Kubernetes08-安全认证和DashBoard的部署
1.Kubernetes访问控制
1.1 访问控制概述
Kubernetes作为一个分布式集群的管理工具,保证集群的安全性是其一个重要的任务。所谓的安全性其实就是保证对Kubernetes的各种客户端进行认证和鉴权操作。
客户端
在Kubernetes集群中,客户端通常有两类:
- User Account:一般是独立于kubernetes之外的其他服务管理的用户账号。
- Service Account:kubernetes管理的账号,用于为Pod中的服务进程在访问Kubernetes时提供身份标识。
1.1.1 认证、授权与准入控制
ApiServer是访问及管理资源对象的唯一入口。任何一个请求访问ApiServer,都要经过下面三个流程:
- Authentication(认证):身份鉴别,只有正确的账号才能够通过认证
- Authorization(授权): 判断用户是否有权限对访问的资源执行特定的动作
- Admission Control(准入控制):用于补充授权机制以实现更加精细的访问控制功能。

1.2 认证管理
Kubernetes集群安全的最关键点在于如何识别并认证客户端身份,它提供了3种客户端身份认证方式:
- HTTP Base认证:通过用户名+密码的方式认证
这种认证方式是把“用户名:密码”用BASE64算法进行编码后的字符串放在HTTP请求中的Header Authorization域里发送给服务端。服务端收到后进行解码,获取用户名及密码,然后进行用户身份认证的过程。 - HTTP Token认证:通过一个Token来识别合法用户
这种认证方式是用一个很长的难以被模仿的字符串–Token来表明客户身份的一种方式。每个Token对应一个用户名,当客户端发起API调用请求时,需要在HTTP Header里放入Token,API Server接到Token后会跟服务器中保存的token进行比对,然后进行用户身份认证的过程。 - HTTPS证书认证:基于CA根证书签名的双向数字证书认证方式
这种认证方式是安全性最高的一种方式,但是同时也是操作起来最麻烦的一种方式。

HTTPS认证大体分为3个过程:
-
证书申请和下发
HTTPS通信双方的服务器向CA机构申请证书,CA机构下发根证书、服务端证书及私钥给申请者 -
客户端和服务端的双向认证
- 客户端向服务器端发起请求,服务端下发自己的证书给客户端,
客户端接收到证书后,通过私钥解密证书,在证书中获得服务端的公钥,
客户端利用服务器端的公钥认证证书中的信息,如果一致,则认可这个服务器- 客户端发送自己的证书给服务器端,服务端接收到证书后,通过私钥解密证书,
在证书中获得客户端的公钥,并用该公钥认证证书信息,确认客户端是否合法
- 服务器端和客户端进行通信
- 服务器端和客户端协商好加密方案后,客户端会产生一个随机的秘钥并加密,然后发送到服务器端。
- 服务器端接收这个秘钥后,双方接下来通信的所有内容都通过该随机秘钥加密
注意: Kubernetes允许同时配置多种认证方式,只要其中任意一个方式认证通过即可
1.3. 授权管理
授权发生在认证成功之后,通过认证就可以知道请求用户是谁, 然后Kubernetes会根据事先定义的授权策略来决定用户是否有权限访问,这个过程就称为授权。
每个发送到ApiServer的请求都带上了用户和资源的信息:比如发送请求的用户、请求的路径、请求的动作等,授权就是根据这些信息和授权策略进行比较,如果符合策略,则认为授权通过,否则会返回错误。
API Server目前支持以下几种授权策略:
- AlwaysDeny:表示拒绝所有请求,一般用于测试
- AlwaysAllow:允许接收所有请求,相当于集群不需要授权流程(Kubernetes默认的策略)
- ABAC:基于属性的访问控制,表示使用用户配置的授权规则对用户请求进行匹配和控制
- Webhook:通过调用外部REST服务对用户进行授权
- Node:是一种专用模式,用于对kubelet发出的请求进行访问控制
- RBAC:基于角色的访问控制(kubeadm安装方式下的默认选项)
RBAC(Role-Based Access Control) 基于角色的访问控制,主要是在描述一件事情:给哪些对象授予了哪些权限
其中涉及到了下面几个概念:
- 对象:User、Groups、ServiceAccount
- 角色:代表着一组定义在资源上的可操作动作(权限)的集合
- 绑定:将定义好的角色跟用户绑定在一起
- Role、ClusterRole:角色,用于指定一组权限
- RoleBinding、ClusterRoleBinding:角色绑定,用于将角色(权限)赋予给对象
Role、ClusterRole
一个角色就是一组权限的集合,这里的权限都是许可形式的(白名单)。
# Role只能对命名空间内的资源进行授权,需要指定nameapce
kind: Role
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
namespace: dev
name: authorization-role
rules:
- apiGroups: [""] # 支持的API组列表,"" 空字符串,表示核心API群
resources: ["pods"] # 支持的资源对象列表
verbs: ["get", "watch", "list"] # 允许的对资源对象的操作方法列表
# ClusterRole可以对集群范围内资源、跨namespaces的范围资源、非资源类型进行授权
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: authorization-clusterrole
