http://blog.itpub.net/28916011/viewspace-2215100/
对作者文章有点改动
注意kubeadm创建的k8s集群里面的认证key是有有效期的,这是一个大坑!!!!!!
目前RBAC是k8s授权方式最常用的一种方式。
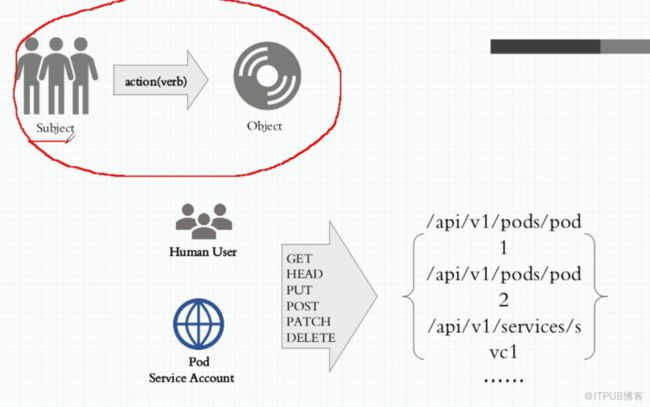
在k8s上,一个客户端向apiserver发起请求,需要如下信息:
1)username,uid,
2) group,
3) extra(额外信息)
4) API
5) request path,例如:http://127.0.0.1:8080/apis/apps/v1/namespaces/kube-system/d
6)HTTP request action,如get,post,put,delete,
7)Http request action,如 get,list,create,udate,patch,watch,proxy,redirect,delete,deletecollection
8) Rresource
9)Subresource
10)Namespace
11)API group
K8s可以支持多版本并存。
其实,我们用kubectl向apiserver发起的命令,都是http方式的。
k8s验证分为useraccount和serviceaccount。
可以用代理:
[root@master ~]# kubectl proxy --port=8080
[root@master ~]# curl
[root@master ~]# kubectl get deploy -n kube-system
NAME DESIRED CURRENT UP-TO-DATE AVAILABLE AGE
coredns 2 2 2 2 20d
[root@master ~]# curl http://127.0.0.1:8080/apis/apps/v1/namespaces/kube-system/deployments
[root@master ~]# kubectl get svc
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
kubernetes ClusterIP 10.96.0.1 443/TCP 12d
[root@master ~]# kubectl describe svc kubernetes
Name: kubernetes
Namespace: default
Labels: component=apiserver
provider=kubernetes
Annotations:
Selector:
Type: ClusterIP
IP: 10.96.0.1
Port: https 443/TCP
TargetPort: 6443/TCP
Endpoints: 172.16.100.64:6443
Session Affinity: None
Events:
上面我们看到10.96.0.1是kubernetes apiserver的地址,从而实现了集群外部通过10.96.0.1访问集群内部的pod,同时也实现了集群内部的pod访问集群外部的应用的功能。
只要访问apiserver,就必须实现认证。而认证信息是存储在pod中的。
[root@master ~]# kubectl explain pods.spec.serviceAccountName
[root@master manifests]# kubectl create serviceaccount mysa -o yaml --dry-run > mysa.yaml
[root@master manifests]# cat mysa.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
creationTimestamp: null
name: mysa
上面我们可以看到,只要是kubectl create的,只要加上-o yaml,就可以导出清单文件,这样我们以后就不用从头到尾写清单文件了,而是只要生产一个,然后改改就行了,这个很不错。
另外kubectl get 也可以导出yaml格式的,如下:
[root@master manifests]# kubectl get pods myapp-1 -o yaml --export
apiVersion: v1
kind: Pod
metadata:
creationTimestamp: null
generateName: myapp-
labels:
app: myapp-pod
controller-revision-hash: myapp-8598dd746f
statefulset.kubernetes.io/pod-name: myapp-1
ownerReferences:
- apiVersion: apps/v1
blockOwnerDeletion: true
controller: true
kind: StatefulSet
name: myapp
uid: a98ebc48-c24f-11e8-bb35-005056a24ecb
selfLink: /api/v1/namespaces/default/pods/myapp-1
spec:
containers:
- image: ikubernetes/myapp:v1
imagePullPolicy: IfNotPresent
name: myapp
ports:
- containerPort: 80
name: web
protocol: TCP
resources: {}
terminationMessagePath: /dev/termination-log
terminationMessagePolicy: File
volumeMounts:
- mountPath: /usr/share/nginx/html
name: myappdata
- mountPath: /var/run/secrets/kubernetes.io/serviceaccount
name: default-token-5r85r
readOnly: true
dnsPolicy: ClusterFirst
hostname: myapp-1
nodeName: node2
priority: 0
restartPolicy: Always
schedulerName: default-scheduler
securityContext: {}
serviceAccount: default
serviceAccountName: default
