【运维知识进阶篇】集群架构-Nginx常用模块(目录索引+状态监控+访问控制+访问限制)
这篇文章给大家介绍Nginx常用模块,包括Nginx目录索引,Nginx状态监控,Nginx访问控制,Nginx访问限制。熟悉使用模块,才能给Nginx增加色彩。
目录索引模块
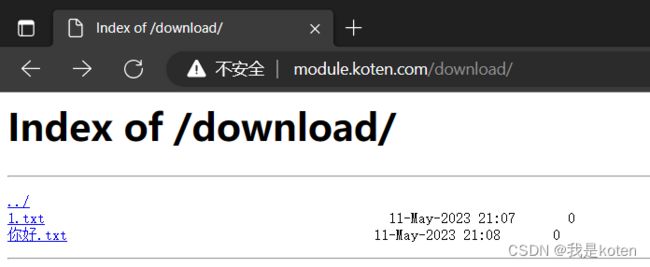
Nginx不允许列出整个目录浏览下载,可以用模块自己做个下载页。
ngx_http_autoindex_module模块处理以斜杠字符(’/’)结尾的请求,并生成目录列表。
当ngx_http_index_module模块找不到索引文件时,通常会将请求传递给ngx_http_autoindex_module模块。配置方法
autoindex on;如果在location下写,只对当前location生效。不能写index.html
#autoindex常用参数
autoindex_exact_size off;
默认为on,显示出文件的确切大小,单位是bytes。
修改为off,显示出文件的大概大小,单位是KB或者MB或者GB。
autoindex_localtime on;
默认为off,显示的文件时间为GMT时间。
修改为on,显示的文件时间为文件的服务器时间。
charset utf-8,gbk;
默认中文目录乱码,添加上解决乱码
对下载资源进行限速
limit_rate rate
limit_rate_after size配置示例
[root@Web01 ~]# cat /etc/nginx/conf.d/module.conf
server {
listen 80;
server_name module.koten.com
charset utf-8,gbk;
location / {
root /code;
index index.html index.htm;
}
location /download {
alias /module; #根下的module
autoindex on;
autoindex_exact_size off;
autoindex_localtime on;
}
}
[root@Web01 code]# systemctl restart nginx
[root@Web01 code]# mkdir /module
[root@Web01 code]# touch /module/1.txt
[root@Web01 code]# touch /module/你好.txt
注意路径问题:
location /{
root /code/; #/=====/code 用户访问www.baidu.com实际是在/code目录下查找index.html
} 状态监控模块
状态监控模块
ngx_http_stub_status_module模块提供对基本状态信息的访问,默认情况下不构建此模块,应使用--with-http_stub_status_module配置参数启用它
[root@Web01 code]# cat /etc/nginx/conf.d/module.conf
server {
listen 80;
server_name module.koten.com;
access_log off;
location /nginx_status {
stub_status;
}
}
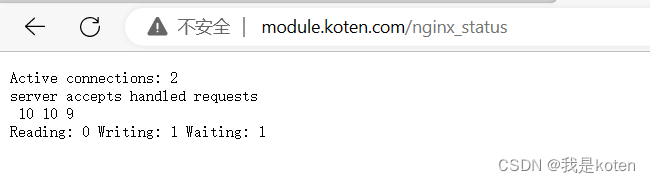
[root@Web01 code]# systemctl restart nginxActive connections # 当前活动的连接数
accepts # 已接收T的总TCP连接数量
handled # 已处理的TCP连接数量
requests # 当前http请求数
Reading # 当前读取请求头数量
Writing # 当前响应的请求头数量
Waiting # 等待的请求数,开启了keepalive
# 注意, 一次TCP的连接,可以发起多次http的请求, 如下参数可配置进行验证
keepalive_timeout 0; # 类似于关闭长连接
keepalive_timeout 65; # 65s没有活动则断开连接访问控制模块
基于IP的访问控制http_access_module和基于用户登陆认证http_auth_basic_module
Nginx基于IP访问控制
1、访问控制配置,拒绝指定IP,其他全部允许
[root@Web01 code]# cat /etc/nginx/conf.d/module.conf
server {
listen 80;
server_name module.koten.com;
access_log off;
location /nginx_status {
stub_status;
deny 10.0.0.1;
allow all;
}
}
[root@Web01 code]# systemctl restart nginx由于本机IP是10.0.0.1所以访问失败,权限拒绝
 2、访问控制配置示例,只允许谁能访问,其他全部拒绝
2、访问控制配置示例,只允许谁能访问,其他全部拒绝
[root@Web01 code]# cat /etc/nginx/conf.d/module.conf
server {
listen 80;
server_name module.koten.com;
access_log off;
location /nginx_status {
stub_status;
allow 10.0.0.1/24;
allow 127.0.0.1;
deny all;
}
}
[root@Web01 code]# systemctl restart nginx
[root@Web02 code]# tail -1 /etc/hosts #修改hosts解析
10.0.0.7 module.koten.com
[root@Web02 code]# curl -s module.koten.com/nginx_status
Active connections: 2
server accepts handled requests
56 56 55
Reading: 0 Writing: 1 Waiting: 1 Nginx基于用户登录认证
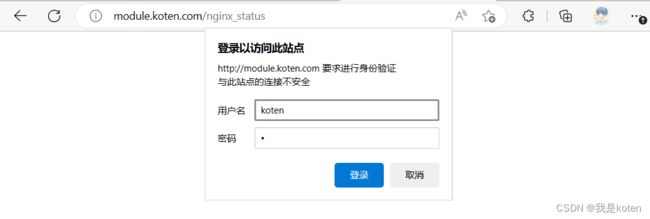
1、安装httpd-tools,该包中携带了httpasswd命令
[root@Web01 ~]# yum -y install httpd-tools2、创建新的密码文件,-c创建新文件,-b允许命令行输入密码