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "watch", "list"]
RoleBinding引用ClusterRole进行授权
RoleBinding可以引用ClusterRole,对属于同一命名空间内ClusterRole定义的资源主体进行授权。
一种很常用的做法就是,集群管理员为集群范围预定义好一组角色(ClusterRole),然后在多个命名空间中重复使用这些ClusterRole。这样可以大幅提高授权管理工作效率,也使得各个命名空间下的基础性授权规则与使用体验保持一致。
# 虽然authorization-clusterrole是一个集群角色,但是因为使用了RoleBinding
# 所以huazige只能读取dev命名空间中的资源
kind: RoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: authorization-role-binding-ns
namespace: dev
subjects:
- kind: User
name: huazige
apiGroup: rbac.authorization.k8s.io
roleRef:
kind: ClusterRole
name: authorization-clusterrole
apiGroup: rbac.authorization.k8s.io
1.3.1 实战:创建一个只能管理dev空间下Pods资源的账号
- 创建账号
[root@master ~]# cd /etc/kubernetes/pki/
[root@master pki]# ll
total 56
-rw-r--r-- 1 root root 1216 Jun 25 22:20 apiserver.crt
-rw-r--r-- 1 root root 1090 Jun 25 22:20 apiserver-etcd-client.crt
-rw------- 1 root root 1679 Jun 25 22:20 apiserver-etcd-client.key
-rw------- 1 root root 1675 Jun 25 22:20 apiserver.key
-rw-r--r-- 1 root root 1099 Jun 25 22:20 apiserver-kubelet-client.crt
-rw------- 1 root root 1679 Jun 25 22:20 apiserver-kubelet-client.key
-rw-r--r-- 1 root root 1025 Jun 25 22:20 ca.crt
-rw------- 1 root root 1675 Jun 25 22:20 ca.key
drwxr-xr-x 2 root root 162 Jun 25 22:20 etcd
-rw-r--r-- 1 root root 1038 Jun 25 22:20 front-proxy-ca.crt
-rw------- 1 root root 1679 Jun 25 22:20 front-proxy-ca.key
-rw-r--r-- 1 root root 1058 Jun 25 22:20 front-proxy-client.crt
-rw------- 1 root root 1675 Jun 25 22:20 front-proxy-client.key
-rw------- 1 root root 1679 Jun 25 22:20 sa.key
-rw------- 1 root root 451 Jun 25 22:20 sa.pub
# 1) 创建证书
[root@master pki]# (umask 077;openssl genrsa -out devman.key 2048)
Generating RSA private key, 2048 bit long modulus
....................+++
...................................+++
e is 65537 (0x10001)
[root@master pki]# ll
total 60
-rw-r--r-- 1 root root 1216 Jun 25 22:20 apiserver.crt
-rw-r--r-- 1 root root 1090 Jun 25 22:20 apiserver-etcd-client.crt
-rw------- 1 root root 1679 Jun 25 22:20 apiserver-etcd-client.key
-rw------- 1 root root 1675 Jun 25 22:20 apiserver.key
-rw-r--r-- 1 root root 1099 Jun 25 22:20 apiserver-kubelet-client.crt
-rw------- 1 root root 1679 Jun 25 22:20 apiserver-kubelet-client.key
-rw-r--r-- 1 root root 1025 Jun 25 22:20 ca.crt
-rw------- 1 root root 1675 Jun 25 22:20 ca.key
#多了一个 devman.key
