【云原生-K8s】检查yaml文件安全配置kubesec部署及使用
-
- 基础介绍
-
- 基础描述
- 特点
- 部署
-
- 在线下载
- 百度网盘下载
- 安装
- 使用
-
- 官网样例yaml
- HTTP远程调用
- 安全建议
- 总结
基础介绍
基础描述
- Kubesec 是一个开源项目,旨在为 Kubernetes 提供安全特性。它提供了一组工具和插件,用于保护和管理在 Kubernetes 集群中的工作负载和基础设施。Kubesec 的目标是帮助开发人员和运维人员在 Kubernetes 环境中实现安全性、可靠性和合规性。
特点
- 自动化的安全策略:Kubesec 提供了自动化的安全策略,可以基于角色的访问控制(RBAC)和标签选择器来定义和执行安全规则。这可以帮助开发人员和运维人员快速部署和管理安全策略,而无需手动编写复杂的脚本来保护 Kubernetes 集群。
- 加密和身份验证:Kubesec 支持对 Kubernetes 集群中的数据和通信进行加密,以确保敏感数据的安全性。它还提供了身份验证和授权机制,可以验证集群中节点的身份并限制它们的访问权限。
- 漏洞扫描和修复:Kubesec 可以与漏洞扫描工具集成,以发现和修复 Kubernetes 工作负载中的漏洞。它还可以监视集群中的容器映像,并在发现新漏洞时自动更新容器映像。
- 合规性检查:Kubesec 可以与合规性框架集成,以确保 Kubernetes 集群符合特定的安全标准和法规要求。它提供了可扩展的插件架构,可以轻松添加新的合规性规则和检查。
- 安全审计日志:Kubesec 可以生成详细的安全审计日志,记录集群中发生的安全事件和操作。这些日志可以用于监控和检测潜在的安全问题,并提供合规性报告。
kubesec官网:https://kubesec.io/
开源地址:https://github.com/controlplaneio/kubesec
部署
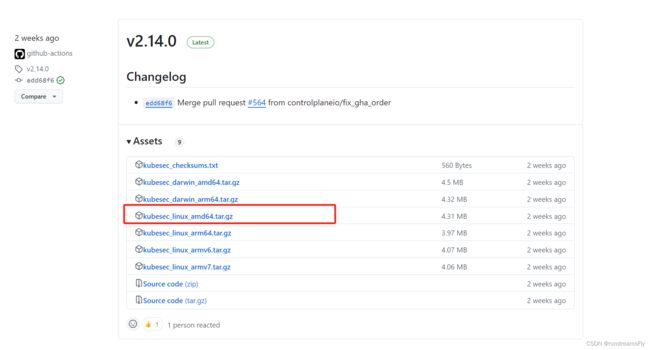
在线下载
wget https://github.com/controlplaneio/kubesec/releases/download/v2.14.0/kubesec_linux_amd64.tar.gz
百度网盘下载
链接:https://pan.baidu.com/s/1KHb5Qn9k1uIQeFOE_Ib6rg?pwd=h0i0
提取码:h0i0
–来自百度网盘超级会员V7的分享
安装
- 解压:
tar -zxf kubesec_linux_amd64.tar.gz - 移入二进制目录:
mv kubesec /usr/bin/ - 查询版本信息:
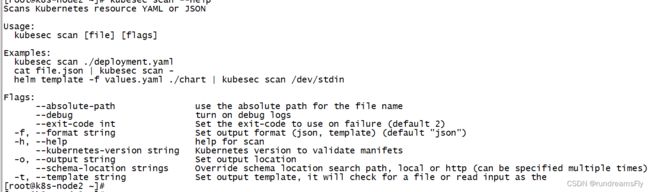
kubesec version - 查询 kubesec scan --help 使用方法
使用
官网样例yaml
cat <> kubesec-test.yaml
apiVersion: v1
kind: Pod
metadata:
name: kubesec-demo
spec:
containers:
- name: kubesec-demo
image: gcr.io/google-samples/node-hello:1.0
securityContext:
readOnlyRootFilesystem: true
EOF
- 执行 检查yaml安全配置
kubesec scan kubesec-test.yaml
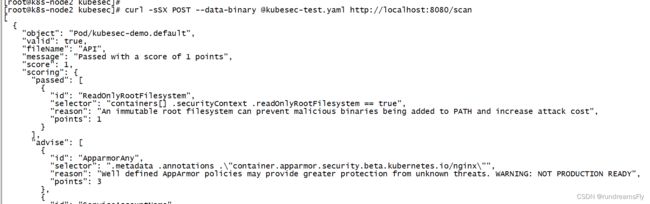
HTTP远程调用
- 部署docker容器
docker run -d -p 8080:8080 kubesec/kubesec http 8080
![]()
- 本地执行post请求进行安全扫描
curl -sSX POST --data-binary @kubesec-test.yaml http://localhost:8080/scan
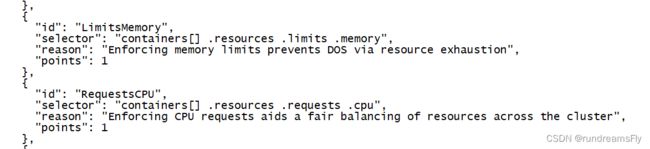
安全建议
- 安全扫描的json结果,每个id给我安全配置建议,可进行参考
[
{
"object": "Pod/kubesec-demo.default",
"valid": true,
"fileName": "kubesec-test.yaml",
"message": "Passed with a score of 1 points",
"score": 1,
"scoring": {
"passed": [
{
"id": "ReadOnlyRootFilesystem",
"selector": "containers[] .securityContext .readOnlyRootFilesystem == true",
"reason": "An immutable root filesystem can prevent malicious binaries being added to PATH and increase attack cost",
"points": 1
}
],
"advise": [
{
"id": "ApparmorAny",
"selector": ".metadata .annotations .\"container.apparmor.security.beta.kubernetes.io/nginx\"",
"reason": "Well defined AppArmor policies may provide greater protection from unknown threats. WARNING: NOT PRODUCTION READY",
"points": 3
},
{
"id": "ServiceAccountName",
"selector": ".spec .serviceAccountName",
"reason": "Service accounts restrict Kubernetes API access and should be configured with least privilege",
"points": 3
},
{
