下载cfssl官方包
[root@master1 k8s]# bash cfssl.sh
[root@master1 k8s]# ls /usr/local/bin/
cfssl cfssl-certinfo cfssljson
3、开始制作证书
//cfssl 生成证书工具 , cfssljson通过传入json文件生成证书,cfssl-certinfo查看证书信息
#定义ca证书
[root@master1 ~]# cd /root/k8s/etcd-cert
cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"www": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
#实现证书签名
[root@master1 ~]# cd /root/k8s/etcd-cert
cat > ca-csr.json <<EOF
{
"CN": "etcd CA",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF
#生产证书,生成ca-key.pem ca.pem
[root@master1 etcd-cert]# cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
2021/04/10 22:53:30 [INFO] generating a new CA key and certificate from CSR
2021/04/10 22:53:30 [INFO] generate received request
2021/04/10 22:53:30 [INFO] received CSR
2021/04/10 22:53:30 [INFO] generating key: rsa-2048
2021/04/10 22:53:30 [INFO] encoded CSR
2021/04/10 22:53:30 [INFO] signed certificate with serial number 397125830926114737701706075410049927608256756699
4、指定etcd三个节点之间的通信验证
[root@master1 ~]# cd /root/k8s/etcd-cert
cat > server-csr.json <<EOF
{
"CN": "etcd",
"hosts": [
"192.168.200.10",
"192.168.200.40",
"192.168.200.60"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF
5、生成ETCD证书 server-key.pem server.pem
[root@master1 ~]# cd /root/k8s/etcd-cert
[root@master1 etcd-cert]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare server
2021/04/10 22:57:45 [INFO] generate received request
2021/04/10 22:57:45 [INFO] received CSR
2021/04/10 22:57:45 [INFO] generating key: rsa-2048
2021/04/10 22:57:45 [INFO] encoded CSR
2021/04/10 22:57:45 [INFO] signed certificate with serial number 219342381748991728851284184667512408378336584859
2021/04/10 22:57:45 [WARNING] This certificate lacks a "hosts" field. This makes it unsuitable for
websites. For more information see the Baseline Requirements for the Issuance and Management
of Publicly-Trusted Certificates, v.1.1.6, from the CA/Browser Forum (https://cabforum.org);
specifically, section 10.2.3 ("Information Requirements").
[root@master1 etcd-cert]# ls
ca-config.json ca-key.pem server.csr server.pem
ca.csr ca.pem server-csr.json
ca-csr.json etcd-cert.sh server-key.pem
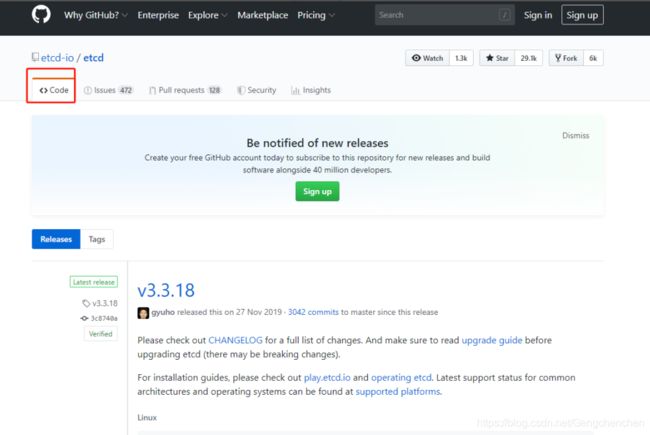
#ETCD 二进制包地址
https://github.com/etcd-io/etcd/releases

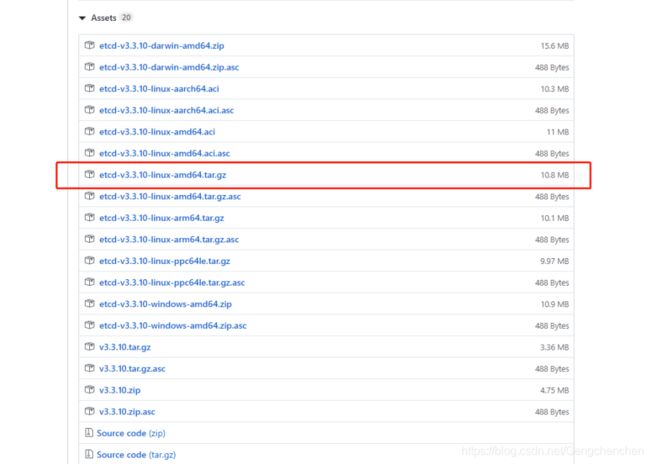
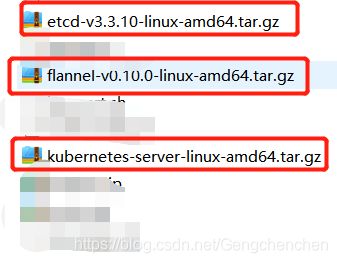
6、将以上三个压缩包上传到 /root/k8s 目录中
[root@master1 etcd-cert]# cd ~/k8s/
[root@master1 k8s]# ls
cfssl.sh etcd.sh flannel-v0.10.0-linux-amd64.tar.gz
etcd-cert etcd-v3.3.10-linux-amd64.tar.gz kubernetes-server-linux-amd64.tar.gz
[root@master1 k8s]# tar zxvf etcd-v3.3.10-linux-amd64.tar.gz
[root@master1 k8s]# ls etcd-v3.3.10-linux-amd64
Documentation etcdctl README.md
etcd README-etcdctl.md READMEv2-etcdctl.md
[root@master1 k8s]# mkdir /opt/etcd/{cfg,bin,ssl} -p //cfg:配置文件,bin:命令文件,ssl:证书
[root@master1 k8s]# mv etcd-v3.3.10-linux-amd64/etcd etcd-v3.3.10-linux-amd64/etcdctl /opt/etcd/bin/
[root@master1 k8s]# ls /opt/etcd/bin/
etcd etcdctl
7、证书拷贝
[root@master1 k8s]# cp etcd-cert/*.pem /opt/etcd/ssl/
[root@master1 k8s]# ls /opt/etcd/ssl/
ca-key.pem ca.pem server-key.pem server.pem
8、进入卡住状态等待其他节点加入
[root@master1 k8s]# bash etcd.sh etcd01 192.168.200.10 etcd02=https://192.168.200.40:2380,etcd03=https://192.168.200.60:2380
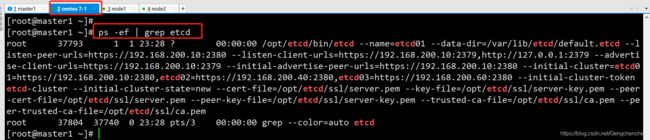
[root@localhost ~]# ps -ef | grep etcd
9、拷贝证书去其他节点
[root@master1 k8s]# scp -r /opt/etcd/ root@192.168.200.40:/opt/
[root@master1 k8s]# scp -r /opt/etcd/ root@192.168.200.60:/opt/
10、启动脚本拷贝其他节点
[root@master1 ~]# scp /usr/lib/systemd/system/etcd.service root@192.168.200.40:/usr/lib/systemd/system/