-rw------- 1 root root 1679 Jul 5 03:46 devman.key
drwxr-xr-x 2 root root 162 Jun 25 22:20 etcd
-rw-r--r-- 1 root root 1038 Jun 25 22:20 front-proxy-ca.crt
-rw------- 1 root root 1679 Jun 25 22:20 front-proxy-ca.key
-rw-r--r-- 1 root root 1058 Jun 25 22:20 front-proxy-client.crt
-rw------- 1 root root 1675 Jun 25 22:20 front-proxy-client.key
-rw------- 1 root root 1679 Jun 25 22:20 sa.key
-rw------- 1 root root 451 Jun 25 22:20 sa.pub
# 2) 用apiserver的证书去签署
# 2-1) 签名申请,申请的用户是devman,组是devgroup
[root@master pki]# openssl req -new -key devman.key -out devman.csr -subj "/CN=devman/O=devgroup"
# 2-2) 签署证书
[root@master pki]# openssl x509 -req -in devman.csr -CA ca.crt -CAkey ca.key -CAcreateserial -out devman.crt -days 3650
Signature ok
subject=/CN=devman/O=devgroup
Getting CA Private Key
[root@master pki]# ll
total 72
-rw-r--r-- 1 root root 1216 Jun 25 22:20 apiserver.crt
-rw-r--r-- 1 root root 1090 Jun 25 22:20 apiserver-etcd-client.crt
-rw------- 1 root root 1679 Jun 25 22:20 apiserver-etcd-client.key
-rw------- 1 root root 1675 Jun 25 22:20 apiserver.key
-rw-r--r-- 1 root root 1099 Jun 25 22:20 apiserver-kubelet-client.crt
-rw------- 1 root root 1679 Jun 25 22:20 apiserver-kubelet-client.key
-rw-r--r-- 1 root root 1025 Jun 25 22:20 ca.crt
-rw------- 1 root root 1675 Jun 25 22:20 ca.key
-rw-r--r-- 1 root root 17 Jul 5 03:47 ca.srl
-rw-r--r-- 1 root root 1001 Jul 5 03:47 devman.crt
-rw-r--r-- 1 root root 911 Jul 5 03:46 devman.csr
-rw------- 1 root root 1679 Jul 5 03:46 devman.key
drwxr-xr-x 2 root root 162 Jun 25 22:20 etcd
-rw-r--r-- 1 root root 1038 Jun 25 22:20 front-proxy-ca.crt
-rw------- 1 root root 1679 Jun 25 22:20 front-proxy-ca.key
-rw-r--r-- 1 root root 1058 Jun 25 22:20 front-proxy-client.crt
-rw------- 1 root root 1675 Jun 25 22:20 front-proxy-client.key
-rw------- 1 root root 1679 Jun 25 22:20 sa.key
-rw------- 1 root root 451 Jun 25 22:20 sa.pub
# 3) 设置集群、用户、上下文信息
[root@master pki]# kubectl config set-cluster kubernetes --embed-certs=true --certificate-authority=/etc/kubernetes/pki/ca.crt --server=https://192.168.56.101:6443
Cluster "kubernetes" set.
[root@master pki]# kubectl config set-credentials devman --embed-certs=true --client-certificate=/etc/kubernetes/pki/devman.crt --client-key=/etc/kubernetes/pki/devman.key
User "devman" set.
[root@master pki]# kubectl config set-context devman@kubernetes --cluster=kubernetes --user=devman
Context "devman@kubernetes" created.
