k8s使用Traefik发布服务
Kubernetes 集群中使用 Traefik 反向代理
在开始之前,需要先了解一下什么是RBAC。RBAC(基于角色的访问控制)使用 rbac.authorization.k8s.io API 组来实现权限控制,RBAC 允许管理员通过 Kubernetes API 动态的配置权限策略。在 1.6 版本中 RBAC 还处于 Beat 阶段,如果想要开启 RBAC 授权模式需要在 apiserver 组件中指定 –authorization-mode=RBAC 选项。
在 RBAC API 的四个重要概念:
Role:是一系列的权限的集合,例如一个角色可以包含读取 Pod 的权限和列出 Pod 的权限
ClusterRole: 跟 Role 类似,但是可以在集群中到处使用( Role 是 namespace 一级的)
RoloBinding:把角色映射到用户,从而让这些用户继承角色在 namespace 中的权限。
ClusterRoleBinding: 让用户继承 ClusterRole 在整个集群中的权限。
简单点说RBAC实现了在k8s集群中对api-server的鉴权,更多的RBAC知识点请查阅官方文档:https://kubernetes.io/docs/admin/authorization/rbac/Cmd
Traefik原理


从上图可以看出,在我们日常业务开发中,我们会部署一系列微服务,外部网络要通过 domain、path、负载均衡等转发到后端私有网络中,微服务之所以称为微,是因为它是动态变化的,它会经常被增加、删除、干掉或者被更新。而且传统的反向代理对服务动态变化的支持不是很方便,也就是服务变更后,我们不是很容易立马改变配置和热加载。traefik 的出现就是为了解决这个问题,它可以时刻监听服务注册或服务编排 API,随时感知后端服务变化,自动重新更改配置并热重新加载,期间服务不会暂停或停止,这对于用户来说是无感知的。
Traefik 还有很多特性如下:
- 速度快
- 不需要安装其他依赖,使用 GO 语言编译可执行文件
- 支持最小化官方 Docker 镜像
- 支持多种后台,如 Docker, Swarm mode, Kubernetes, Marathon, Consul, Etcd, Rancher, Amazon ECS 等等
- 支持 REST API
- 配置文件热重载,不需要重启进程
- 支持自动熔断功能
- 支持轮训、负载均衡
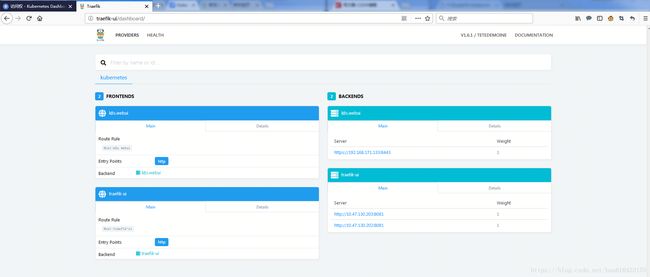
- 提供简洁的 UI 界面
- 支持 Websocket, HTTP/2, GRPC
- 自动更新 HTTPS 证书
- 支持高可用集群模式
k8s上部署Traefik
参考文章
https://cloud.tencent.com/developer/article/1010575
http://docs.traefik.cn/basics
给集群node打上label
因为选择deployment方式部署,所以要给集群的节点打上label,后续选择nodeSelector指定traefik=proxy,副本数和集群节点数一致的时候,所有的节点上都会运行一个pod
#kubectl label node modelxsitapp29 traefik=proxy
#kubectl label node modelxsitapp30 traefik=proxy
#kubectl get nodes --show-labels准备yaml文件
1. rbac文件
# cat traefik-rbac.yaml
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: traefik-ingress-controller
rules:
- apiGroups:
- ""
resources:
- services
- endpoints
- secrets
verbs:
- get
- list
- watch
- apiGroups:
- extensions
resources:
- ingresses
verbs:
- get
- list
- watch
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: traefik-ingress-controller
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: traefik-ingress-controller
subjects:
- kind: ServiceAccount
name: traefik-ingress-controller
namespace: kube-system在启用rbac的环境下,如果鉴权未配置清楚,则traefik pod会报错如下
Failed to list *v1.Endpoints: endpoints is forbidden: User "system:serviceaccount:kube-system:default" cannot list endpoints at the cluster scope 2. traefik的deployment文件
# cat traefik-deployment.yaml
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: traefik-ingress-controller
namespace: kube-system
---
kind: Deployment
apiVersion: extensions/v1beta1
metadata:
name: traefik-ingress-controller
namespace: kube-system
labels:
k8s-app: traefik-ingress-lb
spec:
replicas: 2
selector:
matchLabels:
k8s-app: traefik-ingress-lb
template:
metadata:
labels:
k8s-app: traefik-ingress-lb
name: traefik-ingress-lb
spec:
serviceAccountName: traefik-ingress-controller
hostNetwork: true
nodeSelector:
traefik: proxy
terminationGracePeriodSeconds: 60
containers:
- image: traefik
name: traefik-ingress-lb
imagePullPolicy: Never
ports:
- name: web
containerPort: 80
hostPort: 80
- name: admin
containerPort: 8081
args:
- --web
- --web.address=:8081
- --kubernetes3. traefik的service文件
# cat traefik-service.yaml
apiVersion: v1
kind: Service
metadata:
name: traefik-web-ui
namespace: kube-system
spec:
selector:
k8s-app: traefik-ingress-lb
ports:
- port: 80
targetPort: 8081
type:NodePort4. 通过k8s创建yaml
# kubectl create -f traefik-rbac.yaml
# kubectl create -f traefik-deployment.yaml
# kubectl create -f traefik-service.yaml 通过yaml创建ingress
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: traefik-web-ui
namespace: kube-system
annotations:
kubernetes.io/ingress.class: traefik
spec:
rules:
- host: traefik-ui
http:
paths:
- backend:
serviceName: traefik-web-ui
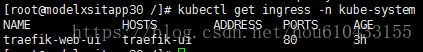
servicePort: 80通过k8s 查看
kubectl get ingress -n kube-system验证
1.修改hosts文件将域名解析分配到两台node上
10.47.130.202 k8s.webui
10.47.130.203 traefik-ui
10.47.130.202 traefik-ui