[root@Web01 ~]# htpasswd -b -c /etc/nginx/auth_conf koten 1
Adding password for user koten3、Nginx配置调用
[root@Web01 ~]# cat /etc/nginx/conf.d/module.conf
server {
listen 80;
server_name module.koten.com;
access_log off;
location /nginx_status {
stub_status;
auth_basic "请输入账号和密码!";
auth_basic_user_file auth_conf;
}
}
[root@Web01 ~]# systemctl restart nginx访问限制模块
企业中经常会遇到服务器流量异常,负载过大的情况,对于大流量恶意的攻击访问,会带来宽带的
浪费,会影响业务,我们往往考虑对同一个IP的连接数,请求数进行限制。
ngx_http_limit_conn_module模块可以根据定义的key来限制每个键值的连接数,如同一个IP来源的连接数。
limit_conn_module连接频率限制
limit_req_module请求频率限制
Nginx连接限制配置示例
1、Nginx配置文件使用模块
[root@Web01 ~]# cat /etc/nginx/nginx.conf |grep limit
limit_conn_zone $remote_addr zone=conn_zone:10m; #放在http中
[root@Web01 ~]# cat /etc/nginx/conf.d/wordpress.conf |grep limit
limit_conn conn_zone 1; #放在server中
[root@Web01 ~]# systemctl restart nginx2、ab工具进行压力测试
[root@Web01 ~]# tail -1 /etc/hosts
10.0.0.7 blog.koten.com
[root@Web01 ~]# yum -y install httpd-tools
[root@Web01 ~]# ab -n 20 -c 2 http://blog.koten.com/
3、查看Nginx报错日志
[root@Web01 ~]# tail -10 /var/log/nginx/error.log
2023/05/11 22:29:45 [error] 96196#96196: *58 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:29:45 [error] 96196#96196: *59 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:29:45 [error] 96196#96196: *60 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:29:45 [error] 96196#96196: *61 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:29:45 [error] 96196#96196: *62 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:29:45 [error] 96196#96196: *63 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:29:45 [error] 96196#96196: *64 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:29:45 [error] 96196#96196: *65 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:29:45 [error] 96196#96196: *66 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:29:45 [error] 96196#96196: *67 limiting connections by zone "conn_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"Nginx请求限制配置实战
修改Nginx配置文件,重启Nginx,ab压力测试
# http标签段定义请求限制, rate限制速率,限制一秒钟最多一个IP请求
http {
limit_req_zone $binary_remote_addr zone=req_zone:10m rate=1r/s;
}
server {
listen 80;
server_name blog.koten.com;
root /code/wordpress;
index index.php index.html index.htm;
location ~\.php$ {
root /code/wordpress;
fastcgi_pass 127.0.0.1:9000;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param HTTPS on;
include fastcgi_params;
}
# 1r/s只接收一个请求,其余请求拒绝处理并返回错误码给客户端
#limit_req zone=req_zone;
# 请求超过1r/s,剩下的将被延迟处理,请求数超过burst定义的数量, 多余的请求返回503
limit_req zone=req_zone burst=3 nodelay;
}
[root@Web01 ~]# systemctl restart nginx
[root@Web01 ~]# ab -n 20 -c 2 http://blog.koten.com/查看Nginx报错日志
[root@Web01 ~]# tail -10 /var/log/nginx/error.log