# 切换账户到devman
[root@master pki]# kubectl config use-context devman@kubernetes
Switched to context "devman@kubernetes".
# 查看dev下pod,发现没有权限
[root@master pki]# kubectl -n dev get pods
Error from server (Forbidden): pods is forbidden: User "devman" cannot list resource "pods" in API group "" in the namespace "dev"
# 切换到admin账户
[root@master pki]# kubectl config use-context kubernetes-admin@kubernetes
Switched to context "kubernetes-admin@kubernetes".
[root@master pki]# kubectl -n dev get pods
NAME READY STATUS RESTARTS AGE
pod-configmap 1/1 Running 0 15h
pod-secret 1/1 Running 0 15h
- 创建Role和RoleBinding,为devman用户授权
kind: Role
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
namespace: dev
name: dev-role
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "watch", "list"]
---
kind: RoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: authorization-role-binding
namespace: dev
subjects:
- kind: User
name: devman
apiGroup: rbac.authorization.k8s.io
roleRef:
kind: Role
name: dev-role
apiGroup: rbac.authorization.k8s.io
[root@master authorization]# kubectl create -f dev-role.yaml
role.rbac.authorization.k8s.io/dev-role created
rolebinding.rbac.authorization.k8s.io/authorization-role-binding created
- 切换用户再次验证
[root@master authorization]# kubectl config use-context devman@kubernetes
Switched to context "devman@kubernetes".
[root@master authorization]# kubectl get pods -n dev
NAME READY STATUS RESTARTS AGE
pod-configmap 1/1 Running 0 15h
pod-secret 1/1 Running 0 15h
1.4.准入控制
通过了前面的认证和授权之后,还需要经过准入控制处理通过之后,apiserver才会处理这个请求。
准入控制是一个可配置的控制器列表,可以通过在Api-Server上通过命令行设置选择执行哪些准入控制器:
--admission-control=NamespaceLifecycle,LimitRanger,ServiceAccount,PersistentVolumeLabel,
DefaultStorageClass,ResourceQuota,DefaultTolerationSeconds
只有当所有的准入控制器都检查通过之后,apiserver才执行该请求,否则返回拒绝
当前可配置的Admission Control准入控制如下:
- AlwaysAdmit:允许所有请求
- AlwaysDeny:禁止所有请求,一般用于测试
- AlwaysPullImages:在启动容器之前总去下载镜像
- DenyExecOnPrivileged:它会拦截所有想在Privileged Container上执行命令的请求
- ImagePolicyWebhook:这个插件将允许后端的一个Webhook程序来完成admission controller的功能。
- Service Account:实现ServiceAccount实现了自动化
- SecurityContextDeny:这个插件将使用SecurityContext的Pod中的定义全部失效
- ResourceQuota:用于资源配额管理目的,观察所有请求,确保在namespace上的配额不会超标
- LimitRanger:用于资源限制管理,作用于namespace上,确保对Pod进行资源限制
- InitialResources:为未设置资源请求与限制的Pod,根据其镜像的历史资源的使用情况进行设置
- NamespaceLifecycle:如果尝试在一个不存在的namespace中创建资源对象,则该创建请求将被拒绝。当删除一个namespace时,系统将会删除该namespace中所有对象。
- DefaultStorageClass:为了实现共享存储的动态供应,为未指定StorageClass或PV的PVC尝试匹配默认的StorageClass,尽可能减少用户在申请PVC时所需了解的后端存储细节
- DefaultTolerationSeconds:这个插件为那些没有设置forgiveness tolerations并具有notready:NoExecute和unreachable:NoExecute两种taints的Pod设置默认的“容忍”时间,为5min
- PodSecurityPolicy:这个插件用于在创建或修改Pod时决定是否根据Pod的security context和可用的PodSecurityPolicy对Pod的安全策略进行控制
2.DashBoard
之前在kubernetes中完成的所有操作都是通过命令行工具kubectl完成的。其实,为了提供更丰富的用户体验,kubernetes还开发了一个基于web的用户界面(Dashboard)。用户可以使用Dashboard部署容器化的应用,还可以监控应用的状态,执行故障排查以及管理kubernetes中各种资源。
2.1 部署DashBoard
- 下载yaml,并运行DashBoard
[root@master dashboard]# wget https://raw.githubusercontent.com/kubernetes/dashboard/v2.0.0/aio/deploy/recommended.yaml
--2022-07-05 04:19:45-- https://raw.githubusercontent.com/kubernetes/dashboard/v2.0.0/aio/deploy/recommended.yaml
Resolving raw.githubusercontent.com (raw.githubusercontent.com)... 185.199.111.133, 185.199.108.133, 185.199.109.133, ...