[root@master1 ~]# scp /usr/lib/systemd/system/etcd.service root@192.168.200.60:/usr/lib/systemd/system/
11、在node1节点与node2节点均需修改
###在node1节点修改
[root@node1 system]# cd /opt/etcd/cfg/
[root@node1 cfg]# vim etcd
#[Member]
ETCD_NAME="etcd02"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.200.40:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.200.40:2379"
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.200.40:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.200.40:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.200.10:2380,etcd02=https://192.168.200.40:2380,etcd03=https://192.168.200.60:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
###在node2节点修改
[root@node2 system]# cd /opt/etcd/cfg/
[root@node2 cfg]# vim etcd
#[Member]
ETCD_NAME="etcd03"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.200.60:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.200.60:2379"
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.200.60:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.200.60:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.200.10:2380,etcd02=https://192.168.200.40:2380,etcd03=https://192.168.200.60:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
13、启动
#首先在master1节点上进行启动
[root@master1 ~]# cd /root/k8s/
[root@master1 k8s]# bash etcd.sh etcd01 192.168.200.10 etcd02=https://192.168.200.40:2380,etcd03=https://192.168.200.60:2380
#接着在node1和node2节点分别进行启动
[root@node1 cfg]# systemctl start etcd.service
[root@node2 cfg]# systemctl start etcd.service
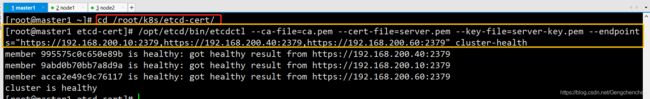
14、检查群集状态,在master1上进行检查
[root@master1 ~]# cd /root/k8s/etcd-cert/
[root@master1 etcd-cert]# /opt/etcd/bin/etcdctl --ca-file=ca.pem --cert-file=server.pem --key-file=server-key.pem --endpoints="https://192.168.200.10:2379,https://192.168.200.40:2379,https://192.168.200.60:2379" cluster-health
member 995575c0c650e89b is healthy: got healthy result from https://192.168.200.40:2379
member 9abd0b70bb7a8d9a is healthy: got healthy result from https://192.168.200.10:2379
member acca2e49c9c76117 is healthy: got healthy result from https://192.168.200.60:2379
cluster is healthy
(二)、docker引擎部署
所有node节点部署docker引擎
1、安装docker的依赖环境
yum -y install yum-utils device-mapper-persistent-data lvm2
2、设置docker的镜像源(此处是阿里源)
yum-config-manager --add-repo http://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo
3、安装docker
yum makecache fast
yum -y install docker-ce docker-ce-cli containerd.io
4、启动并设置为开启自启动
systemctl start docker #启动docker
systemctl enable docker #设置开机自启动
5、配置阿里云镜像加速
tee /etc/docker/daemon.json <<-'EOF'
{
"registry-mirrors": ["https://p3pqujwc.mirror.aliyuncs.com"]
}
EOF
systemctl daemon-reload
systemctl restart docker
6、网络优化
echo 'net.ipv4.ip_forward=1' >> /etc/sysctl.conf
sysctl -p
service network restart
systemctl restart docker
(三)、flannel网络配置
----master1上进行操作-----
1、写入分配的子网段到ETCD中,供flannel使用
[root@master1 ~]# cd k8s/etcd-cert/
[root@master1 etcd-cert]# /opt/etcd/bin/etcdctl --ca-file=ca.pem --cert-file=server.pem --key-file=server-key.pem --endpoints="https://192.168.200.10:2379,https://192.168.200.40:2379,https://192.168.200.60:2379" set /coreos.com/network/config '{ "Network": "172.17.0.0/16", "Backend": {"Type": "vxlan"}}'
{ "Network": "172.17.0.0/16", "Backend": {"Type": "vxlan"}}
#查看写入的信息
[root@master1 etcd-cert]# /opt/etcd/bin/etcdctl --ca-file=ca.pem --cert-file=server.pem --key-file=server-key.pem --endpoints="https://192.168.200.10:2379,https://192.168.200.40:2379,https://192.168.200.60:2379" get /coreos.com/network/config
{ "Network": "172.17.0.0/16", "Backend": {"Type": "vxlan"}}
2、拷贝到所有node节点(只需要部署在node节点即可)
[root@master1 ~]# cd k8s/