subdomain: myapp-svc
terminationGracePeriodSeconds: 30
tolerations:
- effect: NoExecute
key: node.kubernetes.io/not-ready
operator: Exists
tolerationSeconds: 300
- effect: NoExecute
key: node.kubernetes.io/unreachable
operator: Exists
tolerationSeconds: 300
volumes:
- name: myappdata
persistentVolumeClaim:
claimName: myappdata-myapp-1
- name: default-token-5r85r
secret:
defaultMode: 420
secretName: default-token-5r85r
status:
phase: Pending
qosClass: BestEffort
将上面的改改就成为我们新的配置清单了。
创建service account
[root@master manifests]# kubectl create serviceaccount admin
serviceaccount/admin created
[root@master manifests]# kubectl get sa
NAME SECRETS AGE
admin 1 2s
default 1 20d
[root@master manifests]# kubectl describe sa admin
Name: admin
Namespace: default
Labels:
Annotations:
Image pull secrets:
Mountable secrets: admin-token-6jpc5
Tokens: admin-token-6jpc5
Events:
[root@master manifests]# kubectl get secret
NAME TYPE DATA AGE
admin-token-6jpc5 kubernetes.io/service-account-token 3 57s
看到自动就会多一个token。
下面我们用配置清单把serviceaccount和pod绑定起来。
[root@master k8syaml]# cat pod-sa-demo.yaml
apiVersion: v1
kind: Pod
metadata:
name: pod-sa-demo
namespace: default
labels:
app: myapp
tier: frontend
annotations:
lihongxing.com/created-by: "cluster admin"
spec:
containers:
- name: myapp
image: ikubernetes/myapp:v1
ports:
- name: http
containerPort: 80
serviceAccountName: admin
[root@master k8syaml]# kubectl apply -f pod-sa-demo.yaml
pod/pod-sa-demo created
创建useraccount
kubeconfig是客户端连接apiserver时使用的认证格式的配置文件。
[root@master manifests]# kubectl config view
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: REDACTED
server: https://172.16.1.100:6443
name: kubernetes
contexts:
- context: #context定义了哪个集群用哪个用户来访问。
cluster: kubernetes
user: kubernetes-admin
name: kubernetes-admin@kubernetes
current-context: kubernetes-admin@kubernetes
kind: Config
preferences: {}
users:
- name: kubernetes-admin
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
证书存放位置:
[root@master manifests]# cd /etc/kubernetes/pki/
[root@master pki]# ls
apiserver.crt apiserver.key ca.crt front-proxy-ca.crt front-proxy-client.key
apiserver-etcd-client.crt apiserver-kubelet-client.crt ca.key front-proxy-ca.key sa.key
apiserver-etcd-client.key apiserver-kubelet-client.key etcd front-proxy-client.crt sa.pub
例子:
1、做一个私钥
[root@master pki]# cd /etc/kubernetes/pki
[root@master pki]# (umask 077; openssl genrsa -out zhixin.key 2048)
Generating RSA private key, 2048 bit long modulus
...........+++
...........+++
e is 65537 (0x10001)
括号是子shell的意思。
2、基于私钥生成一个证书
CN就是用户的账户名字。
[root@master pki]# openssl req -new -key lihongxing.key -out lihongxing.csr -subj "/CN=lihongxing"
-subj:替换或指定证书申请者的个人信息
[root@master pki]# openssl x509 -req -in lihongxing.csr -CA ca.crt -CAkey ca.key -CAcreateserial -out lihongxing.crt -days 365
Signature ok
subject=/CN=lihongxing
Getting CA Private Key
-days:表示证书的过期时间
x509:生成x509格式证书
4、查看证书内容