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|185.199.111.133|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 7552 (7.4K) [text/plain]
Saving to: ‘recommended.yaml’
100%[====================================================================>] 7,552 --.-K/s in 0s
2022-07-05 04:19:46 (58.0 MB/s) - ‘recommended.yaml’ saved [7552/7552]
############修改下载文件中service类型
# 修改kubernetes-dashboard的Service类型
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kubernetes-dashboard
spec:
type: NodePort # 新增行
ports:
- port: 443
targetPort: 8443
nodePort: 30009 # 新增行
selector:
k8s-app: kubernetes-dashboard
#############
[root@master dashboard]# kubectl create -f recommended.yaml
namespace/kubernetes-dashboard created
serviceaccount/kubernetes-dashboard created
service/kubernetes-dashboard created
secret/kubernetes-dashboard-certs created
secret/kubernetes-dashboard-csrf created
secret/kubernetes-dashboard-key-holder created
configmap/kubernetes-dashboard-settings created
role.rbac.authorization.k8s.io/kubernetes-dashboard created
clusterrole.rbac.authorization.k8s.io/kubernetes-dashboard created
rolebinding.rbac.authorization.k8s.io/kubernetes-dashboard created
clusterrolebinding.rbac.authorization.k8s.io/kubernetes-dashboard created
deployment.apps/kubernetes-dashboard created
service/dashboard-metrics-scraper created
deployment.apps/dashboard-metrics-scraper created
[root@master dashboard]# kubectl get pod,svc -n kubernetes-dashboard
NAME READY STATUS RESTARTS AGE
pod/dashboard-metrics-scraper-c79c65bb7-54bzz 1/1 Running 0 27s
pod/kubernetes-dashboard-56484d4c5-5cgh8 1/1 Running 0 27s
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/dashboard-metrics-scraper ClusterIP 10.102.209.124 <none> 8000/TCP 27s
service/kubernetes-dashboard NodePort 10.100.224.155 <none> 443:30009/TCP 27s
- 创建访问账户,获取token
# 创建账号
[root@master dashboard]# kubectl create serviceaccount dashboard-admin -n kubernetes-dashboard
serviceaccount/dashboard-admin created