[root@master1 k8s]# ls
cfssl.sh
etcd-cert
etcd.sh
etcd-v3.3.10-linux-amd64
etcd-v3.3.10-linux-amd64.tar.gz
flannel-v0.10.0-linux-amd64.tar.gz
kubernetes-server-linux-amd64.tar.gz
[root@master1 k8s]# scp flannel-v0.10.0-linux-amd64.tar.gz root@192.168.200.40:/root
[root@master1 k8s]# scp flannel-v0.10.0-linux-amd64.tar.gz root@192.168.200.60:/root
3、所有node节点操作解压
tar zxvf flannel-v0.10.0-linux-amd64.tar.gz
4、所有node节点创建k8s工作目录
mkdir /opt/kubernetes/{cfg,bin,ssl} -p
mv mk-docker-opts.sh flanneld /opt/kubernetes/bin/
[root@localhost ~]# vim flannel.sh
#!/bin/bash
ETCD_ENDPOINTS=${1:-"http://127.0.0.1:2379"}
cat <<EOF >/opt/kubernetes/cfg/flanneld
FLANNEL_OPTIONS="--etcd-endpoints=${ETCD_ENDPOINTS} \
-etcd-cafile=/opt/etcd/ssl/ca.pem \
-etcd-certfile=/opt/etcd/ssl/server.pem \
-etcd-keyfile=/opt/etcd/ssl/server-key.pem"
EOF
cat <<EOF >/usr/lib/systemd/system/flanneld.service
[Unit]
Description=Flanneld overlay address etcd agent
After=network-online.target network.target
Before=docker.service
[Service]
Type=notify
EnvironmentFile=/opt/kubernetes/cfg/flanneld
ExecStart=/opt/kubernetes/bin/flanneld --ip-masq \$FLANNEL_OPTIONS
ExecStartPost=/opt/kubernetes/bin/mk-docker-opts.sh -k DOCKER_NETWORK_OPTIONS -d /run/flannel/subnet.env
Restart=on-failure
[Install]
WantedBy=multi-user.target
EOF
systemctl daemon-reload
systemctl enable flanneld
systemctl restart flanneld
5、开启flannel网络功能
[root@localhost ~]# bash flannel.sh https://192.168.200.10:2379,https://192.168.200.40:2379,https://192.168.200.60:2379
6、配置docker连接flannel
[root@localhost ~]# vim /usr/lib/systemd/system/docker.service
[Service]
Type=notify
# the default is not to use systemd for cgroups because the delegate issues still
# exists and systemd currently does not support the cgroup feature set required
# for containers run by docker
EnvironmentFile=/run/flannel/subnet.env #添加此行
ExecStart=/usr/bin/dockerd $DOCKER_NETWORK_OPTIONS -H fd:// --containerd=/run/containerd/containerd.sock #修改此行
ExecReload=/bin/kill -s HUP $MAINPID
TimeoutSec=0
RestartSec=2
Restart=always
[root@localhost ~]# cat /run/flannel/subnet.env
DOCKER_OPT_BIP="--bip=172.17.42.1/24"
DOCKER_OPT_IPMASQ="--ip-masq=false"
DOCKER_OPT_MTU="--mtu=1450"
//说明:bip指定启动时的子网
DOCKER_NETWORK_OPTIONS=" --bip=172.17.42.1/24 --ip-masq=false --mtu=1450"
7、重启docker服务
systemctl daemon-reload
systemctl restart docker
8、查看flannel网络
[root@node1 ~]# ifconfig
docker0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
inet 172.17.42.1 netmask 255.255.255.0 broadcast 172.17.42.255
ether 02:42:92:10:6f:24 txqueuelen 0 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
flannel.1: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450
inet 172.17.42.0 netmask 255.255.255.255 broadcast 0.0.0.0
inet6 fe80::3833:cff:fe69:56f6 prefixlen 64 scopeid 0x20<link>
ether 3a:33:0c:69:56:f6 txqueuelen 0 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 26 overruns 0 carrier 0 collisions 0
[root@node2 ~]# ifconfig
docker0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
inet 172.17.70.1 netmask 255.255.255.0 broadcast 172.17.70.255
ether 02:42:75:18:1e:44 txqueuelen 0 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
flannel.1: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450
inet 172.17.70.0 netmask 255.255.255.255 broadcast 0.0.0.0
inet6 fe80::8cd8:34ff:fec1:1dbb prefixlen 64 scopeid 0x20<link>
ether 8e:d8:34:c1:1d:bb txqueuelen 0 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 26 overruns 0 carrier 0 collisions 0
9、测试ping通对方docker0网卡 证明flannel起到路由作用
[root@node1 ~]# ping 172.17.70.1
PING 172.17.70.1 (172.17.70.1) 56(84) bytes of data.