[root@master pki]# openssl x509 -in lihongxing.crt -text -noout
Certificate:
Data:
Version: 1 (0x0)
Serial Number:
ab:45:1b:b3:92:32:59:ae
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN=kubernetes #证书签署人
Validity #有效期限
Not Before: Sep 28 08:01:20 2018 GMT
Not After : Sep 28 08:01:20 2019 GMT
Subject: CN=lihongxing#一会用这个账户登录k8s
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
00:bf:e5:b1:80:1a:a6:d1:24:ca:b8:75:a1:71:08:
d2:ba:43:ee:53:a1:10:b5:7a:83:e7:8b:06:65:c7:
8a:07:02:ca:cc:8f:5c:94:a9:7a:10:24:f6:41:a0:
c6:fe:5f:21:59:21:e7:72:30:12:38:89:85:78:54:
c1:15:c4:13:33:43:9c:94:c0:dc:99:e9:f0:44:7e:
35:66:cd:e0:d9:0c:82:dc:b3:73:ee:ea:47:9e:5e:
e5:bf:0b:45:fb:a3:cf:59:67:ae:13:31:9c:dc:b6:
78:da:b2:7e:c0:7e:c2:30:c5:fd:ea:6f:94:fa:81:
19:9f:71:9c:cf:60:07:5b:fa:0d:c0:6f:2c:b4:e0:
42:d6:6d:d3:39:23:2b:f7:ad:cc:21:f8:df:89:ff:
6e:45:59:1f:5d:db:aa:fa:07:ef:fc:b3:7e:3d:b1:
dd:3e:be:5e:43:de:8f:e2:ea:aa:ec:6c:48:df:2f:
2e:20:61:e3:5c:6a:37:3e:2b:32:e5:1a:ad:35:88:
d6:d2:db:aa:26:5d:cb:67:0a:65:9e:d4:79:76:92:
9a:41:fb:df:db:85:1a:ea:5e:ff:bb:7b:2f:01:10:
9f:8e:9c:a1:fe:ae:ac:9d:43:02:40:01:f7:d6:da:
bf:5a:99:ba:d0:bf:ea:53:1e:f5:51:06:9c:ac:6f:
32:43
Exponent: 65537 (0x10001)
Signature Algorithm: sha256WithRSAEncryption
91:43:cd:36:ad:88:17:a1:81:9f:8f:ad:9b:c5:41:d7:de:aa:
6a:f0:3a:00:f2:d7:9b:0e:89:bc:51:73:cc:4f:10:85:13:70:
aa:d1:67:f8:f3:a1:6b:83:ff:99:76:7f:14:a5:b4:82:fb:1b:
fb:cf:d5:fc:b0:2f:ff:68:c4:b1:c0:ee:f9:6b:41:ea:0a:96:
2f:55:1d:d7:77:f8:70:a6:15:a4:b6:e7:6d:93:61:2e:ac:7a:
10:70:fa:f7:43:da:56:f2:d0:e9:6b:01:72:73:2d:65:ea:4d:
c4:3b:46:2d:1b:ad:f8:1f:eb:71:88:35:51:2a:dc:3a:36:fe:
63:bb:28:ee:d2:a0:d4:e0:14:95:10:96:20:2e:f3:75:12:eb:
05:8e:34:a1:dc:74:19:a5:76:0f:f2:bd:f3:56:aa:c9:40:51:
c7:bd:1f:1f:c1:ec:a5:98:c8:b8:1d:07:67:fa:1c:a0:a3:1f:
d3:ba:cb:09:52:9a:e7:59:39:ce:c8:ef:01:c2:4b:98:ff:05:
12:bf:69:36:0e:a6:a9:f6:40:34:28:36:0d:1b:76:31:b4:96:
6e:09:33:8e:d5:0a:96:77:dd:41:b3:29:db:d5:5e:fa:05:f7:
e7:90:5d:79:6d:a9:59:20:60:0f:fe:d5:b6:38:6c:1a:ee:51:
66:c3:9b:4b
5、把用户账户信息添加到k8s集群中
[root@master pki]# kubectl config set-credentials lihongxing--client-certificate=lihongxing.crt --client-key=lihongxing.key --embed-certs=true
User "lihongxing" set.
embed-certs:表示把用户信息隐藏起来。
5、设置context上下文,指定zhixin用户访问k8s的哪个集群
[root@master pki]# kubectl config view
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: REDACTED
server: https://172.16.1.100:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: kubernetes-admin
name: kubernetes-admin@kubernetes
current-context: kubernetes-admin@kubernetes
kind: Config
preferences: {}
users:
- name: kubernetes-admin
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
- name: zhixin
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
[root@master pki]# kubectl config set-context lihongxing@kubernetes --cluster=kubernetes --user=lihongxing
Context "lihongxing@kubernetes" created.