# 授权
[root@master dashboard]# kubectl create clusterrolebinding dashboard-admin-rb --clusterrole=cluster-admin --serviceaccount=kubernetes-dashboard:dashboard-admin
clusterrolebinding.rbac.authorization.k8s.io/dashboard-admin-rb created
# 获取账号token
[root@master dashboard]# kubectl get secrets -n kubernetes-dashboard | grep dashboard-admin
dashboard-admin-token-zjgbt kubernetes.io/service-account-token 3 28s
[root@master dashboard]# kubectl describe secrets dashboard-admin-token-zjgbt -n kubernetes-dashboard
Name: dashboard-admin-token-zjgbt
Namespace: kubernetes-dashboard
Labels: <none>
Annotations: kubernetes.io/service-account.name: dashboard-admin
kubernetes.io/service-account.uid: 66bd1bea-3b39-48ab-be4a-2e769cd2c70d
Type: kubernetes.io/service-account-token
Data
====
namespace: 20 bytes
# 这里查看token
token: eyJhbGciOiJSUzI1NiIsImtpZCI6Iktha2JfeVF4VzJvcnppeUQ2WG9xWWdjeWxpb081ZGxBTFprZFJzR3Z6X2MifQ.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlcm5ldGVzLWRhc2hib2FyZCIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJkYXNoYm9hcmQtYWRtaW4tdG9rZW4tempnYnQiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC5uYW1lIjoiZGFzaGJvYXJkLWFkbWluIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQudWlkIjoiNjZiZDFiZWEtM2IzOS00OGFiLWJlNGEtMmU3NjljZDJjNzBkIiwic3ViIjoic3lzdGVtOnNlcnZpY2VhY2NvdW50Omt1YmVybmV0ZXMtZGFzaGJvYXJkOmRhc2hib2FyZC1hZG1pbiJ9.EFy1NO1SIsYXHT3BcPe1Qwq7krug0AQgxD__SJBHTq23DStlVUAlHtB9zPb-w_8oy_-nUGyTtracUGMV5PMFYr0kQjuF6YyedDCLOxG5jUD_Qu73EFIurlN6qayqQm5bsmaoIg475OfD51apKZ6tqUEqVABKPQkVYUij8ilk_Ha5P97a0RxbTdgO7wozbkzOvo8h5g2CT6DaH73dvoVK9c3xM_BocxH2-IVopPvJKRR1OLXgXZi6XDXnvc5QLfHoJdJP5V3LAgRQoRIL2qHelJmAE-amypc2h2gugFuuH494bKoZ-baGSDqKEf3RnlROejNnTBoNukUAoQBSiqmVYw
ca.crt: 1025 bytes
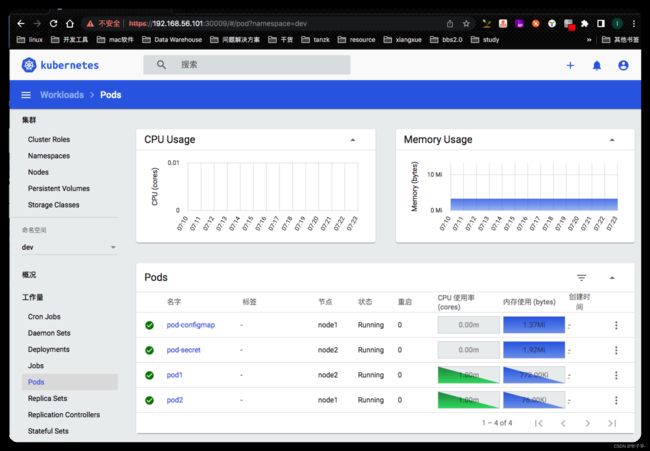
填上token后出现以下页面代表成功
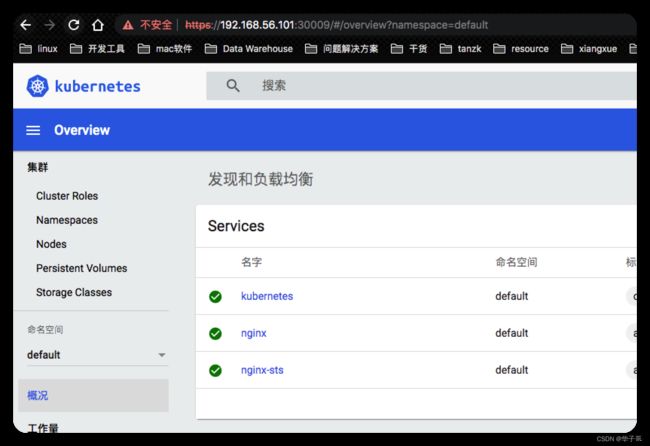
然后就可以愉快的玩耍啦
转载声明:
本文为CSDN博主「[渣渣苏](https://blog.csdn.net/su2231595742?type=blog)」的原创文章,遵循CC 4.0 BY-SA版权协议,转载请附上原文出处链接及本声明。
原文链接:https://blog.csdn.net/su2231595742/article/details/124182312
转载目的只为本人学习记录,如有侵权请联系删除