64 bytes from 172.17.70.1: icmp_seq=1 ttl=64 time=0.211 ms
64 bytes from 172.17.70.1: icmp_seq=2 ttl=64 time=0.257 ms
64 bytes from 172.17.70.1: icmp_seq=3 ttl=64 time=0.228 ms
64 bytes from 172.17.70.1: icmp_seq=4 ttl=64 time=0.171 ms
[root@node1 ~]# docker run -it centos:7 /bin/bash #node1和node2都运行该命令
[root@7c733f24ebeb /]# yum install net-tools -y #node1和node2都运行该命令
[root@7c733f24ebeb /]# ifconfig
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450
inet 172.17.42.2 netmask 255.255.255.0 broadcast 172.17.42.255
ether 02:42:ac:11:2a:02 txqueuelen 0 (Ethernet)
RX packets 20185 bytes 15437540 (14.7 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 9598 bytes 521494 (509.2 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
loop txqueuelen 1 (Local Loopback)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@f4ed072201aa /]# ifconfig
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450
inet 172.17.70.2 netmask 255.255.255.0 broadcast 172.17.70.255
ether 02:42:ac:11:46:02 txqueuelen 0 (Ethernet)
RX packets 20233 bytes 15440288 (14.7 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 9303 bytes 505678 (493.8 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
loop txqueuelen 1 (Local Loopback)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
//再次测试ping通两个node中的centos:7容器
[root@7c733f24ebeb /]# ping 172.17.70.2
PING 172.17.70.2 (172.17.70.2) 56(84) bytes of data.
64 bytes from 172.17.70.2: icmp_seq=1 ttl=62 time=0.364 ms
64 bytes from 172.17.70.2: icmp_seq=2 ttl=62 time=0.245 ms
64 bytes from 172.17.70.2: icmp_seq=3 ttl=62 time=0.236 ms
###注意:如果ping时卡住,可以先退出容器,然后重启flanneld、network和docker,然后重新进入容器,就可以ping通了。(所有节点都要进行重启)
(四)、部署master组件
1、api-server生成证书
#在master上操作
[root@master1 ~]# cd k8s/
#将 master.zip上传到该目录下进行解压
[root@master1 k8s]# unzip master.zip
[root@master1 k8s]# chmod +x controller-manager.sh
[root@master1 k8s]# mkdir /opt/kubernetes/{cfg,bin,ssl} -p
[root@master1 k8s]# mkdir k8s-cert #创建k8s证书存放目录
[root@master1 k8s]# cd k8s-cert/
[root@master1 k8s-cert]# ls #讲写好的k8s-cert.sh脚本上传到该目录下
k8s-cert.sh
#查看并修改k8s-cert.sh脚本
cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"kubernetes": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
cat > ca-csr.json <<EOF
{
"CN": "kubernetes",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
#-----------------------
cat > server-csr.json <<EOF
{
"CN": "kubernetes",
"hosts": [
"10.0.0.1",
"127.0.0.1",
"192.168.200.10", //master1
"192.168.200.20", //master2
"192.168.200.100", //vip
"192.168.200.70", //lb (master)
"192.168.200.80", //lb (backup)
"kubernetes",
"kubernetes.default",
"kubernetes.default.svc",
"kubernetes.default.svc.cluster",
"kubernetes.default.svc.cluster.local"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes server-csr.json | cfssljson -bare server
#-----------------------
cat > admin-csr.json <<EOF
{
"CN": "admin",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing",
"O": "system:masters",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes admin-csr.json | cfssljson -bare admin
#-----------------------
cat > kube-proxy-csr.json <<EOF
{
"CN": "system:kube-proxy",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes kube-proxy-csr.json | cfssljson -bare kube-proxy
2、生成k8s证书
[root@master1 k8s-cert]# bash k8s-cert.sh
[root@master1 k8s-cert]# ls *.pem #
admin-key.pem ca.pem server-key.pem
admin.pem kube-proxy-key.pem server.pem
ca-key.pem kube-proxy.pem
[root@master1 k8s-cert]# cp ca*pem server*pem /opt/kubernetes/ssl/
[root@localhost k8s-cert]# cd ..