[root@master k8syaml]# kubectl config view
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://172.16.100.64:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: kubernetes-admin
name: kubernetes-admin@kubernetes
- context:
cluster: kubernetes
user: lihongxing
name: lihongxing@kubernetes
current-context: kubernetes-admin@kubernetes
kind: Config
preferences: {}
users:
- name: kubernetes-admin
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
- name: lihongxing
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
上面看到contexts里面有lihongxing的名字了。
6、切换到lihongxing用户登录k8s
[root@master pki]# kubectl config use-context lihongxing@kubernetes
Switched to context "lihongxing@kubernetes"
[root@master pki]# kubectl get pods
No resources found.
Error from server (Forbidden): pods is forbidden: User "lihongxing" cannot list pods in the namespace "default"
上面看到get pods时报错了,这是因为用户lihongxing@kubernetes没有管理器权限。
7、切回k8s管理员
[root@master pki]# kubectl config use-context kubernetes-admin@kubernetes
Switched to context "kubernetes-admin@kubernetes".
8、设置新的k8s集群 ,感觉没屌用这一步在实验里面,想表达啥?
[root@master ~]# kubectl config set-cluster mycluster --kubeconfig=/tmp/test.conf --server="https://127.0.0.1:6443" --certificate-authority=/etc/kubernetes/pki/ca.crt --embed-certs=true
Cluster "mycluster" set
--kubeconfig:指定认证文件位置,不指定的话默认就在~/.kube/config
--embed-certs=true 表示证书信息被隐藏
大家看到,我们上面就创建了一个新的k8s集群叫mycluster。
[root@master ~]# kubectl config view --kubeconfig=/tmp/test.conf
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: REDACTED
server: https://127.0.0.1:6443
name: mycluster
contexts: []
current-context: ""
kind: Config
preferences: {}
users: []
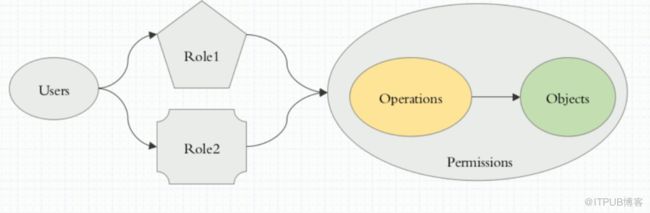
RBAC(基于角色的访问控制)
rbac:role based ac,也就是我们把用户加入角色里面,这样用户就具有角色的权限了。
在k8s中,一切皆对象。
Object_URL: /apis/
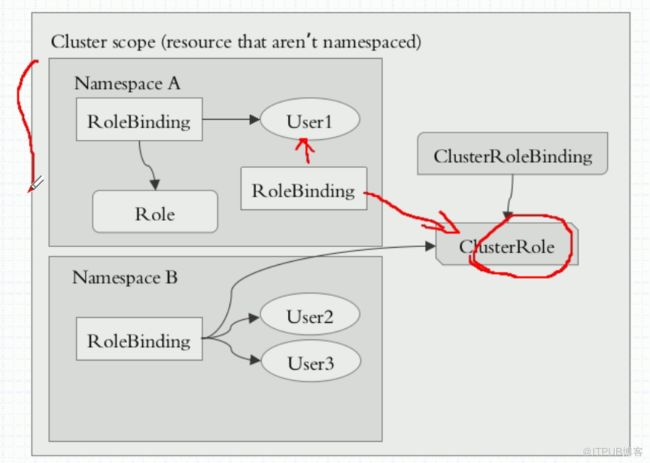
RBAC是通过rolebinding把user绑定到role上的。而role是基于namespace设定的,也就是这说这个user只能访问指定namespace下的pod资源。
而如果把user通过clusterrolebind绑定到clusterrole上后,那么这个user就突破了namespace的限制,而拥有了集群级别的权限,即这个用户可以访问这个集群下所有namespace下的pod了。
但是,我们也可以用rolebinding去把user绑定到clusterrole。在上图中,我们把user1通过rolebinding绑定到clusterrole上,但是我们知道rolebinding只限制在namespace中,所以user1也只限定在namespace中,而不是整个集群中。
[root@master ~]# kubectl create role pods-reader --verb=get,list,watch --resource=pods
注意:想要授予所有权限可以用*来表示
[root@master ~]# kubectl create role pods-reader --verb=get,list,watch --resource=pods --dry-run -o yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
creationTimestamp: null
name: pods-reader
rules:
- apiGroups:
- ""
resources:
- pods
verbs:
- get
- list
- watch
[root@master ~]# kubectl get role
NAME AGE
pods-reader 7s
[root@master ~]# kubectl describe role pods-reader