2023/05/11 22:39:46 [error] 99013#99013: *77 limiting requests, excess: 3.919 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:39:46 [error] 99013#99013: *78 limiting requests, excess: 3.919 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:39:46 [error] 99013#99013: *79 limiting requests, excess: 3.918 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:39:46 [error] 99013#99013: *80 limiting requests, excess: 3.918 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:39:46 [error] 99013#99013: *81 limiting requests, excess: 3.917 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:39:46 [error] 99013#99013: *82 limiting requests, excess: 3.917 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:39:46 [error] 99013#99013: *83 limiting requests, excess: 3.917 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:39:46 [error] 99013#99013: *84 limiting requests, excess: 3.905 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:39:46 [error] 99013#99013: *85 limiting requests, excess: 3.905 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"
2023/05/11 22:39:46 [error] 99013#99013: *86 limiting requests, excess: 3.904 by zone "req_zone", client: 10.0.0.7, server: blog.koten.com, request: "GET / HTTP/1.0", host: "blog.koten.com"Nginx请求限制重定向
在Nginx请求限制的过程中,我们可以自定义一个返回值,也就是错误页面的状态码。
默认情况下是503
1、修改默认返回状态码为478
[root@Web01 ~]# cat /etc/nginx/conf.d/wordpress.conf
server {
listen 80;
server_name blog.koten.com;
root /code/wordpress;
index index.php index.html index.htm;
location ~\.php$ {
root /code/wordpress;
fastcgi_pass 127.0.0.1:9000;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param HTTPS on;
include fastcgi_params;
}
limit_req zone=req_zone burst=3 nodelay;
limit_req_status 478
}
#访问后查看日志发现状态码变为478
[root@Web01 ~]# cat /var/log/nginx/access.log|grep 478
10.0.0.7 - - [11/May/2023:22:53:58 +0800] "GET / HTTP/1.0" 478 130 "-" "ApacheBench/2.3" "-"2、重定向报错页面
[root@Web01 ~]# cat /etc/nginx/conf.d/wordpress.conf
server {
listen 80;
server_name blog.koten.com;
root /code/wordpress;
index index.php index.html index.htm;
location ~\.php$ {
root /code/wordpress;
fastcgi_pass 127.0.0.1:9000;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param HTTPS on;
include fastcgi_params;
}
limit_req zone=req_zone burst=3 nodelay;
limit_req_status 478;
error_page 478 /err.html;
}
[root@Web01 ~]# cat /code/wordpress/err.html

Nginx请求限制比连接限制更有效
首先HTTP是建立在TCP基础之上,在完成HTTP请求需要先建立TCP三次握手(称为TCP连接),在连接的基础上在完成HTTP的请求。所以多个HTTP请求可以建立在一次TCP连接之上, 那么我们对请求的精度限制,当然比对一个连接的限制会更加的有效,因为同一时刻只允许一个TCP连接进入, 但是同一时刻多个HTTP请求可以通过一个TCP连接进入。所以针对HTTP的请求限制才是比较优的解决方案。
Nginx请求限制如何做
如果作为代理服务器,我们需要限制每个用户的请求速度和链接数量,但是,由于一个页面有多个子资源,如果毫无选择的都进行限制,那就会出现很多不必要的麻烦,如:一个页面有40个子资源,那么如果想让一个页面完整的显示,就需要将请求速度和连接数都调整到40,以此达到不阻塞用户正常请求,而这个限制,对服务器性能影响很大,几百用户就能把一台nginx的处理性能拉下来。
所以我们需要制定哪些请求是需要进行限制的,如html页面;哪些是不需要限制的,如css、js、图片等,这样就需要通过配置对应的location进一步细化。不对css、js、gif、png,jpg等进行连接限制,对除此之外的链接进行限制。
我是koten,10年运维经验,持续分享运维干货,感谢大家的阅读和关注!