3、解压kubernetes压缩包
[root@master1 k8s]# tar zxvf kubernetes-server-linux-amd64.tar.gz
[root@master1 k8s]# cd /root/k8s/kubernetes/server/bin
4、复制关键命令文件
[root@master1 bin]# cp kube-apiserver kubectl kube-controller-manager kube-scheduler /opt/kubernetes/bin/
[root@master1 bin]# cd /root/k8s/
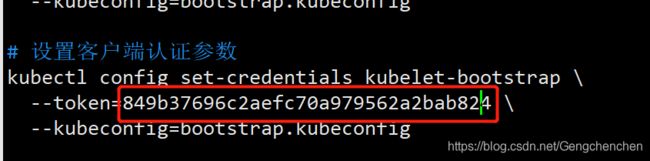
[root@master1 k8s]# head -c 16 /dev/urandom | od -An -t x | tr -d ' '
849b37696c2aefc70a979562a2bab824
#使用 head -c 16 /dev/urandom | od -An -t x | tr -d ' ' 可以随机生成序列号
[root@master1 k8s]# vim /opt/kubernetes/cfg/token.csv
849b37696c2aefc70a979562a2bab824,kubelet-bootstrap,10001,"system:kubelet-bootstrap"
5、二进制文件,token,证书都准备好,开启apiserver
[root@master1 k8s]# bash apiserver.sh 192.168.200.10 https://192.168.200.10:2379,https://192.168.200.40:2379,https://192.168.200.60:2379
#检查进程是否启动成功
[root@master1 k8s]# ps aux | grep kube
root 55228 0.0 0.0 112676 984 pts/2 R+ 17:20 0:00 grep --color=auto kube
6、查看配置文件
[root@master1 k8s]# cat /opt/kubernetes/cfg/kube-apiserver
KUBE_APISERVER_OPTS="--logtostderr=true \
--v=4 \
--etcd-servers=https://192.168.200.10:2379,https://192.168.200.40:2379,https://192.168.200.60:2379 \
--bind-address=192.168.200.10 \
--secure-port=6443 \
--advertise-address=192.168.200.10 \
--allow-privileged=true \
--service-cluster-ip-range=10.0.0.0/24 \
--enable-admission-plugins=NamespaceLifecycle,LimitRanger,ServiceAccount,ResourceQuota,NodeRestriction \
--authorization-mode=RBAC,Node \
--kubelet-https=true \
--enable-bootstrap-token-auth \
--token-auth-file=/opt/kubernetes/cfg/token.csv \
--service-node-port-range=30000-50000 \
--tls-cert-file=/opt/kubernetes/ssl/server.pem \
--tls-private-key-file=/opt/kubernetes/ssl/server-key.pem \
--client-ca-file=/opt/kubernetes/ssl/ca.pem \
--service-account-key-file=/opt/kubernetes/ssl/ca-key.pem \
--etcd-cafile=/opt/etcd/ssl/ca.pem \
--etcd-certfile=/opt/etcd/ssl/server.pem \
--etcd-keyfile=/opt/etcd/ssl/server-key.pem"
#监听的https端口
[root@master1 k8s]# netstat -ntap | grep 6443
tcp 0 0 192.168.200.10:6443 0.0.0.0:* LISTEN 55290/kube-apiserve
tcp 0 0 192.168.200.10:54566 192.168.200.10:6443 ESTABLISHED 55290/kube-apiserve
tcp 0 0 192.168.200.10:6443 192.168.200.10:54566 ESTABLISHED 55290/kube-apiserve
7、启动scheduler服务
[root@master1 k8s]# ./scheduler.sh 127.0.0.1
[root@master1 k8s]# ps aux | grep ku
8、启动controller-manager
[root@master1 k8s]# ./controller-manager.sh 127.0.0.1
9、查看master 节点状态
[root@master1 k8s]# /opt/kubernetes/bin/kubectl get cs
NAME STATUS MESSAGE ERROR
controller-manager Healthy ok
scheduler Healthy ok
etcd-1 Healthy {"health":"true"}
etcd-0 Healthy {"health":"true"}
etcd-2 Healthy {"health":"true"}
(五)、node节点部署
#master上操作
1、把 kubelet、kube-proxy拷贝到node节点上去
[root@master1 ~]# cd /root/k8s/kubernetes/server/bin
[root@master1 bin]# scp kubelet kube-proxy root@192.168.200.40:/opt/kubernetes/bin/
root@192.168.200.40's password:
kubelet 100% 168MB 97.0MB/s 00:01
kube-proxy 100% 48MB 93.9MB/s 00:00
[root@master1 bin]# scp kubelet kube-proxy root@192.168.200.60:/opt/kubernetes/bin/
root@192.168.200.60's password:
kubelet 100% 168MB 96.5MB/s 00:01
kube-proxy 100% 48MB 102.6MB/s 00:00
#nod01节点操作
1、复制node.zip到/root目录下再解压
[root@node1 ~]# ls #将node.zip上传到/root目录下
anaconda-ks.cfg node.zip 视频 音乐
flannel.sh README.md 图片 桌面
flannel-v0.10.0-linux-amd64.tar.gz 公共 文档