Name: pods-reader
Labels:
Annotations:
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
pods [] [] [get list watch]
[root@master k8syaml]# kubectl create rolebinding lihongxing-read-pods --role=pods-reader --user=lihongxing
rolebinding.rbac.authorization.k8s.io/lihongxing-read-pods created
[root@master ~]# kubectl create rolebinding lihongxing-read-pods --role=pods-reader --user=lihongxing-o yaml --dry-run
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
creationTimestamp: null
name: lihongxing-read-pods
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: pods-reader
subjects: #就是引用的用户
- apiGroup: rbac.authorization.k8s.io
kind: User
name: lihongxing
[root@master ~]# kubectl explain rolebinding
[root@master k8syaml]# kubectl describe rolebinding lihongxing-read-pods
Name: lihongxing-read-pods
Labels:
Annotations:
Role:
Kind: Role
Name: pods-reader
Subjects:
Kind Name Namespace
---- ---- ---------
User lihongxing
[root@master k8syaml]# kubectl config use-context lihongxing@kubernetes
Switched to context "lihongxing@kubernetes".
[root@master ~]# kubectl get pods
NAME READY STATUS RESTARTS AGE
client 0/1 Error 0 18d
filebeat-ds-bn7wf 0/1 InvalidImageName 0 4d
filebeat-ds-vd287 0/1 InvalidImageName 0 3d
liveness-httpget-pod 1/1 Running 7 11d
myapp-0 1/1 Running 0 23h
上面我们看到先前我们建立的lihongxing用户是没有get pods权限的,但是我这回把它加入了pods-reader role,也就拥有了pods-reader role的权限。
[root@master k8syaml]# kubectl get pods -n kube-system
Error from server (Forbidden): pods is forbidden: User "lihongxing" cannot list resource "pods" in API group "" in the namespace "kube-system"
但是,zhixin用户就没有访问kube-system权限,因为role就没有访问这个名称空间的权限,而只有访问default名称空间的权限。
rolebinding只对namespace有效。
我们再切换回到管理员。
[root@master k8syaml]# kubectl config use-context kubernetes-admin@kubernetes
Switched to context "kubernetes-admin@kubernetes".
下面我们再定义一个clusterrole。
[root@master k8syaml]# kubectl create clusterrole cluster-reader --verb=get,list,watch --resource=pods -o yaml --dry-run > clusterrole-demo.yaml
[root@master k8syaml]# cat clusterrole-demo.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: cluster-reader
rules:
- apiGroups:
- ""
resources:
- pods
verbs:
- get
- list
- watch
[root@master k8syaml]# kubectl apply -f clusterrole-demo.yaml
clusterrole.rbac.authorization.k8s.io/cluster-reader created
创建了ik8s帐号,后面可以用这个账户开个终端,切到lihongxing上,就不用来回在lihongxing和kubernetes-admin之间切换了
[root@master k8syaml]# useradd ik8s
[root@master k8syaml]# cp -rp /root/.kube/ /home/ik8s/
[root@master k8syaml]# chown -R ik8s.ik8s /home/ik8s/
[root@master k8syaml]# su ik8s
[ik8s@master k8syaml]$ kubectl config use-context lihongxing@kubernetes
Switched to context "lihongxing@kubernetes".