"id": "SeccompAny",
"selector": ".metadata .annotations .\"container.seccomp.security.alpha.kubernetes.io/pod\"",
"reason": "Seccomp profiles set minimum privilege and secure against unknown threats",
"points": 1
},
{
"id": "AutomountServiceAccountToken",
"selector": ".spec .automountServiceAccountToken == false",
"reason": "Disabling the automounting of Service Account Token reduces the attack surface of the API server",
"points": 1
},
{
"id": "RunAsGroup",
"selector": ".spec, .spec.containers[] | .securityContext .runAsGroup -gt 10000",
"reason": "Run as a high-UID group to avoid conflicts with the host's groups",
"points": 1
},
{
"id": "RunAsNonRoot",
"selector": ".spec, .spec.containers[] | .securityContext .runAsNonRoot == true",
"reason": "Force the running image to run as a non-root user to ensure least privilege",
"points": 1
},
{
"id": "RunAsUser",
"selector": ".spec, .spec.containers[] | .securityContext .runAsUser -gt 10000",
"reason": "Run as a high-UID user to avoid conflicts with the host's users",
"points": 1
},
{
"id": "LimitsCPU",
"selector": "containers[] .resources .limits .cpu",
"reason": "Enforcing CPU limits prevents DOS via resource exhaustion",
"points": 1
},
{
"id": "LimitsMemory",
"selector": "containers[] .resources .limits .memory",
"reason": "Enforcing memory limits prevents DOS via resource exhaustion",
"points": 1
},
{
"id": "RequestsCPU",
"selector": "containers[] .resources .requests .cpu",
"reason": "Enforcing CPU requests aids a fair balancing of resources across the cluster",
"points": 1
},
{
"id": "RequestsMemory",
"selector": "containers[] .resources .requests .memory",
"reason": "Enforcing memory requests aids a fair balancing of resources across the cluster",
"points": 1
},
{
"id": "CapDropAny",
"selector": "containers[] .securityContext .capabilities .drop",
"reason": "Reducing kernel capabilities available to a container limits its attack surface",
"points": 1
},
{
"id": "CapDropAll",
"selector": "containers[] .securityContext .capabilities .drop | index(\"ALL\")",
"reason": "Drop all capabilities and add only those required to reduce syscall attack surface",
"points": 1
}
]
}
}
]
- 如上图,yaml安全配置建议配置内存及cpu相关等参数
- 在实际业务中,如自建devops平台、或者在实际编写yaml过程中,都可以使用kubesec进行检查校验,根据实际情况进行修改。
总结
Kubesec 是一个针对 Kubernetes 的安全特性扩展项目,旨在提供自动化的安全策略、加密和身份验证、漏洞扫描和修复、合规性检查以及安全审计日志等功能,以增强 Kubernetes 集群的安全性、可靠性和合规性。
通过部署 Kubesec,可以自动化地定义和执行安全规则,减少手动编写安全脚本的工作量,同时提供加密和身份验证机制,确保集群中的数据和通信的安全性。此外,Kubesec 还支持与漏洞扫描工具集成,以发现和修复工作负载中的漏洞,并可以监视容器映像以自动更新漏洞修复。
Kubesec 还提供了合规性检查功能,以确保 Kubernetes 集群符合特定的安全标准和法规要求。它支持可扩展的插件架构,可以轻松添加新的合规性规则和检查。此外,Kubesec 还生成详细的安全审计日志,记录集群中的安全事件和操作,以便进行监控和检测潜在的安全问题,并提供合规性报告。
总之,Kubesec 是一个强大的工具,可以帮助开发人员和运维人员在 Kubernetes 环境中实现安全性、可靠性和合规性。