initial-setup-ks.cfg 模板 下载
#解压node.zip,获得kubelet.sh proxy.sh
[root@node1 ~]# unzip node.zip
#在master上操作
[root@master1 k8s]# mkdir kubeconfig
[root@master1 k8s]# cd kubeconfig/
#拷贝kubeconfig.sh文件到该目录下,并进行重命名
[root@master1 kubeconfig]# mv kubeconfig.sh kubeconfig
[root@master1 kubeconfig]# vim kubeconfig
----------------删除以下部分----------------------------------------------------------------------
# 创建 TLS Bootstrapping Token
#BOOTSTRAP_TOKEN=$(head -c 16 /dev/urandom | od -An -t x | tr -d ' ')
BOOTSTRAP_TOKEN=0fb61c46f8991b718eb38d27b605b008
cat > token.csv <<EOF
${BOOTSTRAP_TOKEN},kubelet-bootstrap,10001,"system:kubelet-bootstrap"
EOF
1、获取token信息
[root@master1 kubeconfig]# cat /opt/kubernetes/cfg/token.csv
849b37696c2aefc70a979562a2bab824,kubelet-bootstrap,10001,"system:kubelet-bootstrap"
2、配置文件修改为tokenID
[root@master1 kubeconfig]# vim kubeconfig
kubectl config set-credentials kubelet-bootstrap \
--token=849b37696c2aefc70a979562a2bab824 \ #修改此处
--kubeconfig=bootstrap.kubeconfig
3、设置环境变量(可以写入到/etc/profile中)
[root@master1 kubeconfig]# vim /etc/profile
export PATH=$PATH:/opt/kubernetes/bin/ #将此行添加在结尾处
[root@master1 kubeconfig]# source /etc/profile
[root@master1 kubeconfig]# kubectl get cs
NAME STATUS MESSAGE ERROR
scheduler Healthy ok
etcd-1 Healthy {"health":"true"}
etcd-2 Healthy {"health":"true"}
controller-manager Healthy ok
etcd-0 Healthy {"health":"true"}
4、生成配置文件
[root@master1 kubeconfig]# bash kubeconfig 192.168.200.10 /root/k8s/k8s-cert/
[root@master1 kubeconfig]# ls
bootstrap.kubeconfig kubeconfig kube-proxy.kubeconfig
5、拷贝配置文件到node节点
root@master1 kubeconfig]# scp bootstrap.kubeconfig kube-proxy.kubeconfig root@192.168.200.40:/opt/kubernetes/cfg/
root@192.168.200.40's password:
bootstrap.kubeconfig 100% 2168 2.3MB/s 00:00
kube-proxy.kubeconfig 100% 6270 7.4MB/s 00:00
[root@master1 kubeconfig]# scp bootstrap.kubeconfig kube-proxy.kubeconfig root@192.168.200.60:/opt/kubernetes/cfg/
root@192.168.200.60's password:
bootstrap.kubeconfig 100% 2168 1.8MB/s 00:00
kube-proxy.kubeconfig 100% 6270 6.9MB/s 00:00
6、创建bootstrap角色赋予权限用于连接apiserver请求签名(关键)
[root@master1 kubeconfig]# kubectl create clusterrolebinding kubelet-bootstrap --clusterrole=system:node-bootstrapper --user=kubelet-bootstrap
#在node01节点上操作
1、执行kubelet.sh脚本
[root@node1 ~]# bash kubelet.sh 192.168.200.40
2、检查kubelet服务启动
[root@node1 ~]# ps aux | grep kube
root 80970 1.0 2.2 369632 42436 ? Ssl 19:24 0:00 /opt/kubernetes/bin/kubelet --logtostderr=true --v=4 --hostname-override=192.168.200.40 --kubeconfig=/opt/kubernetes/cfg/kubelet.kubeconfig --bootstrap-kubeconfig=/opt/kubernetes/cfg/bootstrap.kubeconfig --config=/opt/kubernetes/cfg/kubelet.config --cert-dir=/opt/kubernetes/ssl --pod-infra-container-image=registry.cn-hangzhou.aliyuncs.com/google-containers/pause-amd64:3.0
root 80988 0.0 0.0 112676 984 pts/2 R+ 19:25 0:00 grep --color=auto kube
#master上操作
1、检查到node01节点的请求
[root@master1 kubeconfig]# kubectl get csr
NAME AGE REQUESTOR CONDITION
node-csr-ROXvPI34y36KB5tjPw2YWHro-g7s9u-9AYDkt7kd_fQ 98s kubelet-bootstrap Pending
#Pending(等待集群给该节点颁发证书)
[root@master1 kubeconfig]# kubectl certificate approve node-csr-ROXvPI34y36KB5tjPw2YWHro-g7s9u-9AYDkt7kd_fQ #此处的序列号为上面使用kubectl get csr显示的NAME
2、继续查看证书状态
[root@master1 kubeconfig]# kubectl get csr
NAME AGE REQUESTOR CONDITION