[ik8s@master k8syaml]$ kubectl config view
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://172.16.100.64:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: kubernetes-admin
name: kubernetes-admin@kubernetes
- context:
cluster: kubernetes
user: lihongxing
name: lihongxing@kubernetes
current-context: lihongxing@kubernetes
kind: Config
preferences: {}
users:
- name: kubernetes-admin
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
- name: lihongxing
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
[ik8s@master k8syaml]$
[ik8s@master k8syaml]$
[ik8s@master k8syaml]$
[ik8s@master k8syaml]$ exit
exit
[root@master k8syaml]# kubectl config view
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://172.16.100.64:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: kubernetes-admin
name: kubernetes-admin@kubernetes
- context:
cluster: kubernetes
user: lihongxing
name: lihongxing@kubernetes
current-context: kubernetes-admin@kubernetes
kind: Config
preferences: {}
users:
- name: kubernetes-admin
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
- name: lihongxing
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
[root@master k8syaml]#
下面开始绑定了,把之前创建的lihongxing绑定到这个clusterrole上,这样lihongxing就拥有了读取整个cluster的权限,上面已经验证是无法读取kube-system的
先删除之前的rolebinding,可以验证lihongxing是无法读取default里面的pods的
[root@master k8syaml]# kubectl config use-context lihongxing@kubernetes
Switched to context "lihongxing@kubernetes".
[root@master k8syaml]# kubectl get pods
NAME READY STATUS RESTARTS AGE
filebeat-ds-4llpp 1/1 Running 1 8d
filebeat-ds-dv49l 1/1 Running 1 8d
myapp-0 1/1 Running 0 16h
myapp-1 1/1 Running 0 23h
myapp-2 1/1 Running 0 22h
myapp-3 1/1 Running 0 22h
myapp-4 1/1 Running 0 22h
pod-sa-demo 1/1 Running 0 61m
pol-vol-hostpath 1/1 Running 1 5d18h
redis-85b846ff9c-fjq69 1/1 Running 0 2d17h
[root@master k8syaml]# kubectl config use-context kubernetes-admin@kubernetes
Switched to context "kubernetes-admin@kubernetes".
[root@master k8syaml]# kubectl get rolebinding
NAME AGE
default-namespace-admin 16h
lihongxing-read-pods 56m
[root@master k8syaml]# kubectl delete rolebinding lihongxing-read-pods
rolebinding.rbac.authorization.k8s.io "lihongxing-read-pods" deleted
[root@master k8syaml]# kubectl config use-context lihongxing@kubernetes
Switched to context "lihongxing@kubernetes".
[root@master k8syaml]# kubectl get pods
Error from server (Forbidden): pods is forbidden: User "lihongxing" cannot list resource "pods" in API group "" in the namespace "default"
[root@master k8syaml]# kubectl config use-context kubernetes-admin@kubernetes
上面可以发现删除之前的绑定是无法在去访问pod资源了
接下来进行绑定
[root@master k8syaml]# kubectl create clusterrolebinding lihongxing-read-all-pods --clusterrole=cluster-reader --user=lihongxing -o yaml --dry-run
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
creationTimestamp: null
name: lihongxing-read-all-pods
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-reader
subjects:
- apiGroup: rbac.authorization.k8s.io
kind: User
name: lihongxing
[root@master k8syaml]# kubectl create clusterrolebinding lihongxing-read-all-pods --clusterrole=cluster-reader --user=lihongxing -o yaml --dry-run > clusterrole-demo.yaml
[root@master k8syaml]# cat clusterrole-demo.yaml
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: lihongxing-read-all-pods
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-reader
subjects:
- apiGroup: rbac.authorization.k8s.io
kind: User
name: lihongxing
[root@master k8syaml]# kubectl apply -f clusterrole-demo.yaml
clusterrolebinding.rbac.authorization.k8s.io/lihongxing-read-all-pods created
[root@master k8syaml]# kubectl get clusterrolebinding
NAME AGE
lihongxing-read-all-pods 13s
[root@master k8syaml]# kubectl describe clusterrolebinding lihongxing-read-all-pods
Name: lihongxing-read-all-pods
Labels:
Annotations: kubectl.kubernetes.io/last-applied-configuration:
{"apiVersion":"rbac.authorization.k8s.io/v1beta1","kind":"ClusterRoleBinding","metadata":{"annotations":{},"name":"lihongxing-read-all-pod...