node-csr-ROXvPI34y36KB5tjPw2YWHro-g7s9u-9AYDkt7kd_fQ 4m57s kubelet-bootstrap Approved,Issued
#Approved,Issued(已经被允许加入群集)
3、查看群集节点,成功加入node01节点
[root@master1 kubeconfig]# kubectl get node
NAME STATUS ROLES AGE VERSION
192.168.200.40 Ready <none> 67s v1.12.3
#在node01节点操作
1、启动proxy服务
[root@node1 ~]# bash proxy.sh 192.168.200.40
root@node1 ~]# systemctl status kube-proxy.service #查看是否启动成功
#node02节点部署
1、在node01节点操作
#把现成的/opt/kubernetes目录复制到其他节点进行修改即可
[root@node1 ~]# scp -r /opt/kubernetes/ root@192.168.200.60:/opt/
2、把kubelet,kube-proxy的service文件拷贝到node2中
[root@node1 ~]# scp /usr/lib/systemd/system/{kubelet,kube-proxy}.service root@192.168.200.60:/usr/lib/systemd/system/
#在node02上操作,进行修改
1、首先删除复制过来的证书,等会node02会自行申请证书
[root@node2 ~]# cd /opt/kubernetes/ssl/
[root@node2 ssl]# ls
kubelet-client-2021-04-13-19-29-15.pem kubelet.crt
kubelet-client-current.pem kubelet.key
[root@node2 ssl]# rm -rf *
2、修改配置文件kubelet kubelet.config kube-proxy(三个配置文件)
[root@node2 ssl]# cd ../cfg/
[root@node2 cfg]# vim kubelet
KUBELET_OPTS="--logtostderr=true \
--v=4 \
--hostname-override=192.168.200.60 \ #修改为node2自己的IP
--kubeconfig=/opt/kubernetes/cfg/kubelet.kubeconfig \
--bootstrap-kubeconfig=/opt/kubernetes/cfg/bootstrap.kubeconfig \
--config=/opt/kubernetes/cfg/kubelet.config \
--cert-dir=/opt/kubernetes/ssl \
--pod-infra-container-image=registry.cn-hangzhou.aliyuncs.com/google-containers/pause-amd64:3.0"
[root@node2 cfg]# vim kubelet.config
kind: KubeletConfiguration
apiVersion: kubelet.config.k8s.io/v1beta1
address: 192.168.200.60 #修改为自己的IP
port: 10250
readOnlyPort: 10255
cgroupDriver: cgroupfs
clusterDNS:
- 10.0.0.2
clusterDomain: cluster.local.
failSwapOn: false
authentication:
anonymous:
enabled: true
[root@node2 cfg]# vim kube-proxy
KUBE_PROXY_OPTS="--logtostderr=true \
--v=4 \
--hostname-override=192.168.200.60 \ #修改为自己的IP
--cluster-cidr=10.0.0.0/24 \
--proxy-mode=ipvs \
--kubeconfig=/opt/kubernetes/cfg/kube-proxy.kubeconfig"
3、启动服务
[root@node2 cfg]# systemctl start kubelet.service
[root@node2 cfg]# systemctl enable kubelet.service
Created symlink from /etc/systemd/system/multi-user.target.wants/kubelet.service to /usr/lib/systemd/system/kubelet.service.
[root@node2 cfg]# systemctl start kube-proxy.service
[root@node2 cfg]# systemctl enable kube-proxy.service
Created symlink from /etc/systemd/system/multi-user.target.wants/kube-proxy.service to /usr/lib/systemd/system/kube-proxy.service.
#在master上操作
1、查看node2请求
[root@master1 kubeconfig]# kubectl get csr
NAME AGE REQUESTOR CONDITION
node-csr-ROXvPI34y36KB5tjPw2YWHro-g7s9u-9AYDkt7kd_fQ 16m kubelet-bootstrap Approved,Issued
node-csr-WpTFLoUV_yPjqF6SvuiX4OwChJWqirvgHtLDoI7ZMVI 68s kubelet-bootstrap Pending
2、授权许可加入群集
[root@master1 kubeconfig]# kubectl certificate approve node-csr-WpTFLoUV_yPjqF6SvuiX4OwChJWqirvgHtLDoI7ZMVI #注意修改序列号
3、查看群集中的节点
[root@master1 kubeconfig]# kubectl get node
NAME STATUS ROLES AGE VERSION
192.168.200.40 Ready <none> 12m v1.12.3
192.168.200.60 Ready <none> 18s v1.12.3
(六)、组件证书级配置参数
1、ca.pem & ca-key.pem & ca.csr
建立完整TLS加密通信,需要有一个CA认证机构,会向客户端下发根证书、服务端证书以及签名私钥给客户端。ca.pem & ca-key.pem & ca.csr组成了一个自签名的CA机构。
| 证书名称 | 作用 |
|---|---|
| ca.pem | CA根证书文件 |
| ca-key.pem | 服务端私钥,用于对客户端请求的解密和签名 |
| ca.csr | 证书签名请求,用于交叉签名或重新签名 |
2、token.csv
该文件为一个用户的描述文件,基本格式为 Token,用户名,UID,用户组;这个文件在 apiserver 启动时被 apiserver 加载,然后就相当于在集群内创建了一个这个用户;接下来就可以用 RBAC 给他授权