Role:
Kind: ClusterRole
Name: cluster-reader
Subjects:
Kind Name Namespace
---- ---- ---------
User lihongxing
验证,可以读取kube-system的pod了
[root@master k8syaml]# kubectl config use-context lihongxing@kubernetes[root@master k8syaml]# kubectl get pods
NAME READY STATUS RESTARTS AGE
filebeat-ds-4llpp 1/1 Running 1 8d
filebeat-ds-dv49l 1/1 Running 1 8d
...
[root@master k8syaml]# kubectl get pods -n kube-system
NAME READY STATUS RESTARTS AGE
coredns-78d4cf999f-lb8dp 1/1 Running 1 12d
coredns-78d4cf999f-qfvns 1/1 Running 1 12d
删是无发删除的
[root@master k8syaml]# kubectl delete pods myapp-0
Error from server (Forbidden): pods "myapp-0" is forbidden: User "lihongxing" cannot delete resource "pods" in API group "" in the namespace "default"
可见,我们把用户lihongxing绑定到clusterrole后,这个 用户对所有的名称空间都有权限了。因为cluserrolebinding是针对集群的,而rolebinding是只针对namespace的。
下面我们再测试一个,把用户用rolebinding绑定到cluserrole里面,看是什么效果:
[root@master ~]# kubectl config use-context kubernetes-admin@kubernetes
Switched to context "kubernetes-admin@kubernetes".
[root@master ~]# kubectl delete clusterrolebinding lihongxing-read-all-pods
clusterrolebinding.rbac.authorization.k8s.io "lihongxing-read-all-pods" deleted
[root@master ~]# kubectl create rolebinding lihongxing-read-pods --clusterrole=cluster-reader --user=lihongxing
rolebinding.rbac.authorization.k8s.io/lihongxing-read-pods created
[root@master ~]# kubectl describe rolebinding lihongxing-read-pods
Name: lihongxing-read-pods
Labels:
Annotations:
Role:
Kind: ClusterRole
Name: cluster-read
Subjects:
Kind Name Namespace
---- ---- ---------
User lihongxing
[root@master ~]# kubectl config use-context lihongxing@kubernetes
Switched to context "lihongxing@kubernetes".
[root@master ~]# kubectl get pods
NAME READY STATUS RESTARTS AGE
client 0/1 Error 0 18d
filebeat-ds-bn7wf 0/1 InvalidImageName 0 4d
filebeat-ds-vd287 0/1 InvalidImageName 0 3d
[root@master ~]# kubectl get pods -n kube-system
No resources found.
Error from server (Forbidden): pods is forbidden: User "lihongxing" cannot list pods in the namespace "kube-system"
可以看出,clusterrole用rolebinding绑定后,会被降级到rolebinding所在的namespace里面。
[root@master ~]# kubectl get clusterrole admin -o yaml
resources:
- pods
- pods/attach
- pods/exec
- pods/portforward
- pods/proxy
verbs:
- create
- delete
- deletecollection
- get
- list
- patch
- update
- watch
[root@master ~]# kubectl create rolebinding default-nameespace-admin --clusterrole=admin --user=lihongxing
rolebinding.rbac.authorization.k8s.io/default-nameespace-admin created
这样,我们就把lihongxing设置为default名称空间的管理员,而不是其他名称空间的管理员。这就是用rolebinding绑定clusterrole的功能。
[root@master ~]# kubectl get clusterrolebinding cluster-admin -o yaml
- apiGroup: rbac.authorization.k8s.io
kind: Group
name: system:masters
[root@master pki]# openssl x509 -in ./apiserver-kubelet-client.crt -text -noout
Subject: O=system:masters, CN=kube-apiserver-kubelet-client
看到system:masters组具有管理员权限 ,lihongxing账户可以删除了
[root@master k8syaml]# kubectl config use-context lihongxing@kubernetes
Switched to context "lihongxing@kubernetes".
[root@master k8syaml]# kubectl get pods -n kube-system
Error from server (Forbidden): pods is forbidden: User "lihongxing" cannot list resource "pods" in API group "" in the namespace "kube-system"
[root@master k8syaml]# kubectl delete pods myapp-0
pod "myapp-0" deleted