3、bootstrap.kubeconfig
该文件中内置了 token.csv 中用户的 Token,以及 apiserver CA 证书;kubelet 首次启动会加载此文件,使用 apiserver CA 证书建立与 apiserver 的 TLS 通讯,使用其中的用户 Token 作为身份标识向apiserver 发起 CSR 请求
4、kubectl
kubectl只是个go编写的可执行程序,只要为kubectl配置合适的kubeconfig,就可以在集群中的任意节点使用 。kubectl的权限为admin,具有访问kubernetes所有api的权限。
| 证书名称 | 作用 |
|---|---|
| ca.pem | CA根证书 |
| admin.pem | kubectl的TLS认证证书,具有admin权限 |
| admin-key.pem | kubectl的TLS认证私钥 |
- –certificate-authority=/opt/kubernetes/ssl/ca.pem 设置了该集群的根证书路径,
- –embed-certs为true表示将–certificate-authority证书写入到kubeconfig中
- –client-certificate=/opt/kubernetes/ssl/admin.pem 指定kubectl证书
- –client-key=/opt/kubernetes/ssl/admin-key.pem 指定kubectl私钥
5、kubelet
| 证书名称 | 作用 |
|---|---|
| ca.pem | CA根证书 |
| kubelet-client.crt | kubectl的TLS认证证书 |
| kubelet-client.key | kubectl的TLS认证私钥 |
| kubelet.crt | 独立于 apiserver CA 的自签 CA |
| kubelet.key | 独立于 apiserver CA 的私钥 |
当成功签发证书后,目标节点的 kubelet 会将证书写入到 --cert-dir= 选项指定的目录中;此时如果不做其他设置应当生成上述除ca.pem以外的4个文件
- kubelet-client.crt 该文件在 kubelet 完成 TLS bootstrapping 后生成,此证书是由 controller manager 签署的,此后 kubelet 将会加载该证书,用于与 apiserver 建立 TLS 通讯,同时使用该证书的 CN 字段作为用户名,O 字段作为用户组向 apiserver 发起其他请求
- kubelet.crt 该文件在 kubelet 完成 TLS bootstrapping 后并且没有配置 --feature-gates=RotateKubeletServerCertificate=true 时才会生成;这种情况下该文件为一个独立于 apiserver CA 的自签 CA 证书,有效期为 1 年;被用作 kubelet 10250 api 端口
6、kube-apiserver
kube-apiserver是在部署kubernetes集群是最需要先启动的组件,也是和集群交互的核心组件。
| 使用的证书 | 证书作用 |
|---|---|
| ca.pem | CA根证书 |
| ca-key.pem | CA端私钥 |
| Server.pem | kube-apiserver的tls认证证书 |
| Server-key.pem | kube-apiserver的tls认证私钥 |
- –token-auth-file=/opt/kubernetes/cfg/token.csv 指定了token.csv的位置,用于kubelet 组件 第一次启动时没有证书如何连接 apiserver 。 Token 和 apiserver 的 CA 证书被写入了 kubelet 所使用的 bootstrap.kubeconfig 配置文件中;这样在首次请求时,kubelet 使用 bootstrap.kubeconfig 中的 apiserver CA 证书来与 apiserver 建立 TLS 通讯,使用 bootstrap.kubeconfig 中的用户 Token 来向 apiserver 声明自己的 RBAC 授权身份
- –tls-cert-file=/opt/kubernetes/ssl/server.pem 指定kube-apiserver证书地址
- –tls-private-key-file=/opt/kubernetes/ssl/server-key.pem 指定kube-apiserver私钥地址
- –client-ca-file=/opt/kubernetes/ssl/ca.pem 指定根证书地址
- –service-account-key-file=/opt/kubernetes/ssl/ca-key.pem 包含PEM-encoded x509 RSA公钥和私钥的文件路径,用于验证Service Account的token,如果不指定,则使用–tls-private-key-file指定的文件
- –etcd-cafile=/opt/etcd/ssl/ca.pem 到etcd安全连接使用的SSL CA文件
- –etcd-certfile=/opt/etcd/ssl/server.pem 到etcd安全连接使用的SSL 证书文件
- –etcd-keyfile=/opt/etcd/ssl/server-key.pem 到etcd安全连接使用的SSL 私钥文件
7、kube-controller-manager
kubelet 发起的 CSR 请求都是由 kube-controller-manager 来做实际签署的,所有使用的证书都是根证书的密钥对 。由于kube-controller-manager是和kube-apiserver部署在同一节点上,且使用非安全端口通信,故不需要证书
| 使用的证书 | 证书作用 |
|---|---|
| ca.pem | CA根证书 |
| ca-key.pem | kube-apiserver的tls认证私钥 |
- –cluster-signing-cert-file=/opt/kubernetes/ssl/ca.pem 指定签名的CA机构根证书,用来签名为 TLS BootStrap 创建的证书和私钥
- –cluster-signing-key-file=/opt/kubernetes/ssl/ca-key.pem 指定签名的CA机构私钥,用来签名为 TLS BootStrap 创建的证书和私钥
- –service-account-private-key-file=/opt/kubernetes/ssl/ca-key.pem 同上
- –root-ca-file=/opt/kubernetes/ssl/ca.pem 根CA证书文件路径 ,用来对 kube-apiserver 证书进行校验,指定该参数后,才会在Pod 容器的 ServiceAccount 中放置该 CA 证书文件
- –kubeconfig kubeconfig配置文件路径,在配置文件中包括Master的地址信息及必要认证信息
8、kube-scheduler && kube-proxy
kube-scheduler是和kube-apiserver一般部署在同一节点上,且使用非安全端口通信,故启动参参数中没有指定证书的参数可选 。 若分离部署,可在kubeconfig文件中指定证书,使用kubeconfig认证,kube-proxy类似